A security firm is warning this week that 88 percent of networks are at risk of being compromised via credential theft and reuse.
Tag Archives: SMB security
FTC, Experts Push Startups to Think About Security From the Beginning
About a decade ago, many large software makers learned some very difficult lessons about software security and building security into their products from the start. Some are still learning. The FTC and a variety of security experts are hoping that today’s crop of start-ups will not have to go through that same painful process. The FTC […]
Default SSH Key Found in Many Cisco Security Appliances
Many Cisco security appliances contain default, authorized SSH keys that can allow an attacker to connect to an appliance and take almost any action he chooses. The company said that all of its Web Security Virtual Appliances, Email Security Virtual Appliances, and Content Security Management Virtual Appliances are affected by the vulnerability. This bug is […]
Your SMB’s Biggest Security Threat Could be Sitting in Your Office
This article is a re-print from the April 1, 2015 edition of Silicon India.

Careless employees, not hackers, are the biggest threat to your company’s data security.
Security threats are evolving quickly, making it difficult to pinpoint just one threat that is currently affecting small and mid-size businesses.
From the threats we have observed in the past and the ones we anticipate for the future, we have learned that while malware can be damaging to businesses, so can human decisions. This makes it vital for small and mid-size business owners to discuss possible threats with their employees and share basic IT guidelines with them, but more importantly, to implement a strong security solution that holds up dangers before they become a real threat.
Taking Advantage of Human Nature: Social Engineering
Hackers understand that it is human nature to make mistakes, which is why they often turn to social engineering. Social engineering is a tactic that tricks people into revealing their personal information, like log in details, or into performing actions, like downloading malware disguised as an attachment or link.
Phishing emails are a popular form of social engineering that can easily sneak their way into your employees’ inboxes, disguising themselves as yet another offer, promotion, or even customer, if you do not have anti-phishing protection. Phishing campaigns come in many forms; they can either use scare tactics to make people believe they are in trouble or that they have won a prize.
In the last few months we have seen Trojans like Pony Stealer and Tinba make their rounds. Both Pony Stealer and Tinba attempted to convince people they owed money and to download an invoice, which was of course not an actual invoice, but a Trojan.
Falling for phishing scams can have devastating effects on businesses; they could not only steal personal information, but also attack Point of Sale (PoS) systems to steal customers’ financial information, thus not only affecting the business itself, but its clients as well.
Lack of security awareness: Beneficial for hackers, bad for your business
Not taking proper security precautions, like choosing weak passwords or ignoring security updates, is another human flaw cybercriminals like to abuse to access accounts and networks. To gain control of a system, hackers can enter common or weak passwords or simply look up hardware’s default administrative log in credentials.
Neglecting to update software is another gateway for hackers, leaving vulnerabilities and loopholes wide open for them to take advantage of. Similarly, connecting to public and open Wi-Fi connections while on a business trip is like sending hackers a personal invitation to snoop around your business.
India’s SMBs are getting technology ready – hackers are getting ready, too
According to Indian consulting firm, Zinnov, 20% of India’s 50 million small and mid-size businesses are technology ready. Cybercriminals will take note of this and are probably preparing plans at this very moment, which is exactly what you should do, too.
Set up basic security guidelines for your employees, teach them about possible threats and make sure they understand how imperative their role plays in securing your business. For example, your employees should be encouraged to choose strong passwords for their devices and accounts, to keep their software updated – if that’s not what you manage centrally – and to use a VPN when connecting to unsecure wireless networks.
You cannot, of course, rely solely on your employees to protect your business – humans innately make mistakes. To protect your business and to provide your employees with a safety net, you need to have a proper business security solution. Small to mid-size businesses should look for security solutions that include anti-phishing, firewall to control network traffic, and server-side protection. If employees are required to travel frequently, it also makes sense to implement a VPN solution on their laptop, smartphone, and tablet. If connecting to open Wi-Fi at an airport, hotel or café, a VPN can be used to encrypt valuable business data and protect it from hackers.
As humans do make mistakes, you cannot rely on your employees to implement and manage the security solution themselves. It is recommendable to choose a solution that empowers you to remotely manage the security on your employees’ computers.
Whether your business is a two-man show, or an army of 2,000, awareness, paired with the right security technology are essential.
Dyre Banking Malware A Million-Dollar Threat
IBM warns banks and corporate officers of a change to the dangerous Dyre banking Trojan that involves the phone scam used to bypass fraud detection, and a DDoS attack that distracts security teams away from big-money transfers.
