Yahoo has hired former Twitter and Rapid7 security executive Bob Lord as its new CISO, taking over for Alex Stamos, who this summer left Yahoo for Facebook.
Tag Archives: Privacy
Arrest Made in TalkTalk Hack
TalkTalk CEO Dido Harding said someone purporting to be the hackers who attacked the U.K. telecom demanded a ransom to keep them from publishing the stolen data.
NSA’s Divorce from ECC Causing Crypto Hand-Wringing
The NSA is moving away from Elliptic Curve Cryptography, and cryptographers aren’t buying their reasoning that advances in post quantum computing put ECC in jeopardy.
Government and misuse of technology are most feared by Americans
Americans don’t trust that technology will be kept out of the hands of bad guys.
Forget about zombies, vampires, and ghosts. Americans don’t fear things that go bump-in-the-night as much as they do their own government. The annual Survey of Fear conducted by Chapman University asked Americans about their level of fear in 88 different topics ranging from crime, the government, disasters, personal anxieties, technology, and others. The majority of Americans said that they are “afraid” or “very afraid” of the corruption of government officials.

One of American’s greatest fears is government-sponsored spying
The misuse of technology, financial crime, and privacy-related issues took up half of the Top 10 fears of 2015. After two years of high-profile data breaches and the revelations of government spying from the Edward Snowden leaks, it’s not too surprising. Here’s the list:
- Corruption of government officials (58.0%)
- Cyber-terrorism (44.8%)
- Corporate tracking of personal information (44.6%)
- Terrorist attacks (44.4%)
- Government tracking of personal information (41.4%)
- Bio-warfare (40.9%)
- Identity theft (39.6%)
- Economic collapse (39.2%)
- Running out of money in the future (37.4%)
- Credit card fraud (36.9%)
From this survey, it’s apparent that Americans’ awareness and concern about guarding their personal privacy is growing. An interesting topic that was further down the list is “Technology I don’t understand,” feared by 19% of Americans surveyed. At least that is something that individuals can control – just watch some videos or read this blog and you will learn about technology and how you can minimize your risks of these other things happening to you. For example, here’s how to secure your Facebook login and protect your personal privacy and identity.
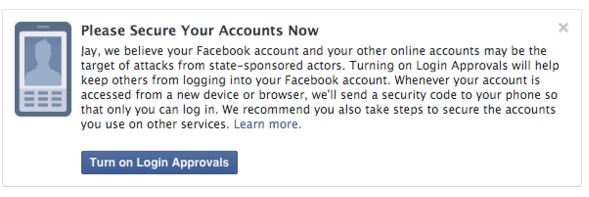
Facebook announces government spying alert
The fears of government spying don’t go unwarranted. Facebook has reason to believe that it’s an important issue “because these types of attacks tend to be more advanced and dangerous than others.” These are the words of Facebook’s Chief Security Officer, Alex Stamos, in a recent announcement telling if the social media network suspects that a user is being targeted by government-sponsored hackers, they will issue an alert advising them to “take the actions necessary to secure all of their online accounts” such as “rebuild or replace these systems [your computer or mobile device] if possible.”
Follow Avast on Facebook, Twitter, YouTube, and Google+ where we keep you updated on cybersecurity news every day.
![]()
Apple: It is impossible to access encrypted data on iPhones
Apple has once again reiterated its claim that it is technically impossible for it to access encrypted data on iPhones that are running iOS 8 or higher and even if it was possible, it would be apprehensive to perform such an action.
The post Apple: It is impossible to access encrypted data on iPhones appeared first on We Live Security.
![]()
Protecting your wallet in the digital age
In days gone by, keeping your wallet safe while out and about just meant making sure it was still in your pocket. But with a variety of new payment technologies such as contactless payment or Chip and PIN being developed and rolled out, and hackers becoming increasingly creative about how they access and use your information, times are changing fast.
While we all want speedier, more convenient payment options, have you stopped to consider the level of personal information you now carry around about yourself, and whether you are still doing such a good job of keeping your wallet safe in today’s digital age?
As National Cyber Security Awareness month continues, I’ve jotted down a few of my top tips:
When is a wallet, not a wallet?
There has been much talk of the ‘digital wallet’ in recent years, but with NFC payments now enabled through schemes such as Apple Pay and Android Pay, your smartphone could now be considered a wallet on its own. As such, you’ll need to consider both its physical and cyber security. This means taking steps such as considering where you’re carrying and using your phone, making sure you have software to protect it from malware, and ensuring you only use it at trusted locations for sensitive transactions such as money transfers.
Does you wallet speak for itself?
With contactless payment systems becoming more popular, especially in Europe, even cards in your wallet could speak without you knowing. If you card has the ‘contactless’ Wi-Fi type symbol on it then it most likely has RFID technology that allows details to be read from the card without the need to swipe or insert into a chip and pin reader. This also means that if a cybercriminal can get close enough to your card then they might be able to read some of the data from it. Wallet manufacturers are now producing wallets that add pockets of protection for you to store cards of this type. I recently purchased one and now it stores both my driver’s licence and contactless cards in the protected zone.
