Hacker sends woman images of herself and her boyfriend, which were captured through their own webcam.
The post Hacker sends woman pictures of herself from her own webcam appeared first on We Live Security.
![]()
Hacker sends woman images of herself and her boyfriend, which were captured through their own webcam.
The post Hacker sends woman pictures of herself from her own webcam appeared first on We Live Security.
![]()
A major information-sharing bill that’s in the Senate right now would allow private organizations to share threat data with any government agency, something that the Department of Homeland Security says could have severe privacy implications and cause confusion and inefficiencies inside the federal government. The bill, known as the Cybersecurity Information Sharing Act, would allow […]
After years of discussions, disagreements, and digressions, the Do Not Track header is supported by all of the major browsers. But because there’s no real requirement for sites or advertisers to respect it, DNT is not as effective as it could be. Now, the EFF, Disconnect, and several other organizations are publishing a new DNT standard […]
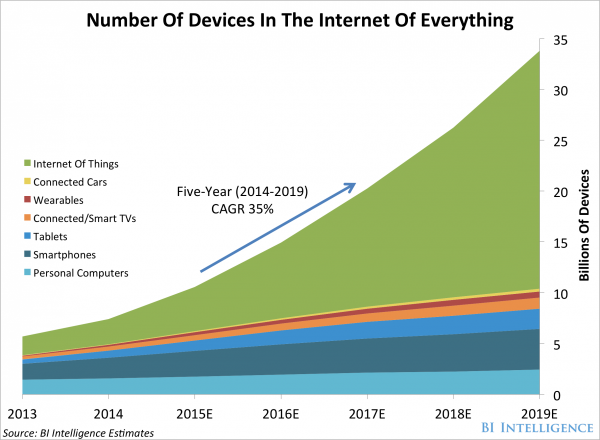
By now, most of us are familiar with the term the “Internet of Things”. It has come to describe the always on, always connected world where day to day objects are online. It ranges from smart-watches to smart fridges and is closer to reality than you may think.
Much has been written about the need to secure the devices that make up the Internet of Things, but I believe there is another battle to be won.
According to most reliable research, the number of Internet connected devices is growing rapidly and will continue to do so for the foreseeable future.
Building security into each and every one of these devices is no mean feat. In fact, it will be very difficult indeed. That’s what I believe that it is of vital importance that we focus our attention on securing routers and Wi-Fi hotspots.
As the number of Internet enabled devices in our homes continues to increase, more and more members of the public are getting ready to adopt smart home appliances, energy meters and wearables.

All of these newly connected devices entering the home should be rigorously secured as they will be handling data specific to your household. Securing them individually could be tough though, until you realise that they share something in common – they communicate via the Internet access point, a home router.
As you can see, the number of home routers in the market is continuing to grow rapidly, but is only a fraction of the number of total devices.

Robustly securing each home router or a public hotspot has the knock-on effect of securing the data transmission of dozens of devices and, for my money, is a much more realistic approach to securing the Internet of Things.
Sadly, security on most popular routers is still pretty basic and has a user experience to match. Clunky menus that aren’t immediately intuitive can leave users at a loss when it comes to making changes to their Internet settings.
Here are three simple things that you can do right now to help improve the security of your home Wi-Fi network.
Change the login details
Most routers will come with default login details. Many people never get round to changing them but you really should. “User name: admin Password: Password” is not a secure login and could potentially grant router level access to attackers if they know the manufacturer defaults of your device.
Set up an access list:
Most routers will allow you to set up a “permitted devices” list that limits access to your network. Setting this list up and including all your family’s devices is a good way to make sure that no unauthorized devices access your network.
Double check your Firewall
A Firewall is an important router feature that helps filter out bad traffic requests coming into your home. All traffic that is sent and received in your home goes through a Firewall and more specifically through “ports”. These are akin to doors, with each one dedicated to certain traffic types. It is always worth checking your Firewall settings in your router to make sure that you do not have any unnecessarily opened ports.
For tips on how to improve your home Wi-Fi Signal, check out the video below.
![]()
![]()
A new Chrome extension called KeyboardPrivacy injects delays into typing patterns, thwarting attempts to build biometric profiles of users for authentication.
Security researchers have created a practical privacy attack out of a well-known theory around user behaviour. The attack appears to defeat privacy measures such as Tor.
The post ‘Keystroke Biometrics’ exploit defeats Tor privacy appeared first on We Live Security.
![]()
Moonpig, the online personalised card company, has blocked the accounts of an unspecified number of customers after users’ details were published online.
