It only took Apple 24 hours to get 4 million pre-orders of the new iPhone 6, and scammers were right there with them to cash in.
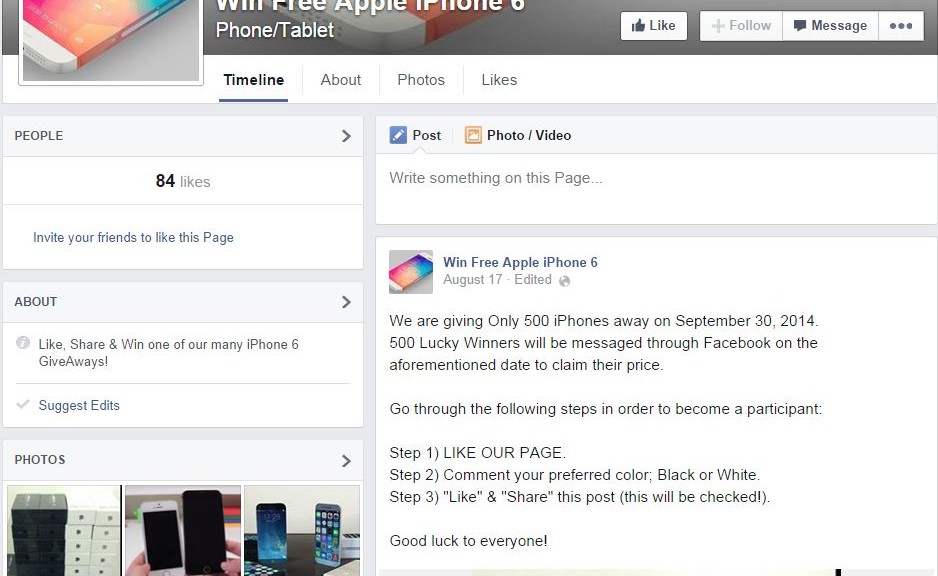
This example of a like-harvesting scam page promises an iPhone 6 giveaway.
In the newest iteration of a scam used every time a new product is launched with fanfare, Facebook pages have been popping up claiming that people who like, share, and comment on a post can win an iPhone 6.
This type of scam is referred to as like-harvesting. The scammer makes the page popular by collecting likes and then sells the page to other scammers. The offer of a new device, like the iPhone 6, entices people to click the like button then spam their friends with the bogus promotion. Thousands of likes can accumulate within a few hours, making the page quite valuable on the black market. The new owner rebrands it to peddle more questionable products and services with their built-in audience.
A variation on this scam is the Survey Scam. As with like-harvesting, you must first like the Facebook page. The difference is that you need to also share a link with your Facebook friends.
This link takes you to a page where you are instructed to download a “Participation Application.†Generally, a pop-up window leads you to participate in a survey before you can download the application. Some surveys will ask for personal information like your mobile phone number or name and address. If you provide those details, you open yourself up to expensive text-messaging services, annoying phone calls, and junk mail. In some cases, the download contains malicious code. The only thing you can be guaranteed not to get is an iPhone 6! Meanwhile, the scammer earns money for every survey through an affiliate marketing scheme.
What to do if you liked a ‘Win iPhone 6′ page
If you fell for the scam, then learn from it and don’t do it again! Make sure you unlike the page, delete comments that you made, and remove the post from your news feed. You may also want to alert your friends to the scams, so they don’t fall for it.
Thank you for using avast! Antivirus and recommending us to your friends and family. For all the latest news, fun and contest information, please follow us on Facebook, Twitter and Google+. Business owners – check out our business products.