More than one million consumer web-connected video cameras and DVRs are compromised by bot herders who use the devices for DDoS attacks, researchers say.
Tag Archives: Videos
Trey Ford on Mapping the Internet with Project Sonar
Trey Ford from Project Sonar describes the group’s initiative at Kaspersky’s Security Analyst Summit. The Rapid 7 service scans public-facing networks for apps, software, and hardware, then analyzes that cache of information to gain insight to trends and common vulnerabilities.
Internet of Things is web’s next money spinner say small businesses
We all suspected it and now we know it to be true. Most small businesses (57 percent) are expecting the Internet of Things (IoT) – IP-connected devices, machines with sensors and cloud-based services – to make a significant impact on their bottom line. Yet almost three quarters (71 percent) admit they are not ready from an IT security and data protection point of view.
These are just two of the key findings in AVG’s latest independent research which polled 1,770 small businesses and MSPs in the United States, Canada, the United Kingdom, Germany and Australia on a number of issues related to monetizing IoT. Over half (55 percent) of MSPs taking part in the study confirmed that customers are demanding IoT-related services and 77 percent are planning to expand their service or product portfolio to meet it. Little surprise then that only 18 percent of the small businesses we spoke to thought their IT provider was ahead of the curve when it came to their capacity to manage IoT.
So just what is IoT’s potential as a money spinner? Well, more and more devices with built-in sensors are being connected to the Internet. By remotely monitoring the data on these devices a business can achieve much greater all-round efficiency through raised productivity, lower costs and reduced wastage. And as cloud services become the default way to make sense of this data you no longer need heavy up-front investment so IoT starts to become affordable for small businesses.
Our research highlighted four industries in particular – IT/telecoms, pharmaceuticals, utilities and manufacturing – that are set to make money from IoT. The IT/telecoms industry, as might be expected, is especially upbeat on IoT. Among the IT decision makers surveyed 84 percent indicate that their organization would shift its product/service offering to make the most out of the rise of IoT. The proportion of pharmaceuticals companies looking to expand product offerings using IoT was even greater (91 percent).  Three quarters (75 percent) of utilities companies and 73 percent of manufacturers are also expecting to benefit.
Overall our study found the vibe from small businesses around IoT to be extremely positive. If there was one note of caution it was the recognition that they need to do more about the security side of things. They are right to be cautious. Many connected devices use the Linux operating system which has its own set of vulnerabilities as highlighted by the recent Shellshock event. The lesson for companies is that they need to approach IoT just like the rest of their IT – by keeping them regularly updated and using identity management and user authentication.
A summary of the other key findings in the study were:
- Almost half (46 percent) of SMBs think that the Internet of Things will be the IT trend that has the greatest impact on their organization over the next five years.
- Around three fifths (62 percent) of SMB respondents report that their organization has budget specifically assigned over the next 12 months for the development of Internet of Things solutions. 49 percent have a moderate or substantial budget assigned for these solutions.
- Only 18 percent of SMB respondents say that their IT provider is completely ahead of the curve with regard to the Internet of Things and the potential for their business. Of those with an IT provider, 68 percent feel that their provider could improve their service with regard to Internet of Things offerings and understanding.
- The majority (84 percent) of SMB respondents say that their organization has purchased mobile devices within the last year, spending an average of over $6,500 on these devices. Of those who have purchased mobile devices within the last 12 months, SMB respondents estimate that their organization spends an average of around $4,500 in hidden costs annually.
In conclusion, the days when work was confined to an office with four walls and a locked door are gone for good. Thanks to mobile technology and popular cloud-based applications today’s start-ups are already living in a world where doing business without walls is perfectly normal. IoT is a further example of how small businesses are becoming more and more connected. The flexibility and simplicity is great. But is it secure? AVG is ready to help businesses embrace IoT safely. A couple of weeks ago we announced that we will shortly expand AVG CloudCare’s capabilities to include breakthrough integration of Multi Factor Authentication, Secure Sign-On (SSO), Mobile Device Management and Mobile Application Management all managed through Active Directory to ease complexity and simplify management.
![]()
![]()
Get rid of clutter from your Android devices now!
We all have way too much unnecessary clutter on our phones and tablets – things that eat away our storage, waste mobile data and drain battery life. Some of this is caused by the apps we use on a daily basis, like games or social media– but much is also caused by apps we no longer use or that are running constantly in the background.

Our new AVG Cleaner for Android 2.2 makes it quick and easy to identify (and remove) such unwanted apps but also helps you clean the clutter from your phone, such as cache, history, and call logs.
So what’s New in Version 2.2?
- Large file finder: Our all-new version 2.2 app scans your Android tablet and phone for massive files, such as downloads, app packages, videos, music files or other data that you may have downloaded or copied over to your device – and perhaps forgotten about.
