[SYSS-2015-031] sysPass – SQL Injection
Monthly Archives: July 2015
Bugtraq: CVE-2015-4670 – AjaxControlToolkit File Upload Directory Traversal
CVE-2015-4670 – AjaxControlToolkit File Upload Directory Traversal
Fedora 21 Security Update: thunderbird-38.1.0-1.fc21
Update to latest upstream version, see following page for changes:
https://www.mozilla.org/en-US/thunderbird/38.1.0/releasenotes/
This update also should fixed problems with thunderbird-lightning-gdata package.
Rebase to Thunderbird 38. By this release thunderbird-lightning (calendar) package has become obsolete, because it is a part of Thunderbird 38 package now.
For changes see: https://www.mozilla.org/en-US/thunderbird/38.0.1/releasenotes/
Do third-party app stores pose a threat to mobile security?
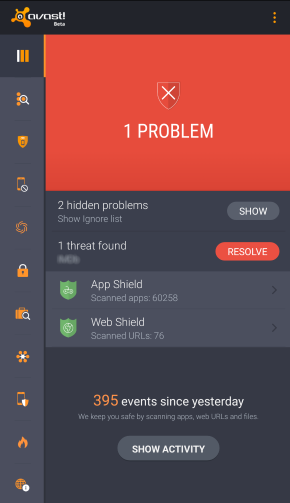
Malware detected on Android
Over time, we’ve noticed the presence of some fairly heated user debates disputing the necessity of security or antivirus apps for Android devices. This could have been sparked by our recent post which argues that you can’t always rely on the security of Google Play or because of the myth that antivirus companies create viruses to sell more software.
Certain security gurus claim that if users stick to downloading and purchasing apps using only the Google Play Store, nothing bad will happen to their devices. However, we found that this line of thinking is not 100% correct, as was demonstrated through the discovery of a rogue Dubsmash app or in the infamous case of apps on Google Play posing as games and infecting millions of users with adware. Despite these findings, there are some users who still feel that they’re safe whenever using Google Play. This feeling of false security could have negative consequences; for example, when your data or financial information is stolen or when you have to resort to resetting your device in order to cleanse it of malware.
So, we know we can’t rely on the Google Play Store all the time, but are third-party stores more secure? Of course not. In this case, how is it still possible that it’s not a problem to use third-party stores? First of all, it’s necessary to point out that there are certain legitimate and clean third-party stores, such as Amazon and FDroid. At the same time, there are tons of shady stores and even more black market .apk files promising to deliver you the latest features of a cracked app.
With these things in mind, how can users navigate the world of third-party stores?
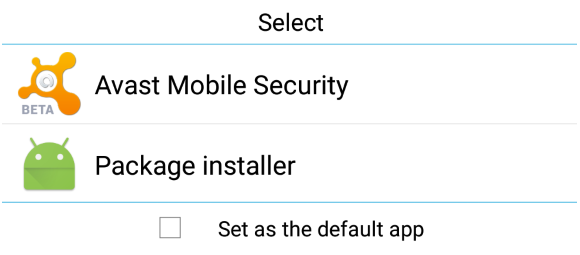
Android default apk handler
Besides the well known (and default) security options of Android, there is another useful feature that remains more or less unknown by average users: the default app feature. When Android (and also Windows) is about to open a file, it looks into its database to determine which application should be used and launches it. If you set Avast Mobile Security to be run at this preliminary stage of an app’s installation, it will scan the .apk file before it is opened and the installation process has begun. If any mistake or bug is detected, the process is halted and you’ll be given the option to uninstall the app.
If you have already installed Avast in your Android smartphone or tablet and this option is no longer shown, the easiest option will be to uninstall it, reboot and install it again. When the dialog pops up, choose Avast as your default handler for .apk files. As mobile malware reached the one million Android sample mark last year, the Avast database continues to grow exponentially. Avast Mobile Security also performs very well with new and unknown malware, as independent tests show us.
You can be safer and have a complete peace of mind while using third-party stores if you keep Avast Mobile Security running as your default installation package app. Download Avast Mobile Security for free on the Google Play Store.
![]()
Fedora 22 Security Update: libidn-1.31-1.fc22
Fedora 22 Security Update: thunderbird-38.1.0-1.fc22
Update to latest upstream version, see following page for changes:
https://www.mozilla.org/en-US/thunderbird/38.1.0/releasenotes/
This update also should fixed problems with thunderbird-lightning-gdata package.
Rebase to Thunderbird 38. By this release thunderbird-lightning (calendar) package has become obsolete, because it is a part of Thunderbird 38 package now.
