All posts by 007admin
A Google Site Meant To Protect You Is Helping Hackers Attack You
Google Accelerates End Of SHA-1 Support, Certificate Authorities Nervous
Secure password: CyberVor hoard of 1.2 billion details ‘used in attack’
Hosting provider Namecheap has come under attack from hackers apparently using the “CyberVor†hoard of 1.2 billion usernames and passwords, and has warned that some accounts that had failed to use a secure password may have been compromised.
In a blog post entitled, “Urgent Security Warningâ€, the company said that some accounts had been compromised, but Computer World reports that the “vast majority†of login attempts had failed.
Namecheap said that it was now “aggressively blocking†the IP addresses that the attack appeared to have come from, and said that the logins appeared to come from the record-breaking hoard of passwords and usernames stolen by the gang known as “CyberVorâ€.
Secure password: Record-breaking hoard used in attack
Veteran security writer and researcher, and We Live Security contributor Graham Cluley said, “The gang, which has been dubbed “CyberVor†(“vor†means “thief†in Russian) by security researchers, is thought to be in possession of the largest known haul of stolen internet credentials – 1.2 billion usernames and passwords, together with 542 million email addresses. And the data has been stolen from some 420,000 different websites.â€
Company officials did not reveal why they suspected the credentials being used in the attack were the ones from the Cybervor (“Vor†is Russian for “thiefâ€) trove which was discovered online last month, with a mix of passwords, usernames and email addressses in one online cache, according to CIO magazine.
“Overnight, our intrusion detection systems alerted us to a much higher than normal load against our login systems. Upon investigation, we determined that the username and password data gathered from third party sites, likely the data identified by The Register (i.e. not Namecheap) is being used to try and gain access to Namecheap.com accounts,†Namecheap said, also offering advice for users on how to create a secure password for their accounts.
Fake browser used in mass attack
“The group behind this is using the stored usernames and passwords to simulate a web browser login through fake browser software. This software simulates the actual login process a user would use if they are using Firefox/Safari/Chrome to access their Namecheap account. The hackers are going through their username/password list and trying each and every one to try and get into Namecheap user accounts,” Namecheap said.
Veteran security writer and researcher, and We Live Security contributor Graham Cluley advises, “Whenever you create accounts online you are putting trust in the hands of web developers that they are properly securing your information. The very best you can do is enable additional security measures (such as multi-factor authentication when made available), and ensure that you never reuse the same password nor choose a password that is easy to guess or crack.
“Because one thing is clear: The Russian CyberVor gang may or may not be sitting on one of the largest cybercriminal hauls in history, but unless we all work harder to keep our private information safe and secure, this is not going to be the last time that you’re waking up to newspaper headlines of stolen passwords.”
The post Secure password: CyberVor hoard of 1.2 billion details ‘used in attack’ appeared first on We Live Security.
![]()
Teaching cyber-security from school age
As the Internet increasingly becomes part of our everyday lives and we use new technologies in all areas of our life, there’s an ever greater need for professionals capable of guaranteeing our security in these areas.
However, in a field as new and complex as cyber-security there is still a lack of people prepared to work in it. As we saw recently, in the United States there is already a plan under way to tackle the situation: training army veterans to become cyber-warriors and consequently, helping them to adjust to civilian life again.
Yet this is only one of the solutions put forward, and there are others that take a longer view. To ensure the future of the profession, the only viable plan for the long term involves educating children in this area and stimulating their interest in computing in general and specifically in IT security.
Along such lines, countries like the USA and the UK have projects that will hopefully provide the cyber-warriors of the future.

The UK’s Cyber-Centurion challenge
In the UK in fact, an initiative called Cyber Centurion has been launched to get thousands of youngsters competing in teams in a cyber-security challenge.
The key to the initiative is that young people will be in direct contact with situations that a real cyber-security expert could encounter. In fact, the challenge, which is to be held in two rounds, involves downloading a virtual computer full of vulnerabilities that could present opportunities for a cyber-criminal. What the teams (comprising 4 to 6 youngsters and one adult) have to do is identify these vulnerabilities and patch them as soon as possible.
As this is the first edition of the challenge, there will first be a practice round in October before the two competition rounds. The top six teams will then battle it out in April 2015 in the Grand Final. The winners will be awarded a scholarship at Northrop Grumman, one of the largest defense contractors in the United States and maker of the B-2 stealth bomber who is funding this initiative with a view to uncovering future talents in IT security.
This however isn’t the only cyber-security initiative in the UK. The Cyber Centurion challenge is supported by Cyber Security Challenge UK , a platform funded by the British government that has organized other educational initiatives such as workshops and other challenges in schools, colleges and universities across the UK.
