core/string_api.php in MantisBT before 1.2.18 does not properly categorize URLs when running under the web root, which allows remote attackers to conduct open redirect and phishing attacks via a crafted URL in the return parameter to login_page.php.
Monthly Archives: December 2014
CVE-2014-7265 (linpha)
Cross-site scripting (XSS) vulnerability in LinPHA allows remote attackers to inject arbitrary web script or HTML via unspecified vectors.
CVE-2014-8270 (bmc_track-it!)
BMC Track-It! 11.3 allows remote attackers to gain privileges and execute arbitrary code by creating an account whose name matches that of a local system account, then performing a password reset.
CVE-2014-9365 (python)
The HTTP clients in the (1) httplib, (2) urllib, (3) urllib2, and (4) xmlrpclib libraries in CPython (aka Python) 2.x before 2.7.9 and 3.x before 3.4.3, when accessing an HTTPS URL, do not (a) check the certificate against a trust store or verify that the server hostname matches a domain name in the subject’s (b) Common Name or (c) subjectAltName field of the X.509 certificate, which allows man-in-the-middle attackers to spoof SSL servers via an arbitrary valid certificate.
Mobile advertising firms spread malware by posing as official Google Play apps
As a malware analyst, I find new pieces of malware day in and day out. In fact, I see so many new malware samples that it’s difficult for me to determine which pieces would be really interesting for the public. Today, however, I found something that immediately caught my attention and that I thought would be interesting to share.
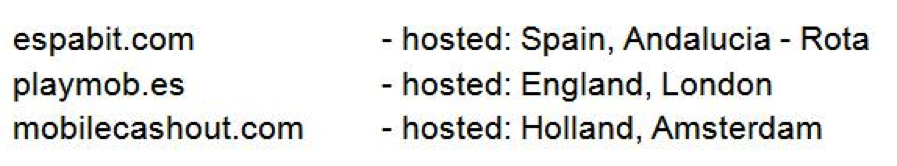
The three URLs listed above are websites that offer mobile monetizing kits, which are advertising kits that developers can implement in their mobile apps. The goal for developers is to monetize from advertisements. If a user clicks on one of the ads delivered by one of the above listed providers, he may be lead to a malicious subdomain.
The most visited of the three URLs is Espabit. According to our statistics, we know that Espabit’s servers get around 150,000 views a day and nearly 100% of the views are from mobile devices. This may not seem like that much compared to the number of Android users there are in the world, but it is still a considerable number. Espabit is trying to position themselves as a world leader in advertising, and their website may appear innocent, but first impressions can be deceiving.
The most visited Espabit subdomain, with more than 400,000 views during the last few months, leads app users to pornographic sites via the ads displayed in their apps. The site displays a download offer for nasty apps (no pun intended) that have malicious behavior.
The above is just one example of the malicious links; there are many others hosted on the same server. The majority of the links lead to pornography or fake apps that all have one thing in common: They all steal money from innocent users.
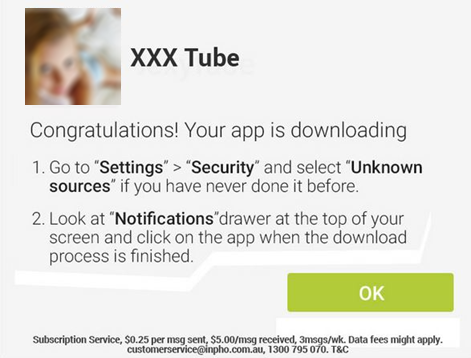
How do they convince people to download their app? By posing as official Google Play apps. The apps are designed to look like they are from the official Google Play Store – tricking people into trusting the source. Since Android does not allow users to install apps from untrusted sources, the sites offer manuals in different languages, like English, Spanish, German, and French, explaining how to adjust Android’s settings so that users can install apps from untrusted sources, like these malicious apps. How considerate of them.
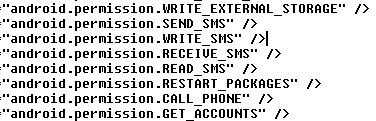
Now let’s take a deeper look at what the apps are capable of doing:
All of the “different” apps being offered by the three sites listed above are essentially the same in that they can steal personal information and send premium SMS. So far, we know about more than 40 of them stored on the websites’ servers. Most of the apps are stored under different links and, again, are offered in different languages (they want everyone to be able to “enjoy” their apps). The goal behind all of the apps is always the same: Steal money.
