Mike Mimoso and Chris Brook discuss the news of the week, including the latest Linux bug, Sony closing backdoors in cameras, and Google’s new open source fuzzer.
Tag Archives: Sony
Sony PlayStation Network offline for 12 hours
It feels like a deja-vu: The PlayStation Network was offline with a hacker group claiming responsibility.
The post Sony PlayStation Network offline for 12 hours appeared first on Avira Blog.
U.S. Sanctions North Korea Defense Agencies, Individuals in Sony Hack
President Obama signed an Executive Order sanctioning three North Korea defense agencies and 10 individuals for the country’s alleged role in the Sony hack.
XBox and PSN attacks were “marketing scheme†for Lizard Squad’s DDoS service
The attack which knocked the PlayStation Network (PSN) and Xbox Live offline over Christmas appears to have been a publicity stunt, designed to gain notoriety and draw attention to the hacking group which has claimed responsibility – Lizard Squad.
The post XBox and PSN attacks were “marketing scheme” for Lizard Squad’s DDoS service appeared first on We Live Security.
Hackers claim Christmas day outage of Sony PlayStation and Microsoft’s Xbox networks
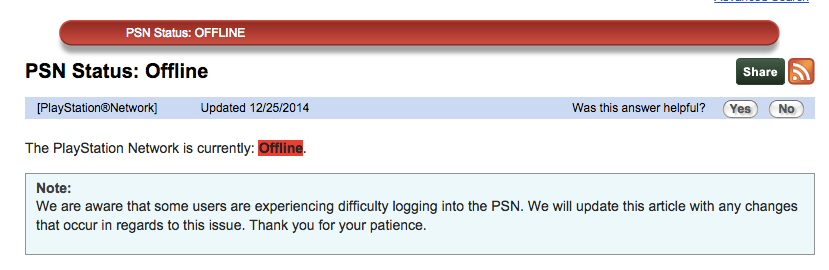 Earlier this month, as the Sony Entertainment breach was making headlines, Sony’s PlayStation Network (PSN) was knocked offline due to an alleged hacking attack. On Christmas morning, just as kids everywhere were unwrapping their new PlayStation and Xboxes, the PSN and Microsoft’s Xbox Live network were both disrupted leading to speculation that they were once again hacked. A group calling themselves Lizard Squad claiming responsibility for the attacks via Twitter.
Earlier this month, as the Sony Entertainment breach was making headlines, Sony’s PlayStation Network (PSN) was knocked offline due to an alleged hacking attack. On Christmas morning, just as kids everywhere were unwrapping their new PlayStation and Xboxes, the PSN and Microsoft’s Xbox Live network were both disrupted leading to speculation that they were once again hacked. A group calling themselves Lizard Squad claiming responsibility for the attacks via Twitter.
As of now, PlayStation is still offline and PSN is directing users to their @AskPlayStation Twitter account for updates.
Please follow @AskPlayStation to get the latest updates as we work to restore full network functionality.
— Ask PlayStation (@AskPlayStation) December 26, 2014
Xbox Live Status reports that its core services are running, but there is limited access to apps for IGN, Maxim, and MLG.tv.
Related article: Sony PlayStation Network down due to hacker attack
A Silver Lining in the Sony Hack Attack?
As the tale of Sony Entertainment’s victimization at the hands of cyber hackers continues to play out (with new twists in the plot revealed almost daily for the last month), it feels like ultimately there may be something positive to emerge from the unprecedented event for us as a society.
While unfortunately, it may have been at Sony’s expense, the Sony hack attack has made cyber security a top-of-mind issue for mainstream media, businesses and consumers.
(Full disclosure, Sony is a valued AVG partner.)
From the initial reports of hacked celebrity email revelations that first put the incident front and center – to a decision by Sony to pull (for now) the film “The Interview” – to unprecedented charges by the FBI of the involvement of a state-sponsored hacker (North Korea) and our U.S. president vowing a “proportional” response for the ‘cyber vandalism’ attack on Sony and our freedom of speech…to North Korea’s internet subsequently going down (as we publish this blog) without explanation on Dec. 22nd 2014. It has now been confirmed by Sony that there will be a limited release of the movie on Christmas Day.
This incident has been playing out like a plot to a thriller –with all of us watching and trying to identify the bad actors. Unfortunately, it really is reality TV.
But one of the impacts also has been well-deserved attention to the increasing concerns about cyber security – from personal to national.
Cyber security is, without doubt, one of the most serious issues of our time.
Clearly, in 2014 the issue of cyber security has moved from being perceived as a somewhat “wonky” IT issue, to one that average Americans are now concerned with. Unfortunately, it has taken the Sony episode along with a year of high-profile data breaches and hacking at other very high profile businesses (Target, Home Depot, JP Morgan Chase, among them) to bring the issue into the mainstream consciousness and concern.
As we close 2014, it feels like it has been the (unofficial) year of the hacker. But it has made people more appreciative of the need for digital security. For that much we can be thankful. And, perhaps it will prompt us all to make 2015 the year of digital security.
It makes me very proud of what we do here at AVG to contribute to making the digital world safer for everyone.
Title image courtesy of BBC
North Korea falls off the internet – is the United States to blame?
Barack Obama promises that the United States will respond to the Sony hack, and North Korea drops off the internet. Is there a connection?
The post North Korea falls off the internet – is the United States to blame? appeared first on We Live Security.
Avast revisits the biggest threats of 2014
2014 has been an active year for cybercrime. Let’s start with the most recent and then take a look at some of the other important security events of the year.