CyberPatriot
In fact, this exciting British initiative is really an adaptation of the US Cyber Patriot program, the National Youth Cyber Education Program. This program is now in its seventh edition and is also funded by Northrop Grumman, which claims to have already dramatically reduced America’s cyber-security talent shortage.
This search for US Cyber Patriots involves three programs:
- A competition among high school students similar to the one that will begin in a few months in the UK (where the teams have to identify and fix vulnerabilities in an operating system to prevent cyber-criminals from entering),
- A camp organized for the first time this summer and which aims to teach the principles of cyber-security in an entertaining way and
- An initiative that will take basic IT security knowledge to primary schools and teach children how to protect themselves on the Internet.
So why in the US and the UK is there so much interest in students learning firsthand what it takes to be a cyber-security professional and not any other job?
Basically, because the future (and the present) will require IT professionals dedicated to cyber-security. Moreover, international threats and attacks can now come across the Internet, so another profession of the (short-term) future will be cyber-warriors, who even now are being recruited by companies like Northrop Grumman. This will no doubt be the army of the future.
The post Teaching cyber-security from school age appeared first on MediaCenter Panda Security.
Labor Day Reflection: The 77% Rule and Women in Tech
You don’t have to be anti-man to be pro-woman.
–Jane Galvin Lewis
Yesterday while I was observing Labor Day, the day set aside to celebrate the social and economic advancement of the American worker in the U.S.— it provided some time to reflect and consider the topic of women in the workforce and specifically pay parity.
What if I gave you 77 cents for every dollar you earned? Would you feel fairly compensated? Unfortunately, that’s generally the wages the average working woman makes as opposed to her male counterparts.
The 77 cents for every dollar? That’s a generalization that averages in all jobs across the board. The good news is that the tech industry is more progressive. Pay parity, according to various surveys, is equal in our industry as long as the job titles are the same.
Of course, the catch is that women aren’t as likely to have the top titles. (For a more in-depth look at this you can go to one survey at Dice.)
Nevertheless, I believe tech is a great place for women and has a rich tradition, from Ada Lovelace to Admiral Grace Hopper. When I began in tech, role models were few. Today, if you look around today, there are a number of role models for women starting out: Marissa Mayer, Sheryl Sandberg, and Susan Wojcicki, to name a few. But the playing field is still far from level.
Where and how can we level the playing field?
Maybe online? As reported in a survey by freelance job site Elance, women in technology are finding more opportunities online than on-site. According to their survey of 7,000 global independent professionals, 80% of respondents also said they’re optimistic about the future of high-tech professions for women even though a majority still sees a lag in pay equality and encouragement from parents and/or teachers.
Fabio Rosati, CEO of Elance, noted, “Online work provides an attractive avenue to neutralize gender discrimination around the world and create flexible professional opportunities not available in traditional job markets.â€
That’s one solution. I think another has got to be education. Basically, education is a great lever to pay parity.  And, backing programs such as Girls Who Code is a great way to get young women engaged in technology.
Mentoring is also another great avenue. It’s something I’m proud to say I use to measure my success as well.
I hope to share more of my thoughts and experiences at SWXS this coming year as a featured speaker on the topic “Boardroom or Baby.†You can support me and continue to raise awareness for the issue by going here to vote for my presentation.  Voting closes Friday, Sept. 5th – so go check out the SXSW PanelPicker and vote today!
![]()
![]()
Several vulnerabilities in third party extensions
Release Date: September 02, 2014
Bulletin update: September 5, 2014 (added CVEs)
Please read first: This Collective Security Bulletin (CSB) is a listing of vulnerable extensions with neither significant download numbers, nor other special importance amongst the TYPO3 Community. The intention of CSBs is to reduce the workload of the TYPO3 Security Team and of the maintainers of extensions with vulnerabilities. Nevertheless, vulnerabilities in TYPO3 core or important extensions will still get the well-known single Security Bulletin each.
Please read the chapter in the Security Guide about the different types of Extension Security Bulletins.
All vulnerabilities affect third-party extensions. These extensions are not part of the TYPO3 default installation.
Extension: CWT Frontend Edit (cwt_feedit)
Affected Versions: 1.2.4 and all versions below
Vulnerability Type: Arbitrary Code Execution
Severity: Critical
Suggested CVSS v2.0: AV:N/AC:L/Au:S/C:C/I:C/A:C/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6231
Solution: An updated version 1.2.5 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/cwt_feedit/1.2.5/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Milan Altenburg who discovered and reported the issue.
Extension: LDAP (eu_ldap)
Affected Versions: 2.8.17 and all versions below
Vulnerability Type: Information Disclosure
Severity: Low
Suggested CVSS v2.0: AV:N/AC:H/Au:S/C:C/I:N/A:N/E:ND/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6232
Solution: An updated version 2.8.18 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/eu_ldap/2.8.18/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Florian Seirer who discovered and reported the issue.
