Secret Conversations available on mobile devices Source FB newsroom
![]()
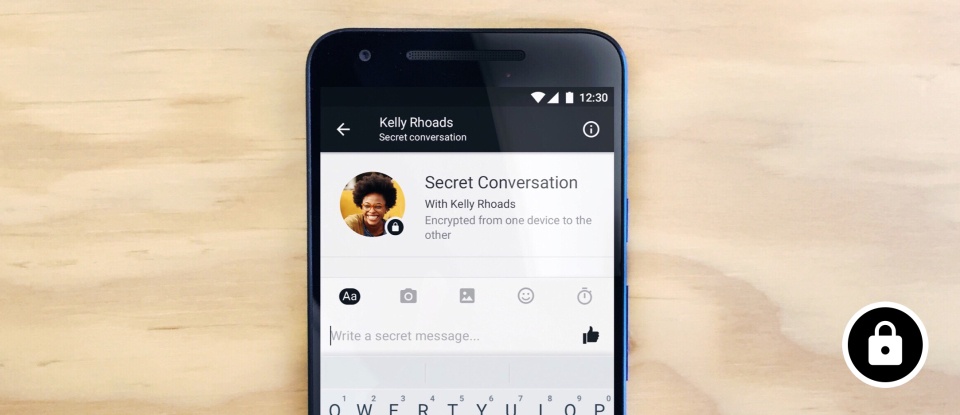
Secret Conversations available on mobile devices Source FB newsroom
![]()
My colleagues from the Avast Threat Labs published an interesting (and detailed) blog post about Petya ransomware and its little brother, Mischa. This duo works together to encrypt disks and files, pushing innocent victims to pay thousands of dollars to regain access to their computers and files. Particularly interesting is that the ransomware authors have an established marketing strategy to promote Petya and Mischa. They created a brand for the ransomware, as well as an affiliate program, making it possible for the IT-savvy average Joe to distribute the ransomware.
![]()
This season finale had me sitting in front of the TV saying “what?” a couple of times – a sign that this was another great episode!
![]()
Petya and Mischa ransomware, come as a package deal, distributed by its creators, Janus. They are very unusual in that they combine two different methods to encrypt user data. Unlike most other ransomware, Petya primarily encrypts MFT (Master File Table) and MBR (Master Boot Record). If Petya has insufficient privileges to access MBR on HDD (Hard Disk Drive), the Mischa module is deployed and encrypts files one by one.
![]()
Things are slowly starting to come together, as they should be considering this was the second to last episode of the season!
![]()
Should you put a tape or a sticker over the lens of your laptop’s webcam?
Yes, even Facebook CEO Mark Zuckerberg and FBI Director James Comey do that.
Covering your laptop’s webcam might be a hell cheap and good idea to guard against hackers and intruders who might want to watch your private life and environment through your devices.
<!– adsense –>
In fact, Comey recently came out
![]()
Zepto ransomware is a relatively new player in the ransomware scene, and it’s closely related to the infamous Locky ransomware. Taking a closer look at Zepto’s code, we found that the code is pretty much the same as Locky’s code, but it has been slightly modified. The malware authors behind Zepto use the same methods used to spread Locky, and even the infection vector and the TOR payment page are the same, which makes us think that the people behind Locky are now spreading Zepto. The only difference between Locky and Zepto is the ransom demand. Zepto’s demand is much higher than Locky’s, 3 Bicoins (approximately $1,850).
![]()
I honestly do not know where to begin with this week’s episode of Mr. Robot, I am still in a bit of shock! Elliot only carried out one hack, but many other things unraveled, leaving with me with so many questions.
![]()

Dropbox has suffered a password dump of epic proportions. (Image via Graham Cluley)
Dropbox has been going through some rough times as of late. In the past 24 hours, headlines have been popping up left and right about a Dropbox password dump of epic proportions.
![]()