The University of Texas information security office disclosed details of a vulnerability in remote management software Webmin that could allow someone to remotely delete files on a host server.
All posts by 007admin
Apache Warns of Tomcat Remote Code Execution Vulnerability
Some older versions of Apache Tomcat, the company’s open source web server and servlet container, are vulnerable to remote code execution.
MH17 plane crash victims exploited by cold-hearted scammers
When Malaysia Airlines Flight 17 (MH17) was shot down in Ukrainian airspace in July of this year, the world was understandably shocked.
The news of an civilian passenger flight from Amsterdam to Kuala Lumpur being possibly downed by a surface-to-air missile was horrifying enough, but coming just months after the loss of another Malaysian Airlines flight (MH370) in mysterious circumstances made the headlines seemed even harder to believe.
As we have previously documented on We Live Security, the earlier lost aircraft has been the subject of various scams including a fraudulent message that spread on Facebook claiming it had been found, a fake video of the supposed rescue of its passengers, as well as claims that hackers had stolen secret classified documents held by Malaysian government officials.
Now it appears, the cold-hearted scammers are exploiting the tragic events that befell MH17 over Ukraine too.
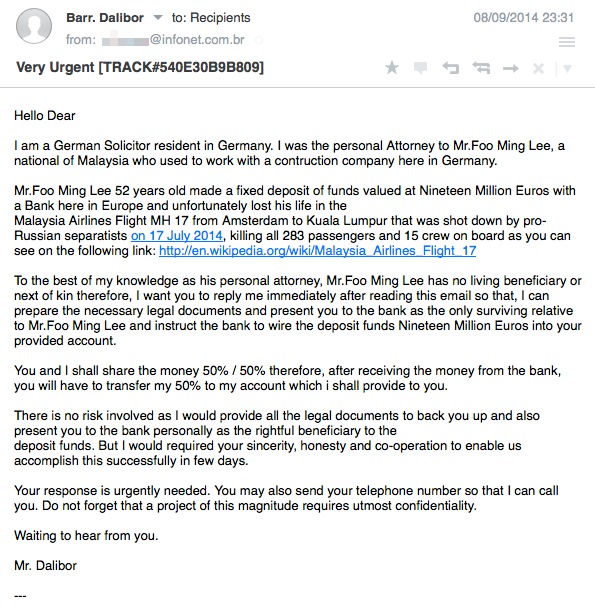
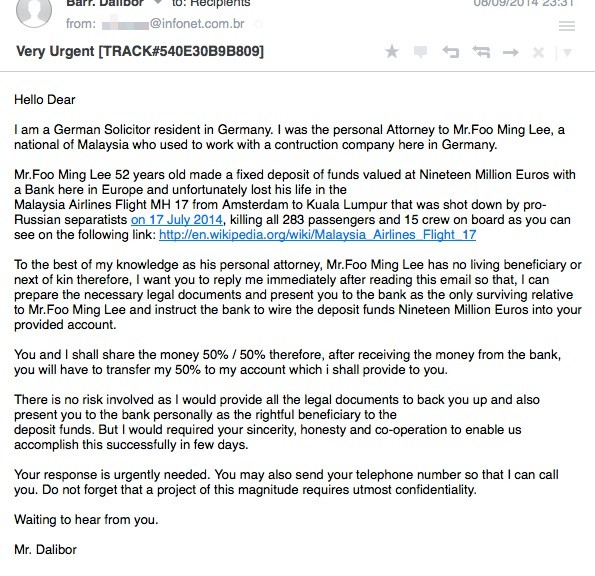
Part of the spammed out message reads as follows:
<blockquote style=”margin: 15px;padding: 15px 15px 5px;border-left: 5px solid #ccc;font-size: 13px;
font-style: normal;font-family: ‘Helvetica Neue’, Helvetica, sans-serif;line-height: 19px;”>
I am a German Solicitor resident in Germany. I was the personal Attorney to Mr.Foo Ming Lee, a national of Malaysia who used to work with a contruction company here in Germany.
Mr.Foo Ming Lee 52 years old made a fixed deposit of funds valued at Nineteen Million Euros with a Bank here in Europe and unfortunately lost his life in the
Malaysia Airlines Flight MH 17 from Amsterdam to Kuala Lumpur that was shot down by pro-Russian separatists on 17 July 2014, killing all 283 passengers and 15 crew on board as you can see on the following link: http://en.wikipedia.org/wiki/Malaysia_Airlines_Flight_17
To the best of my knowledge as his personal attorney, Mr.Foo Ming Lee has no living beneficiary or next of kin therefore, I want you to reply me immediately after reading this email so that, I can prepare the necessary legal documents and present you to the bank as the only surviving relative to Mr.Foo Ming Lee and instruct the bank to wire the deposit funds Nineteen Million Euros into your provided account.
