In an increasingly interconnected community where more relationships are formed through online connections, people not only need a way to safeguard their information, but to protect themselves from cyber threats.
Short Version: Since 1991, AVG products, which are now part of Avast, have been one of the most popular providers of online security software, offering a free-to-download antivirus product for Windows, Mac, and Android devices. For those wanting additional features and functionality, the subscription option, AVG Internet Security, automatically scans your system and gets rid of any harmful malware and viruses while keeping your security up to date against the latest threats. For online daters, that means instant peace of mind. While you browse through a dating site, the HMA! Pro VPN application will automatically encrypt sensitive information, hide your location, and keep you safe online. You can maintain your privacy on a dating site by using AVG Internet Security, the #1 resource for security software.
Tony Anscombe, AVG Product Evangelist, has made online security his life’s work. For over two decades, his job has been to speak directly to consumers and raise awareness about cyber-security issues by writing blog posts and articles and giving lectures around the world.

A while back, in London, he gave a memorable presentation to a group concerned about privacy online. Before the talk, he asked their permission to do some digging and see what he could pull up about an attendee’s online footprint — using just her name.
Even those who consider themselves very private often leave a trail. Someone who knows what they’re doing (like Tony) can follow old accounts and access data that users may not want to be public knowledge.
In the case of one woman, he was able to find old dating profiles where many personal details lay hidden. He’d never met her, but suddenly he was an expert on her.
As Tony rattled off her favorite song, favorite car, and where she vacationed last year, she sat dumbfounded. She hadn’t imagined so much information existed about her online. “That’s remarkable,” she said.
When you enter the world of online dating, you don’t want to reveal too much information to the wrong people. The AVG product line, one of most popular brands of security software, provides the best options to keep you safe while flirting over the web. Since 1991, this tech-savvy team has backed up singles online with state-of-the-art protection from phishing, spamming, malware, viruses, and other threats to personal information.
“We believe everybody has a right to a certain level of protection,” Tony said. “If somebody’s got a laptop or a phone today, there are so many cyber threats that it’s essential they have a security product to protect them from bad guys.”
AVG’s Free Online Security Protects You on Any Device
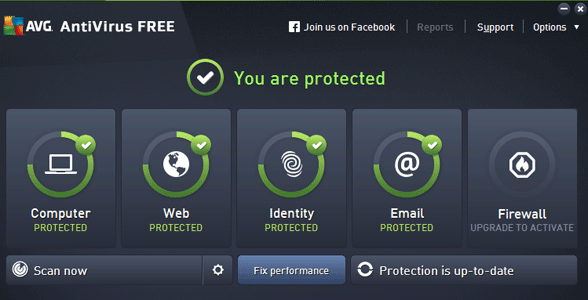
AVG security products provide protection, performance, and privacy for people, and you can get a great product immediately at no cost. If you want more features, you can also sign up for the free 30-day trial of AVG Internet Security to experience enhanced firewall, disk cleaner, automatic updates, and other functions that keep all your devices running smoothly.
Whether you’re a fan of desktop dating using your Mac computer or you like to date on the go with your Android phone, AVG Internet Security protects consumers from the latest threats ranging from malware to email spam.
Anyone can be hacked, even Mark Zuckerberg, if proper measures of protection aren’t in place. To keep your dating profile as safe as possible, Avast also offers proactive solutions like the HMA! Pro VPN application, which encrypts your Internet connection and hides your location to keep you and your information safe. In the unlikely event you are hacked, its Remote Virus Removal service can get rid of any viruses or malware on your computer and restore your devices.
As his family’s resident IT guy, Tony said he uses AVG Internet Security to manage everyone’s software, sometimes running a scan for his son or updating the software for his parents. “I’ve become their remote IT manager, and I can do all that from my phone,” he said. “There’s a whole host of protection products to choose from.”
The company sees 1 billion malware attacks per month, blocks more than 500 million malicious URLs per month, and blocks around 50 million phishing attacks per month. When it comes to protecting people on their mobiles, in 2010, the AVG AntiVirus for Android app was the first antivirus app available on Google Play to surpass 100 million downloads. Free for the first 30 days, the AVG app comes with a device lock, app backup, and other features to protect mobile users.
