Tuesday’s impending deadline ending security support for Internet Explorer 8, 9 and 10 is putting companies on notices about moving off older versions of the browser.
Tag Archives: Internet Explorer
Threatpost News Wrap, January 8, 2016
Mike Mimoso and Chris Brook discuss the week in news: How the Dutch are opening encryption with open arms, the end of support for IE 8, 9, and 10, and the latest bounty offered up by Zerodium.
Microsoft ends support for older versions of Internet Explorer
Update from an older Internet Explorer to avoid security risks
After January 12th, only the most current version of Internet Explorer available for a supported operating system will receive technical support and security updates.
People using Internet Explorer 8, 9, and 10 will no longer receive security or technical updates after Tuesday, January 12th. This means that the older versions of Internet Explorer can be exploited by hackers which puts your computer and your data at risk. One last patch will be released January 12th with a reminder to upgrade your browser. If you do not upgrade to Internet Explorer 11, you will begin to receive “End of Life” upgrade notifications urging you to make the switch to Internet Explorer 11. Windows 10 and Windows 8.1 users should upgrade to Internet Explorer 11. Windows 7 users with Internet Explorer 9 or 10 should upgrade to Internet Explorer 11.
Choose a different browser
If you want to stay with a Microsoft product, then you also have the option to switch to Microsoft Edge, their latest, most modern browser, but you must also be using Windows 10.
This is a good opportunity to try another browser like Google Chrome, Firefox, or Opera. We recommend Google Chrome as an alternative to Internet Explorer because of its security features and automatic updates.
There are plenty of alternative browsers to switch to as well; those that specialize in gaming, privacy, media consumption, and other things. Check out this listing of 10 obscure, highly specialized browsers from PCWorld.
How to check which version of Internet Explorer you are using
- 1. Open the browser
- 2. Click the gear or Question icon on the top right
- 3. Select ‘About Internet Explorer’ and a pop-up will appear with the version of your browser
Follow Avast on Facebook, Twitter, YouTube and Google+ where we keep you updated on cybersecurity news every day.
![]()
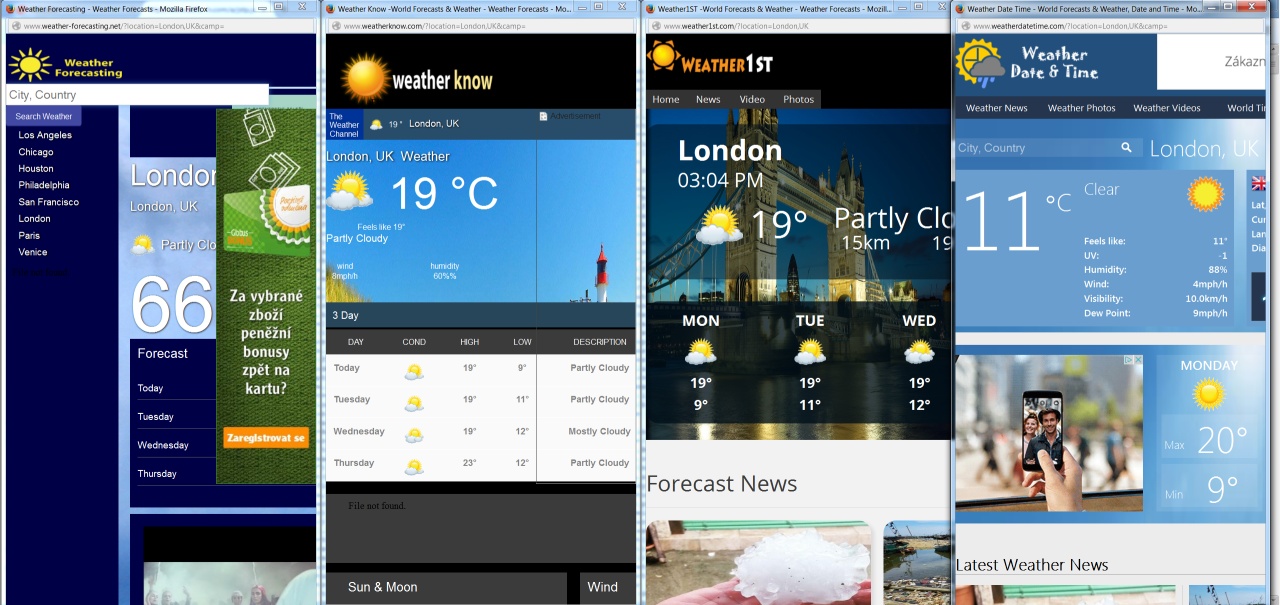
Weather Forecast for Today? Advert Flood Coming from East
Despite blocking efforts, online advertising is a daily part of our lives. Most of us get used to the large volume of adverts displayed daily, but authors of malicious code are trying to push the limits much further nowadays via advert-injection techniques used in malware threats.