Some of the permissions the apps are granted when downloaded…
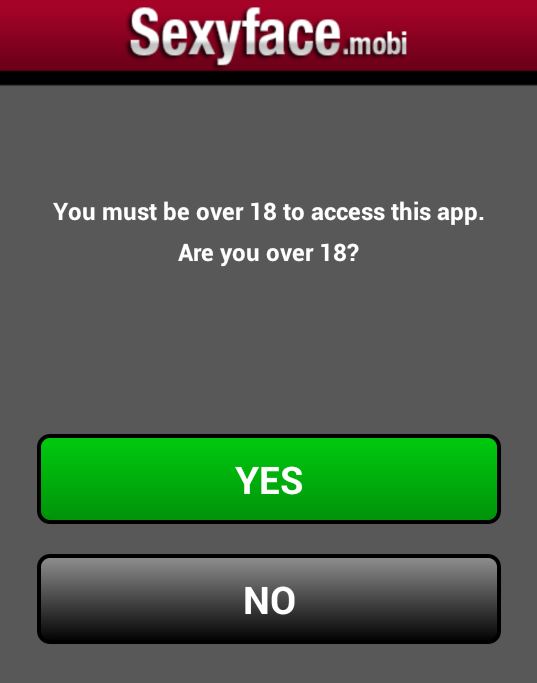
Once you open the apps, you get asked if you are 18 or older (they are not only considerate in that they offer their product in various languages, but they also have morals!).
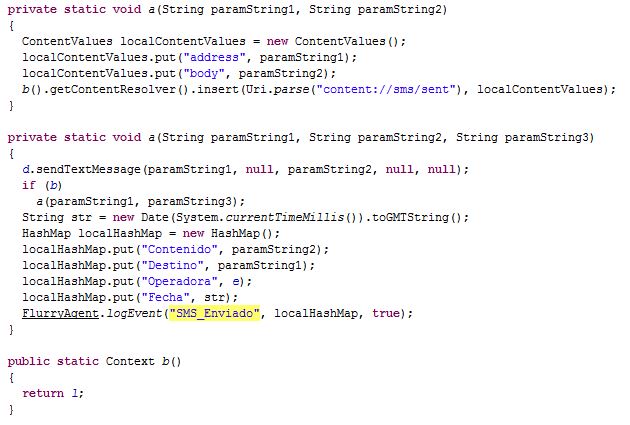
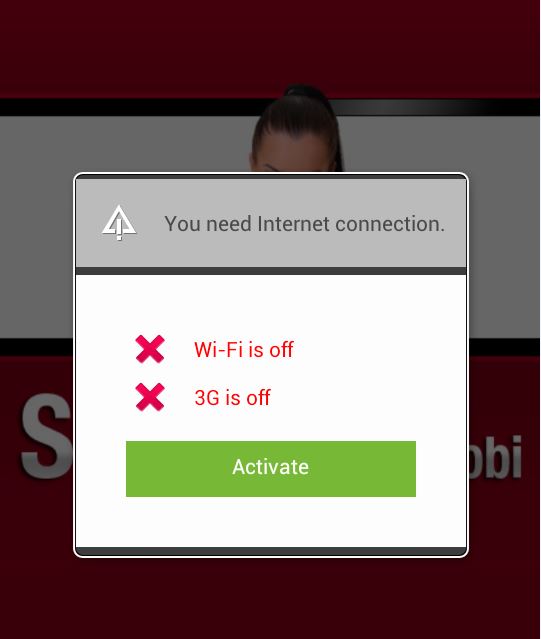
After you click on “YES” you are asked to connect your device to the Internet. Once connected to the Internet your device automatically starts sending premium SMS, each costing $0.25 and sent three times a week. That’s all the app does! The amount stolen a week does not seem like much, but that may be done on purpose. People may not notice if their phone bill is $3.00 more than it was the month before and if they don’t realize that the app is stealing money from them and don’t delete the app it can cost them $36.00 a year.
This malware is actually not unique in terms of the technique it uses. However, collectively, the three websites have around 185,000 views daily, which is a lot considering there is malware stored on their servers. Not everyone is redirected to malware, but those who are, are being scammed. Considering that the most visited malicious subdomain had around 400,000 views in the last quarter, it tells us that a large number of those visitors were infected. This means these ad providers are making a nice sum of money and it’s not all from ad clicks and views.