The post Moonpig warns of password breach – but it may be more than their users who are at risk appeared first on We Live Security.
![]()
Hammertoss, a backdoor uncovered by researchers at FireEye, combines many previous communication venues used by APT29, a espionage outfit linked to the Russian government.
The National Security Agency says that once its legal authority to conduct Section 215 bulk telephone surveillance ends on Nov. 29, its analysts no longer will be allowed to access the database that holds all of the collected Section 215 records. In May, an appeals court ruled that bulk telephone metadata collection as performed by […]
When security experts warn us about sharing and publishing our location data, it’s easy to think that they are exaggerating the importance, and really what harm can come from “checking-in”?
I got a nasty shock this week when I found out about Google’s new Timeline feature which it launched last week.
Timeline will dot everywhere you’ve accessed Google Maps and plot it on a map. Mine, for example, looks a bit like this.

As you can see, a couple of trips around Europe but most dots are in and around London, where I live.
This alone is quite strange to see but it gets creepier. Click on any one of these dots and it opens your journey. Here for example, is my stroll around Barcelona at Mobile World Congress last year.
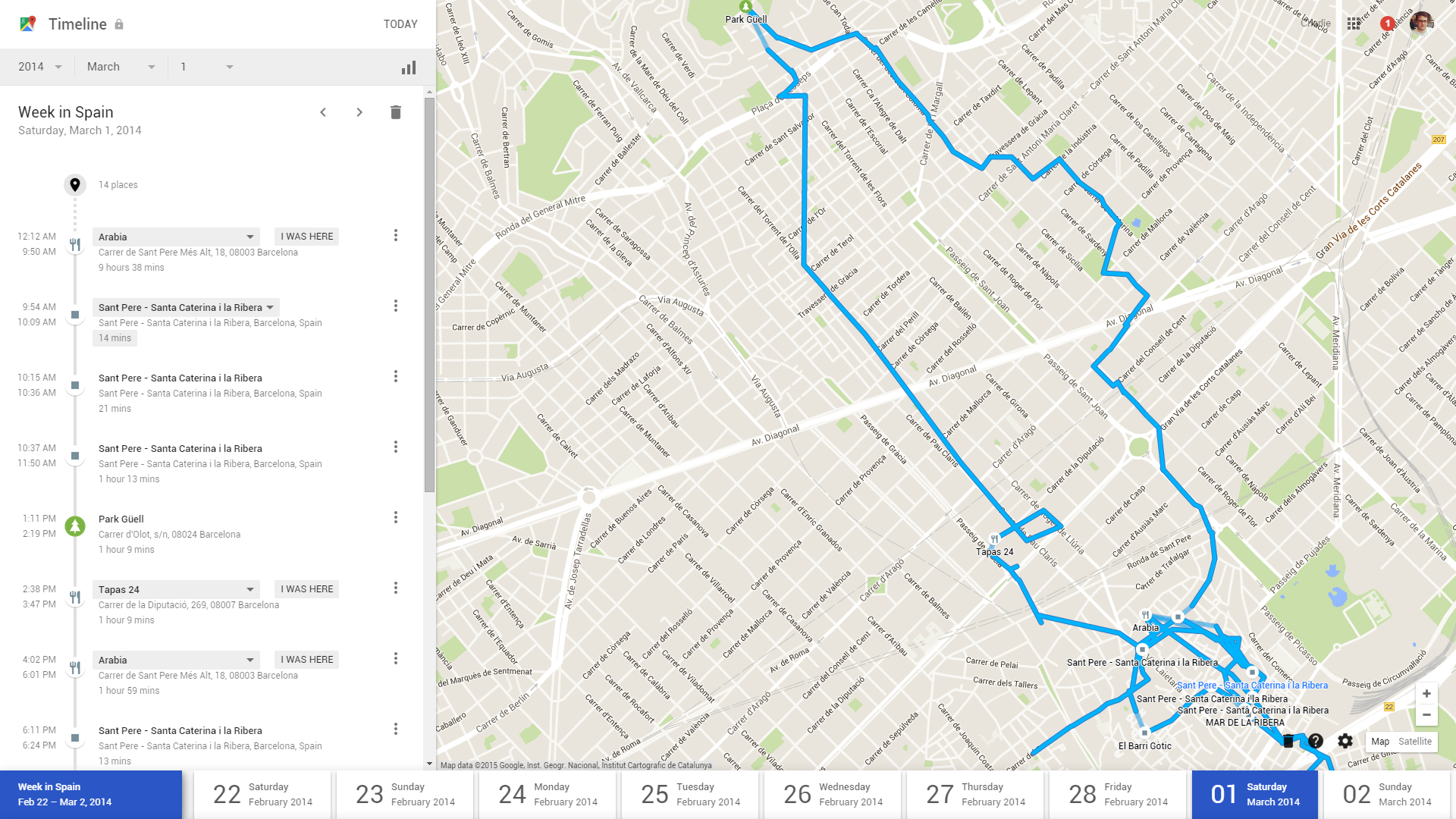
This is an exact map of where I went, which roads I took and how long I stayed at each location. Very surreal to see, given that I wasn’t even sure I was actively using my phone to navigate.
