Tech companies’ privacy policies have the ability to help or hinder users.
When was the last time you sat down and read through the entirety of a tech company’s privacy policy, even if you visit the site every day?
In an article recently published by TIME in collaboration with the Center for Plain Language, a selection of the world’s leading and regularly visited tech websites were ranked in a list in relation to their privacy policies. In short, they rated the companies based on the manner in which they communicated with the public while walking them through their privacy policies. In this case, it wasn’t the actual data that these companies collect from current and potential new users that was being analyzed. Instead, this study looked at the way in which that information is brought to the attention of these users.
When picking apart a company’s policy, it’s important to think about how users can actually benefit from taking the time to read it. While that may sound obvious, we’ve all come across our fair share of unfortunate company pages (such as T&Cs, FAQs, or even About Us sections) that add up to a bunch of unintelligible language that we ultimately digest as gibberish. Regarding the level of clarity in a company’s policy, TIME writes:
Does the policy, for instance, make it easy for people to limit the ways in which the company collects their personal information? Or are instructions about opting out obscured in the policy’s hinterlands with no hyperlinks?
In addition to Google, within the list are three social media platforms that many of us use on a regular (if not daily) basis: Facebook, LinkedIn and Twitter. When taking a closer look at these four websites’ policies, it becomes clear that they approach the issue of individuals’ privacy and personal information in very different ways:
1. Google: Unsurprisingly, Google does a great job of spelling out their policies using language that users can easily understand – hence, it came in first place in this study. The Center for Plain Language concluded that by reading through Google’s privacy policy, users’ trust in the company can actually increase. Impressive, considering that most people’s trust in Google is already considerably high to begin with.
2. Facebook: While certain policies simply acknowledge that they store and analyze user information, Facebook’s “What kinds of information” section takes it a step further, breaking down each kind of interaction users have while using the site and clearly explaining which information is collected and stored while those interactions are being executed.
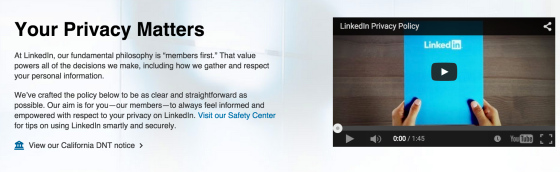
Photo via TIME
3. LinkedIn: Coming in at number three on the Center’s list, LinkedIn is an example of a company with a privacy policy that is mediocre in its clarity and messaging. However, LinkedIn does claim to have crafted “the policy to be as clear and straightforward as possible”, so the company’s third place rating could be a bit of subjective judgement call.
Photo via TIME
4. Twitter: Jump down to the second to last place on the list, and that’s where you’ll find Twitter. In a series of long and hard-to-read paragraphs, users are left wondering what it was that they just read when trying to pick apart Twitter’s privacy policy. This social media channel is a good example of what not to write when attempting to be transparent with audience members.
This study goes to show that it’s not only privacy policies that are crucial – it’s also important to pay attention to the way in which these policies are written and shared with users. Users should always be able to feel that they understand how and why their personal information is stored, analyzed, and/or shared on websites that they frequently use. Read the full report from the Center for Plain Language for a complete privacy policy analysis.
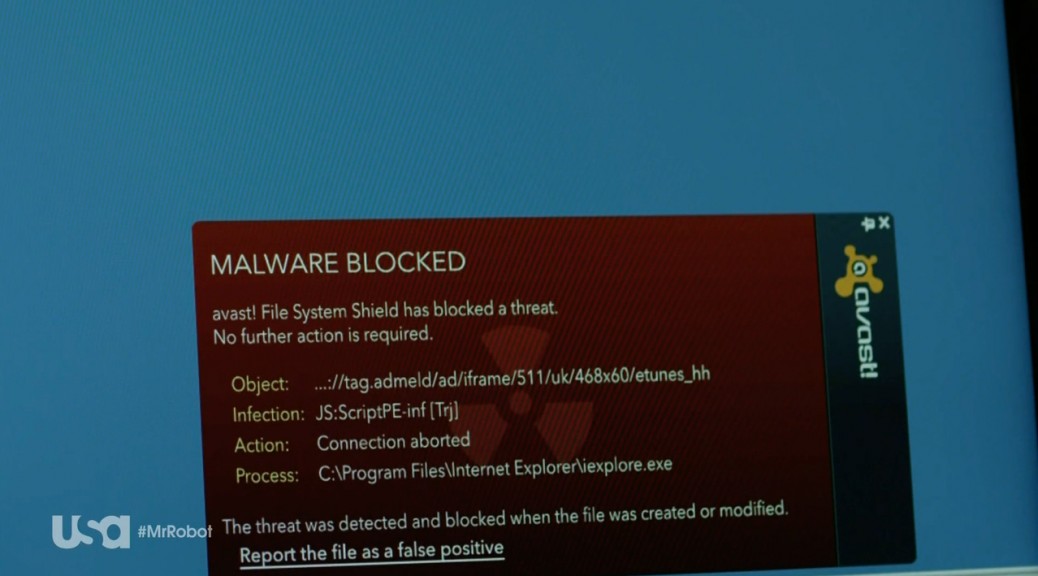
Follow Avast on Facebook, Twitter, YouTube, and Google+ where we keep you updated on cybersecurity news every day.
