Monthly Archives: November 2014
TA14-317A: Apple iOS "Masque Attack" Technique
Original release date: November 13, 2014
Systems Affected
iOS devices running iOS 7.1.1, 7.1.2, 8.0, 8.1, and 8.1.1 beta.
Overview
A technique labeled “Masque Attack†allows an attacker to substitute malware for a legitimate iOS app under a limited set of circumstances.
Description
Masque Attack was discovered and described by FireEye mobile security researchers.[1] This attack works by luring users to install an app from a source other than the iOS App Store or their organizations’ provisioning system. In order for the attack to succeed, a user must install an untrusted app, such as one delivered through a phishing link. Â
This technique takes advantage of a security weakness that allows an untrusted app—with the same “bundle identifier†as that of a legitimate app—to replace the legitimate app on an affected device, while keeping all of the user’s data. This vulnerability exists because iOS does not enforce matching certificates for apps with the same bundle identifier. Apple’s own iOS platform apps, such as Mobile Safari, are not vulnerable.
Impact
An app installed on an iOS device using this technique may:
- Mimic the original app’s login interface to steal the victim’s login credentials.
- Access sensitive data from local data caches.
- Perform background monitoring of the user’s device.
- Gain root privileges to the iOS device.
- Be indistinguishable from a genuine app.
Solution
iOS users can protect themselves from Masque Attacks by following three steps:
- Don’t install apps from sources other than Apple’s official App Store or your own organization.
- Don’t click “Install†from a third-party pop-up when viewing a web page.
- When opening an app, if iOS shows an “Untrusted App Developer†alert, click on “Don’t Trust†and uninstall the app immediately.
Further details on Masque Attack and mitigation guidance can be found on FireEye’s blog [1]. US-CERT does not endorse or support any particular product or vendor.
References
Revision History
- November 13, 2014: Initial Release
This product is provided subject to this Notification and this Privacy & Use policy.
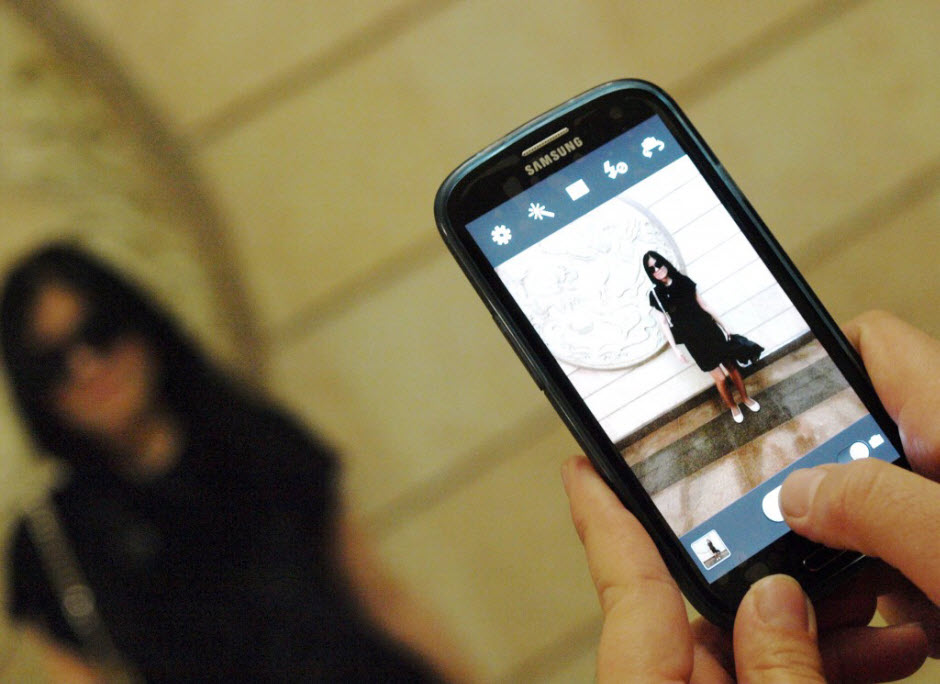
Careful with photos from unknown sources in Android: They could now contain a nasty surprise
We now live in the age of the image. Hardly a day goes by when we don’t download or share an image of friends or family. The saying ‘A picture is worth a thousand words’ has become a motto for our everyday lives.
