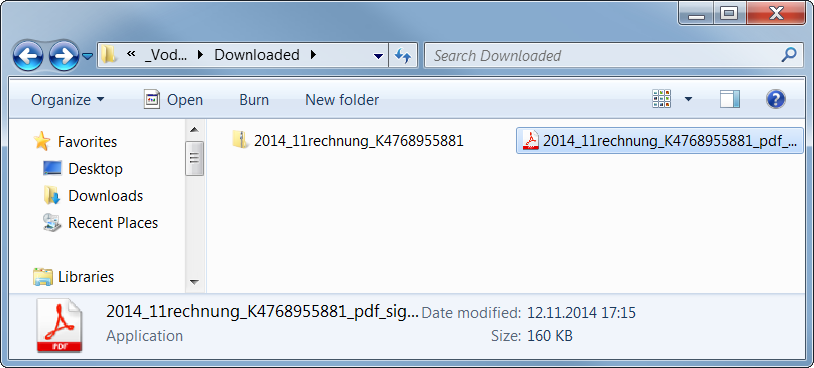
The author of this sample used steganography because 99% bytes of the image content represents an encrypted code. This code is decrypted first and the control is passed to this decrypted code.
Furthermore, WinAPI functions are called indirectly (via functions
LoadModule()
and
GetProcAddress()
) and names of these functions are obfuscated and decoded during run-time on the application’s stack in order to make analysis more difficult.
Afterwards, it creates a new process with the same name and fills its sections with the decrypted code from the GIF image (via the
WriteProcessMemory()
function).
This new process copies the original file into
C:Users%USERNAME%AppDataRoamingIdentitiesqwrhwyyy.exe
(as a read-only system file), registers itself to be run at system startup (registry key
HKCUSoftwareMicrosoftWindowsCurrentVersionRun
), and deletes the original file by using a generated batch file.
Once the file is executed from this new location, it behaves differently:
It checks whether it is analyzed or virtualized via the following techniques.
Afterwards, it extracts and decrypts another executable file on stack from the aforementioned GIF image and injects it into other processes, such as
explorer.exe
,
firefox.exe
. This starts the second stage of infection. Note: some versions of this malware try also to check a working Internet connection via a DnsQuery of www.microsoft.com before starting the second stage.
Second Stage
This extracted file is relatively small (52 kB) because it is packed by the UPX packer (version 3.08).
After its run-time unpacking, it uses the same anti-debugging tricks as the previous sample.
The main body of this file can be described by the following decompiled code:
CreateMutexA(0, 1, mutexName); // "qazwsxedc"
Sleep(1800000); // wait for 30 minutes
WSAStartup(0x202, &WSAData); // initiate Winsock
seconds = getLocalTimeInSeconds(0);
if (GetTickCount() < 1920000 /* 32 minutes after startup */ &&
GetTickCount() > 1000) {
while (1) {
malicious(); // the main functionality
gStateInactive = 1;
Sleep(300000); // wait for 5 minutes
}
}
- For synchronization between the first and second stage, the mutex
qazwsxedc
is used (e.g. another variation of classical
qwert
or
asdfg
names).
- Afterwards, the malware waits for 30 minutes to remain stealthy. After that, it also checks whether no more than 32 minutes have passed since the system startup (i.e. whether it was started during the first two minutes after startup).
- In its main loop, it follows the malicious behavior described in the remaining paragraphs (function
malicious()
). After each iteration, it makes a 5 minutes break before the next action.
In this function, the string
DC85CCC4C4CCC7CED385C6CE919F9F98
is decrypted at first by using the fixed XOR key
0xAB
. The resulting string
w.googlex.me:443
represents a remote address of the command-and-control (C&C) host and its port. The second one is
m.googlex.me:53
. At first, the sample tries to check connection with these servers by using the Winsock functions. The other samples contain different lists of C&C servers:
ahokcjidanptacyu.eu
gctrbwqyxxyamcnn.eu
ggcrguelfhvtuxdb.eu
gkkelsrkypraqhto.eu
gunvpvqhnwxxgjsn.eu
gvlmoefoqapvrvec.eu
mcfpeqbotiwxfxqu.eu
...
Afterwards, it obtains information about the local computer, such as:
- computer name;
- version of operating system;
- processor information and number of cores;
- memory information.
