Monthly Archives: December 2015
Congress Slips CISA Into A Budget Bill That's Sure To Pass
May the force, but not the malware, be with you!
Not very long ago, in a galaxy not far away, a group of cybercriminals decided to take advantage of the Star Wars effect to spread malware among the most impatient fans.

A lot of people cannot wait to see Star Wars: The Force Awakens, and that’s something cybercrooks know. That’s why a lot of links that theoretically allow the download of the new movie of the popular saga appeared. As many of you can imagine, those links do not include the films, the only thing they include is malware! An idea worthy of Darth Vader!
We can see those links in popular download sites, along with a lot of comments from users that warn about the true purpose of the links: To install malware on users’ devices.
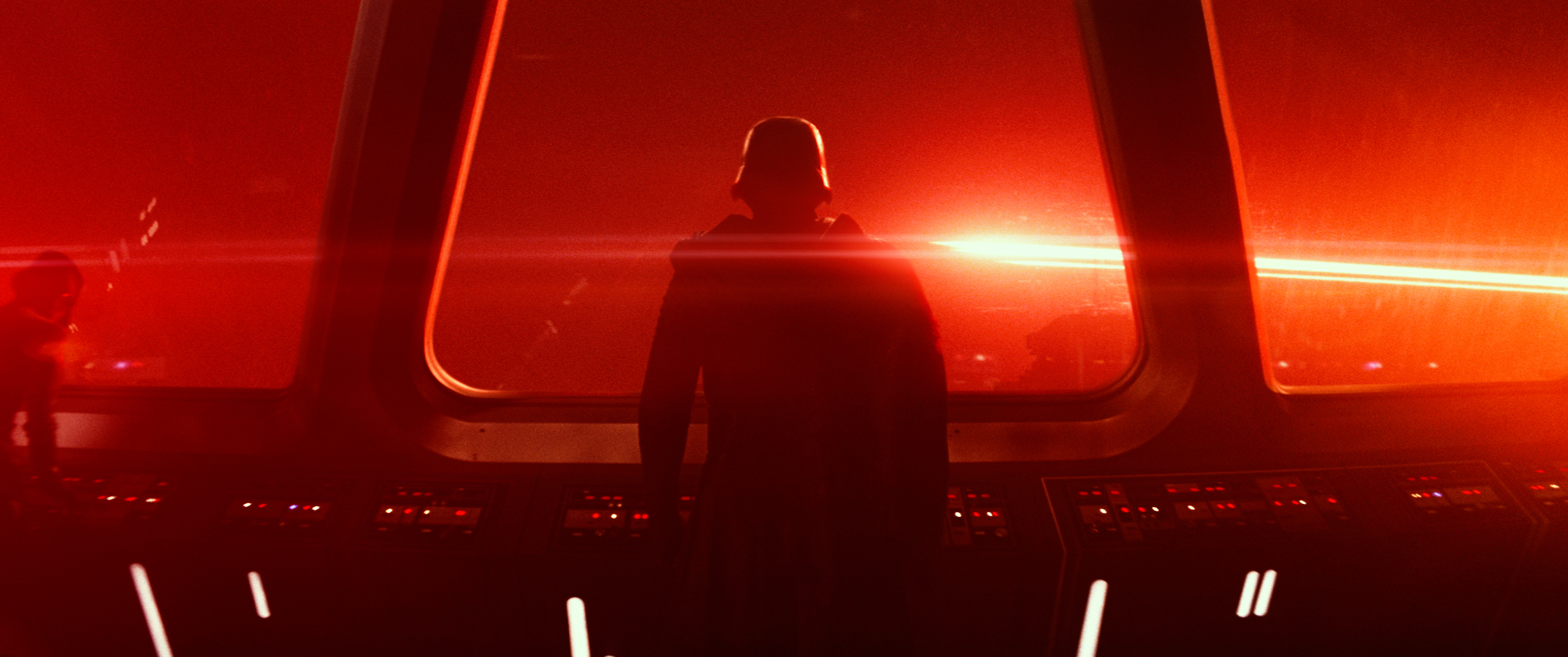
Is easy to avoid falling victim of this type of scam; just avoid clicking on suspicious links and install an antivirus, like Avast 2016, and keep it updated.