Google Timeline allows you to search for your location by date, so if I wanted to know everywhere I went in October 2013, or even on a specific day, I can find out.
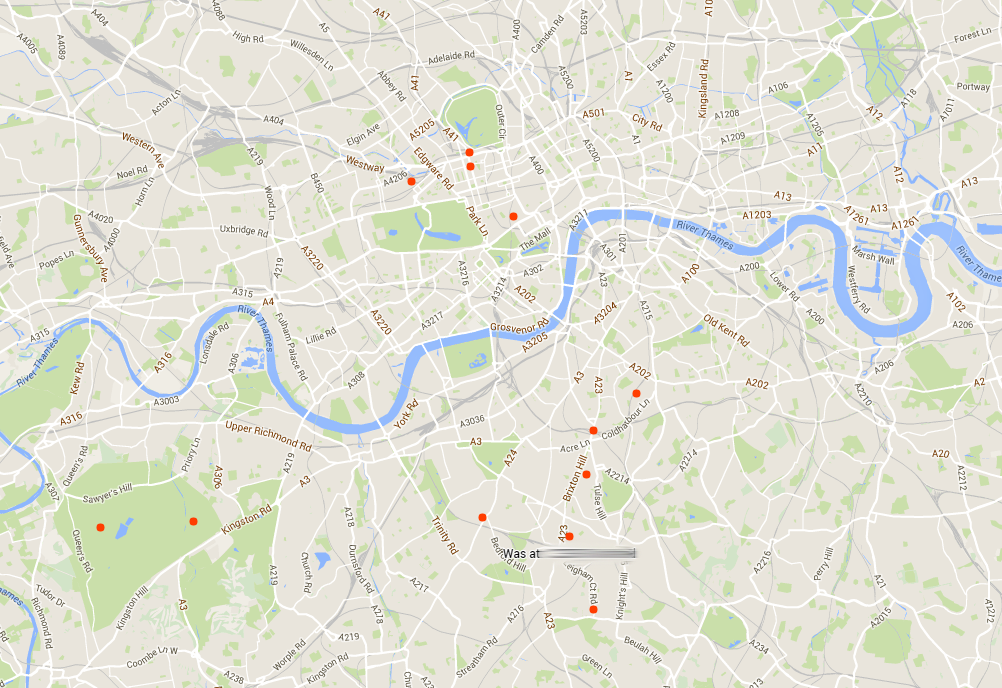
Google Timeline also arranges these journeys for me by calling them useful things like “Day Trip to Cambridge”.
This is a brand new feature and one that has certainly made me reconsider how much data I leave behind in my everyday life.
Naturally, all of this information is private and only visible to me, but I strongly suggest you access your own Google Timeline and see whether you are comfortable with what information is being stored.
Turning off your location tracking is simple. In Google Timeline, click the cog at the bottom right corner and select Pause Location History.