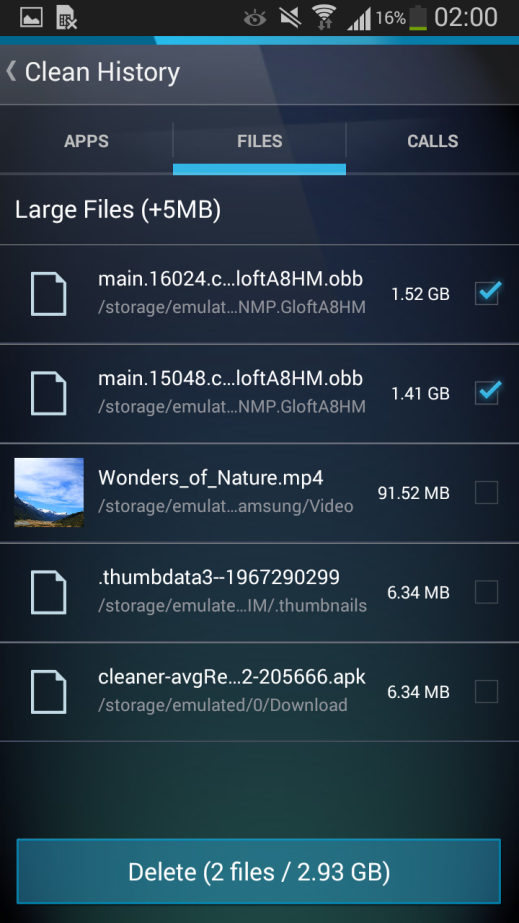
- Caller History Cleaner: AVG Cleaner for Android helps you clean up all calls or even one specific entry in your call history.
- Check up on your Android from your PC: You can remotely check up on your Android smartphone or tablet from your PC. In this example, I added a Galaxy S5 to my AVG Zen network and monitored it right from my PC.

Now the really cool thing is that you can’t just check up on your AVG Zen network from your PC – but also direct from your Android. That’s right, you can even check up the Performance and the Security status of all your AVG Zen connected devices, such as PCs or Laptops running Windows and Mac computers right from your phone. To do that, fire up your Google Play store and download AVG Zen Admin console:
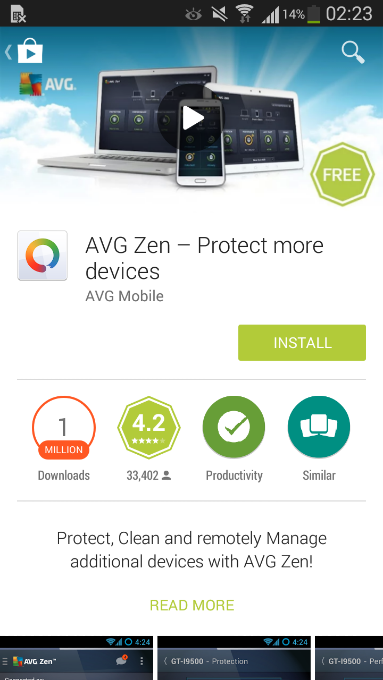
Once you’ve signed into your AVG Zen account, you can even check up on your devices from wherever you are!
Â
![]()
![]()
Protection for your family, plain and simple
Sadly, the hassle of managing the family technology is only going to get greater. The number of connected devices in our homes is growing rapidly. In 2013, the average home already had more than five connected devices. Homes like mine, with more than 20 devices, are driving this average up with every passing day.
As we start to realize that our families are spending so much time online, it is our responsibility as parents to ensure that they are doing so safely. Then the long to-do list of Internet safety comes into focus.
Our tablet has run out of space? Has my son set his privacy setting correctly on social media accounts? Is the security software on my own phone updated? What can I do to speed up my wife’s laptop?
As our list of devices continues to grow, so too does the to-do list of the family tech wiz.
There must be a simpler way to manage my family’s devices without having to actually track down each device every time I want to do something.
That’s why for 2015, AVG is launching AVG Protection: the one-stop solution to help me keep my family protected across all our devices—no matter how many—wherever we are.
AVG Protection brings together our best security products for all platforms: AVG Internet Security for Windows desktop, laptops and tablets; AVG AntiVirus for Android smartphones and tablets; and AVG AntiVirus for Mac under a single subscription. Add to this AVG PrivacyFix and AVG Cleaner for Mac and Android, which are free, to complete my protection, performance and privacy needs — the solution is a compelling one.
But most importantly, AVG Protection has AVG Zen to tie them all together. AVG Zen allows me to manage all of our devices from one screen, fix issues, scan machines, and enable protection remotely from my PC or my Android device when mobile. And the alerting system lets me know when something needs my attention so I can rest assured my family is safe online. The days of checking up on each of my direct family or my extended family devices one by one are over.
It couldn’t be easier to start protecting your family using AVG Protection, click here to get started.