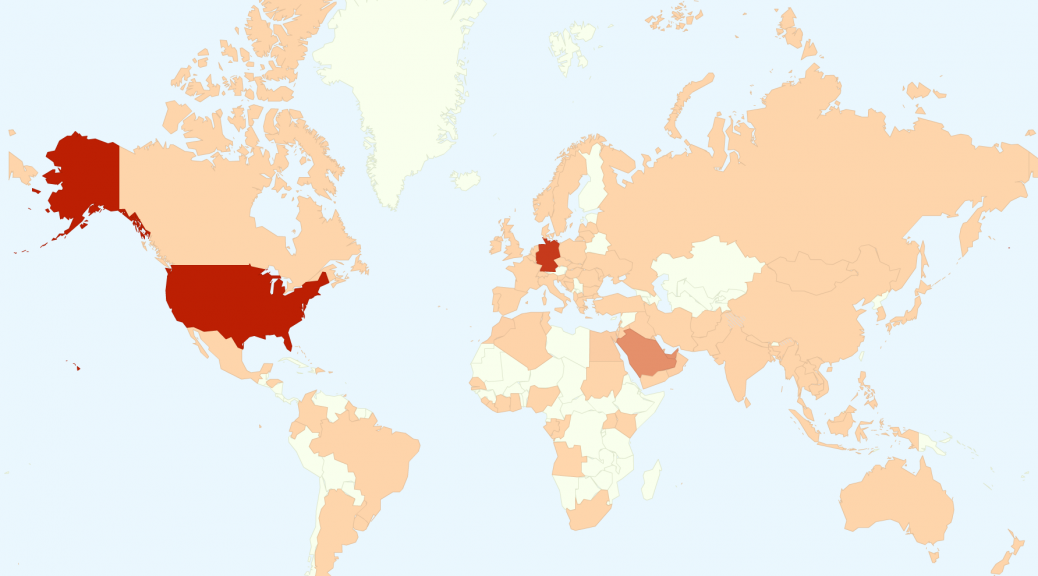
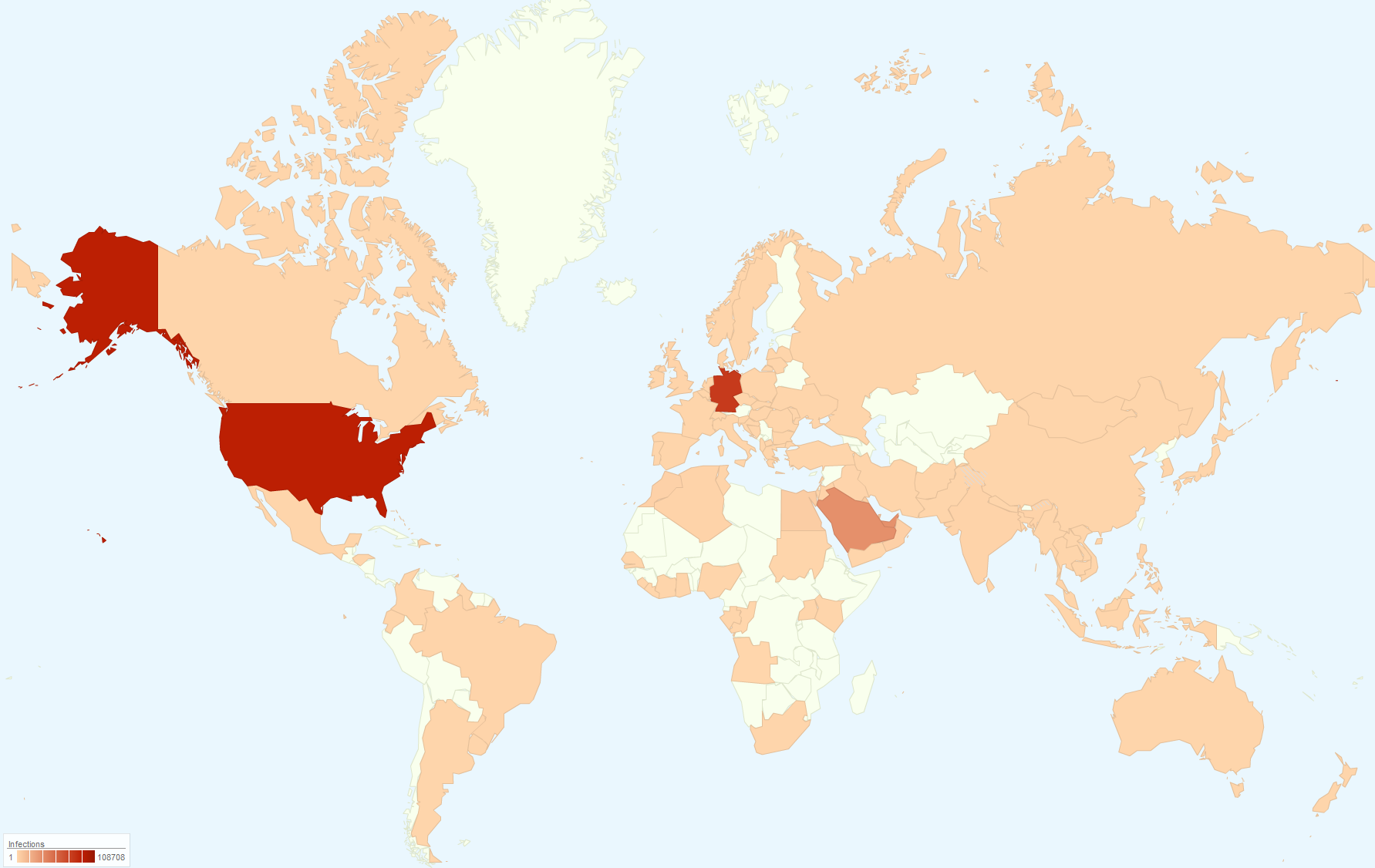
Spreading
In this post, we present a case study of one such malware that we detected via our AVG Identity Protection (IDP) component. Based on our telemetry, this infection is highly active and it is reaching its maximal peak. The most affected countries are the United States and Germany, followed by Saudi Arabia and the United Arab Emirates.
Behaviour of This Threat
The user infection starts while installing an application proclaimed by its authors as a “Weather Forecast Application”. However, once installed, this application silently downloads and installs other components that are purely malicious – this threat tries to infect all installed browsers and inject additional adverts in browser pages. It also periodically loads sets of adverts in the background without user notification. As a side-effect, it sacrifices security and performance of the infected systems for the purpose of making money via ad providers.

Detailed Analysis
Details about this threat are described in the following technical analysis.
You can also download the report now.
Stay Safe
AVG customers are protected against this threat via our multi-level protection in AVG Internet Security. If you’re not protected, you might want to check your systems using the indicators of compromise (IOC) listed in the aforementioned technical analysis.
![]()
![]()
Emergency IE Patch Fixes Vulnerability Under Attack
Microsoft released an out-of-band patch for an Internet Explorer vulnerability under attack.
Adobe rushes to patch Flash flaw under attack
Adobe Systems has issued a sizeable security update with patches for 36 vulnerabilities, at least one of which is currently under attack in the wild.
The post Adobe rushes to patch Flash flaw under attack appeared first on We Live Security.
![]()
HP Releases Details, Exploit Code for Unpatched IE Flaws
Researchers at HP’s Zero Day Initiative have disclosed full details and proof-of-concept exploit code for a series of bugs they discovered that allow attackers to bypass a key exploit mitigation in Internet Explorer.