Yes, it’s “yet another 419 scam”.
Also commonly known as “Letters from Nigeria” or “Advanced Fee Fraud”, the scams typically involve the promise of a vast fortune – but sooner or later (once you have begun to be sucked in and lost all wariness) you will be told that you need to advance an amount of money for logistical reasons, or share sensitive information such as your passport or banking details.
You might not fool for a scam like this, but unfortunately there are plenty of vulnerable people out there who do. And it only requires one person to fool for the scam for it to be worthwhile to the fraudsters, who have typically spammed it out to thousands.
But what makes this scam particularly sick is that it uses the name of a genuine victim of the MH17 tragedy.
As media reports confirm, Foo Ming Lee, who lived in Geneva and was a sales and marketing chief for a Japanese tobacco company, was indeed a passenger on MH17 and was amongst the 43 Malaysians who perished in the downing of MH17 over Ukraine.
It’s clear that whoever is behind this scam has scooped up the name of a victim from media reports, and exploited it in an attempt to defraud the unwary.
After all, anyone who was dubious about the unsolicited message might Google some of the details in an attempt to confirm if any elements of it could be confirmed to be true or not.
Yes, the plane crash happened on the date the scam claims, and Mr Foo Ming Lee was amongst the victims.
What is not true, however, is the claim that he had no next of kin. Another news report confirms that his widow, son and daughter laid his ashes to rest at Nirwana Memorial Park on August 24th.
If scammers had any conscience, they wouldn’t compound the misery of those who have been left bereaved and heartbroken by using the names of victims and details of horrendous accidents and tragedies in their money-making plots.
But the sad truth is that the scammers and fraudsters don’t have any conscience, and are prepared to do anything if it might net them a rich reward.
Hat-tip: Thanks to ESET researcher Pierre-Marc Bureau for bringing this scam to my attention.
The post MH17 plane crash victims exploited by cold-hearted scammers appeared first on We Live Security.
![]()
Bitcoin creator – could he be ‘outed’ after email ransom?
Bitcoin creator ‘Satoshi Nakamoto’ – a pseudonym – could be about to have his identity made public, after a series of odd emails from the address that has been his only point of contact with the world after he ‘went dark’ in 2011, according to a report in Forbes.
Someone claiming to be a hacker has access to “[email protected]â€, and has posted a threat to Pastebin, saying that he would “de-anonymize†the mysterious Bitcoin creator for a ransom of 25 Bitcoins.
The threat says, “Releasing the so called “gods” dox if my address hits 25 BTC.And no, this is not a scam.†A series of mysterious emails from the Bitcoin creator’s supposed address, reported by Vice.com, have done little to clear up the mystery.
A test email from We Live Security found that the address is now delivering a “mailbox unavailable†error message.
Bitcoin creator: Mystery emails
One colleague received a threat to “hitman†him from the account, which Forbes reports drily as not being in the “usual style†of the cryptocurrency founder.
The identity of ‘Satoshi Nakamoto’ who handed over control of the site to a developer nearly four years ago, has been hot property since Newseek incorrectly identified a man, Dorian Nakamoto, as beeing the mysterious developer of the cryptocurrency.
Forbes reports that the email address has lain dormant since 2011, since ‘Nakamoto’ ceased corresponding with people via the address. The magazine speculates that the GMX.com addresss may have fallen dormant through disuse, and been opened up to another user, as GMX’s terms of service specify that accounts can be “terminated†after that time.
Threat to “hitman” colleague
Things got yet more mysterious when two separate people appeared to correspond with Motherboard at Vice from the same address. One sent a screenshot showing an Inbox with 11,000 emails.
The site writes, “Motherboard was able to communicate with two individuals who have access to Nakamoto’s old email address. The first said he was only browsing Nakamoto’s for fun. The second not only claimed to be the real hacker of the account, but also said the first person we spoke with was Nakamoto himself.â€
The series of emails, chronicled by Vice, become increasingly cryptic as the supposed hacker denies he is associated with the Pastebin post.
One of the concluding emails thickens the plot still further. Asked if he is sure that the other individual with access is definitely Satoshi, the hacker replies, “Satoshi is smart and will have tried to put the people looking for him on the wrong path. This is why I can’t be sure.â€
The post Bitcoin creator – could he be ‘outed’ after email ransom? appeared first on We Live Security.
![]()
Nude Celebs, Target, Home Depot: Who is to blame? Criminals!
