Monthly Archives: October 2014
Hacker-Hunters Finger 'Keyser Soze' Of Russian Underground Card Sales
OpenSSL Releases Patch for POODLE Attack
The OpenSSL Project has released a new version of the encryption software, which patches several security flaws, including the bug that is exploited by the POODLE attack on SSLv3. The updated versions of OpenSSL come just a couple of days after a trio of researchers at Google revealed the POODLE attack, which allows an attacker to […]
OpenSSL Patches Four Vulnerabilities
Original release date: October 16, 2014
OpenSSL has released updates patching four vulnerabilities, some of which may allow an attacker to cause a Denial of Service (DoS) condition or execute man-in-the-middle attacks. The following updates are available:
- OpenSSL 1.0.1 users should upgrade to 1.0.1j
- OpenSSL 1.0.0 users should upgrade to 1.0.0o
- OpenSSL 0.9.8 users should upgrade to 0.9.8zc
US-CERT recommends users and administrators review the OpenSSL Security Advisory for additional information and apply the necessary updates.
Â
Â
This product is provided subject to this Notification and this Privacy & Use policy.
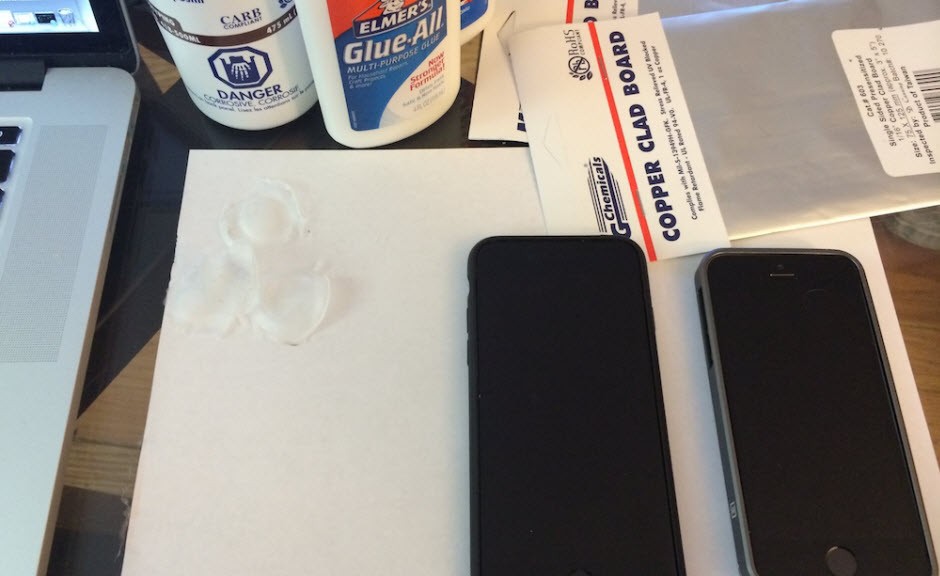
iPhone 6. The fingerprint reader security
Being the leading technology brand can have its downsides. And if you don’t believe it, ask Apple. Every time the firm from Cupertino introduces a new product, the same thing happens: there is great anticipation, with seemingly half the world awaiting, long queues of tech disciples… and an army of people looking for bugs in the new devices.
In the end, vulnerabilities emerge and obviously their impact is far greater than with other brands (especially if it is a new device). Apple has already suffered a few embarrassing errors discovered by users. You don’t have to go too far back to see: the aluminum case of the iPhone 6 Plus was said to be too flexible, meaning that the phone can even bend under certain conditions.
A secure iPhone?
While the tech world looked on in amazement at this problem in the new Apple device, a second rather more difficult issue emerged: Apple’s ‘Touch ID’ fingerprint identification system is not entirely secure.
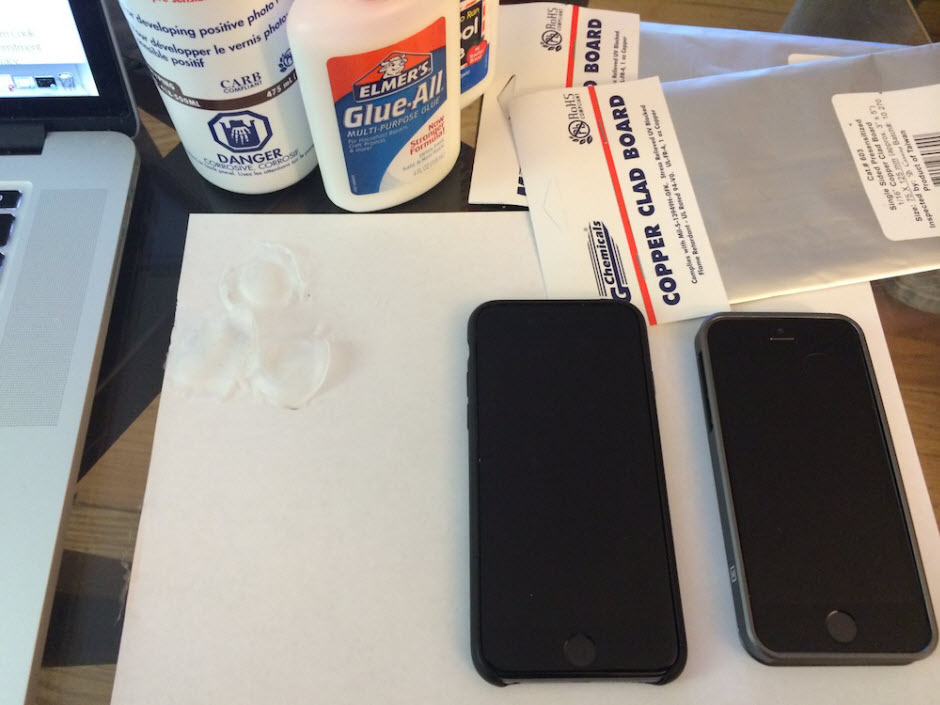
This technology has already been used in iPhone 5s and as with iPhone 6, a few days after the launch an error was discovered: there was a relatively simple way to get past Apple’s fingerprint ID system.
