It’s European #DataProtection day! Every day we visit websites and willingly hand over our name, address, and credit card number. Have you ever thought about what happens to that data or what your rights are?
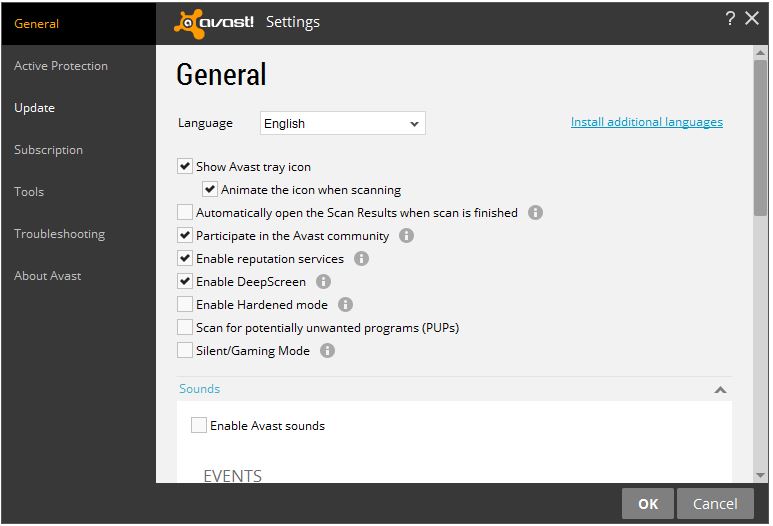
Avast keeps your personal data private.
Members of the European Union (EU) enjoy a high standard of protection of their personal data. The Digital Agenda for Europe lays it all out for you on their website. Here’s a summary:
The burden to protect you is on organizations
The EU Data Protection Directive ensures that personal data can only be gathered under strict conditions and for legitimate purposes. Organizations that collect and manage your personal information must also protect it from misuse and respect certain rights. One of the objectives is that organizations notify their customers, in plain language, what information is collected and how it is used as well as get permission before using any personal information.
One of the stumbling blocks has been the so-called one-stop-shop for businesses and citizens in each member state in which authorities will handle citizens’ complaints about any breach of the rules. There are just as many ideas on how to run it as there are EU member states.
You must be notified of cookies and data breaches
The Directive on Privacy and Electronic communications (ePrivacy Directive) ensures that all communications over public networks maintain a high level of privacy. For example, this directive requires website owners marketing online to EU citizens to obtain consent from users, via some kind of opt-in, before implementing cookies or other technologies to capture online visitor information. (See below for information on managing your cookies.)
If your data is stolen, the ePrivacy Directive states that you should be notified. That’s good because data theft can result in identity theft or fraud, damage to your reputation, loss of control over your personal data or a loss of confidentiality.
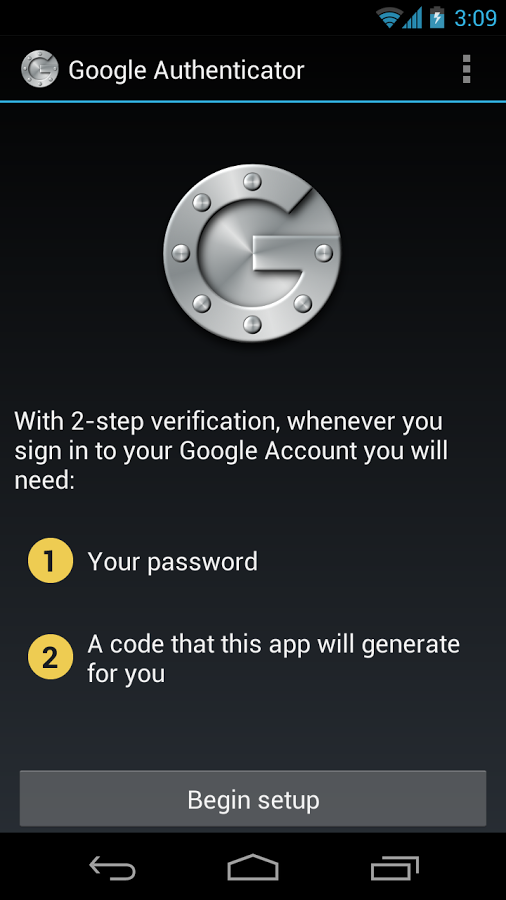
However, this fall, the rules changed slightly and now businesses don’t have to notify consumers that their personal data has been lost or stolen if the data has been encrypted. The ministers figure that the business has “appropriate technological protection measures” to protect the data that has been lost or stolen from being accessed by people not authorized to see it.
Viewing and managing your cookies
For those of you not familiar with the term, cookies are small files stored in your browser that contain information about your visit to a web page. They help tailor your online shopping experiences by doing things such as recording items in your shopping cart, they also recommend products based on your interests, allow auto-log in and compile browsing histories.
In most modern browsers, you can control cookie settings. The options include viewing stored cookies, controlling which sites you accept cookies from, and setting how long they may be stored and used.
Chrome
- 1. Open the drop-down menu in the top right corner of the Chrome browser, select Settings.
- 2. At the bottom of the page, click Show advanced settings.
- 3. In the Privacy section, open the button that says Content settings.
- 4. Under Cookies, you check or uncheck the options to manage the settings.
- 5. To see individual cookies, click All cookies and site data.
- 6. To remove cookies, hover the mouse over the entry. Click the X to delete.
- 7. To delete all cookies, click Remove all.
Firefox
For instructions to clear cookies in Firefox, please visit Mozilla’s support page.
Chrome
For instructions on clearing and managing cookies in Internet Explorer, please search Microsoft help for your version of IE. Here’s general information.