Extension: Flat Manager (flatmgr)
Affected Versions: 2.7.9 and all versions below
Vulnerability Type: SQL Injection
Severity: High
Suggested CVSS v2.0: AV:N/AC:L/Au:N/C:C/I:P/A:N/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6233
Solution: An updated version 2.7.10 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/flatmgr/2.7.10/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Ingo Schmitt who discovered and reported the issue.
Extension: Open Graph protocol (jh_opengraphprotocol)
Affected Versions: 1.0.1 and all versions below
Vulnerability Type: Cross-Site Scripting
Severity: Medium
Suggested CVSS v2.0: AV:N/AC:L/Au:N/C:P/I:P/A:N/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6234
Solution: An updated version 1.0.2 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/jh_opengraphprotocol/1.0.2/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Heiko Kromm who discovered and reported the issue.
Extension: ke DomPDF (ke_dompdf)
Affected Versions: 0.0.3 and all versions below
Vulnerability Type: Remote Code Execution
Severity: Critical
Suggested CVSS v2.0: AV:N/AC:L/Au:N/C:C/I:C/A:C/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6235
Solution: An updated version 0.0.5 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/ke_dompdf/0.0.5/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Hendrik Nadler who discovered and reported the issue.
Extension: LumoNet PHP Include (lumophpinclude)
Affected Versions: 1.2.0 and all versions below
Vulnerability Type: Arbitrary Code Execution
Severity: Critical
Suggested CVSS v2.0: AV:N/AC:L/Au:N/C:C/I:C/A:C/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6236
Solution: An updated version 1.2.1 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/lumophpinclude/1.2.1/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Jost Baron who discovered and reported the issue.
Extension: News Pack (news_pack)
Affected Versions: 0.1.0 and all versions below
Vulnerability Type: Cross-Site Scripting
Severity: Medium
Suggested CVSS v2.0: AV:N/AC:L/Au:S/C:P/I:P/A:N/E:F/RL:U/RC:C (What’s that?)
CVE: CVE-2014-6237
Solution: Versions of this extension that are known to be vulnerable will no longer be available for download from the TYPO3 Extension Repository. The extension author failed in providing a security fix for the reported vulnerability in a decent amount of time. Please uninstall and delete the extension folder from your installation.
Credits: Credits go to Frederic Gaus who discovered and reported the issue.
Extension: SB Folderdownload (sb_akronymmanager)
Affected Versions: 0.5.0 and all versions below
Vulnerability Type: Cross-Site Scripting
Severity: Medium
Suggested CVSS v2.0: AV:N/AC:L/Au:S/C:P/I:P/A:N/E:F/RL:U/RC:C (What’s that?)
CVE: CVE-2014-6238
Solution: Versions of this extension that are known to be vulnerable will no longer be available for download from the TYPO3 Extension Repository. The extension author failed in providing a security fix for the reported vulnerability in a decent amount of time. Please uninstall and delete the extension folder from your installation.
Extension: Address visualization with Google Maps (st_address_map)
Affected Versions: 0.3.5 and all versions below
Vulnerability Type: SQL Injection
Severity: High
Suggested CVSS v2.0: AV:N/AC:L/Au:N/C:C/I:P/A:N/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6239
Solution: An updated version 0.3.6 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/st_address_map/0.3.6/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Marc Bastian Heinrichs who discovered and reported the issue.
Extension: Google Sitemap (weeaar_googlesitemap)
Affected Versions: 0.4.3 and all versions below
Vulnerability Type: Cross-Site Scripting
Severity: Medium
Suggested CVSS v2.0: AV:N/AC:L/Au:S/C:P/I:P/A:N/E:F/RL:U/RC:C (What’s that?)
CVE: CVE-2014-6240
Solution: Versions of this extension that are known to be vulnerable will no longer be available for download from the TYPO3 Extension Repository. The extension author failed in providing a security fix for the reported vulnerability in a decent amount of time. Please uninstall and delete the extension folder from your installation.
Extension: wt_directory (wt_directory)
Affected Versions: 1.4.0 and all versions below
Vulnerability Type: SQL Injection
Severity: High
Suggested CVSS v2.0: AV:N/AC:L/Au:N/C:C/I:P/A:N/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6241
Solution: An updated version 1.4.1 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/wt_directory/1.4.1/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Marc Bastian Heinrichs who discovered and reported the issue.
General advice: Follow the recommendations that are given in the TYPO3 Security Guide. Please subscribe to the typo3-announce mailing list to receive future Security Bulletins via E-mail.
