Yesterday, we looked at two hot areas to be aware of regarding your online security: Data breaches and mobile security. Today, we’ll look at two more areas that haven’t caused as much trouble or damage as the other two, but are likely to grow in importance.
Internet of (Every)Thing at risk
 The “smart” home has been in the works for some time now, and this year, we’ll see more and more gadgets from household appliances to wearables like fitness bracelets to industrial equipment becoming connected to mobile devices and social networks. This proliferation of inter-connected things will open up a whole new glorious space for hackers to play in.
The “smart” home has been in the works for some time now, and this year, we’ll see more and more gadgets from household appliances to wearables like fitness bracelets to industrial equipment becoming connected to mobile devices and social networks. This proliferation of inter-connected things will open up a whole new glorious space for hackers to play in.
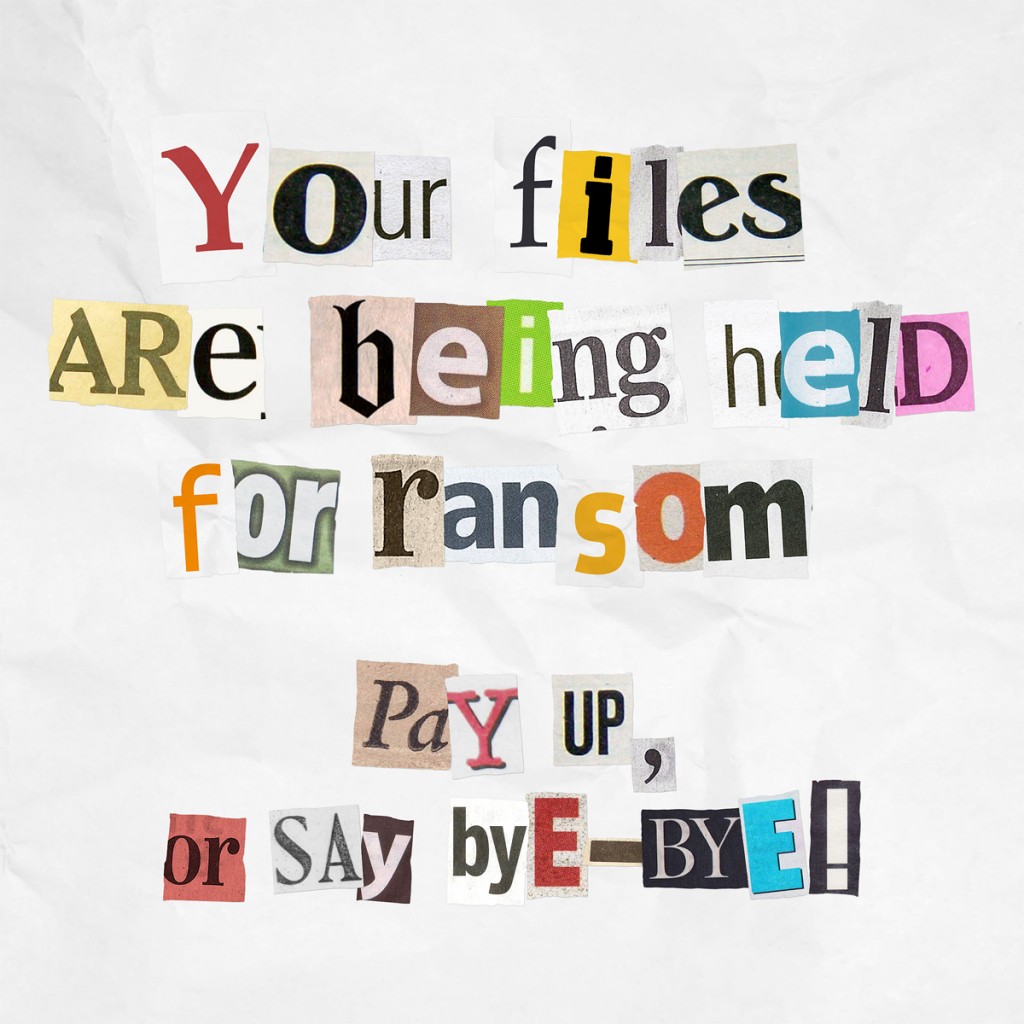
We predict that from now on, devices will increase by an order of magnitude (not too bold a prediction, huh?), and of course, that will result in greater privacy and security concerns. A breach in the Internet of Things (IoT) will give cybercrooks the ability to install malware or ransomware on private networks – not only consumer, but corporate and government – steal personal information, or even cause physical harm to a space or a person. But before you run around the yard yelling, “Skynet is falling, Skynet is falling”, we will see adware uploaded on our smart TVs.
What to keep your eye out for
- New technologies and businesses around the IoT including
o Increased demand for low cost bandwidth and processing
o Expansion of infrastructure that carries Wi-Fi traffic
o Start-ups focused on communication and sensors between devices, storage, data analytics
o Home and factory automation
- The rise of “fog” computing architectures, where data is closer to the source as opposed to residing in a data center somewhere
Room for improvement
- Keeping multiple smart devices updated with the latest version of this-and-that software. You think it’s hard now with a couple of devices? Wait until your house, body, garage, and workplace are full of smart gadgets.
- The fractured ecosystem will make it harder to identify threats or protect against security exploits.
- Home routers are still unsecure and people are using open, unencrypted Wi-Fi. Start by securing your own home router by scanning with Avast’s Home Network Security scan, then follow whatever suggestions are given.
Social media world
By now, social media users know that sharing too much personal information can give strangers access to their personal life. To illustrate that point on a national scale, Allstate Insurance, aired a series of commercials about what happened to a couple who shared on social networks that they were away from their home for the weekend. Read about it on our blog.
Last year, we saw new privacy settings introduced on social media, and 2015 will see a rise in anonymous interactions via social media.
Hoaxes and scams spread by email and social networks were successful in 2014, as they have been for years now, so we see no reason that occurrences will decrease. Social engineering can trick unwitting victims and the rate of identity theft will increase.
What to keep your eye out for
- Continuation of scams associated with important events like celebrity gossip or sporting events.
- Watching videos on Facebook equaled watching videos on YouTube at the end of 2014, so we can expect hackers to take advantage of this by hiding malicious links in Facebook videos.
- More fraudulent and malicious ads will appear on social networks.
- Ransomware made the jump from PC to mobile in 2014, and it will likely hit social networks.
Room for improvement
- Cut back on sharing too much on social media and through Internet of Things devices.
Adjust privacy settings in each social network.