Celebgate, the leaking of nude photos of celebrities from iCloud that started in August, continues to make headlines but now has competition from another big cybercrime story. The compromise of payment card data at Home Depot is emerging under headlines that make comparisons with another huge retail breach, as in: “bigger than Target?†What’s the connection between the sleazy creeps who hack private online storage accounts to share the contents thereof and folks who hack into point-of-sale systems to steal and sell payment card data? They are all criminals, a fact that is too often overlooked in the angry aftermath of the data breach du jour.
Blaming Cybercrime Victims
As the Celebgate story was emerging I received an interview request from a journalist with the Hungarian edition of CHIP magazine. His first question was: “Who’s responsible for the latest Apple iCloud ‘celebrity nude pictures leak’ scandal and why?†My response went something like this: The correct answer to this question is people, not technology. I continued:
The creepy people who stole the pictures are the ones responsible for this scandal and they should be held accountable. For some strange reason, the world tends to approach computer security differently from physical security. If you forget to lock your car, that does not make you responsible for it being stolen. The car thief is clearly the only person truly responsible. To think that any party other than the sleazy criminals who exposed private information is responsible is to condone their actions.
I was not just saying this to differentiate my analysis from that of actress and Celebgate victim Kirsten Dunst. I’m sure most people have seen headlines like this: “Kirsten Dunst Slams Apple After Alleged Nude Photo Leak: blames iCloud for photo hacking†(Hollywood Life). Much as I admire Ms. Dunst as an actress and sympathize with her entirely justified outrage at this incident, I don’t agree that Apple is to blame, any more than I would blame BMW if my car was stolen. Of course, any company whose business model involves handling sensitive private information has a responsibility to protect it. But persons who work to defeat those protections and then violate the privacy of that information are, in that case, the persons to blame, the responsible party. We must not forget that Target and Home Depot are victims of cybercrime, just as Ms. Dunst and other celebrities whose private photos were exposed are victims of cybercrime, whatever the passwords protecting their accounts happened to be.
To think that any party other than the sleazy criminals who exposed private information is responsible is to condone their actions. I say this because to say otherwise is to go down a road best avoided. Consider Apple’s reaction to Celebgate: they have instituted improved security measures. What if we fast forward 12 months and hear that, once again, a determined group of sick-minded perverts has defeated those enhanced security measures and exposed another batch of private pictures. Is Apple still responsible? Before you answer, let’s consider the Home Depot hack. Reports so far indicate that the criminals used an enhanced version of the malware deployed to steal tens of millions of payment card records from Target stores. The response from Target includes a commitment to use EMV cards in the future. EMV cards contain a chip and are much harder for criminals to replicate, making the conversion of stolen card data into cash more challenging. But notice that I’m saying “harder, more challenging†but not impossible.
In other words, unless human nature experiences a sudden and unprecedented global upgrade, some people somewhere will always be trying to defeat security measures for their own ends. A certain number will always succeed, so the trick is to reduce that number. And that is why societies put in place policies and allocate resources to deter criminal activity, notably through the detection, identification, apprehension, prosecution, and punishment of persons deemed to be criminal perpetrators. If any party other than the criminals is to blame for Celebgate and the Target and Home Depot hacks I would say it is society for failing to devote enough resources to the deterrence of cybercrime.
Cybercrime and Society
Sure, many companies and consumers could do a better job of protecting the information systems they use, from changing the default password on point of sale devices, to using stronger passwords on our accounts than 123456 (which recently replaced password as the most widely used password, according to an analysis of millions of compromised records – see this paper on password advice to choose something better).
In recent years a lot of useful advice on how to improve our digital security has been made freely available. The federal government publishes a wide range of guides to best practices, including the comprehensive Framework for Improving Critical Infrastructure Cybersecurity from NIST (the National institute of Standards and Technology).
So why don’t more organizations do a better job at security? There are many reasons, cost being the most obvious, but failing to fit your front door with an expensive pick-proof lock does not make you responsible for a burglary or home invasion; there seems to be broad consensus that responsibility for those crimes rests with any criminal who chooses to violate your physical space. Violations of private virtual space should be considered equally criminal, and violators should be vigorously pursued.
America has well-established measures in place for responding to such physical crimes, from tracking down the perpetrators to arresting, prosecuting, and punishing them. And America’s efforts to deter traditional physical crime appear to be effective when you look at the number of bank robberies each year and the average amount of loot they yield. Both numbers are gradually declining: from 7,644 incidents yielding an average of $10,000 in 2003 to 5,086 incidents yielding $7,539 in 2011 (based on FBI reporting).