Several vulnerabilities in third party extensions
Release Date: September 02, 2014
Bulletin update: September 5, 2014 (added CVEs)
Please read first: This Collective Security Bulletin (CSB) is a listing of vulnerable extensions with neither significant download numbers, nor other special importance amongst the TYPO3 Community. The intention of CSBs is to reduce the workload of the TYPO3 Security Team and of the maintainers of extensions with vulnerabilities. Nevertheless, vulnerabilities in TYPO3 core or important extensions will still get the well-known single Security Bulletin each.
Please read the chapter in the Security Guide about the different types of Extension Security Bulletins.
All vulnerabilities affect third-party extensions. These extensions are not part of the TYPO3 default installation.
Extension: CWT Frontend Edit (cwt_feedit)
Affected Versions: 1.2.4 and all versions below
Vulnerability Type: Arbitrary Code Execution
Severity: Critical
Suggested CVSS v2.0: AV:N/AC:L/Au:S/C:C/I:C/A:C/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6231
Solution: An updated version 1.2.5 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/cwt_feedit/1.2.5/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Milan Altenburg who discovered and reported the issue.
Extension: LDAP (eu_ldap)
Affected Versions: 2.8.17 and all versions below
Vulnerability Type: Information Disclosure
Severity: Low
Suggested CVSS v2.0: AV:N/AC:H/Au:S/C:C/I:N/A:N/E:ND/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6232
Solution: An updated version 2.8.18 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/eu_ldap/2.8.18/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Florian Seirer who discovered and reported the issue.
Extension: Flat Manager (flatmgr)
Affected Versions: 2.7.9 and all versions below
Vulnerability Type: SQL Injection
Severity: High
Suggested CVSS v2.0: AV:N/AC:L/Au:N/C:C/I:P/A:N/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6233
Solution: An updated version 2.7.10 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/flatmgr/2.7.10/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Ingo Schmitt who discovered and reported the issue.
Extension: Open Graph protocol (jh_opengraphprotocol)
Affected Versions: 1.0.1 and all versions below
Vulnerability Type: Cross-Site Scripting
Severity: Medium
Suggested CVSS v2.0: AV:N/AC:L/Au:N/C:P/I:P/A:N/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6234
Solution: An updated version 1.0.2 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/jh_opengraphprotocol/1.0.2/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Heiko Kromm who discovered and reported the issue.
Extension: ke DomPDF (ke_dompdf)
Affected Versions: 0.0.3 and all versions below
Vulnerability Type: Remote Code Execution
Severity: Critical
Suggested CVSS v2.0: AV:N/AC:L/Au:N/C:C/I:C/A:C/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6235
Solution: An updated version 0.0.5 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/ke_dompdf/0.0.5/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Hendrik Nadler who discovered and reported the issue.
Extension: LumoNet PHP Include (lumophpinclude)
Affected Versions: 1.2.0 and all versions below
Vulnerability Type: Arbitrary Code Execution
Severity: Critical
Suggested CVSS v2.0: AV:N/AC:L/Au:N/C:C/I:C/A:C/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6236
Solution: An updated version 1.2.1 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/lumophpinclude/1.2.1/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Jost Baron who discovered and reported the issue.
Extension: News Pack (news_pack)
Affected Versions: 0.1.0 and all versions below
Vulnerability Type: Cross-Site Scripting
Severity: Medium
Suggested CVSS v2.0: AV:N/AC:L/Au:S/C:P/I:P/A:N/E:F/RL:U/RC:C (What’s that?)
CVE: CVE-2014-6237
Solution: Versions of this extension that are known to be vulnerable will no longer be available for download from the TYPO3 Extension Repository. The extension author failed in providing a security fix for the reported vulnerability in a decent amount of time. Please uninstall and delete the extension folder from your installation.
Credits: Credits go to Frederic Gaus who discovered and reported the issue.
Extension: SB Folderdownload (sb_akronymmanager)
Affected Versions: 0.5.0 and all versions below
Vulnerability Type: Cross-Site Scripting
Severity: Medium
Suggested CVSS v2.0: AV:N/AC:L/Au:S/C:P/I:P/A:N/E:F/RL:U/RC:C (What’s that?)
CVE: CVE-2014-6238
Solution: Versions of this extension that are known to be vulnerable will no longer be available for download from the TYPO3 Extension Repository. The extension author failed in providing a security fix for the reported vulnerability in a decent amount of time. Please uninstall and delete the extension folder from your installation.
Extension: Address visualization with Google Maps (st_address_map)
Affected Versions: 0.3.5 and all versions below
Vulnerability Type: SQL Injection
Severity: High
Suggested CVSS v2.0: AV:N/AC:L/Au:N/C:C/I:P/A:N/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6239
Solution: An updated version 0.3.6 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/st_address_map/0.3.6/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Marc Bastian Heinrichs who discovered and reported the issue.