Putting a PIN in your security
With the increase in payment technologies such as Chip and PIN and contactless, the contents of your traditional wallets are also more vulnerable than ever before. So what steps should you take here?
Just as you wouldn’t leave your house keys in your front door, your card or phone’s PIN number should never be written down and certainly not left with the card or phone itself. If you have trouble remembering the PIN provided by your bank, you should change it to a number that’s easier for you to remember – but not so easy that others could guess it. When entering your PIN, you should also hide it from anyone who might be looking!
While not yet mainstream in the U.S., ‘touch and go’ NFC payment from a phone or ‘contactless’ RFID from a credit card is already common in Europe. Making a payment in seconds is appealing to many of us, but this convenience comes with a number of other security considerations. In the UK, there is currently a cap of $45 (£30) on such purchases – minimising the risk of significant purchases being made on a stolen card or phone. For anyone still feeling nervous, it is possible to ‘opt out’ and request a simple Chip and PIN card.
Beyond these more ‘high-tech’ tips, there are other points of best practice that should always be observed in protecting your financial security.
Check what you’re paying for
As cashless payment becomes the norm, it’s easy to lose track of what you’re spending, and even if you’re the one spending it! Always make sure to check your bank statement, even if online, for any ‘rogue’ payments. Many of us have the attitude that ‘it won’t happen to me’, but fraudsters will often start with small amounts that may go unnoticed to those who aren’t vigilant.
Bin those receipts
Is your wallet bulging with six months’ worth of receipts? If so, de-clutter! Receipts can carry a whole host of valuable information including your credit card details or signature. Keep any important receipts for returns, warranties or business expenses, at home and make sure to shred the rest. Expired cards should also be cleared out of your wallet. While you can’t use them anymore, your information could still be of use to a potential fraudster.
Having taken my wallet with me on various travels abroad recently, I know I’ve kept these tips in mind, and fingers crossed, remained fraud free! Hopefully they will help you do the same!
![]()
![]()
Let’s Encrypt Hits Another Free HTTPS Milestone
Let’s Encrypt hit a milestone last night when it received the cross-signatures necessary to render its beta-and free-certificates trusted by all browsers.
CIA director’s personal email account ‘breached by teen’
It has been claimed that the director of the CIA has had his personal email account breached by a teenager, with social engineering playing a part in the hack.
The post CIA director’s personal email account ‘breached by teen’ appeared first on We Live Security.
![]()
Protect sensitive documents and data with AVG’s Data Safe
If you need to protect sensitive files or documents on your PC, you’re going to want an extra layer of security. AVG’s Data Safe feature can help.
Data Safe encrypts and stores your valuable documents, pictures or any other files onto a password-protected virtual disk on your PC. You can move files into your Data Safe and open them just like any other disk.
The contents of your AVG Data Safe are protected using AES 256-bit encryption. Once the Data Safe is locked it needs a password to be opened, without the password it’s not possible to access the contents—so your documents will remain protected.
AVG Data Safe is available in:
- AVG Internet Security and AVG Protection PRO
You can create multiple Data Safes and change their size as needed. - AVG AntiVirus
You can create one Data Safe with a fixed size.
How to create a Data Safe
- Open AVG.
- In the AVG interface, click the Computer tab
- On the Data Safe tab, click Create Safe.
- Create a name for the Safe
- Fill in the Password twice—for verification. Make it strong and memorable.
- Fill in the Password hint. Remember: If you forget your password you will not be able to access your files!
- Click Next.
- Select a Location and the Size of the vault, review the other options.
- When you’re happy with your choices, click Create Safe.
Once the Safe has been created, click the Open Now button. If the safe isn’t already unlocked, fill in your password to unlock the safe for the first time. The safe will now be accessible via the selected drive letter in Windows Explorer.
How to lock your Data Safe
- Open AVG.
- In the AVG interface, click the Computer tab, and then click Manage your Safes.
- Click the Unlocked slider next to the safe you want to lock. The status will change from unlocked to locked, and the Data Safe virtual drive will be disabled.
If you want to try AVG’s Data Safe feature for yourself, download a 30-day trial of AVG Internet Security. If you have multiple PCs and devices, you can protect and mange them all with AVG Protection PRO.
For more great tips on getting the most out of your PC, Mac and mobile devices, follow us on Twitter and Facebook.
![]()
![]()
Webcam hacker spent up to 12 hours a day watching his victims
A hacker who used the notorious Blackshades RAT malware to hijack webcams on computers, and secretly watch people engaged in sexual activity, has received a suspended prison sentence.
The post Webcam hacker spent up to 12 hours a day watching his victims appeared first on We Live Security.
![]()