English (United States) // local settings
TEST-PC // PC name
Windows 7 Professional // Windows version
4096 MB // memory
Intel(R) Xeon(R) CPU E5-1620 v2 @ 3.70GHz | CORE 8 // CPU
2014-10 // malware version
Afterwards, this information is encrypted and send as a registration to a C&C server from the aforementioned list. The reply from the server is encrypted by the same algorithm. The very first byte of the reply message specifies an action (i.e. a control code) to be performed. To date, we have identified the following codes:
GET %FILE% HTTP/1.1
Accept: image/gif, image/x-xbitmap, image/jpeg, image/pjpeg, application/x-shockwave-flash, application/vnd.ms-excel, application/vnd.ms-powerpoint, application/msword, */*
Accept-Language: en-us
Accept-Encoding: gzip, deflate
User-Agent:Mozilla/4.0 (compatible; MSIE %VERSION%.0; Windows NT %VERSION%.1; SV1)
Host: %HOST%:%PORT%
Connection: Keep-Alive
GET %FILE% HTTP/1.1
Content-Type: text/html
Host: %HOST%
Accept: text/html, */*
User-Agent:Mozilla/5.0 (X11; U; Linux i686; en-US; re:1.4.0) Gecko/20080808 Firefox/%VERSION%.0
GET %FILE% HTTP/1.1
Referer: http://%ADDR%:80/http://%ADDR%
Host: %HOST%
Connection: Close
Cache-Control : no-cache
GET %FILE% HTTP/1.1
Content-Type: text/html
Host: %HOST%
Accept: text/html, */*
User-Agent:Mozilla/4.0 (compatible; MSIE %d.00; Windows NT %d.0; MyIE 3.01)
Those actions are constantly executed until the process is terminated by the C&C server (unlikely) or by user (e.g. system shutdown). However, this process is started once again during the system startup.
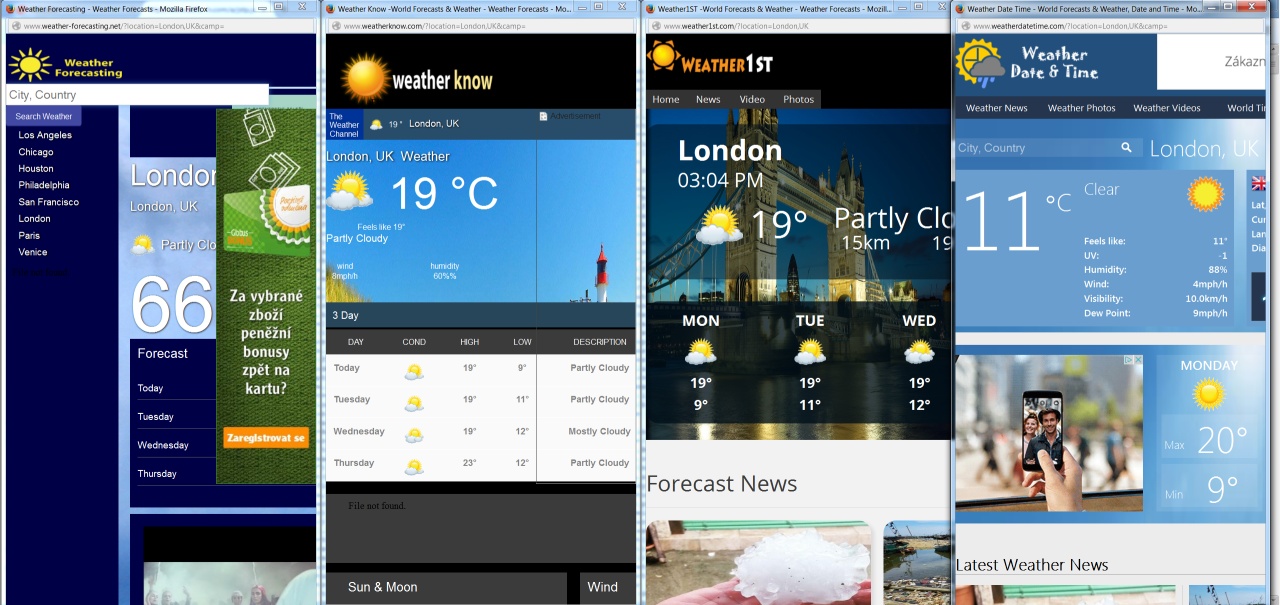
As we can see, it is up to the attacker to download and execute other malicious modules, such as password stealers, bankers, or to include the infected PC into a botnet.