When it comes to computer fraud, the graph is a steep line going in the opposite direction: up from $125 million in 2003 to $781 million in 2013 (based on Internet Crime Complaint Center reporting, in conjunction with the FBI). So where is the effort to deter cybercrime? And where is it located on the list of national priorities? Clearly there are some law enforcement resources devoted to catching and prosecuting cybercriminals. We have seen a number of high profile arrests already this year (and I expect to see more). I have seen some very impressive computer forensics conducted by law enforcement at the local, national, and international levels.
What I don’t see are sufficient resources deployed to fight cybercrime at anything like the scale on which such crime is being conducted. In no way is this a criticism of the folks in the field who are knocking on doors and dissecting hard drives. I just don’t think there are enough of them. An in-depth academic study of cybercrime put the annual global law enforcement spend on the fight against cybercrime at $400 million in 2010 (Anderson, Barton, Bohme, Clayton, van Eeten, Levi, Moore, Savage. 2012). In speaking with one of the authors of that study, I found that about half of that figure, $200 million, was U.S. spending. Compare that to the FBI’s total budget request for fiscal year 2015: $8.3 billion.
Now compare that number to the $21 billion budget for the espionage activities of the NSA/NRO, which is on top of the $14.7 billion we shell out for whatever the CIA does these days. Now look at the staffing levels funded in the 2015 FBI budget request: 34,970 permanent positions including 13,050 special agents. Compare that with the FBI’s 2014 request for $8.4 billion to cover 34,787 permanent positions including 13,082 special agents. By my count, that $100 million less in spending, and a reduction in force of 32 special agents.
I’m a security professional and not a budget analyst, but to me those numbers don’t seem consistent with a firm national resolve to tackle cybercrime. So, speaking as a security professional, I suggest that the next time a major IT security breach hits the headlines, we take a break from blaming the victims, and that includes people who use weak passwords on their accounts or companies who have holes in their security systems. Let’s put some of that anger and outrage into lobbying our government to take more decisive action against cybercrime and the people who perpetrate it.
Disagree? Leave a comment and let me know what you think. BTW, here’s a link to the FBI’s most wanted cyber criminal page. ÂThe post Nude Celebs, Target, Home Depot: Who is to blame? Criminals! appeared first on We Live Security.
![]()
Facebook offers a new tool for configuring privacy

As Facebook is always changing, keeping your profile private and secure is a complicated and time consuming task. The social network therefore, aware that this could put many users off sharing their news with contacts, has developed a new tool to simplify the job.
With this new feature, a friendly blue dinosaur helps you to quickly and simply check which of your contacts can see your latest posts.
To access it you have to click the padlock symbol in the top right of the screen and select “Privacy checkup”

A dialog box then opens with three simple steps.
How to configure privacy settings in Facebook
- The first option lets you control who can see your posts when you update your status from the news section or from the wall. As well as telling you the current settings, you can also change them to suit your preferences
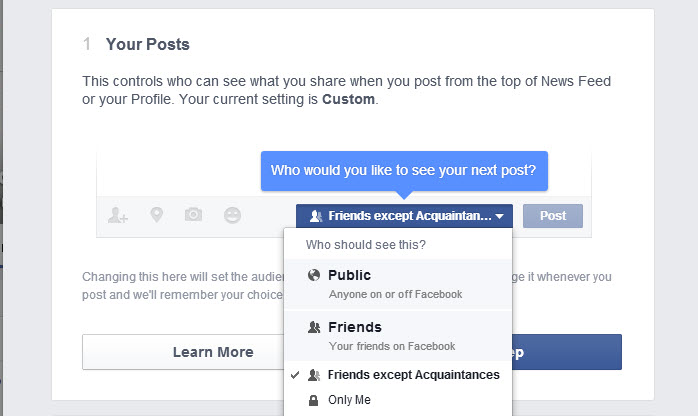
- The next step displays a list of all the applications that can access your profile and information. Here you can also prevent this access if you no longer use the application in question. What’s more you can see which of your contacts can see posts that the applications publish ​​in your name.