![]()


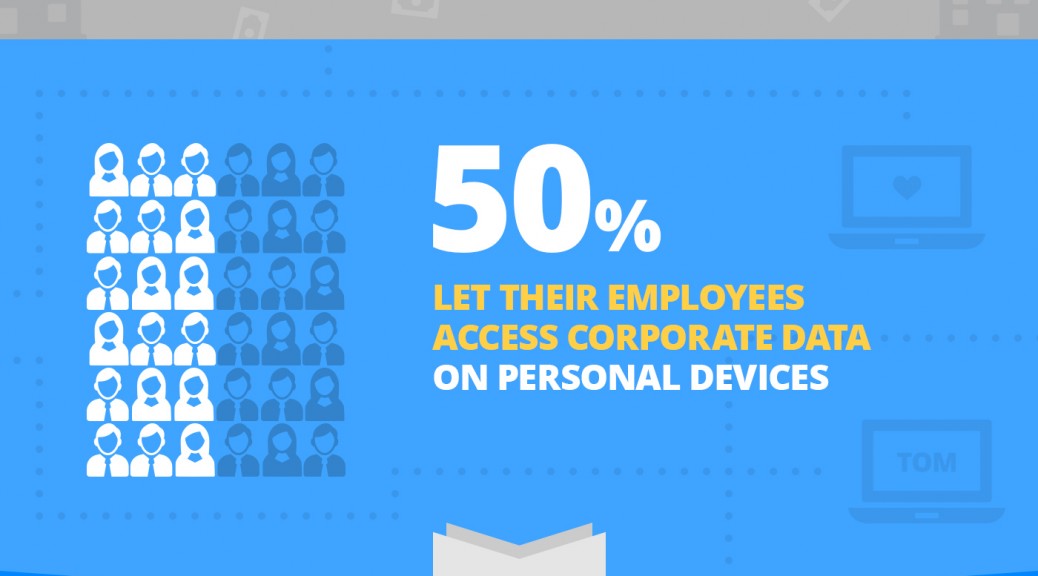
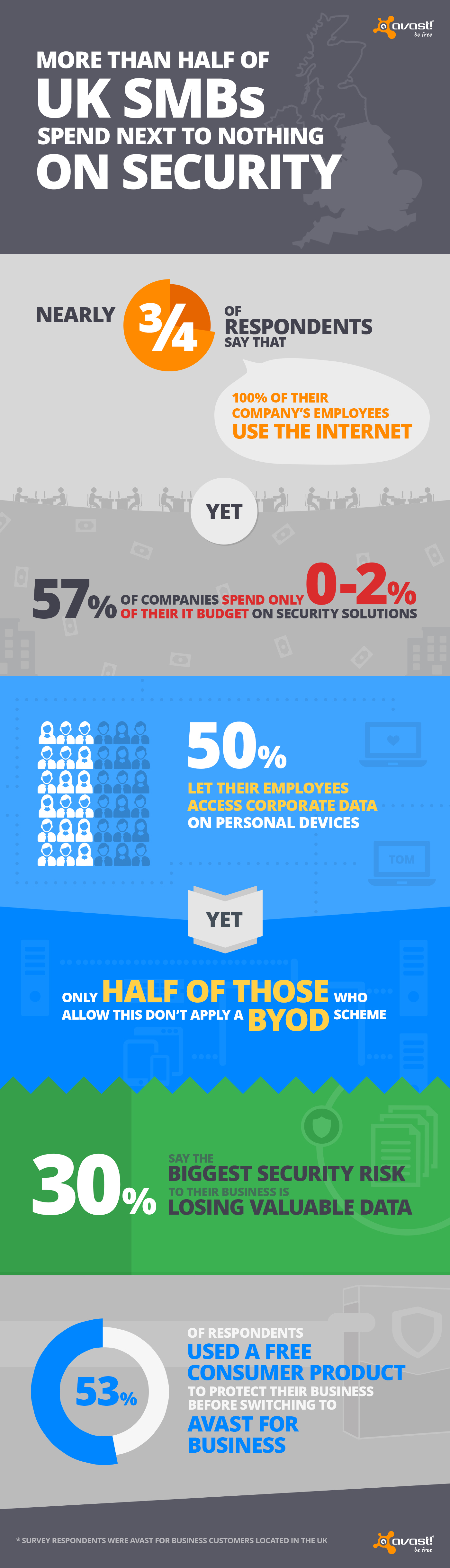 In February, Avast launched the world’s first free, easy to use, cloud-managed security offering, Avast for Business, protecting SMBs from viruses and cyberattacks. We conducted a survey amongst our Avast for Business users in the UK to gain further insight into how local SMBs handle their security.
In February, Avast launched the world’s first free, easy to use, cloud-managed security offering, Avast for Business, protecting SMBs from viruses and cyberattacks. We conducted a survey amongst our Avast for Business users in the UK to gain further insight into how local SMBs handle their security.