Extension: Google Sitemap (weeaar_googlesitemap)
Affected Versions: 0.4.3 and all versions below
Vulnerability Type: Cross-Site Scripting
Severity: Medium
Suggested CVSS v2.0: AV:N/AC:L/Au:S/C:P/I:P/A:N/E:F/RL:U/RC:C (What’s that?)
CVE: CVE-2014-6240
Solution: Versions of this extension that are known to be vulnerable will no longer be available for download from the TYPO3 Extension Repository. The extension author failed in providing a security fix for the reported vulnerability in a decent amount of time. Please uninstall and delete the extension folder from your installation.
Extension: wt_directory (wt_directory)
Affected Versions: 1.4.0 and all versions below
Vulnerability Type: SQL Injection
Severity: High
Suggested CVSS v2.0: AV:N/AC:L/Au:N/C:C/I:P/A:N/E:F/RL:O/RC:C (What’s that?)
CVE: CVE-2014-6241
Solution: An updated version 1.4.1 is available from the TYPO3 extension manager and at http://typo3.org/extensions/repository/download/wt_directory/1.4.1/t3x/. Users of the extension are advised to update the extension as soon as possible.
Credits: Credits go to Marc Bastian Heinrichs who discovered and reported the issue.
General advice: Follow the recommendations that are given in the TYPO3 Security Guide. Please subscribe to the typo3-announce mailing list to receive future Security Bulletins via E-mail.
SB14-244: Vulnerability Summary for the Week of August 25, 2014
Original release date: September 01, 2014
The US-CERT Cyber Security Bulletin provides a summary of new vulnerabilities that have been recorded by the National Institute of Standards and Technology (NIST) National Vulnerability Database (NVD) in the past week. The NVD is sponsored by the Department of Homeland Security (DHS) National Cybersecurity and Communications Integration Center (NCCIC) / United States Computer Emergency Readiness Team (US-CERT). For modified or updated entries, please visit the NVD, which contains historical vulnerability information.
The vulnerabilities are based on the CVE vulnerability naming standard and are organized according to severity, determined by the Common Vulnerability Scoring System (CVSS) standard. The division of high, medium, and low severities correspond to the following scores:
-
High – Vulnerabilities will be labeled High severity if they have a CVSS base score of 7.0 – 10.0
-
Medium – Vulnerabilities will be labeled Medium severity if they have a CVSS base score of 4.0 – 6.9
-
Low – Vulnerabilities will be labeled Low severity if they have a CVSS base score of 0.0 – 3.9
Entries may include additional information provided by organizations and efforts sponsored by US-CERT. This information may include identifying information, values, definitions, and related links. Patch information is provided when available. Please note that some of the information in the bulletins is compiled from external, open source reports and is not a direct result of US-CERT analysis.
High Vulnerabilities
| Primary Vendor — Product |
Description | Published | CVSS Score | Source & Patch Info |
|---|---|---|---|---|
| apache — openoffice | Apache OpenOffice before 4.1.1 allows remote attackers to execute arbitrary commands and possibly have other unspecified impact via a crafted Calc spreadsheet. | 2014-08-26 | 9.3 | CVE-2014-3524 XF SECTRACK BID BUGTRAQ |
| emc — rsa_identity_management_and_governance | EMC RSA Identity Management and Governance (IMG) 6.5.x before 6.5.1 P11, 6.5.2 before P02HF01, and 6.8.x before P07, when Novell Identity Manager (aka NovellIM) is used, allows remote attackers to bypass authentication via an arbitrary valid username. | 2014-08-27 | 9.3 | CVE-2014-4619 BUGTRAQ |
| fortinet — fortios | The FortiManager protocol service in Fortinet FortiOS before 4.3.16 and 5.0.0 before 5.0.8 on FortiGate devices allows remote attackers to cause a denial of service and possibly execute arbitrary code via a crafted request. | 2014-08-25 | 7.5 | CVE-2014-2216 SECUNIA |
| freereprintables — articlefr | Multiple SQL injection vulnerabilities in Free Reprintables ArticleFR 3.0.4 and earlier allow remote attackers to execute arbitrary SQL commands via the id parameter in a (1) get or (2) set action to rate.php. | 2014-08-22 | 7.5 | CVE-2014-5097 MISC BID BUGTRAQ MISC |
| google — chrome | Use-after-free vulnerability in the SVG implementation in Blink, as used in Google Chrome before 37.0.2062.94, allows remote attackers to cause a denial of service or possibly have unspecified other impact by leveraging improper caching associated with animation. | 2014-08-26 | 7.5 | CVE-2014-3168 CONFIRM |