Conclusion
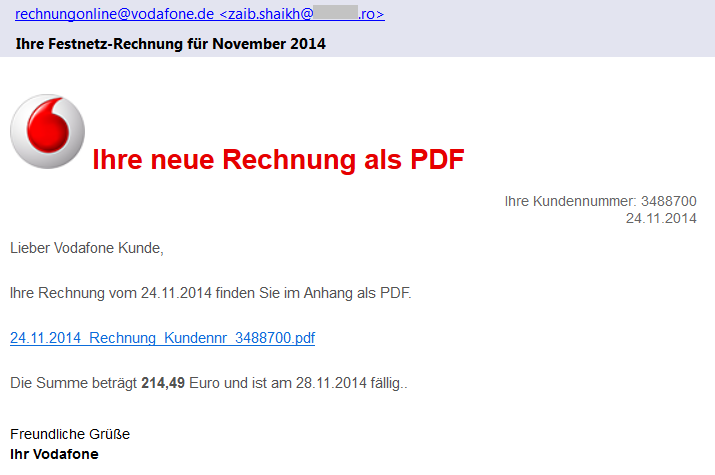
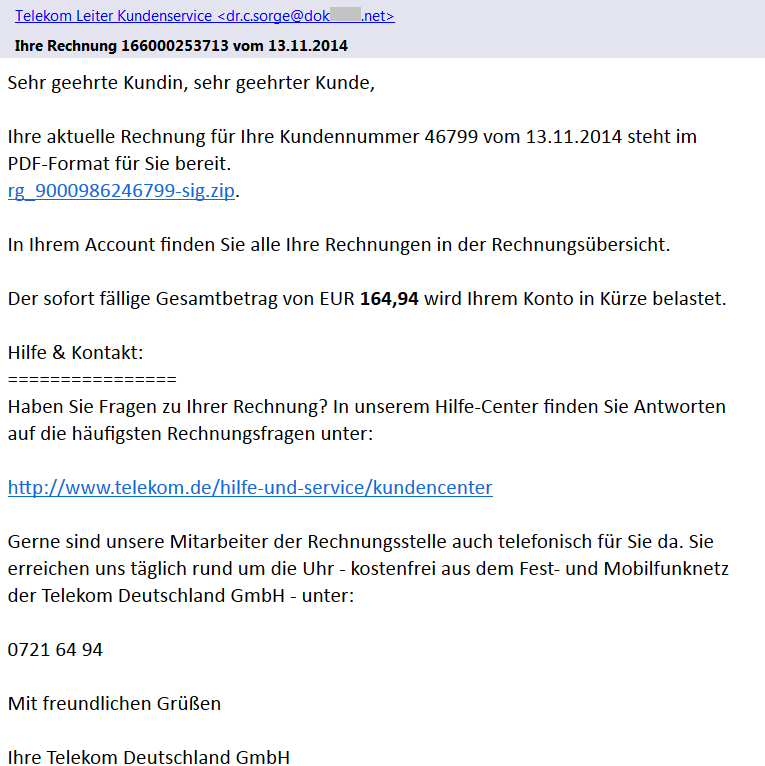
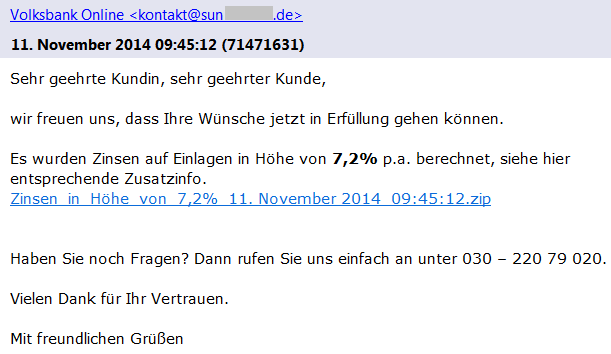
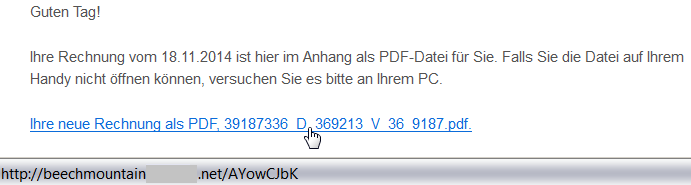
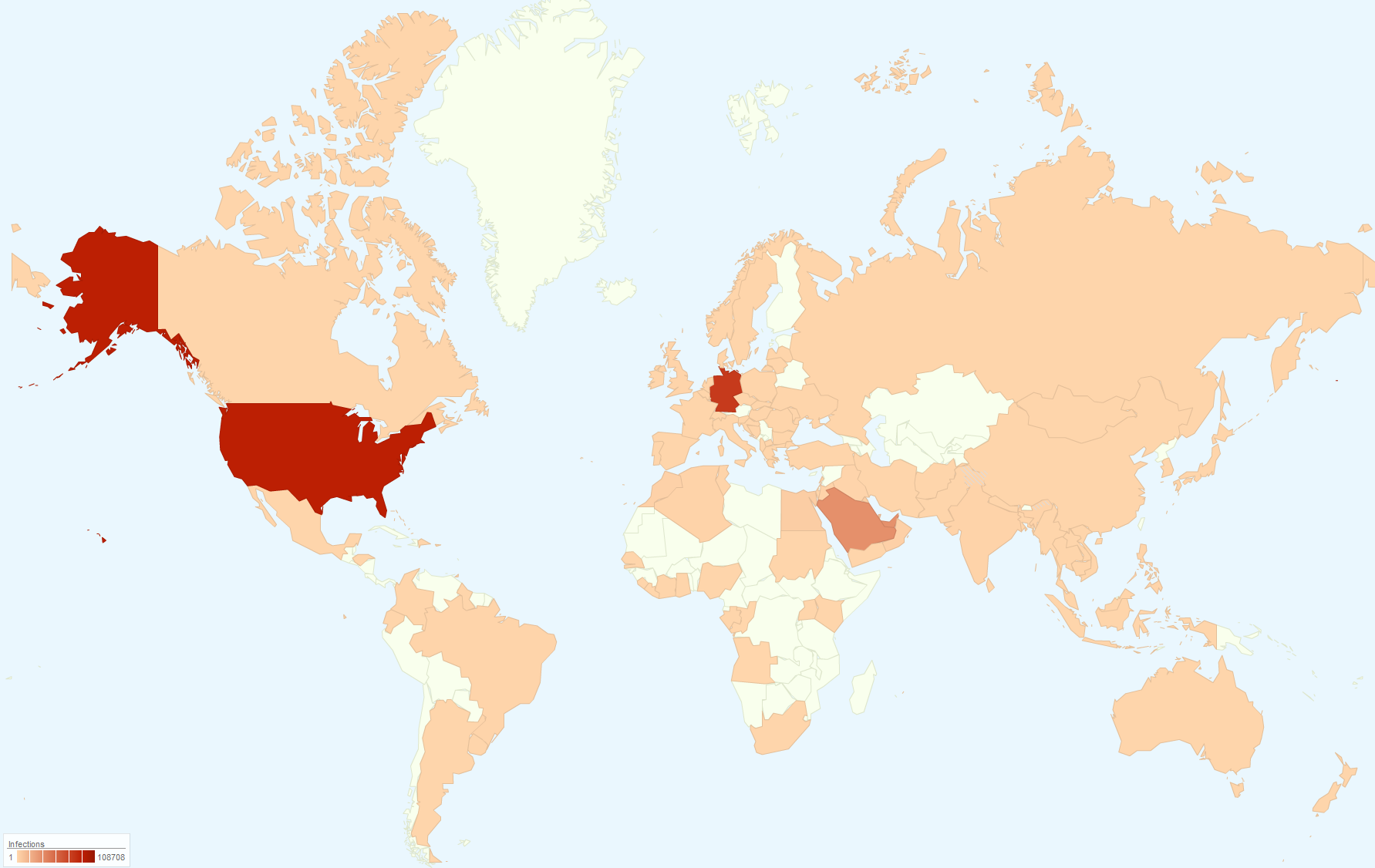
Although, the analyzed phishing emails are far from perfect (download links and sender addresses are suspicious, the text of email is only available in German, etc.), it is still possible to fool a user into executing the malicious file. This file is powerful enough to infect the user’s machine and turn it into an unsafe place.
Here are some basic tips, that we’ve previously shared about how to detect a phishing email:
- Check the spelling and grammar – it is unlikely that your bank or service provider will send you an email with such mistakes.
- Sender’s name and email address can be spoofed, do not rely on them.
- Look at the target address of the link – different domains than the official ones are highly suspicious.
- Do not panic and do not do any action in haste. The attacker often tries to threaten you and make a time pressure on you.
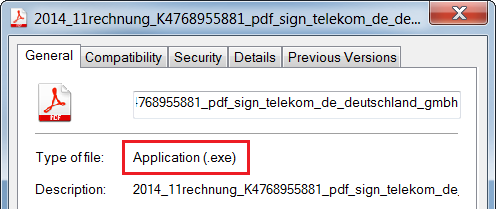
- Do not open suspicious attachments or links. If you really need to open a file, check its file type before double-clicking it. The file name and icon can be easily crafted to look like a picture or document.
- If you are not sure about the email’s origin, try to contact that company directly (e.g. call official customer care), but do not respond to such email and never ever send your credentials in this way.
- And as always: use AVG to stay protected.



![]()
![]()