At the end of this month, Avast will end support for our older consumer versions of Avast Antivirus. Those are: Avast Free Antivirus, Avast Pro Antivirus, Avast Internet Security, and Avast Premier.

Update to Avast 2015 for maximum protection.
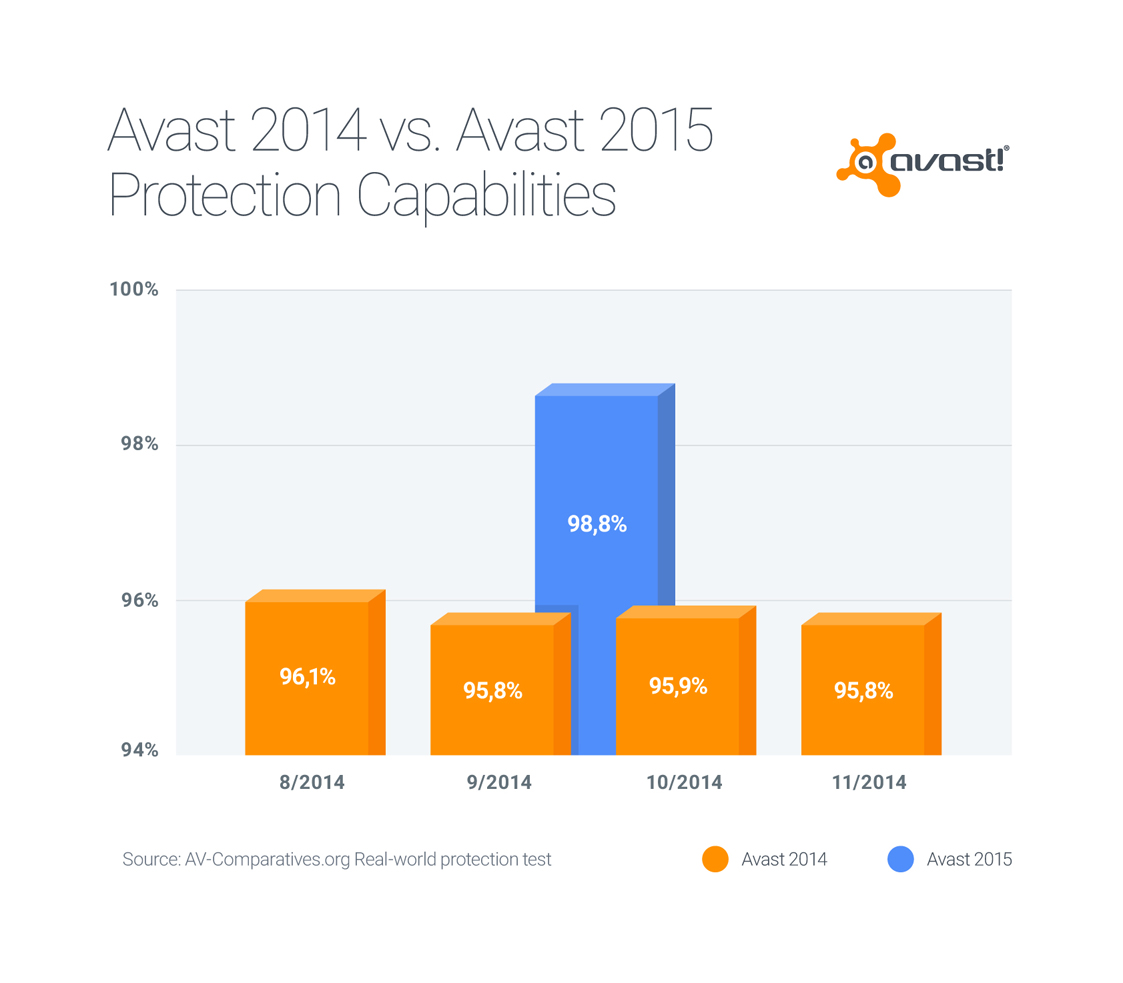
A good antivirus program is a necessity to protect your Windows PC from malware attacks, to keep your computer running smoothly, and to protect your online identity and personal data. Over the past 3 years, Avast engineers have improved our database of known virus definitions, the mechanism in which zero- day and widespread malware are detected, and the frequency of streaming updates sent to our customers. Avast 2015, with its unique Home Network Security feature which scans your home network for potential risks, is our best performing security product yet.
After May 31st, 2015, Avast will no longer provide security patches or technical support for versions 8.0.1497 and lower. Security updates patch vulnerabilities that could be exploited by malware, endangering your machine and the data on it. Please update to the latest version so you can receive regular security updates and benefit from the enhanced features and higher detection rates that protect your computer from malicious attacks. This update is also recommended because the latest version is compatible with Windows 10.