| google — chrome | Use-after-free vulnerability in core/dom/ContainerNode.cpp in the DOM implementation in Blink, as used in Google Chrome before 37.0.2062.94, allows remote attackers to cause a denial of service or possibly have unspecified other impact by leveraging script execution that occurs before notification of node removal. | 2014-08-26 | 7.5 | CVE-2014-3169 CONFIRM |
| google — chrome | Use-after-free vulnerability in the V8 bindings in Blink, as used in Google Chrome before 37.0.2062.94, allows remote attackers to cause a denial of service or possibly have unspecified other impact by leveraging improper use of HashMap add operations instead of HashMap set operations, related to bindings/core/v8/DOMWrapperMap.h and bindings/core/v8/SerializedScriptValue.cpp. | 2014-08-26 | 7.5 | CVE-2014-3171 CONFIRM |
| google — chrome | Multiple unspecified vulnerabilities in Google Chrome before 37.0.2062.94 allow attackers to cause a denial of service or possibly have other impact via unknown vectors, related to the load_truetype_glyph function in truetype/ttgload.c in FreeType and other functions in other components. | 2014-08-26 | 10.0 | CVE-2014-3175 CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM CONFIRM |
| google — chrome | Google Chrome before 37.0.2062.94 does not properly handle the interaction of extensions, IPC, the sync API, and Google V8, which allows remote attackers to execute arbitrary code via unspecified vectors, a different vulnerability than CVE-2014-3177. | 2014-08-26 | 10.0 | CVE-2014-3176 CONFIRM |
| google — chrome | Google Chrome before 37.0.2062.94 does not properly handle the interaction of extensions, IPC, the sync API, and Google V8, which allows remote attackers to execute arbitrary code via unspecified vectors, a different vulnerability than CVE-2014-3176. | 2014-08-26 | 10.0 | CVE-2014-3177 CONFIRM |
| hp — service_manager | Unspecified vulnerability in the WebTier component in HP Service Manager (SM) 7.21 and 9.x before 9.34 allows remote attackers to execute arbitrary code via unknown vectors. | 2014-08-23 | 10.0 | CVE-2014-2632 |
| hp — service_manager | Unspecified vulnerability in the server in HP Service Manager (SM) 7.21 and 9.x before 9.34 allows remote attackers to bypass intended access restrictions, and modify data or cause a denial of service, via unknown vectors. | 2014-08-23 | 9.4 | CVE-2014-2634 |
| ibm — monitoring_agent_for_unix_logs | Monitoring Agent for UNIX Logs 6.2.0 through FP03, 6.2.1 through FP04, 6.2.2 through FP09, and 6.2.3 through FP04 and Monitoring Server (ms) and Shared Libraries (ax) 6.2.0 through FP03, 6.2.1 through FP04, 6.2.2 through FP08, 6.2.3 through FP01, and 6.3.0 through FP01 in IBM Tivoli Monitoring (ITM) on UNIX allow local users to gain privileges via unspecified vectors. | 2014-08-29 | 7.2 | CVE-2013-5467 XF |
| invensys — wonderware_information_server | Schneider Electric Wonderware Information Server (WIS) Portal 4.0 SP1 through 5.5 uses weak encryption, which allows remote attackers to obtain sensitive information by reading a credential file. | 2014-08-27 | 7.8 | CVE-2014-2380 MISC |
| invensys — wonderware_information_server | SQL injection vulnerability in Schneider Electric Wonderware Information Server (WIS) Portal 4.0 SP1 through 5.5 allows remote attackers to execute arbitrary SQL commands via unspecified vectors. | 2014-08-27 | 7.5 | CVE-2014-5399 MISC |
| little_kernel_project — little_kernel_bootloader | The image_verify function in platform/msm_shared/image_verify.c in the Little Kernel (LK) bootloader, as distributed with Qualcomm Innovation Center (QuIC) Android contributions for MSM devices and other products, does not check whether a certain digest size is consistent with the RSA_public_decrypt API specification, which makes it easier for attackers to bypass boot-image authentication requirements via trailing data. | 2014-08-24 | 7.2 | CVE-2014-0973 |
| little_kernel_project — little_kernel_bootloader | The cmd_boot function in app/aboot/aboot.c in the Little Kernel (LK) bootloader, as distributed with Qualcomm Innovation Center (QuIC) Android contributions for MSM devices and other products, allows attackers to bypass intended device-lock and kernel-signature restrictions by using fastboot mode in a boot command for an arbitrary kernel image. | 2014-08-24 | 7.2 | CVE-2014-4325 |