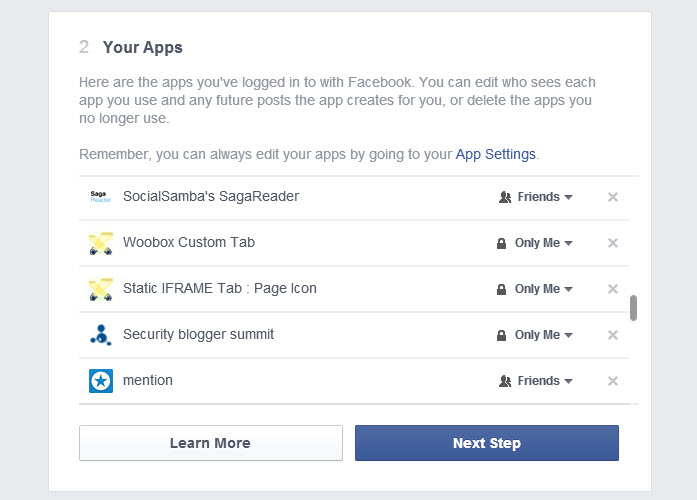
- Finally, Facebook helps you check which personal information you’re sharing on your profile: your job, school and college background, where you live … you can add or delete data and restrict access to it.
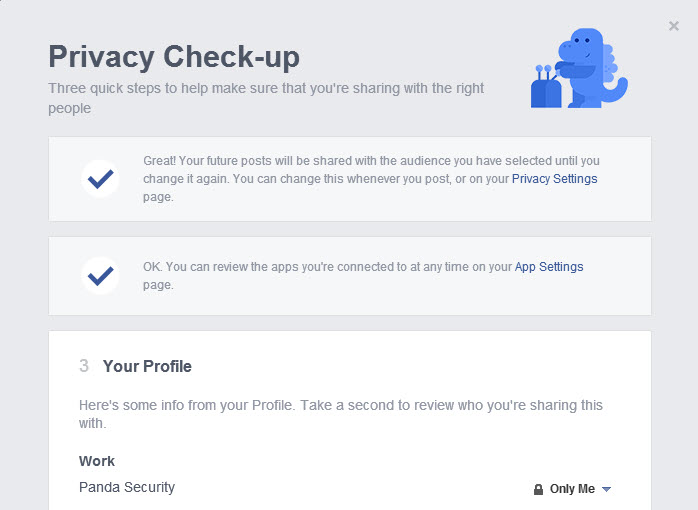
Although none of these settings prevent Facebook from using your personal information for advertising, it can help you know which contacts can see which posts.
At present this help feature does not include settings for albums or photos as a profile or homepage, which you will have to check directly.
If after meeting Facebook’s new dinosaur you still have questions about the privacy settings of your profile, you can always check our guide.
More | Facebook Privacy Guide
The post Facebook offers a new tool for configuring privacy appeared first on MediaCenter Panda Security.
Online ad threat – Yahoo, Amazon, YouTube ‘victims of malvertising’
Anyone who has visited popular domains such as YouTube.com, Amazon.com or Ads.Yahoo.com could be a victim of a new, mutating malware attack distributed through the online ad network adverts displayed on the sites, according to a new blog by networking specialist Cisco.
The blog describes how the online ad malware (which comes in two forms, one for PC, one for Mac), is distributed via online advertising networks – basically by conning one of the large companies whose ads are seen on thousands of sites into forwarding an ad with a malicious payload.
The Register describes the process as, “The high-profile serving domains – along with many others – are, of course, receiving the “malvertising†from online ad networks that have been tricked into hosting the attack content.â€
Online ad threat: How it works
The Cisco bloggers say that a number of major domains, listed in their original blog post, have been affected by the current attack. The attack has been nicknamed Kyle and Stan, due to the naming scheme of the subdomains within the group – “stan.mxp2099.com†and “kyle.mxp2038.comâ€.
Threatpost reports that the likely size of the attack is probably much larger than the 700 domains analyzed by Cisco, and says, “700 domains and nearly 10,000 users have hit these domains and been exposed to the malicious advertisements.â€
Threatpost points out that the attack vector is not new – the New York Times has previously fallen victim to a malvertising campaign – but that ‘Kyle and Stan’ takes a unique approach.
Cisco says that the attack delivers a unique malicious payload for every visitor, packaged with a legitimate media player, and a piece of malware which is tailored to each user.
 “Extremely effective attack”
“The idea is very simple: use online advertising to spread malware. This attack form is not new, but extremely effective,†Cisco says.
“The world of online ads has only a few major players. If an attacker can get one of those major online ad networks to display an advertisement with a malicious payload just for a few minutes without being detected, then countless machines can be infected by such an attack.â€
The attack comes in various forms, Cisco reports, but so far relies on pure social-engineering, rather than ‘drive-by downloads’ where users who don’t click are infected. Different malware packages are delivered according to platform and user, and the attack is evolving, the bloggers warn.
A discussion of the murky world of malvertising, adware and ‘badware’ by ESET researcher Joan Calvet can be found here.
The post Online ad threat – Yahoo, Amazon, YouTube ‘victims of malvertising’ appeared first on We Live Security.