Well aware of this are those who prowl the Internet with malicious intent. They know that images are now swarming across the Web, and as such represent the perfect Trojan horse to conceal malicious content. In fact, had it not been for Axelle Apvrille and Ange Albertini, many have already tried. These researchers were responsible for uncovering a crack in the defensive wall of Google’s mobile operating system, through which images can be used to hide malicious software, which could then slip past the system’s protection.

At the latest Black Hat Europe event in Amsterdam, these cyber-security experts presented their work on the vulnerability in Android. Due to this flaw, malicious users could reach the smartphone or tablet of any user through an image which, when downloaded, would become a file that could infect the device.
According to Apvrille and Albertini, the malicious payload could be concealed in any image, regardless of format. Whether a .png or .jpg, what to the naked eye is simply a picture of a person, could simply be a front for code that would be released from the image and spread malware.
To demonstrate the existence of the vulnerability, they created a tool called AngeCryption, which let them convert images into packets. Thanks to this, they could hide anything they wanted to transmit from one device to another without security systems or Google’s own scanner being aware of its existence. So behind an apparently inoffensive image there could be an .apk, the type of executable file that allows applications to be installed.
In the proof-of-concept presented by the researchers, they used an image of Darth Vader to hide a malicious app designed to steal photos, messages and other data from the devices it is downloaded to.
Imagine a contact sent you an image via WhatsApp and you downloaded it, without you knowing an app would be installed on your device that could search for and steal anything it found. This is precisely what this vulnerability allows.
“Such an attack is highly likely to go unnoticed, because the wrapping Android package hardly has anything suspicious about it,†explain Apvrille and Albertini. They also warn that this flaw has been present in all versions of Android so far.
The discovery of this security hole was kept quiet until the researchers were able to inform Google and the company’s security team had time to fix it. So are you now safe? Yes, but only if you remember to upgrade your smart phone or tablet. If you don’t, you will be exposed to potentially nasty surprises.
So we advise you:
- To be careful with photos from unknown sources
- Install any available Google updates.
Also, as prevention is better than cure, install our antivirus for Android devices. Why take unnecessary risks?
The post Careful with photos from unknown sources in Android: They could now contain a nasty surprise appeared first on MediaCenter Panda Security.
Joomla Eventbooking Cross Site Scripting
The Joomla Eventbooking component suffers from a cross site scripting vulnerability.
Bugtraq: [ESNC-2039348] Multiple Critical Security Vulnerabilities in SAP Governance, Risk and Compliance (SAP GRC)
[ESNC-2039348] Multiple Critical Security Vulnerabilities in SAP Governance, Risk and Compliance (SAP GRC)
Bugtraq: [SECURITY] [DSA 3072-1] file security update
[SECURITY] [DSA 3072-1] file security update
Bugtraq: CVE-2014-8731 – RCE in phpMemcachedAdmin <=1.2.2
CVE-2014-8731 – RCE in phpMemcachedAdmin <=1.2.2
Bugtraq: CVE-2014-8732
CVE-2014-8732
RHSA-2014:1846-1: Moderate: gnutls security update
Red Hat Enterprise Linux: Updated gnutls packages that fix one security issue are now available for
Red Hat Enterprise Linux 7.
Red Hat Product Security has rated this update as having Moderate security
impact. A Common Vulnerability Scoring System (CVSS) base score, which
gives a detailed severity rating, is available from the CVE link in the
References section.
CVE-2014-8564
RHEA-2014:1847-1: Red Hat Network Tools spacewalk-remote-utils enhancement update
Red Hat Enterprise Linux: An updated spacewalk-remote-utils package that adds one enhancement is now
available for Red Hat Network Tools.