State-sponsored espionage
We are ending the year with the most publicized and destructive hack of a major global company by another country – now identified as North Korea. The Sony Entertainment attack, still being investigated by the FBI, resulted in the theft of 100 terabytes of confidential employee data, business documents, and unreleased films. It was an attack on privacy due to the theft of a massive amount of personal records, but also essentially blackmail; aiming to silence something that the North Korean government didn’t like – namely the release of The Interview, a movie depicting an assassination attempt on Kim Jong-Un.
Most of the blame for state-sponsored cybercrime in 2014 has been with Russian or Chinese hackers. Whether private or state-sponsored, these hackers have attempted to access secret information from the United States government, military, or large American companies. Recently, Chinese hackers sponsored by the military were indicted for economic espionage by the U.S. Department of Justice.
 Large data breaches
Large data breaches
Along with the Sony breach, other notable companies that suffered from cybercrime include Home Depot, eBay, Michaels, Staples, Sally Beauty Supply, and others. A significant number of these breaches were begun months or years ago, but were revealed or discovered in 2014.
Nearly 110 million records were stolen from Home Depot; the largest ever breach of a U.S retailer. The cyber-heist included 56 million payment card numbers and 53 million email addresses.
JPMorgan Chase’s data breach impacted nearly 80 million households in the U.S., as well as 7 million small- and medium-sized businesses. Cybercriminals were able to gain access after stealing an employee’s password, reminiscent of the Target breach from 2013. This breach is said to be one of the largest breaches of a financial institution. The FBI is still investigating.
Financial and data stealing malware
GameOver Zeus, called the most infamous malware ever created, infected millions of Internet users around the world and has stolen millions of dollars by retrieving online banking credentials from the infected systems.
Tinba Trojan banking malware uses a social engineering technique called spearfishing to target its victims. The spam campaign targeted Bank of America, ING Direct, and HSBC customers using scare tactics to get customers to download a Trojan which gathered personal information.
Chinese hackers were at it again, and again, targeting South Korean banking customers with banking malware using a VPN connection. The customers were sent to a look-alike webpage where they were unknowingly handing cybercrooks their banking passwords and login information.
Software vulnerabilities
Many of the breaches that occurred in 2014 were because of unpatched security holes in software that hackers took advantage of. The names we heard most often were Adobe Flash Player/Plugin, Apple Quicktime, Oracle Java Runtime, and Adobe Acrobat Reader.
Avast’s selection of security products have a feature called Software Updater which shows you an overview of all your outdated software applications, so you can keep them up to date and eliminate any security vulnerabilities.
 Numerous new exploits
Numerous new exploits
Flaws in software led to Shellshock and Heartbleed, two names that struck terror in IT administrator’s hearts.
Heartbleed takes advantage of a serious vulnerability in OpenSSL. It allows cybercrooks to steal encryption keys, usernames and passwords, financial data and other sensitive data they have no right to, and leaves no trace of the operation.
Shellshock ended up affecting more than half of the websites on the Internet. Hackers deployed malware on legitimate websites in order to retrieve confidential data from compromised computers.
Ransomware
Another name that made headlines was a group of malware dubbed ransomware, such as CryptoLocker, and its variants Cryptowall, Prison Locker, PowerLocker, and Zerolocker. The most widespread is Cryptolocker, which encrypts data on a computer and demands money from the victim in order to provide the decryption key.
Avast detects and protects its users from CryptoLocker and GameoverZeus. Make sure you back up important files on a regular basis to avoid losing them to ransomware.
Ransomware made its way from desktop to Android during the year, and Avast created a Ransomware Removal app to eliminate Android ransomware and unlocks encrypted files for free.
Privacy attacks
Mac users were shocked, celebrities mortified, and fans titillated by news of the iCloud hack which lead to the online publication of numerous private photos of Hollywood famous celebrities. The serious cloud breach was launched using brute force methods on targeted iCloud accounts.
Social engineering
The art of deception is a highly successful method for cybercrooks. The weakest link in security is the end-user, and hackers take advantage of us all the time using social engineering schemes.
In a phishing or spearphishing attack, hackers use email messages to trick people into providing sensitive information, click on links, or download malware. One of the most famous instances was the Target breach, in which hackers got a network password from a third party vendor that worked for Target, to get into the network and compromise their point-of-sale machines in November 2013.
Social media scams
Social channels, like Facebook, offer a perfect environment for social engineers. They can create buzz, grab users’ interest with shocking content, and encourage people to share the scams themselves. Scams often come in the form of fake video links which lead to surveys and rogue webpages.
Exploit kits for sale
The Avast Virus Lab observed increased activity of malware distributed through exploit kits this year. These kits, often for sale on the deep web, allow cybercrooks to develop customized malware threats in order to attack specific targets. Zeus source code was used to develop Gameover, and the Zeus Gameover network was used to download and install Cryptolocker.
Avast Software’s security applications for PC, Mac, and Android are trusted by more than 200-million people and businesses. Please follow us on Facebook, Twitter and Google+.
Dave Aitel on the Sony Hack
Dennis Fisher and security expert Dave Aitel discuss the Sony hack and why it makes sense for North Korea to be responsible for it.
New Version of Destover Malware Signed by Stolen Sony Certificate
Researchers have discovered a new version of the Destover malware that was used in the recent Sony Pictures Entertainment breaches, and in an ironic twist, the sample is signed by a legitimate certificate stolen from Sony. The new sample is essentially identical to an earlier version of Destover that was not signed. Destover has been used […]