Microsoft Brings HSTS to Windows 7 and 8.1
Microsoft announced it has added HTTP Strict Transport Security (HSTS) to Internet Explorer 11 on Windows 8.1 and Windows 7, in addition to its native inclusion in Microsoft Edge on Windows 10.
All four major browsers hacked at pwn2own
Last week computer hacking competition pwn2own once again took place at the CanSecWest conference in Vancouver.
During the competition, hackers and security researchers are challenged to exploit popular software and devices using previously unknown vulnerabilities.
Successful hackers win the device that they exploited, a cash prize, and a “Masters” jacket celebrating the year of their win.
Pwn2own 2015 was an incredibly eventful competition with over $500,000 dollars of rewards issued and all four major browsers successfully hacked, some in under a second.
News of ubiquitous software being hacked in such a short time can often leave us feeling despondent about the state of security but I believe that competitions such as pwn2own give us cause for optimism.
Cash prizes for hacking at competitions and bug bounty programs, such as those run by Google and Facebook, motivate hackers and researchers to use their skills to help improve security and not just exploit it.
As long as vulnerabilities are disclosed to the right parties when they are discovered, it helps to reduce the window of opportunity for malicious hackers to turn a profit.
Remember to update
While software manufacturers were likely hoping to come through pwn2own 2015 unscathed, most will now set about fixing and patching their products and services to mitigate these newly discovered threats.
Expect new security updates in the near future and remember to always keep your operating system and programs up to date.
Title image courtesy of securityaffairs.co
Flash, Reader, Firefox and IE Fall on Pwn2Own Day 1
Four different research teams cracked four different products on Wednesday–Adobe Flash, Reader, Mozilla Firefox, and Microsoft Internet Explorer—and collectively earned a payout of $317,000 on the first day of Pwn2Own 2015.