Cisco Small Business IP Phones Open to Remote Eavesdropping
Cisco is warning customers about several vulnerabilities in some of its IP phones that can allow an attacker to listen in on users’ conversations. The bug affects the Cisco SPA 300 and 500 Series IP phones. Cisco had confirmed the vulnerabilities, which were discovered by Chris Watts, a researcher at Tech Analysis in Australia, and is […]
AVG CloudCare scoops award in independent tests
AVG CloudCare’s AntiVirus 2014 component has just received an award following its first ever participation in one of the industry’s top security comparison tests. The latest Virus Bulletin  gave us a score of 91.2 out of a possible 100 in both Reactive and Proactive tests.
In an age where security breaches are common and a company trades more than ever on its reputation, small businesses simply cannot afford to take any chances when it comes to protecting their confidential or customer data.
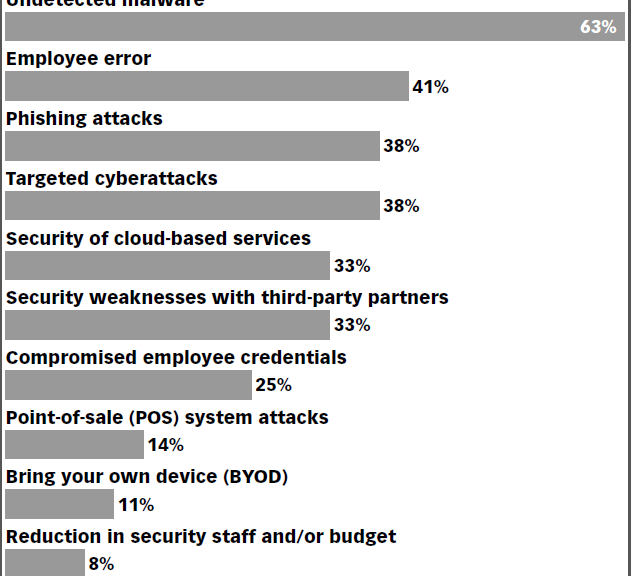
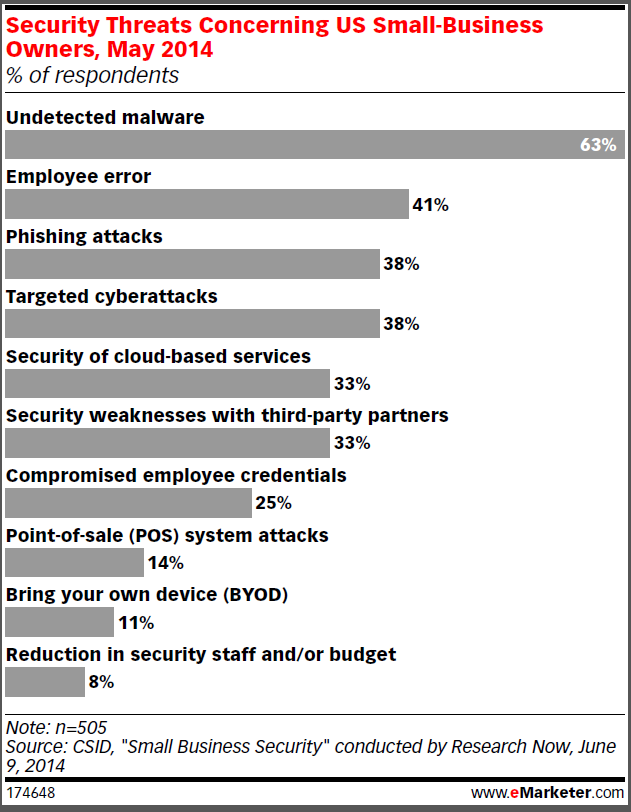
In fact a recent eMarketer study shows that undetected malware and cloud-based security are still among the top security concerns for small businesses.
That’s why I’m delighted that the Virus Bulletin test singled out AVG CloudCare for its scanning and detection performance. It is a strong indicator that we design our product wholly with users in mind and are addressing their very real concerns.
Here’s what Virus Bulletin had to say:
“Scanning was very fast indeed, even in the initial runs, and overheads were pretty light, barely detectable once files had been checked for the first time. Our set of activities ran through in good time, and resource use was low. Detection was very strong indeed with excellent scores throughout our sets, and with no issues to report in the WildList or clean sets, a VB100 award is well deserved, adding another good result to that strong score.â€
Â
Our customers are echoing this sentiment:
Thomas Keats of Rainbow Computers, a small business and AVG IT partner told us  “I love so much about AVG CloudCare, it’s increasing the bottom line, increasing interaction with the customer on more than one level, keeping me and my shop more in their mind each step of the way.”
If you are a small business looking for a way to stay ahead of the security curve why not ask a local IT contractor about AVG CloudCare? Your company’s security would be one less thing to worry about!
Learn more about AVG CloudCare at: www.avg.com/cloudcare
Learn more about the Virus Bulletin 100 test at: https://www.virusbtn.com/virusbulletin/archive/2014/06/vb201406-comparative
![]()
![]()