As master Yoda said: “Patience you must have, my young Padawan”.
The power of the dark side is very tempting, but do not let cravings take over you. May the Force and Avast be with you!
Images via ADSLZone and Starwars.com
Follow Avast on Facebook, Twitter, YouTube, and Google+ where we keep you updated on cybersecurity news every day.
![]()
How to be a cybersecurity Jedi – 5 things we’ve learnt from Star Wars
While we await the premiere of the seventh installment in the famous series, Star Wars VII: The Force Awakens, we’ve decided to look back on the original trilogy to look for subtle security tips that are hidden in films.
Pop culture, especially when it concerns robots, spaceships, and technology, can show us a lot about data protection and strategies to prevent possible cyberattacks.

Hiding places can be found
In The New Hope, the original film, Princess Leia managed to record a message on R2-D2 in the hangar that she’d been held captive in. Later, the lovable robot escaped with his companion, C-3PO, and they made it to Tatooine.
There they found a young Luke Skywalker who, after playing around with some buttons, succeeded in unlocking the holograph message that the princess has left on the machine, which also included blue prints of the Death Star.
All of this valuable information was protected by what is known in the real world as security through obscurity: a strategy that uses a secret in the design of a program to hide information. Its defenders don’t think it’s likely that anyone could discover what’s hidden but, without a good encryption, Darth Vader could have easily accessed the information saved on R2-D2 (if he had managed to capture the two friends).
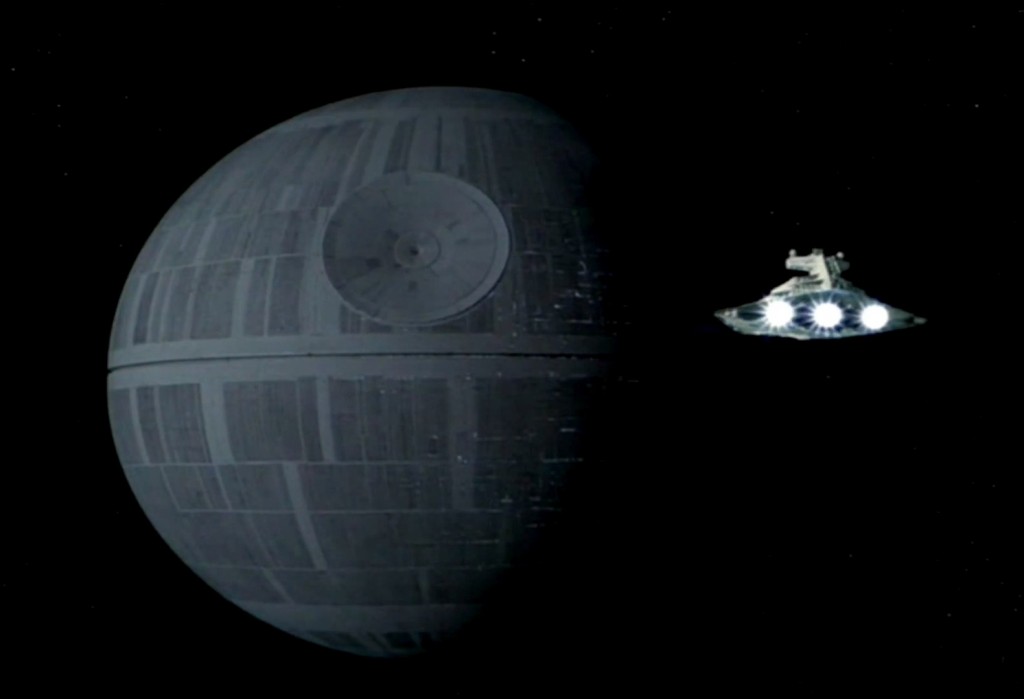
Small vulnerabilities, big problems
At the end of the film, Luke Skywalker is able to blow up the massive Death Star with just two shots: applied to the right spot, a small hit can cause huge damage.
Something similar happens in IT security. Sometimes it’s the small vulnerabilities in the most basic of software that serves as an entry point for cybercriminals, allowing them to carry out complex attacks, steal information, or take control of the entire network. The conclusion is that, in order not to wind up like the Death Star, be sure to look after the security of your devices, up to the smallest of details.