My favorite is the Camera Trap, which takes a picture of anyone snooping on your phone or tablet. If a nosy partner tries and fails to unlock your device, it’ll snap a photo and email it to you. Caught red-handed!
A Security Expert Gives 4 Safety Tips to Online Daters
With 20 years of background working as a technician and consumer advocate, Tony has plenty of expertise regarding how to date safely on the web. He takes his security-conscious perspective everywhere he goes.
Sitting at the airport during our phone interview, he looks around and sees people on their phones, most likely using public WiFi to surf online. Unless it’s encrypted, he told us, that traffic can easily be turned into public information.
“Especially when you’re dating, you’re sending lots of personal contact information back and forth,” he said. “All of that is flowing in free texts. It’s like sending a love letter via postcard. Everyone along the delivery train is probably going to read it.”
To help you secure your information, Tony shared four essential tips for safely creating an online dating profile.
1. Research Your Electronic Footprint Beforehand
Tony is happily married but tells singles if he were online dating, his first step would be “to actually go out on the Internet and find out what’s out there about me already.”
This is as easy as Googling your name or your username. You’ll see what someone searching for you will find — hopefully, nothing too embarrassing — and you can make sure your virtual identity appears the way you want it. Goodbye, embarrassing LiveJournal profile from 2005.
You can also set up Google Alerts to let you know automatically if any new information about you enters the public domain. That way no one can share any details about you without your knowledge.
2. Create a Separate Email Account With a Unique Password
When you actually set up your dating account, you should have an escape route mapped out, just in case. That means creating a profile that is totally separate from your other online identities: new email account, new username, and new password.
You don’t want people to be able to cross-reference your dating profile with social media accounts. A burner email account will lead any potential stalkers to a dead end, with no way to find your more permanent profiles.
“If everything doesn’t work out on the dating site,” Tony said, “you can kill your existence.”
3. Make Sure Your Pictures Don’t Reveal Your Location
You may not intend to broadcast your location when you post a picture, but for someone who knows where to look, that could be exactly what happens.
Thanks to geo-tagging, when you send your potential match a quick selfie, you could also be sending your exact whereabouts.
“A lot of Internet safety is as much about education and the person behaving responsibly as it is about the technology. Our technology is there as a line of defense to support your good behavior.” — Tony Anscombe, AVG Product Evangelist
“You need to start thinking about if you’re advertising your location,” Tony explained. “If you’re sending a picture in its raw format, and you have your location setting turned on on your camera, your GPS coordinates are attached to it.”
If you’re not ready to share your home address with someone you met online, be sure to extract that data from any media you send.
4. Pay With a Burner Credit Card
“I would also recommend somebody get a burner credit card to pay for a dating profile,” Tony said. “That way it keeps people away from your permanent life.”
You can pick up a prepaid card at the supermarket or buy a virtual visa online. However you go about it, the point is keeping your primary credit card safe from hacking. This way, if the company itself is hacked into — as AshleyMadison was in 2015 — your payment information won’t be compromised.
“Make sure, whatever you’re doing, you’re using different, complex passwords,” he added. “You don’t want to be the next victim of a data breach.”
The Company Continues Growing & Updating Their Safeguards
In 1991, AVG was a small company based out of the Czech Republic. Their security products soon generated high demand, and the company grew to have hundreds of millions of users, and to be known as one of the most reliable products on the market.
By 1998, they were selling products in Europe and the U.S., and in October they were acquired by Avast, an industry-leading maker of the most trusted security software in the world.

Because of AVG’s relentless support, singles signing up on a dating site don’t need to feel vulnerable to online scammers or hackers anymore. Daters have the power to keep themselves safe from cyber threats by downloading the AVG software or apps.
As Tony demonstrated in London, a lot of information is floating freely on the web — AVG has an array of versatile products that can hide details you don’t want to become part of the public domain.
“Keeping ahead of cyber criminals is a huge task,” Tony said. “We are continually developing new engines, new techniques, and new mechanisms to keep people safe.”
*This article was also featured on Dating Advice online site www.datingadvice.com
![]()
![]()