Monthly Archives: July 2016
Teenager Cautioned For Hacking Rivals In Online Game
Security Firm Clarifies Power Station SCADA Malware Claim
Tor Veteran Lucky Green Exits
The evolution of the Retefe banking Trojan
Three weeks ago, we published a blog post about the
Retefe banking Trojan
, which began targeting banking customers in the United Kingdom. The Trojan steals login credentials and other personal information. Retefe is usually spread via a phishing email. The email contains a document, which is embedded with malicious JavaScript and user interaction is needed to activate the Trojan.
Another UK bank has now been added to the list of affected banks. The main behavior of the Trojan has largely remained unchanged, with the exception of its malicious components. The infection vector, as well as the installation of the malicious certificate, are the same as we reported in our last blog post.
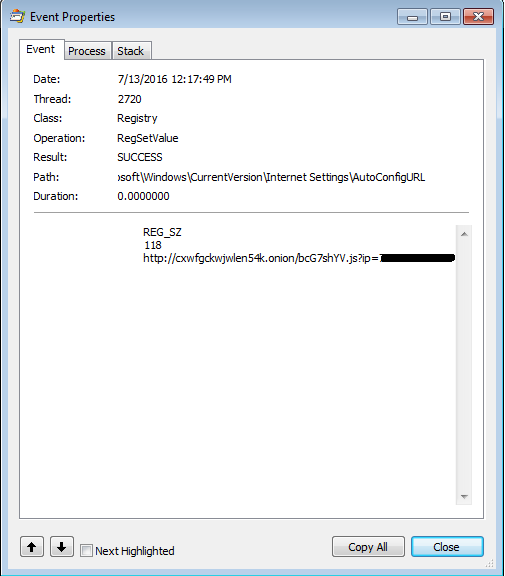
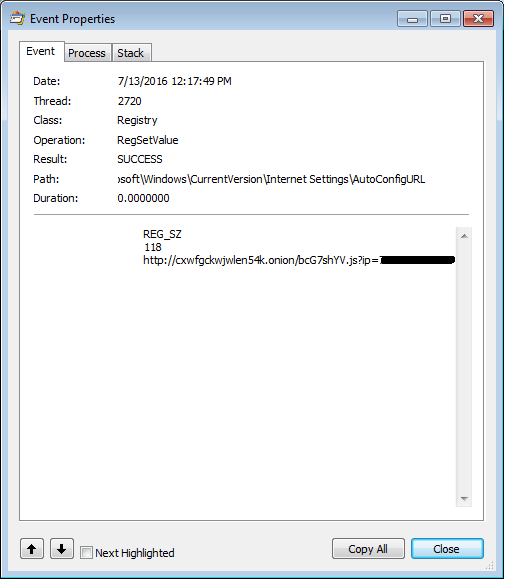
Once the JavaScript runs it attempts to kill open Web browser processes. It then installs a fake certificate and changes the proxy auto-config URL. All scripts are obfuscated with the Dean Edwards packer. This behavior is similar to the previous version of Retefe.
The JavaScript, however, now contains three powershell scripts, two of which are the same as in the previous version. ConfirmCert clicks “OK” in the window displayed during the installation of the rogue certificate and AddCertFF adds the rogue certificate to FireFox. InstallTP is the new powershell script. It downloads and installs three programs: Task Scheduler wrapper, Tor and Proxifier.
The Task Scheduler Managed Wrapper is downloaded from Codeplex. This adds the option to use the object “New-Object Microsoft.Win32.TaskScheduler.TaskService”, which is later used for establishing persistence.
The Tor client gives the Trojan the possibility to access .onion domains directly.
Proxifier, as stated on their website, “allows network applications that do not support working through proxy servers to operate through a SOCKS or HTTPS proxy and chains.”.
The AutoConfigURL contains a link to a .onion domain and it can be reached now because Tor was, installed.
![]()
A smarter approach to password security ‘needed’
A smarter approach to password security is needed to help prevent cybercriminals from easily accessing our accounts and stealing personal information.
The post A smarter approach to password security ‘needed’ appeared first on We Live Security.
![]()
Drupal Core – Highly Critical – Injection – SA-CORE-2016-003
- Advisory ID: DRUPAL-SA-2016-002
- Project: Drupal core
- Version: 8.x
- Date: 2016-July-18
- Security risk: 20/25 ( Highly Critical) AC:Basic/A:None/CI:All/II:All/E:Proof/TD:Default
- Vulnerability: Injection
Description
Drupal 8 uses the third-party PHP library Guzzle for making server-side HTTP requests. An attacker can provide a proxy server that Guzzle will use. The details of this are explained at https://httpoxy.org/.
CVE identifier(s) issued
- CVE-2016-5385
Versions affected
- Drupal core 8.x versions prior to 8.1.7
Solution
Install the latest version:
- If you use Drupal 8.x, upgrade to Drupal core 8.1.7
- If you use Drupal 7.x, Drupal core is not affected. However you should consider using the mitigation steps at https://httpoxy.org/ since you might have modules or other software on your server affected by this issue. For example, sites using Apache can add the following code to .htaccess:
<IfModule mod_headers.c> RequestHeader unset Proxy </IfModule>
We also suggest mitigating it as described here: https://httpoxy.org/
Also see the Drupal core project page.
What if I am running Drupal core 8.0.x?
Drupal core 8.0.x is no longer supported. Update to 8.1.7 to get the latest security and bug fixes.
Why is this being released Monday rather than Wednesday?
The Drupal Security Team usually releases Security Advisories on Wednesdays. However, this vulnerability affects more than Drupal, and the authors of Guzzle and reporters of the issue coordinated to make it public Monday. Therefore, we are issuing a core release to update to the secure version of Guzzle today.
Contact and More Information
The Drupal security team can be reached at security at drupal.org or via the contact form at https://www.drupal.org/contact.
Learn more about the Drupal Security team and their policies, writing secure code for Drupal, and securing your site.
Follow the Drupal Security Team on Twitter at https://twitter.com/drupalsecurity
5 questions with: Marek Chrenko

Get to know Marek Chrenko in the following Q&A.
Marek Chrenko came to Avast in the summer of 2014, when the mobile development startup Inmite joined the Avast team. Originally an Android developer, Marek started developing iOS products last year.
![]()
Firefighting, security and compliance
Security includes firefighting and compliance as well as systems and network management, but should the same people do it all?
The post Firefighting, security and compliance appeared first on We Live Security.
![]()