![]()
TLS landscape
Transport Layer Security (TLS) or, as it was known in the beginnings of the Internet, Secure Sockets Layer (SSL) is the technology responsible for securing communications between different devices. It is used everyday by nearly everyone using the globe-spanning network.
Let’s take a closer look at how TLS is used by servers that underpin the World Wide Web and how the promise of security is actually executed.
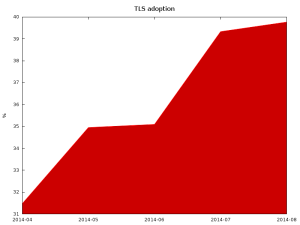
Adoption
Hyper Text Transfer Protocol (HTTP) in versions 1.1 and older make encryption (thus use of TLS) optional. Given that the upcoming HTTP 2.0 will require use of TLS and that Google now uses the HTTPS in its ranking algorithm, it is expected that many sites will become TLS-enabled.
Surveying the Alexa top 1 million sites, most domains still don’t provide secure communication channel for their users.
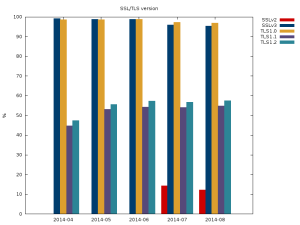
Additionally, if we look at the version of the protocol supported by the servers most don’t support the newest (and most secure) version of the protocol TLSv1.2. Of more concern is the number of sites that support the completely insecure SSLv2 protocol.
(There are no results for SSLv2 for first 3 months because of error in software that was collecting data.)
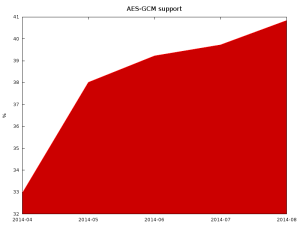
One of the newest and most secure ciphers available in TLS is Advanced Encryption Standard (AES) in Galois/Counter Mode (AES-GCM). Those ciphers provide good security, resiliency against known attacks (BEAST and Lucky13), and very good performance for machines with hardware accelerators for them (modern Intel and AMD CPUs, upcoming ARM).
Unfortunately, it is growing a bit slower than TLS adoption in general, which means that some of the newly deployed servers aren’t using new cryptographic libraries or are configured to not use all of their functions.
Bad recommendations
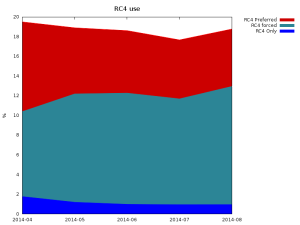
A few years back, a weakness in TLS 1.0 and SSL 3 was shown to be exploitable in the BEAST attack. The recommended workaround for it was to use RC4-based ciphers. Unfortunately, we later learned that the RC4 cipher is much weaker than it was previously estimated. As the vulnerability that allowed BEAST was fixed in TLSv1.1, using RC4 ciphers with new protocol versions was always unnecessary. Additionally, now all major clients have implemented workarounds for this attack, which currently makes using RC4 a bad idea.
Unfortunately, many servers prefer RC4 and some (~1%) actually support only RC4. This makes it impossible to disable this weak cipher on client side to force the rest of servers (nearly 19%) to use different cipher suite.
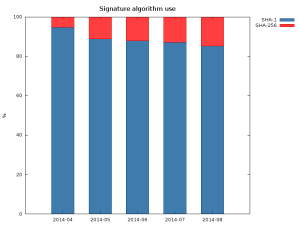
The other common issue, is that many certificates are still signed using the obsolete SHA-1. This is mostly caused by backwards compatibility with clients like Windows XP pre SP2 and old phones.
The sudden increase in the SHA-256 between April and May was caused by re-issuance of certificates in the wake of Heartbleed.
Bad configuration
Many servers also support insecure cipher suites. In the latest scan over 3.5% of servers support some cipher suites that uses AECDH key exchange, which is completely insecure against man in the middle attacks. Many servers also support single DES (around 15%) and export grade cipher suites (around 15%). In total, around 20% of servers support some kind of broken cipher suite.
While correctly implemented SSLv3 and later shouldn’t allow negotiation of those weak ciphers if stronger ones are supported by both client and server, at least one commonly used implementation had a vulnerability that did allow for changing the cipher suite to arbitrary one commonly supported by both client and server. That’s why it is important to occasionally clean up list of supported ciphers, both on server and client side.