![]()
![]()
Thoughts on Mobile Digital Parenting
Dear Abby: My birthday is in 26 days…And I really want an iPod Touch for school. I’m in the fifth grade and everyone in my class has an iPod Touch, iPad or iPhone. EXCEPT ME!
Desperate Girl in North Carolina
This was a real letter sent recently to the venerable U.S. newspaper advice columnist Dear Abby. In her response to the 10-year-old, Abby wisely advised the “desperate†girl of some of the possible reasons for her parents’ opposition (among them, the ability to afford a device) and then encouraged the girl to talk with her parents about their concerns and how they could address them.
Digital-age parenting means there is a lot to consider about if and when is the right time for a child to get their own cell phone or other digital devices. Depending on the research you look at, between 56% (CTIA) and 30% (Kaiser) of children aged 8-12 have cell phones. In most cases, the research is a few years old – which means the percentage is likely to be much larger.
On the “pro†side a cellphone can be a great device to keep you connected to and keep track of your kids. On the “con†side, it also connects your kids more readily to the vast and not-always-friendly online world of social media, videos, games, movies, music, and TV shows and more.  Online safety and protection for our kids is a paramount concern.
In research we conducted earlier this year, 42% of parents said they worry that their child is spending too much time online. They are also unsure of what their kids are exposed to and many are uncertain as to how to keep them safe.
If your child is ready for a mobile phone, it’s important to educate them and have rules. Here are a few suggestions, starting with some rules:
House Rules
- Consider a basic phone as a starter phone. Turn off extras if you are passing down an older model phone.
- Set limits. Such as: Designated times the phone can be used. Number of minutes that can be used. Caps on number of texts that can be sent.
- Block internet access and calls from unapproved numbers.
Some Do’s and Don’ts
- Just as in the real world – never talk to strangers. Never respond to messages, emails, and texts from people they don’t know.
- Always tell an adult if they receive any hurtful messages online… or requests from online friends to meet offline
In addition to our online and mobile security software, we’ve attempted to help parents by giving them other tools to address online safety. We’ve collaborated with the international children’s safety organization, Childnet, to create a guide to online and mobile phone safety starting at an early age, with our new Magda and Mo eBook series …The series, developed from a child’s eyes, using a series of click-and-tell stories that parents can use to help educate and foster dialogue with their kids about online safety.
![]()
![]()
The truth behind Snapchat “hackâ€
Well, it’s happened again. Another security breach, more embarrassing photos and films leaked all over the Web. Throw in privacy issues and possible child pornography charges and Cyber Security Awareness Month is getting off to a really bad start…or at least, to put a more positive spin on it, hopefully making people more aware.
“Snappening,†as its been called, which was revealed over the past weekend, is a breach involving users of a web site called SnapSaved.com and consists of approx. 90,000 photo’s and 9,000 videos  shared by as many as 200,000 Snapchat users.
SnapSaved.com, as you can probably tell by the description is a web service that allowed users to covertly save incoming message. The service did this by using your login credentials to access Snapchat’s servers and then store the images permanently on the SnapSaved servers.
Hackers managed to access the SnapSaved.com web site and steal the content that users had been storing there. While most of the content is reported to be of every day life there is of course some content that is more personal and inappropriate for viewing by anyone that it was not specifically meant for.
It’s important to understand that the hack was not on Snapchat’s servers.
It’s important to understand that the hack was not on Snapchat’s servers. Snapchat has built a growing and loyal user base on the promise that anything sent over its network disappears after a set period of time, typically a matter of seconds. This obviously promotes users sending material they would not send over other services and can possibly lead to people being a little more daring than they should be. You can read Snapchat’s reaction to these issues here.
The breach brings home the message that whatever you post online may well end up online forever and could be seen by people that it was not intended for. In fact recently we highlighted the potential issues that Snapchat users may have if someone decides to take a copy of something that was not intended to live beyond a few seconds. You can view the video for this here.
Here are some quick steps you can take:
- Consider which third-party apps you and your family use. Clearly many of these apps have more vulnerability and less oversight than the actual services themselves. For the two bigger services, Facebook and Twitter, you can check: With Twitter, click on your profile image and select “Settings” and “Apps” to revoke access to applications you no longer use or do not trust. And for Facebook, in a browser, click the lock icon on the upper right corner and do a “Privacy Checkup” to review “Your Apps”. AVG PrivacyFix allows easy access to the privacy settings of major networks, you can download it here.
- Review your Security Settings on all your programs. Consider who you are sharing information with, and who has access. Do you know whom your child has friended? Clearly there are trust and privacy issues here as well between you and your loved ones, but a healthy discussion is certainly not a step over the line.
- Consider what content is being shared. It’s a matter of education that this content could be made public and may have value to hackers. This can be discussed with children in the same way you might discuss the danger in posting vacation plans or financial info.
We all need to be more vigilant in keeping our families, our businesses and ourselves safe and cyber-secure. And some the best tools we have are education, communication, and awareness.
![]()
![]()