Hackers with Jedi abilities
We also see in The New Hope that Obi-Wan Kenobi shows his Jedi abilities to trick the imperial soldiers, playing with their minds to make them believe something different to the reality.
Cybercriminals use a similar trick to make programs miss certain details. Many types of malware include what is known as a rootkit, which hides in the operating system and stops the malware from being detected.

The importance of good training
In The Empire Strikes Back, Luke had to decide between sticking with his Jedi training or rescuing Han Solo and Princess Leia. Despite his masters advising him against it, he went with the latter. As a result of this, he couldn’t save any of his friends and ended up losing an arm. Perhaps if he had continued with his training he would’ve been better prepared.
Security professionals don’t have to rescue any princesses, but they also can’t afford to let their training be an afterthought. It’s important to always be prepared as cybercriminals are constantly developing new and more sophisticated strategies.

The secret of the Ewoks
Even the loveable Ewoks from The Return of the Jedi have something to show us: they may have only used simple weapons, such as wooden catapults, but that didn’t hold them back.
As a whole, simple security strategies are extremely useful. One of the most basic, the application of various security layers to protect devices, hasn’t lost its use despite ever more complex attacks. If you use different tools, they will each cover the deficiencies of the other.
The post How to be a cybersecurity Jedi – 5 things we’ve learnt from Star Wars appeared first on MediaCenter Panda Security.
Announcing release for Python 2.7, 3.3 and 3.4 on CentOS Linux 6 and 7 x86_64 SCL
I am pleased to announce the immediate availability of versions 2.7, 3.3 and 3.4 of the Python on CentOS Linux 6 x86_64 and CentOS Linux 7 x86_64, delivered via a Software Collection (SCL) built by the SCLo Special Interest Group (https://wiki.centos.org/SpecialInterestGroup/SCLo). QuickStart ---------- You can get started in three easy steps (example of Python 3.4): $ sudo yum install centos-release-scl $ sudo yum install rh-python34 $ scl enable rh-python34 bash At this point you should be able to use python just as a normal application. An examples of commands run might be: $ python my-app.py $ easy_install Flask $ easy_install Django $ bundle In order to view the individual components included in this collection, including additional python modules, you can run: $ sudo yum list rh-python34* About Software Collections -------------------------- Software Collections give you the power to build, install, and use multiple versions of software on the same system, without affecting system-wide installed packages. Each collection is delivered as a group of RPMs, with the grouping being done using the name of the collection as a prefix of all packages that are part of the software collection. The collections rh-python34, python33 and python27 deliver versions 3.4, 3.3 and 2.7 of the Python interpreter, pip installer (except python33, which does not include pip) and some other modules that are also included in the collections as RPMs. For more on the Python, see https://www.python.org/. The SCLo SIG in CentOS ---------------------- The Software Collections SIG group is an open community group co-ordinating the development of the SCL technology, and helping curate a reference set of collections. In addition to the Python collections being released here, we also build and deliver databases, web servers, and language stacks including multiple versions of PostgreSQL, MariaDB, Apache HTTP Server, NodeJS, Ruby and others. Software Collections SIG release was announced at https://lists.centos.org/pipermail/centos-announce/2015-October/021446.html You can learn more about Software Collections concepts at: http://softwarecollections.org You can find information on the SIG at https://wiki.centos.org/SpecialInterestGroup/SCLo ; this includes howto get involved and help with the effort. We meet every second Wednesday at 16:00 UTC in #centos-devel (ref: https://www.centos.org/community/calendar), for an informal open forum open to anyone who might have comments, concerns or wants to get started with SCL's in CentOS. Enjoy! Honza SCLo SIG member
Announcing release for Ruby 1.9.3, 2.0.0, 2.2 and Ruby on Rails 3.2, 4.0, 4.1 on CentOS Linux 6 x86_64 SCL