If you are running an older version of Avast, you can easily move to the latest version of Avast 2015.
How to check for the latest version and do a program update
If you need to update later, here’s a quick way to do it.
- Right click on the orange Avast ball icon in the system tray.
- Select Update from the menu and then click Program.
The update screen in the Avast user interface shows you the overall progress of the program update. When it’s done you will be asked to restart your computer. Click Yes to reboot immediately. Once the computer is restarted, information about the update may appear. If you are using a paid subscription, then your protection will be valid for the remaining period of your subscription.


Why to upgrade
- Better detection rates
- Easier technical support
- We fixed bugs and problems that still might exist on your current version
- Receive further program updates to ensure best protection
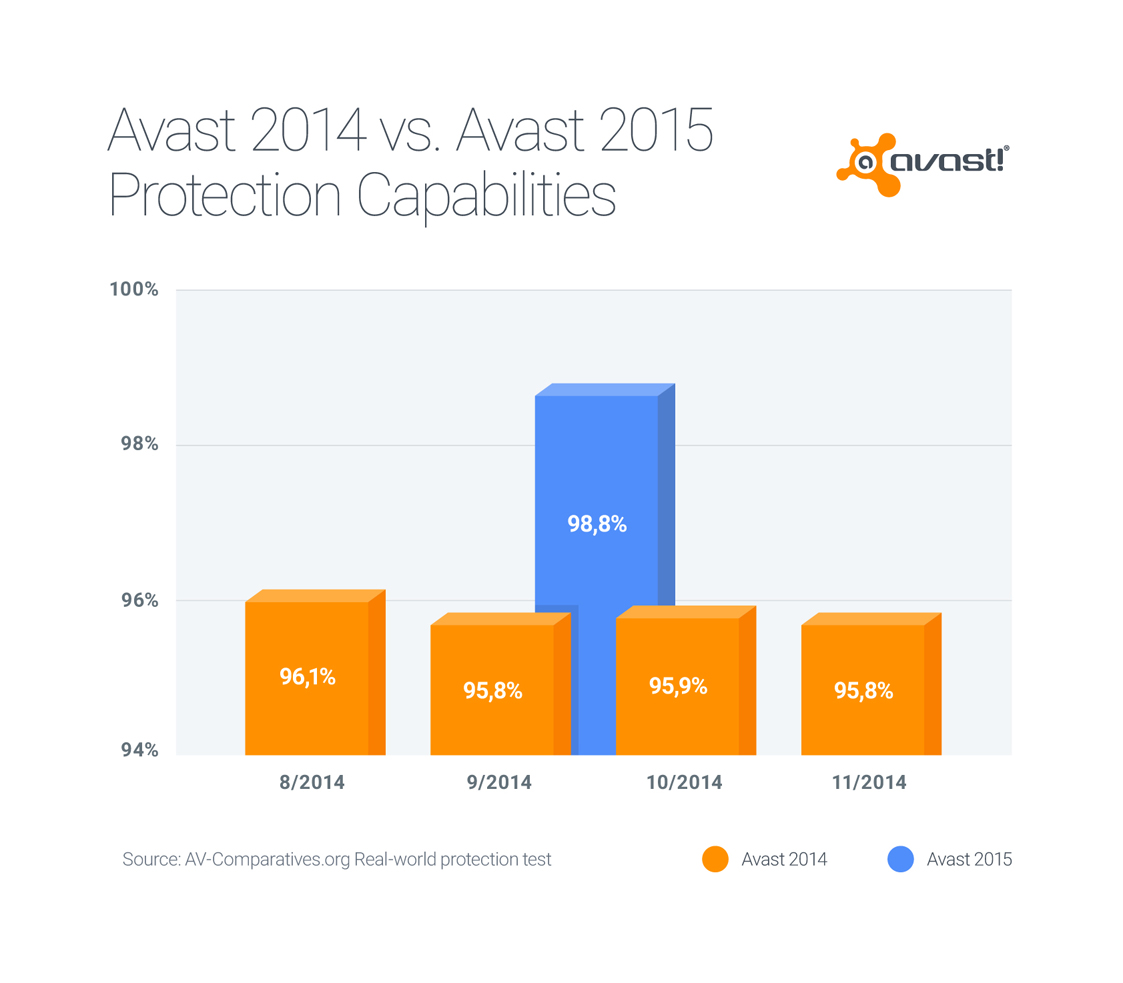
Avast 2015 has better detection rates than older versions. Update as soon as possible for maximum antivirus protection.
If you prefer an older version of Avast and require technical support, you will be asked to update first before we can assist you. There will be no patches issued and technical support will end on May 31st, 2015.