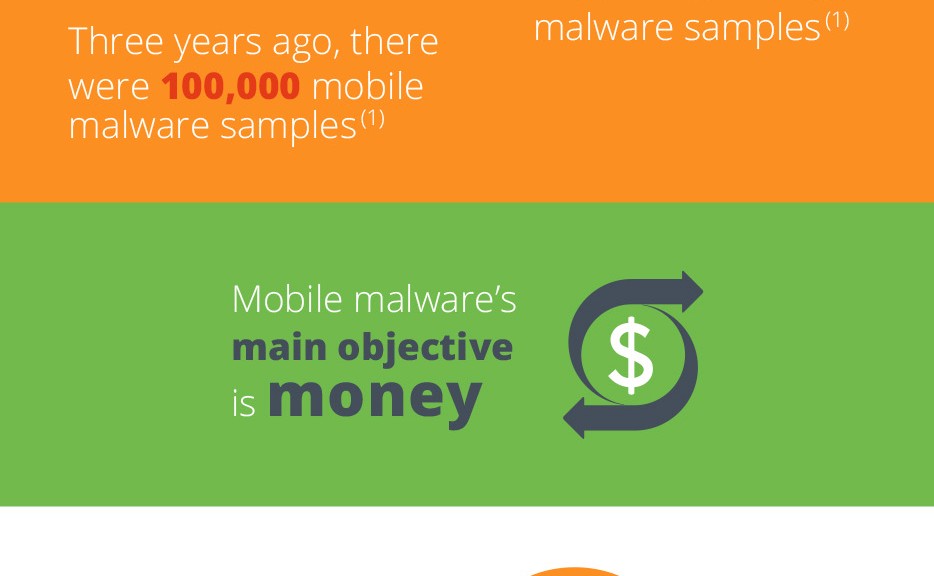
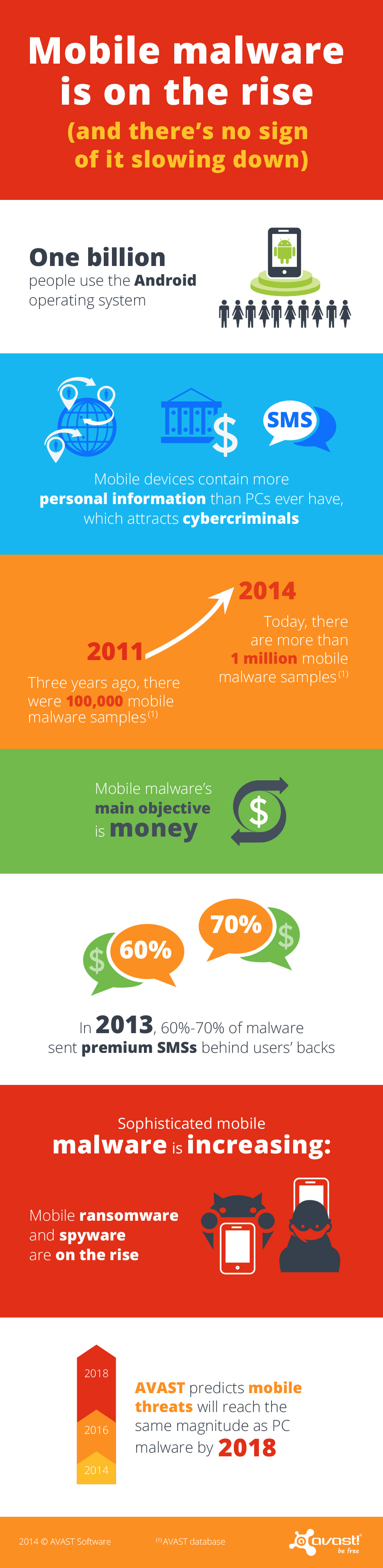
Mobile malware is growing exponentially. We now have more than 1 million malicious samples in our database, up from 100,000 in 2011. Still relatively young, most mobile malware has a pretty simple structure, yet it is designed to effectively steal people’s money. Newer mobile malware is, however, adapting and evolving, slowly embracing more deceitful and complex tactics to target users.
PC malware authors started in a garage, mobile malware authors in an office
Mobile malware is undergoing a similar development as PC malware did years ago with two significant differences: First, PC malware, in its early stages, was created by hobbyists and has only slowly evolved into a serious business within the last 10 years. Mobile malware, even with its simple structure, has been a serious business from the get-go. Smartphones and tablets are capable of gathering and storing more personalized data than PCs ever did – there is an abundance of valuable data to collect, including personal data and financial information. Thus, the focus of mobile malware has always been on monetization, meaning that even early mobile malware posed real-life threats to its victims, stealing money from them. Secondly, even though malware targeting smartphones and tablets is still young, it’s developing much faster than PC malware did in its initial years.
There are multiple entry points for mobile malware; apart from malicious apps placed in app stores and in-app ads linking to malicious content, malware authors also often take advantage of bugs in mobile operating systems, in popular apps or carrier billing structures. In 2013, around 60 to 70% of malware was tailored to send premium text messages behind users’ backs, a simple trick malware authors took advantage of to get into people’s wallets. The industry is catching up to malware and retaliating – carriers in the US and other countries have banned premium text messaging services. As the industry reacts, mobile malware authors start thinking of and using much more sophisticated and deceitful ways to get to people’s money.
The next generation of mobile malware
Elaborate malware, such as ransomware and spyware, is on the rise and is slowly taking control of mobile devices and the pool of potential victims can only get larger. Google now has more than 1 billion Android users. Formerly only known on the PC platform, a Cryptolocker-like ransomware has recently targeted Android devices for the first time, scaring users by holding their devices hostage, claiming to encrypt files until the user paid the ransom. Mobile spyware, on the other hand, is capable of tracking user location and a variety of other personal data, which can later be used to hack accounts or for identity theft.
We predict that with the emergence of new technologies, malware authors will find new ways of taking advantage of them. For example, as the use of new payment methods like Near Field Payment (NFC) increases, we expect hackers will change the way they go after money.
Users need to become aware of how valuable smartphones really are – not just the hardware, but the data it contains
Mobile threats are increasing – we expect them to reach the same magnitude as PC malware by 2018. However, out of the more than 1 billion smartphones that were shipped globally last year, only a small percentage are currently protected with antivirus software.
To make mobile devices safer and more secure, we need to collectively work together – the security industry, carriers, app store providers and consumers. At AVAST, we are constantly refining our tactics to detect mobile malware, to protect our users with our free and paid solutions. Actions like major carriers in the US, Brazil and the UK no longer billing customers for most forms of commercial Premium SMS messages, thus shutting an important door for malware creators, are a great initiative – and we hope carriers in other countries will follow this step, soon. Also, stricter security rules for apps on Google Play and other app stores could help make some types of malware extinct.
In the end, it’s also up to users to protect their devices and data with security solutions. People need to understand that there are new threats being built to target their mobile devices. Phones and tablets contain people’s personal treasures, in the form of data, whether that be personal information about loved ones or bank details – all of which is interesting for cybercriminals. Therefore, it is essential that people care for their smartphones and tablets in the same way as they protect their PC, the majority of which has antivirus installed.
Thank you for using avast! Antivirus and recommending us to your friends and family. For all the latest news, fun and contest information, please follow us on Facebook, Twitter and Google+. Business owners – check out our business products.
Â