I am pleased to announce the immediate availability versions 1.9.3, 2.0.0, and 2.2 of the Ruby, and versions 3.2, 4.0 and 4.1 of the Ruby on Rails, now also on CentOS Linux 6 x86_64, delivered via a Software Collection (SCL) built by the SCLo Special Interest Group (https://wiki.centos.org/SpecialInterestGroup/SCLo). This is an addition for the Ruby collections that are already available for CentOS 7 (https://lists.centos.org/pipermail/centos-announce/2015-November/021501.html). QuickStart ---------- You can get started in three easy steps (example of Ruby 2.2 and Ruby on Rails 4.1): $ sudo yum install centos-release-scl $ sudo yum install rh-ruby22 rh-ror41 $ scl enable rh-ruby22 bash At this point you should be able to use ruby just as a normal application. An examples of commands run might be: $ ruby my-app.rb $ gem install activeresource $ bundle In order to view the individual components included in this collection, including additional rubygems plugins, you can run: $ sudo yum list rh-ruby22* rh-ror41* The rh-ror41 collection relies on the rh-ruby22 collection and the ror40 collection relies on the ruby200 collection, so the Ruby collections will be also installed when the Ruby on Rails collection is installed. About Software Collections -------------------------- Software Collections give you the power to build, install, and use multiple versions of software on the same system, without affecting system-wide installed packages. Each collection is delivered as a group of RPMs, with the grouping being done using the name of the collection as a prefix of all packages that are part of the software collection. The collection rh-ruby22 delivers bundler and version 2.2 of the Ruby interpreter, while the collection rh-ror41 delivers version 4.1 of the Ruby on Rails framework that allows to create and run applications in Ruby or Ruby on Rails framework. The collection ruby200 delivers version 2.0.0 of the Ruby interpreter, while the ror40 collection delivers version 4.0 of the Ruby on Rails framework and bundler. The collection ruby193 delivers version 1.9.3 of the Ruby interpreter, bundler and version 3.2 of the Ruby on Rails framework. Some of the most common rubygems are also included in the collections as RPMs, the rest may be installed using bundler or gem tools. For more on the Ruby and Ruby on Rails, see https://www.ruby-lang.org, http://rubyonrails.org or https://rubygems.org. The SCLo SIG in CentOS ---------------------- The Software Collections SIG group is an open community group co-ordinating the development of the SCL technology, and helping curate a reference set of collections. In addition to the Ruby and Ruby on Rails collections being released here, we also build and deliver databases, web servers, and language stacks including multiple versions of PostgreSQL, MariaDB, Apache HTTP Server, NodeJS, Python and others. Software Collections SIG release was announced at https://lists.centos.org/pipermail/centos-announce/2015-October/021446.html You can learn more about Software Collections concepts at: http://softwarecollections.org You can find information on the SIG at https://wiki.centos.org/SpecialInterestGroup/SCLo ; this includes howto get involved and help with the effort. We meet every second Wednesday at 16:00 UTC in #centos-devel (ref: https://www.centos.org/community/calendar), for an informal open forum open to anyone who might have comments, concerns or wants to get started with SCL's in CentOS. Enjoy! Honza SCLo SIG member
Australian parents’ concerns differ from kids’ actual behavior online
When it comes to protecting your children online, knowledge of risks is vital. With this in mind, ESET asked Australian parents about their main concerns.
The post Australian parents’ concerns differ from kids’ actual behavior online appeared first on We Live Security.
![]()
Star Wars: A New Hope – 5 information security lessons
If you are looking to boost your cybersecurity prowess, then make some time for the first Star Wars film, A New Hope. You’d be surprised at what this hugely popular and successful movie has to offer.
The post Star Wars: A New Hope – 5 information security lessons appeared first on We Live Security.
![]()
19-Year-Old Teen Steals $150,000 by Hacking into Airline's Website
What do you do to earn up to $150,000?
Somebody just hacks into airlines and sells fake tickets.
That’s exactly what a 19-year-old teenager did and made approximately 1.1 Million Yuan (£110,000 or $150,000) by hacking into the official website of an airline and using the stolen booking information to defraud hundreds of passengers.
<!– adsense –>
The teenager, identified as Zhang
![]()
Bad Santa! Microsoft Offers — 'Upgrade now' or 'Upgrade tonight' to Push Windows 10
Many Windows 7 and Windows 8.1 users don’t want to upgrade their machines to Microsoft’s newest Windows 10 operating system now or anytime soon. Isn’t it?
But what if you wake up in the morning and found yourself a Windows 10 user?
<!– adsense –>
That’s exactly what Microsoft is doing to Windows 7 and 8.1 users.
Windows 10 Upgrade Becomes More Aggressive
Ever since Microsoft
![]()