Forward secrecy
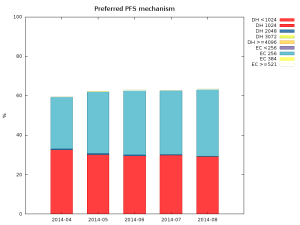
Forward secrecy, also known as perfect forward secrecy (PFS), is a property of a cipher suite that makes it impossible to decrypt communication between client and server when the attacker knows the server’s private key. It also protects old communication in case the private key is leaked or stolen. That’s why it is such a desirable property.
The good news is that most servers (over 60%) not only support, but will actually negotiate cipher suites that provide forward secrecy with clients that support it. The used types are split essentially between 1024 bit DHE and 256 bit ECDHE, scoring respectively 29% and 33% of all servers in latest scan. The amount of servers that do negotiate PFS enabled cipher suites is also steadily growing.
Summary
Most Internet facing servers are badly configured, sometimes it is caused by lack of functionality in software, like in case of old Apache 2.2.x releases that don’t support ECDHE key exchange, and sometimes because of side effects of using new software with old configuration (many configuration tutorials suggested using !ADH in cipher string to disable anonymous cipher suites, that unfortunately doesn’t disable anonymous Elliptic Curve version of DH – AECDH, for that, use of !aNULL is necessary).
Thankfully, the situation seems to be improving, unfortunately rather slowly.
If you’re an administrator of a server, consider enabling TLS. Performance issues when encryption was slow and taxing on servers are long gone. If you already use TLS, double check your configuration preferably using the Mozilla guide to server configuration as it is regularly updated. Make sure you enable PFS cipher suites and put them above non-PFS ciphers and that you as well as the Certificate Authority you’ve chosen, use modern crypto (SHA-2) and large key sizes (at least 2048 bit RSA).
If you’re a user of a server and you’ve noticed that the server doesn’t use correct configuration, try contacting the administrator – he may have just forgotten about it.
Virus Bulletin, AVAR conferences: a tasty Conference Pair*
It’s that time of year. That is, the time for two of my favourite security conferences: Virus Bulletin and AVAR.
Sadly, I’m unable to attend the 2014 Virus Bulletin conference, taking place in Seattle 24th-26th September, but there’s a healthy sprinkling of ESET researchers on the programme, which now includes information on the seven last-minute presentations.
On Wednesday 24th at 11.30, ESET Canada’s Pierre-Marc Bureau co-presents a paper with Evgeny Sidorov and Konstantin Otrashkevich from the Yandex Safe Search team on Ebury and CDorked. Full disclosure. This is an area ESET research blogging has focused on for quite a while.
Also on Wednesday, at 14.30, ESET Canada researcher Jean-Ian Boutin presents his paper about The evolution of webinjects. And at 17.00, Matias Porolli and Pablo Ramos deliver a presentation about Brazilian malware trends: CPL in the spotlight.
On Thursday 25th at 12.00, it’s the turn of Robert Lipovsky and Anton Cherepanov with their last minute paper on Back in BlackEnergy: 2014 targeted attacks in the Ukraine and Poland.
And among the four reserve papers you’ll find Bootkits: past, present & future, written by ESET’s Eugene Rodionov, Intel’s Aleksandr Matrosov (formerly of ESET), and myself: this is my 15th Virus Bulletin conference paper. 🙂 Because it’s a reserve paper, it’s not in the programme, but if needed, it will be presented by Eugene and Alex. It’s partly based on research for their forthcoming book on bootkits, to which I’m delighted to be making a small contribution.
There are, of course, lots of other presentations I’d love to have heard: here are just a few of those that strike me as being particularly interesting:
- Malware Investigator by the Federal Bureau of Investigation’s Jonathan Burns
- The three levels of exploit testingby Richard Ford and Marco Carvalho (Florida Institute of Technology)
- Tech Support Scams 2.0: an inside look into the evolution of the classic Microsoft tech support scam by Jérôme Segura (Malwarebytes)
- Microsoft Anti-Virus – extortion, expedience, or the extinction of the AV industry: the jury has reached a verdict by my one-time colleague and frequent co-presenter, Randy Abrams (NSS Labs)
- Inevitably, a couple of Apple-related presentations: Methods of malware persistence on Mac OS X by Synack’s Patrick Wardle, and Apple without a shell – iOS under targeted attack by FireEye’s Tao Wei, Min Zheng, Hui Xue and Dawn Song
- And two very different presentations from Kaspersky: How I hacked my own house! by David Jacoby and OPSEC for security researchers by Vicente Diaz and Dani Creus
This is the first time I’ll have missed a VB since 2007 (I have been to 14 since 1996, though, so I can’t complain too bitterly), and I’ll miss the face-to-face contact with all my friends inside and outside the security industry (not to mention the VB team), but I hope to make the next one in 2015. And I am looking forward to my first AVAR in several years. Again, ESET will be well-represented.
