Unspecified vulnerability in the MySQL Client component in Oracle MySQL 5.5.36 and earlier and 5.6.16 and earlier allows remote attackers to affect confidentiality, integrity, and availability via unknown vectors.
Monthly Archives: April 2014
CVE-2014-2422 (hp-ux, javafx, jdk, jre)
Unspecified vulnerability in Oracle Java SE 7u51 and 8, and JavaFX 2.2.51, allows remote attackers to affect confidentiality, integrity, and availability via unknown vectors.
Oracle Critical Patch Update Advisory – April 2014
CVE-2013-5704
The mod_headers module in the Apache HTTP Server 2.2.22 allows remote attackers to bypass “RequestHeader unset” directives by placing a header in the trailer portion of data sent with chunked transfer coding. NOTE: the vendor states “this is not a security issue in httpd as such.” (CVSS:5.0) (Last Update:2014-07-24)
CVE-2014-0159 (debian_linux, openafs)
Buffer overflow in the GetStatistics64 remote procedure call (RPC) in OpenAFS 1.4.8 before 1.6.7 allows remote attackers to cause a denial of service (crash) via a crafted statsVersion argument.
Panda Security will continue to support and provide protection for Windows XP
Panda Security, The Cloud Security Company, today announced that its 2014 consumer solutions (Panda Global Protection 2014, Panda Internet Security 2014 and Panda Antivirus Pro 2014), as well as Panda Gold Protection and Panda Cloud Antivirus Pro, will continue to provide the same level of service to Windows XP users, despite the fact that Microsoft support for the operating system officially ended on April 8.
Microsoft launched Windows XP on October 25, 2001, and now, after almost 13 years, the Redmond company has decided to stop providing support for the popular platform. This means that users will no longer receive technical assistance, automatic security updates or fixes to help protect their PCs. However, as previously announced last January, Panda Security products will continue to support Windows XP systems for the foreseeable future.
“Windows XP’s end of life does not mean that computers will stop working from one day to the next. April 8 will be no more dangerous for Windows XP users than April 7. The only thing that’s going to happen is that, officially, Microsoft is no longer going to support XP and there will be no more updatesâ€, explained Hervé Lambert, Retail Product Marketing Manager at Panda Security. “It is very important for us to keep our commitments to our customers. Therefore, users with a Panda Security product installed on their systems will continue to enjoy maximum protection for Windows XPâ€.Â
Advice for Windows XP and Office 2003 users
Microsoft’s decision affects all Windows XP users worldwide. In this context, computers with Windows XP and Office 2003 will still work, but they might become more vulnerable to security risks.
“These vulnerabilities or security holes will leave an open door on computers, and these holes could lead to, say, a Web page infecting users’ computers simply when they visit it. This is something that happens at present, which is why we often remind users of the importance of applying all security updates, both to the operating system and to other software they have installed. However, from April 8, there will be no more updates for Windows XP and Office 2003, and consequently the risk of an attack will increase over time. It is a question of ‘when’ rather than ‘if’ new vulnerabilities will appearâ€, said Lambert.
Windows XP users who have a Panda Security 2014 consumer product installed on their systems (Panda Global Protection 2014, Panda Internet Security 2014 and Panda Antivirus Pro 2014), as well as Panda Gold Protection or Panda Cloud Antivirus, will continue to enjoy the same level of protection on their computers.
“At Panda Security we advise users to upgrade to a newer version that offers greater security such as Windows 7, Windows 8.1, Mac OS X or GNU/Linux. There is no need to panic if you have Windows XP, though it is time to think seriously about whether you ought to migrate to a more current operating system and protect it with a robust security solutionâ€, concluded Lambert.
![]()
CVE-2014-0636 (rsa_bsafe)
EMC RSA BSAFE Micro Edition Suite (MES) 3.2.x before 3.2.6 and 4.0.x before 4.0.5 does not properly validate X.509 certificate chains, which allows man-in-the-middle attackers to spoof SSL servers via a crafted certificate chain.
