Last year is proof that stories about Kim Kardashian and Pikotaro’s PPAP song were not the only things able to break the internet, 2016 was a year full of news about data breaches, stolen sensitive information, hackers extortion and DDoS attacks that in some cases had a significant impact on the lives of many Americans. Phew, it’s all gone, and we are already in 2017!
Hopefully, reputable tech giants such as LinkedIn, Verizon, Google and Microsoft will be a bit more vigilant about keeping our sensitive information safe. Luckily there are anti-virus companies who have our backs even when tech companies’ security fail.
Having anti-virus software is similar to having a second layer of clothes in the winter. You like being prepared, don’t you?
After such a turbulent 2016, we’ve developed a little list of cyber threats to watch out for in 2017.
Cyber threats to watch out for in 2017
Connected devices
Currently, there are billions of connected devices all over the world – the revolution of self-driving cars is just about to kick in too. Drones, doorbells, kitchen appliances, thermostats and health gadgets – all sorts of new technology is now able to be monitored and controlled over the internet. The power of IoT gives us an unparalleled convenience, things we’ve never experienced before, but also poses a grave danger.
The potential threat is no longer about getting your fridge or printer hacked, but cracks in the system of such technology which if penetrated by criminals could cause significant security risks. No one would want a self-driving car or a drone hacked and operated by hackers.
This poses a great concern for our safety. We are expecting a wild 2017 for the consumers out there, as more attacks throughout the year are likely to follow. Currently, it is easier for cyber trouble-makers to create and control an IoT army of devices, than to develop new spyware. We hope to see the security features of IoT devices advance in 2017.
Sophisticated phishing attacks
It’s just the beginning of the New Year, and multiple sources have reported innovative and more sophisticated phishing attacks targeting Gmail accounts in the US. Sources say these phishing attacks can fool even experienced internet users. What is so different about these phishing attaches from the regular ones?
Not much, except for the fact that the design of the landing pages is getting better and better. Another difference worth mentioning is the URL bar. Anti-virus software companies have been preaching for years to always look at the URL bar and never input your login details in websites of whose URLs are not https or/and marked in red color.
In the new case of phishing attacks, the URL bar is in plain text, its’ not green nor red. Apparently, this tends to confuse people so be aware if you don’t want to be in the news as the next victim of a well-executed scam.
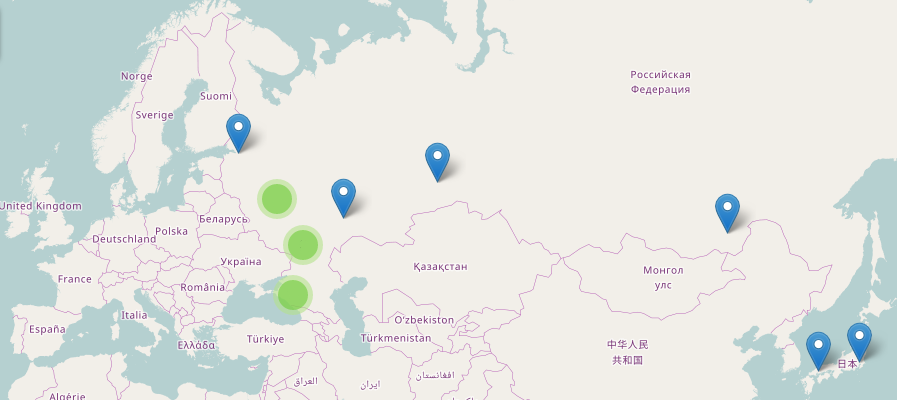
State-sponsored espionage
The New Year will surely bring us news of state-sponsored cyber espionage. Mainstream media still finds it hard to accept the legitimacy of the new president of the United States, and the means he used to make it to the chief commander of the free world role. WikiLeaks founder Julian Assange argued that the emails which revealed information about Secretary Hillary Clinton were part of a leak, not a state-sponsored campaign designed to elect Donald Trump. We will most likely never know the full truth but what we are aware is that state sponsored cyber-attacks will become a norm in 2017.