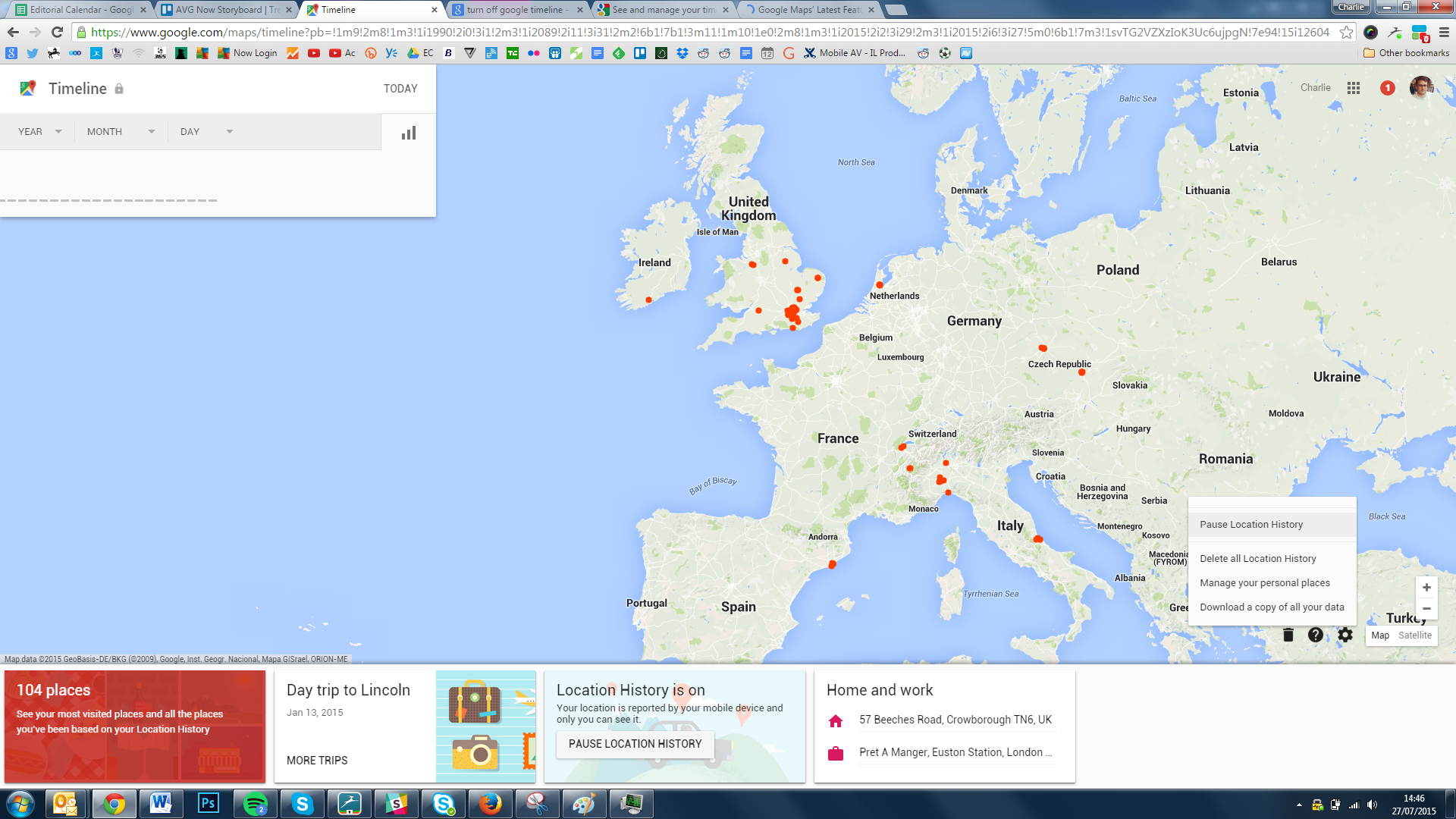
You’ll see the following message
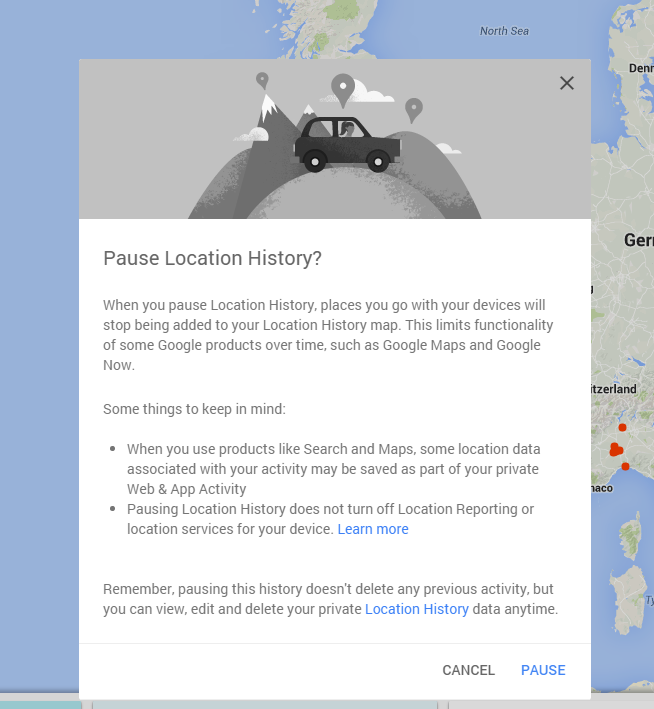
Click “Pause”.
Within the options, you can also delete all stored location history and even download your history.
![]()
![]()