For changes see: https://www.mozilla.org/en-US/thunderbird/38.0.1/releasenotes/
CEBA-2015:1222 CentOS 6 dracut BugFix Update
CentOS Errata and Bugfix Advisory 2015:1222 Upstream details at : https://rhn.redhat.com/errata/RHBA-2015-1222.html The following updated files have been uploaded and are currently syncing to the mirrors: ( sha256sum Filename ) i386: 8dc75ad1b4ce63d4d8d42fc791f54703fffb59e2eae6970bb576897ded5de370 dracut-004-356.el6_6.3.noarch.rpm 5df19b031cbd618cd9fab321a053b771271625ba5a267433e8ee8d25b6510e4f dracut-caps-004-356.el6_6.3.noarch.rpm 8ea7b720b3a5fe5c9e0df940506d7dab7a1cd4c6800100ae1ac852e3e6d30a5b dracut-fips-004-356.el6_6.3.noarch.rpm 6ba71308b46cde9d653ed7dd933b0e8a4b4d70cb8f368f4d6755555c52ec528e dracut-fips-aesni-004-356.el6_6.3.noarch.rpm fbd763e2e444d0feb615ddc2bb253a5a992bfa58c2a7b9807abdb17ada951f99 dracut-generic-004-356.el6_6.3.noarch.rpm 88b454575602d2991391c3edba2c308224307e67dea01c3e630257f7ea8137ab dracut-kernel-004-356.el6_6.3.noarch.rpm e575e9550930005c20b879480ca8ece2f885211d11703c1f313307f983b41edd dracut-network-004-356.el6_6.3.noarch.rpm aef9250752bfcee0493bcc8295b5b0db16f38b1076d12043c9e48455b6a900be dracut-tools-004-356.el6_6.3.noarch.rpm x86_64: 8dc75ad1b4ce63d4d8d42fc791f54703fffb59e2eae6970bb576897ded5de370 dracut-004-356.el6_6.3.noarch.rpm 5df19b031cbd618cd9fab321a053b771271625ba5a267433e8ee8d25b6510e4f dracut-caps-004-356.el6_6.3.noarch.rpm 8ea7b720b3a5fe5c9e0df940506d7dab7a1cd4c6800100ae1ac852e3e6d30a5b dracut-fips-004-356.el6_6.3.noarch.rpm 6ba71308b46cde9d653ed7dd933b0e8a4b4d70cb8f368f4d6755555c52ec528e dracut-fips-aesni-004-356.el6_6.3.noarch.rpm fbd763e2e444d0feb615ddc2bb253a5a992bfa58c2a7b9807abdb17ada951f99 dracut-generic-004-356.el6_6.3.noarch.rpm 88b454575602d2991391c3edba2c308224307e67dea01c3e630257f7ea8137ab dracut-kernel-004-356.el6_6.3.noarch.rpm e575e9550930005c20b879480ca8ece2f885211d11703c1f313307f983b41edd dracut-network-004-356.el6_6.3.noarch.rpm aef9250752bfcee0493bcc8295b5b0db16f38b1076d12043c9e48455b6a900be dracut-tools-004-356.el6_6.3.noarch.rpm Source: c6c08bcbd66cb00545749e3d57a18b31a39225c047e84bf443d85a7584e32ad2 dracut-004-356.el6_6.3.src.rpm
CVE-2015-5122 (flash_player)
Use-after-free vulnerability in the DisplayObject class in the ActionScript 3 (AS3) implementation in Adobe Flash Player 13.x through 13.0.0.302 on Windows and OS X, 14.x through 18.0.0.203 on Windows and OS X, 11.x through 11.2.202.481 on Linux, and 12.x through 18.0.0.204 on Linux Chrome installations allows remote attackers to execute arbitrary code or cause a denial of service (memory corruption) via crafted Flash content that leverages improper handling of the opaqueBackground property, as exploited in the wild in July 2015.
CVE-2015-5123 (flash_player)
Use-after-free vulnerability in the BitmapData class in the ActionScript 3 (AS3) implementation in Adobe Flash Player 13.x through 13.0.0.302 on Windows and OS X, 14.x through 18.0.0.203 on Windows and OS X, 11.x through 11.2.202.481 on Linux, and 12.x through 18.0.0.204 on Linux Chrome installations allows remote attackers to execute arbitrary code or cause a denial of service (memory corruption) via crafted Flash content that overrides a ValueOf function, as exploited in the wild in July 2015.
RHBA-2015:1220-1: chromium-browser bug fix and enhancement update
Red Hat Enterprise Linux: Updated chromium-browser packages that fix several bugs and add various
enhancements are now available for Red Hat Enterprise Linux 6.