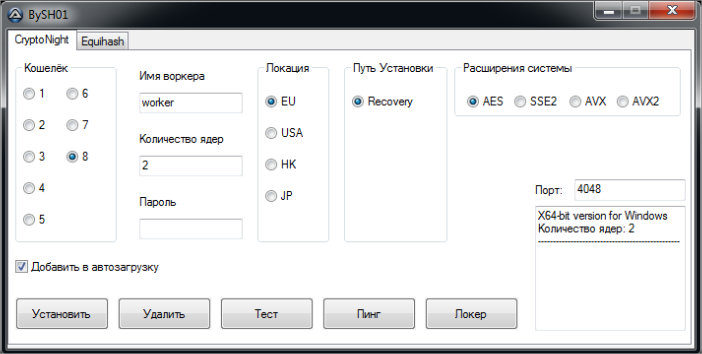
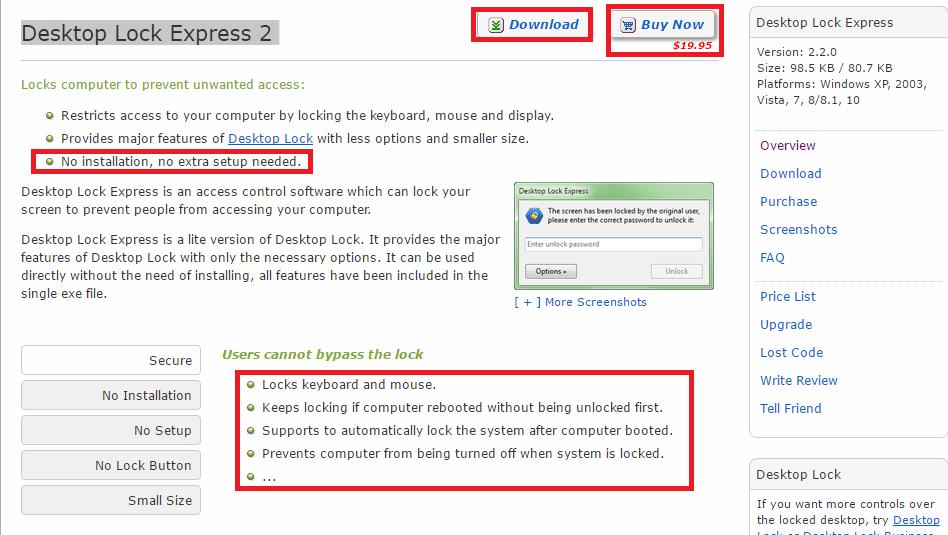
Hacker extortion
Last year a California hospital paid $17,000 in Bitcoin to hackers, a well-known university in the US also became a victim of an attack where cyber criminals installed ransomware on the company’s systems and demanded payment to unlock it. In all known hacker extortion cases, the victim ended up paying up the criminals. The main problem is that not only companies are under threat, but individuals too. There have been reported cases of senior citizens who have been held up by cyber bullies, demanding payments so they can regain access to precious family imagery. Or celebrities ending up paying to stop sensitive photos from being released into the world. Having in mind that most of all known occurrences of cyber extortion have been successful, and the fact that governments tend to lose the battles against it, the occurrences of such incidents are very likely to continue into this year.
Digital fingerprinting, biometric security and health data protection
Digital fingerprinting is getting popular among consumer devices. We saw tens and probably hundreds of them at CES 2017. Currently, all major cell phone manufacturers have it as an option to unlock their phones. Now there are home locks, padlocks, deadbolts and USB sticks that could be unlocked/opened with a simple touch. Even some car manufacturers are integrating the technology into their new car models. Sadly, a Japanese researcher recently came out with a statement that your fingerprints could be stolen when posing for a photo doing the piece sign. Criminals are getting creative, what a surprise! Facial and iris recognition may soon become a norm too so protecting the databases that store this information will become a challenge.
What an amazing time to be alive, the predictions for 2017 are straight out of a sci-fi movie.
However, these issues are now real and protecting our data in all its forms is vital. The convenience the new technology is bringing us opens backdoors for criminals to take advantage. Luckily there are anti-virus specialists such as Panda Security, who make sure your data stays safe and provide you with that extra layer of security that we all need.
The post Top Cyber Risks of 2017 appeared first on Panda Security Mediacenter.