| novell — groupwise | FileUploadServlet in the Administration service in Novell GroupWise 2014 before SP1 allows remote attackers to read or write to arbitrary files via the poLibMaintenanceFileSave parameter, aka ZDI-CAN-2287. | 2014-08-29 | 7.8 | CVE-2014-0600 CONFIRM MISC |
| pandasecurity — panda_av_pro_2014 | Heap-based buffer overflow in the PavTPK.sys kernel mode driver of Panda Security 2014 products before hft131306s24_r1 allows local users to gain privileges via a crafted argument to a 0x222008 IOCTL call. | 2014-08-26 | 7.2 | CVE-2014-5307 MISC XF BID BUGTRAQ FULLDISC MISC |
| php-sqrl_project — php-sqrl | SQL injection vulnerability in sqrl_verify.php in php-sqrl allows remote attackers to execute arbitrary SQL commands via the message parameter. | 2014-08-25 | 7.5 | CVE-2014-5458 CONFIRM MISC FULLDISC |
| qeiinc — epaq-9410_substation_gateway | The DNP3 driver in CG Automation ePAQ-9410 Substation Gateway allows remote attackers to cause a denial of service (infinite loop or process crash) via a crafted TCP packet. | 2014-08-27 | 7.1 | CVE-2014-0761 MISC |
| saltstack — salt | Multiple unspecified vulnerabilities in Salt (aka SaltStack) before 2014.1.10 allow local users to have an unspecified impact via vectors related to temporary file creation in (1) seed.py, (2) salt-ssh, or (3) salt-cloud. | 2014-08-22 | 7.2 | CVE-2014-3563 XF BID |
| schrack — technik_microcontrol | The web interface in Schrack Technik microControl with firmware before 1.7.0 (937) has a hardcoded password of not for the “user” account, which makes it easier for remote attackers to obtain access via unspecified vectors. | 2014-08-22 | 7.5 | CVE-2014-5396 MISC FULLDISC |
| tenda — a5s | The Shenzhen Tenda Technology Tenda A5s router with firmware 3.02.05_CN allows remote attackers to bypass authentication and gain administrator access by setting the admin:language cookie to zh-cn. | 2014-08-22 | 10.0 | CVE-2014-5246 XF BID EXPLOIT-DB MISC OSVDB |
| ubi — uplay_pc | Ubisoft Uplay PC before 4.6.1.3217 use weak permissions (Everyone: Full Control) for the program installation directory (%PROGRAMFILES%Ubisoft Game Launcher), which allows local users to gain privileges via a Trojan horse file. | 2014-08-25 | 7.2 | CVE-2014-5453 MISC EXPLOIT-DB OSVDB |
Medium Vulnerabilities
| Primary Vendor — Product |
Description | Published | CVSS Score | Source & Patch Info |
|---|---|---|---|---|
| apache — openoffice | The OLE preview generation in Apache OpenOffice before 4.1.1 and OpenOffice.org (OOo) might allow remote attackers to embed arbitrary data into documents via crafted OLE objects. | 2014-08-26 | 4.3 | CVE-2014-3575 XF SECTRACK BUGTRAQ |
| apache — axis | The getCN function in Apache Axis 1.4 and earlier does not properly verify that the server hostname matches a domain name in the subject’s Common Name (CN) or subjectAltName field of the X.509 certificate, which allows man-in-the-middle attackers to spoof SSL servers via a certificate with a subject that specifies a common name in a field that is not the CN field. NOTE: this issue exists because of an incomplete fix for CVE-2012-5784. | 2014-08-26 | 5.8 | CVE-2014-3596 XF SECTRACK BID MLIST |
| check_mk_project — check_mk | Multiple cross-site scripting (XSS) vulnerabilities in the multisite component in Check_MK before 1.2.4p4 and 1.2.5 before 1.2.5i4 allow remote authenticated users to inject arbitrary web script or HTML via unspecified vectors to the (1) render_status_icons function in htmllib.py or (2) ajax_action function in actions.py. | 2014-08-22 | 4.3 | CVE-2014-5338 XF BID BUGTRAQ MISC |
| christos_zoulas — file | Integer overflow in the cdf_read_property_info function in cdf.c in file through 5.19, as used in the Fileinfo component in PHP before 5.4.32 and 5.5.x before 5.5.16, allows remote attackers to cause a denial of service (application crash) via a crafted CDF file. NOTE: this vulnerability exists because of an incomplete fix for CVE-2012-1571. | 2014-08-22 | 4.3 | CVE-2014-3587 CONFIRM DEBIAN CONFIRM |
| cisco — asr_9000_rsp440_router | Cisco IOS XR 4.3(.2) and earlier on ASR 9000 devices does not properly perform NetFlow sampling of packets with multicast destination MAC addresses, which allows remote attackers to cause a denial of service (chip and card hangs) via a crafted packet, aka Bug ID CSCup77750. | 2014-08-26 | 4.6 | CVE-2014-3335 |