Although many mobile carriers around the world block premium SMS, including major carriers in the U.S., Brazil, and the UK, this case should not be taken lightly. These malware authors use social engineering to circumvent Google’s security and target innocent app users via ads. Think of how many apps you use that display ads, then think of all the valuable information you have stored on your phone that could be abused.
All malicious apps we found and described here are detected by Avast as:
Android:Erop-AG [Trj]
Android:Erop-AJ [Trj]|
Android:Erop-AS [Trj]
Some of SHA256:
DBEA83D04B6151A634B93289150CA1611D11F142EA3C17451454B25086EE0AEF
87AC7645F41744B722CEFC204A6473FD68756D8B2731A4BF82EBAED03BCF3C9B
More controversy for Uber: The app compiles user data without permission
 The emergence of Uber has put taxi drivers around the world on red alert. Just this week, the Spanish High Court has ordered the company to cease operations on the grounds of unfair competition with taxi drivers.
The emergence of Uber has put taxi drivers around the world on red alert. Just this week, the Spanish High Court has ordered the company to cease operations on the grounds of unfair competition with taxi drivers.
Yet it’s not just the business model (putting customers in touch with unlicensed drivers) that stretches the limits of legality. The app, which effectively manages requests and responses, also contains some dubious aspects.
This is what a group of IT security researchers have discovered after analyzing how the mobile app works. They have analyzed the code of the Android app in detail and their findings don’t reflect well on Uber.
The study revealed that while users take advantage of the services they offer, the system transmits information about their Internet habits along with certain features of their phone, details that are entirely unrelated to the service.
The San Francisco based ‘start-up’ would seem to be interested in the people its customers are in contact with; it collects data on the length of calls and the phone numbers.
It also gathers information about the apps installed on the device, the free memory space and byte circulation. Similarly, the GPS coordinates and the IP address of the phone are recorded.

The company wants to know what messages (SMS, MMS and emails) are sent and received by users, and suspiciously, the tool reports the malware that the phone is vulnerable to and the security algorithm used on the device. The obvious question is, why would a company that only offers a transport service need all this information about its users?
Some have defended its strategy, claiming that this is an anti-fraud measure to identify fake accounts (competitors could use the app covertly with other intentions). Still, the end doesn’t justify the means. The terms and conditions of the app don’t reflect the entire flow of information that really takes place.
For the moment these experts have only analyzed the app for Android; it’s still unclear whether the same things happen on the iOS version. Nevertheless, it may be best to fear the worst, as Apple is hardly renowned for its discretion.
If you think that after this news Google will be withdrawing the app from its platforms, you’re probably forgetting a small detail -in the form of a bundle of cash. Google Ventures, the branch of the company that invests in new ventures and business opportunities, has financed Uber to the tune of $258 million. It’s unlikely to write that off just for a small problem of privacy.
Uber is not the only app that uses your data without clarifying the reasons. We recently discussed some torch apps that do the same with GPS coordinates, photos and text messages.
You can’t entirely avoid being spied upon, though revelations like these are a wake-up call to be on your guard with respect to the permissions on the apps that you download. It’s common to accept conditions without reading them in the belief that an app must be trustworthy, but all that glitters isn’t gold.
Remember that Panda Mobile Security, our free antivirus for Android, can help you to monitor which personal data on your phone is shared with third-parties.
The post More controversy for Uber: The app compiles user data without permission appeared first on MediaCenter Panda Security.
APPLE-SA-2014-12-11-1 Safari 8.0.2, Safari 7.1.2, and Safari 6.2.2
From: Apple Product Security
Reply to list
APPLE-SA-2014-12-11-1 Safari 8.0.2, Safari 7.1.2, and Safari 6.2.2 Safari 8.0.2, Safari 7.1.2, and Safari 6.2.2 are now available and include the security content of Safari 8.0.1, Safari 7.1.1, and Safari 6.2.1: https://support.apple.com/en-us/HT6596 Safari 8.0.2, Safari 7.1.2, and Safari 6.2. [...]
Bugtraq: [SECURITY] [DSA 3096-1] pdns-recursor security update
[SECURITY] [DSA 3096-1] pdns-recursor security update
Bugtraq: ResourceSpace Multiple Cross Site Scripting, and HTML and SQL Injection Vulnerabilities
ResourceSpace Multiple Cross Site Scripting, and HTML and SQL Injection Vulnerabilities
Bugtraq: [SECURITY] [DSA 3098-1] graphviz security update
[SECURITY] [DSA 3098-1] graphviz security update