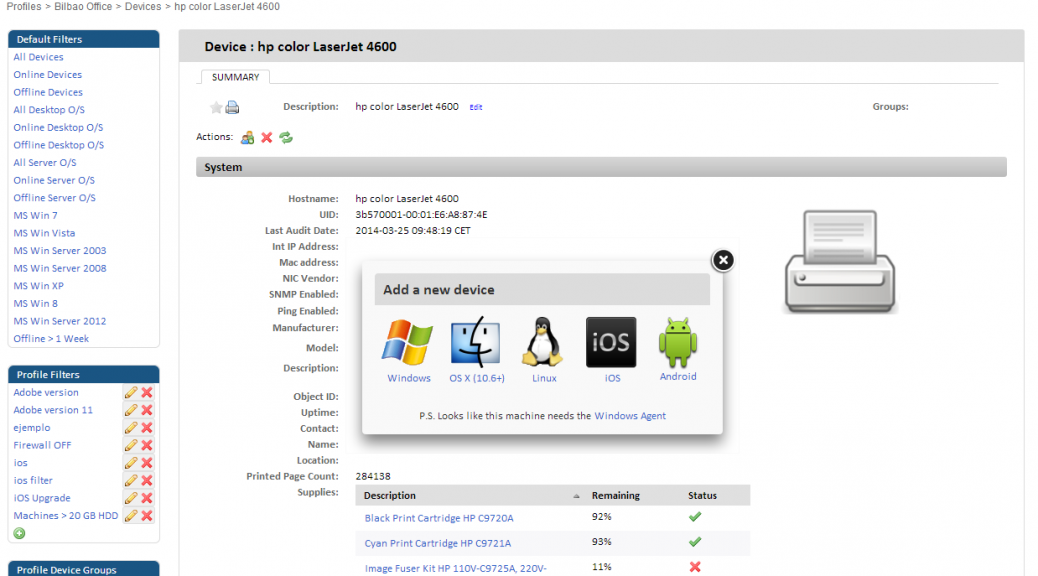
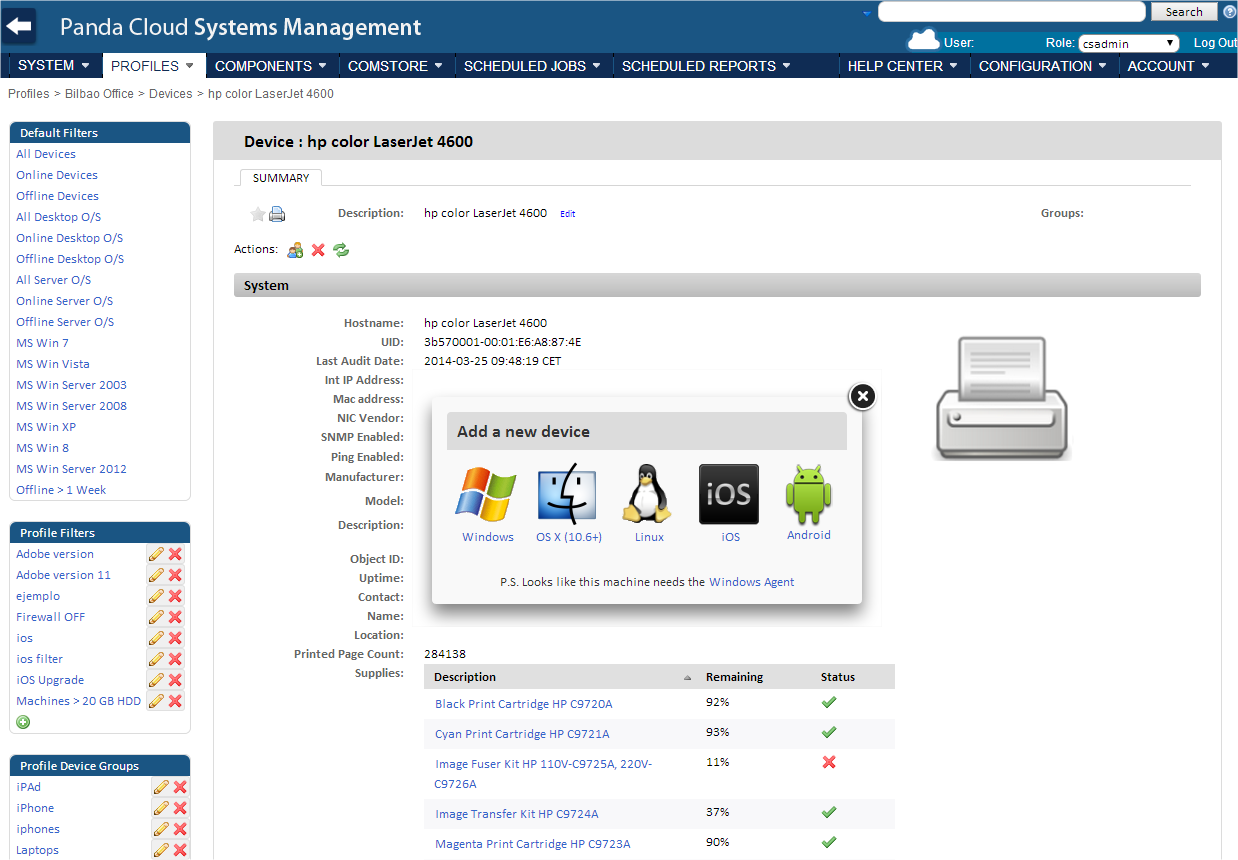
Panda Cloud Systems Management Now Allows Management of Windows, Mac and Linux devices as well as tablets and smartphones
Panda Security, The Cloud Security Company, today announced the addition of significant enhancements and new features to Panda Cloud Systems Management (PCSM), its remote management and monitoring solution designed to help organizations manage, monitor and support all types of devices on their computer networks, both in the office and on the road.