- Peter Kosinar presents his paper on Stealing the internet, one router at a time
- Sébastien Duquette presents his paper on Exploitation of CVE-2014-1761 in targeted attack campaigns
- I’ll be presenting my paper with Sebastian Bortnik on Lemming Aid and Kool Aid: Helping the Communityto help itself through Education
Unfortunately, there are no abstracts to link to at the moment, but there will be plenty of speakers there from other sectors of the security community who can be relied on to deliver good presentations.
*Yes, it’s another fruitful Harley pun.
David Harley
ESET Research Fellow
The post Virus Bulletin, AVAR conferences: a tasty Conference Pair* appeared first on We Live Security.
![]()
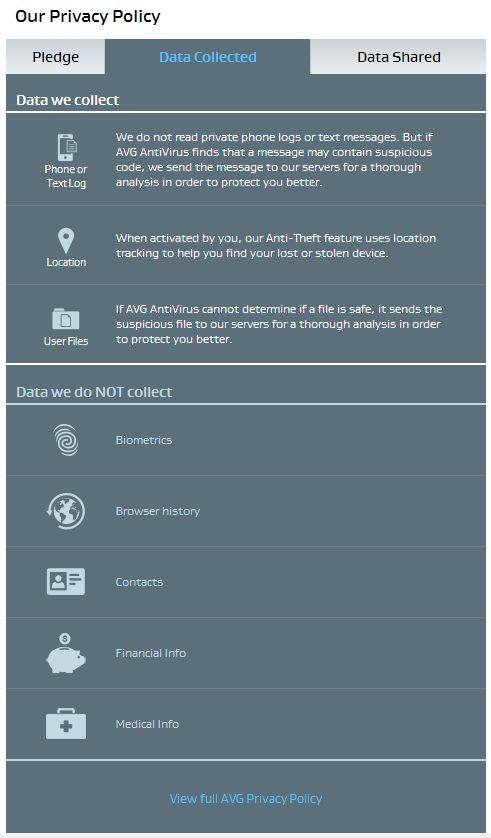
AVG makes privacy crystal clear with Short Privacy Notice
In our connected world, mobile technology is an integral part of daily living. Apps help us find the stores we are looking for, meet our friends at the right time and place, and keep us safe online. We trust these apps with our personal information in exchange for these services, which are often free. Sometimes we share sensitive information with the app in order to optimize that service. But do we ever think about what these apps do with the data they collect, and do we really know why they collect it?
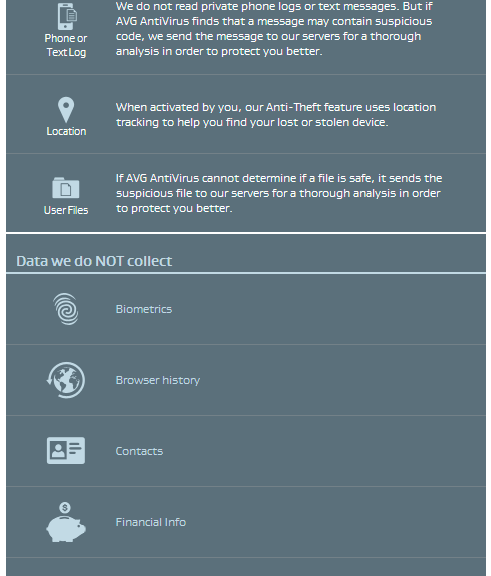
At AVG, we believe that building trust in relationships is important. Transparency is a key element to build that trust which means you have to know what’s going with the data behind the app. The mobile environment is even more challenging because of the limited space and form factor. We’ve been innovating in this area to better show users what data is collected and how it is used. We’ve done this with initially with a Short Data Privacy Notice that tells our customers in a clear, straightforward, and transparent way what our apps collect and share in an easy to read form. Today I am delighted to tell you that the AVG Short Data Privacy Notice has been launched on our following apps: AVG AntiVirus FREE for Android, AVG Privacy Fix and AVG Cleaner for Android. Overtime we expect this approach will become the standard in mobile and desktop environments.
This simple-to-use feature is accessed from the corner menu of the app main screen. To ensure full transparency for all our customers, we still give quick and easy access to our full privacy policy notice at the bottom of each page of the AVG Short Data Privacy Notice.
In the video below, AVG’s Chief Legal Officer Harvey Anderson explains how to use the AVG Short Data Privacy Notice and what we disclose to you through it.
![]()
![]()