Summer is in full swing, but school season is right around the corner. Young people are targeted for data theft at 35 times the rate of adults – they are considered an easy target for both digital and physical theft. You can make going back to school an easier transition by ensuring your data and devices are secure both at school and at home. Even if you’ll be using the computers provided by your school’s libraries or labs, there are plenty of steps you can take to make your data safer.
Protecting Your Devices at School
If you’re using your own desktop, laptop or smartphone, there are two things to be concerned with: Physical and information theft. There are a few things you can do to minimize the odds of both types of theft, and mitigate the damage if either does occur.
- Minimize the target
Don’t leave your laptop or phone unlocked and unattended, whether you’re at home or in public – these items are easily grabbed when you’re not looking. And when you take your laptop with you in public, it’s best to carry it in a bag that doesn’t advertise what’s inside; laptop sleeves or carriers let people know exactly what you’re carrying. - Minimize the damage
Installing a Tracker App will help you track down your device, should it be lost or stolen. And if the files on your device are encrypted, even if someone gets access to your computer, they won’t be able to profit from your information. - Beef up your security
Physical loss and thefts are not the only ways to lose information on your phone. Malware and phishing are becoming increasingly common on mobile devices, so be sure to protect yourself. To protect yourself from phishing, make sure you’re using different passwords for all your different accounts, and pick a strong password for each. Using a password manager can help make this an easier task. Once you’ve got a good password, protect it: Don’t share it with others and don’t enter your password into sites you’ve visited via links in email or IM. To protect yourself from malware, install apps only from reputable apps stores, and scan those files with an anti-malware product before installing. - Be cautious on public Wi-Fi
You can never be entirely sure who’s sharing the network with you on public Wi-Fi, so be extra careful when you use public Wi-Fi, like at school or at your local coffee shop. Use VPN software so that your web traffic will all be encrypted – it’ll help keep people from electronically eavesdropping on you.
Securing Your Data When Using Communal Machines
There may be times when you may need to use the computers that are provided by the school. You really have no idea who was using that computer last, or what they were doing before you got there, so you should probably assume the worst. It’s best to act as if anything you type or see on the screen can be recorded and act accordingly:
- Do not use public machines to log into accounts, especially accounts that store financial information (e.g., bank accounts or credit cards).
- Avoid online shopping, as someone could get not just your login credentials, but your credit card number.
- If for some reason you do need to log into an account on a public machine, it is essential to change any passwords you may have used, when you get back to your own machine.
- Browse in Privacy Mode if you can – if not, be sure to clear your browser history and all cookies.
Younger people may feel that their information is of lesser value than more established adults, because they may have smaller bank accounts or less-juicy data, and may not take security as seriously. Ultimately, it doesn’t matter how young you are – your data and identity are valuable to cybercriminals and correcting the problems caused by loss and theft is a pain, no matter your age. Protecting your data now will help you avoid those headaches.
The post How to protect your identity at school appeared first on We Live Security.
![]()

 ‘See who has been looking at your Facebook profile’
‘See who has been looking at your Facebook profile’
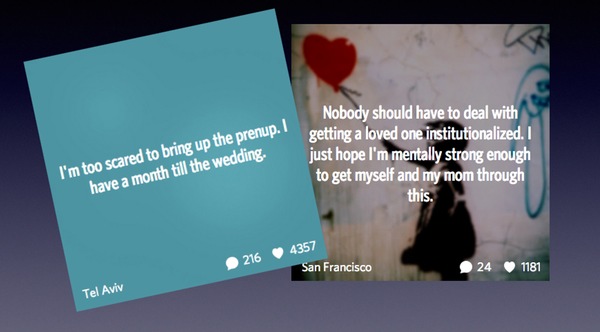
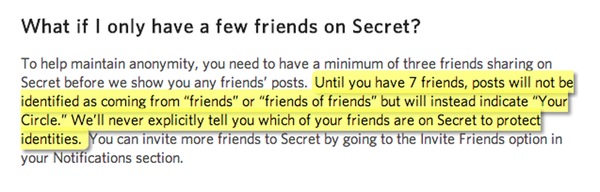
 And the Secret app’s developers have confirmed that since a bug bounty was introduced in February, a total of 42 security holes have been identified and fixed.
And the Secret app’s developers have confirmed that since a bug bounty was introduced in February, a total of 42 security holes have been identified and fixed.