“A fingerprint of the phone user, photographed from a glass surface, was enough to create a fake finger that could unlock an iPhone 5s secured with TouchID,” claimed the European hacker group, Chaos Computer Club, a year ago. This was something that could be performed by anyone with a bit of skill and patience.
So despite the company’s claims that with the new biometric system your fingerprint is one of the strongest passwords in the world, once again such claims might be premature.
History has repeated itself, and this time surprisingly, it has done so quite literally. Even though the Touch ID flaw was discovered a year ago, Apple has launched two new iPhones with the same problem.
This is confirmed by security expert Marc Rogers. “Sadly there has been little in the way of measurable improvement in the sensor between these two devices,†he claims. Although he underlines that the same fake prints that could deceive the Touch ID in iPhone 5s are no longer viable in the latest Apple device.
According to Rogers, the difference is that the company has improved the scan resolution to improve the reliability of the system. However, this doesn’t mean that the same technique used to unlock the iPhone 5s couldn’t be used for iPhone 6. The difference is that the fake print would need to be a better quality.
This new flaw in Apple’s security system is serious, and even more so given the launch of Apple Pay, the company’s new mobile device payment system.
Thanks to NFC technology, users of this service can pay for things simply by waving their iPhone at the point of sale (POS) terminal. Indeed, the tool used by Apple to secure the payment service is none other than the Touch ID technology which, as Rogers explains, is easily hacked.
Nevertheless, Rogers does point out that using fingerprints is an effective form of user authentication, though Apple should include two-factor verification to give users complete peace of mind.
What do you think? Would you activate this type of payment?
The post iPhone 6. The fingerprint reader security appeared first on MediaCenter Panda Security.
Bypassing blacklists based on IPy
Posted by Nicolas Grégoire on Oct 16
IPy is a Python “class and tools for handling of IPv4 and IPv6 addresses
and networks” (https://github.com/haypo/python-ipy). This library is
sometimes used to implement blacklists forbidding internal, private or
loopback addresses.
Using octal encoding (supported by urllib2), it is possible to bypass
checks based on the result of the iptype() function. For example, IP
address ‘0177.0000.0000.0001’ is considered as…
Advisory 01/2014: Drupal7 – pre Auth SQL Injection Vulnerability
Posted by Stefan Horst on Oct 16
SektionEins GmbH
www.sektioneins.de
-= Security Advisory =-
Advisory: Drupal – pre-auth SQL Injection Vulnerability
Release Date: 2014/10/15
Last Modified: 2014/10/15
Author: Stefan Horst [stefan.horst[at]sektioneins.de]
Application: Drupal >= 7.0 <= 7.31
Severity: Full SQL injection, which results in total control and code execution of Website.
Risk: Highly Critical…
CVE-2014-2230 – OpenX Open Redirect Vulnerability
Posted by Jing Wang on Oct 16
Exploit Title: OpenX Open Redirect Vulnerability
Product: OpenX
Vendor: OpenX
Vulnerable Versions: 2.8.10 and probably prior
Tested Version: 2.8.10
Advisory Publication: OCT 8, 2014
Latest Update: OCT 8, 2014
Vulnerability Type: Open Redirect [CWE-601]
CVE Reference: CVE-2014-2230
Risk Level: Low
CVSSv2 Base Score: 2.6 (AV:N/AC:H/Au:N/C:N/I:P/A:N)
Solution Status: Solution Available
Credit: Wang Jing [Mathematics, Nanyang Technological…
New York Times nytimes.com Page Design XSS Vulnerability (Almost all Article Pages Before 2013 are Affected)
Posted by Jing Wang on Oct 16
New York Times nytimes.com Page Design XSS Vulnerability (Almost all
Article Pages Before 2013 are Affected)
Domain:
http://www.nytimes.com/
Vulnerability Description:
The vulnerability occurs at New York Times’s URLs. Nytimes (short for New
York Times) uses part of the URLs to construct its pages. However, it seems
that Nytimes does not filter the content used for the construction at all
before 2013.
Based on Nytimes’s Design, Almost all…
CESA-2014:1647 Important CentOS 5 thunderbirdSecurity Update
CentOS Errata and Security Advisory 2014:1647 Important Upstream details at : https://rhn.redhat.com/errata/RHSA-2014-1647.html The following updated files have been uploaded and are currently syncing to the mirrors: ( sha256sum Filename ) i386: bc59af1c3aa2950614736db2e2e1e1596eb77228a98ac4a83fec2735e6a58257 thunderbird-31.2.0-2.el5.centos.i386.rpm x86_64: b3065ffa9bbe359d2b810a2c7ac3eb702966e4c37cb638b69229019965584992 thunderbird-31.2.0-2.el5.centos.x86_64.rpm Source: 0c0305b9aedc7ced272157b8582dfa756f4db974dc4d5bdb394b02a0fe489cb0 thunderbird-31.2.0-2.el5.centos.src.rpm