The new features incorporated in Panda Cloud Systems Management include printer management via SNMP, which allows IT administrators to configure monitors and alerts to control printer status, track toner and paper usage, etc. This feature will extend to routers and switches in future releases.
Activity Log
The new version of Panda Cloud Systems Management also boasts a new activity log feature. Every action that takes place on users’ computers is logged in a report, giving administrators the ability to search, filter and export log data. This feature provides detailed, comprehensive visibility into network activity, so that administrators can see at any time which actions have been performed by each user and when.
Additionally, the solution provides additional security measures, such as two-factor authentication to access the PCSM Web console. “With this new feature it will be extremely difficult, if not impossible, to compromise user accountsâ€, said Manuel SantamarÃa, Product Manager Director at Panda Security.
Linux Device Management
The new version of Panda Cloud Systems Management adds Linux support to its cross-platform management capabilities. Panda Security understands that today’s enterprise environments consist of multiple operating systems and platforms, and helps IT administrators deal with this situation by offering them PCSM, a unified solution for managing Windows, Mac, iOS, Android and now Linux devices.
This feature is available for Linux computers running Ubuntu and Red Hat, and includes hardware and software inventory. Additionally, the solution supports remote access to network computers via a command line interface, and includes advanced system utilities such as Shell, Restart, Shutdown, File Transfer, Quick Jobs and Wake on LAN.
“The new features incorporated into PCSM deliver significant benefits to companies, easing IT management and reducing costs,†explained SantamarÃa. “With the launch of this new service, Panda Security reinforces its commitment to providing comprehensive solutions that reduce the complexity of security management. Thanks to Panda Cloud Systems Management, partners have an easy-to-use, centralized management tool that reduces maintenance time and costs, improves margins and revenue and provides added value for customers.â€
More information about Panda Cloud Systems Management here.
![]()
Captcha Bypass in extension "powermail" (powermail)
Release Date: April 10, 2014
Bulletin update: September 18, 2014 (added CVE)
Component Type: Third party extension. This extension is not a part of the TYPO3 default installation.
Affected Versions: powermail: Version 2.0.0 – 2.0.10
Vulnerability Type: Captcha Bypass
Severity: Low
Suggested CVSS v2.0: AV:N/AC:L/Au:N/C:N/I:N/A:P/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6288
Problem Description: The extension powermail offers the use of a captch validation to secure forms. It was possible to bypass the captcha validation and submit forms.
Important Note: Other field validators weren’t involved so any other validation worked as expected.
Solution: Updated version 2.0.11 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/powermail/2.0.11/t3x/. Users of the extension are advised to update the extension as soon as possible as long as they use captchas in their forms.
Credits: Credits go to Jigal van Hemert who discovered and reported this issue.
General advice: Follow the recommendations that are given in the TYPO3 Security Guide. Please subscribe to the typo3-announce mailing list to receive future Security Bulletins via E-mail.
OpenSSL heartbeat information disclosure
A serious vulnerability in the popular open source cryptographic library OpenSSL has been disclosed and Proof-of-Concept (POC) exploit code is publicly available. This affects deployments using 1.0.1 and 1.0.2-beta releases with TLS heartbeat extension enabled. Successful exploitation allows an attacker to remotely read system memory contents without even needing to log on to the server. It is highly advised to update all the affected products as soon as a patch for the particular product is available and to proactively get updates from the affected vendors.