| cisco — transport_gateway_installation_software | Multiple cross-site scripting (XSS) vulnerabilities in the web framework in Cisco Transport Gateway for Smart Call Home (aka TG-SCH or Transport Gateway Installation Software) 4.0 allow remote attackers to inject arbitrary web script or HTML via unspecified parameters, aka Bug IDs CSCuq31129, CSCuq31134, CSCuq31137, and CSCuq31563. | 2014-08-27 | 4.3 | CVE-2014-3344 |
| cisco — transport_gateway_installation_software | The web framework in Cisco Transport Gateway for Smart Call Home (aka TG-SCH or Transport Gateway Installation Software) 4.0 does not properly check authorization for administrative web pages, which allows remote attackers to modify the product via a crafted URL, aka Bug ID CSCuq31503. | 2014-08-28 | 5.0 | CVE-2014-3345 |
| cisco — transport_gateway_installation_software | The web framework in Cisco Transport Gateway for Smart Call Home (aka TG-SCH or Transport Gateway Installation Software) does not validate an unspecified parameter, which allows remote authenticated users to cause a denial of service (service crash) via a crafted string, aka Bug ID CSCuq31819. | 2014-08-29 | 6.3 | CVE-2014-3346 |
| cisco — 1801_integrated_service_router | Cisco IOS 15.1(4)M2 on Cisco 1800 ISR devices, when the ISDN Basic Rate Interface is enabled, allows remote attackers to cause a denial of service (device hang) by leveraging knowledge of the ISDN phone number to trigger an interrupt timer collision during entropy collection, leading to an invalid state of the hardware encryption module, aka Bug ID CSCul77897. | 2014-08-28 | 5.4 | CVE-2014-3347 |
| cisco — cloud_portal | Cisco Intelligent Automation for Cloud (aka Cisco Cloud Portal) does not validate file types during the handling of file submission, which allows remote authenticated users to upload arbitrary files via a crafted request, aka Bug ID CSCuh87410. | 2014-08-29 | 4.0 | CVE-2014-3349 |
| cisco — cloud_portal | Cisco Intelligent Automation for Cloud (aka Cisco Cloud Portal) does not properly implement URL redirection, which allows remote authenticated users to obtain sensitive information via a crafted URL, aka Bug ID CSCuh84870. | 2014-08-29 | 4.0 | CVE-2014-3350 |
| cisco — cloud_portal | Cisco Intelligent Automation for Cloud (aka Cisco Cloud Portal) does not properly consider whether a session is a problematic NULL session, which allows remote attackers to obtain sensitive information via crafted packets, aka Bug IDs CSCuh87398 and CSCuh87380. | 2014-08-29 | 5.0 | CVE-2014-3351 |
| debian — python-imaging | PIL/IcnsImagePlugin.py in Python Imaging Library (PIL) and Pillow before 2.3.2 and 2.5.x before 2.5.2 allows remote attackers to cause a denial of service via a crafted block size. | 2014-08-25 | 5.0 | CVE-2014-3589 DEBIAN |
| djangoproject — django | The core.urlresolvers.reverse function in Django before 1.4.14, 1.5.x before 1.5.9, 1.6.x before 1.6.6, and 1.7 before release candidate 3 does not properly validate URLs, which allows remote attackers to conduct phishing attacks via a // (slash slash) in a URL, which triggers a scheme-relative URL to be generated. | 2014-08-26 | 5.8 | CVE-2014-0480 DEBIAN |
| djangoproject — django | The default configuration for the file upload handling system in Django before 1.4.14, 1.5.x before 1.5.9, 1.6.x before 1.6.6, and 1.7 before release candidate 3 uses a sequential file name generation process when a file with a conflicting name is uploaded, which allows remote attackers to cause a denial of service (CPU consumption) by unloading a multiple files with the same name. | 2014-08-26 | 4.3 | CVE-2014-0481 DEBIAN |
| djangoproject — django | The contrib.auth.middleware.RemoteUserMiddleware middleware in Django before 1.4.14, 1.5.x before 1.5.9, 1.6.x before 1.6.6, and 1.7 before release candidate 3, when using the contrib.auth.backends.RemoteUserBackend backend, allows remote authenticated users to hijack web sessions via vectors related to the REMOTE_USER header. | 2014-08-26 | 6.0 | CVE-2014-0482 DEBIAN |
| esri — arcgis_for_server | Multiple cross-site scripting (XSS) vulnerabilities in ESRI ArcGIS for Server 10.1.1 allow remote attackers to inject arbitrary web script or HTML via unspecified parameters. | 2014-08-22 | 4.3 | CVE-2014-5121 BUGTRAQ MISC |
| esri — arcgis_for_server | Open redirect vulnerability in ESRI ArcGIS for Server 10.1.1 allows remote attackers to redirect users to arbitrary web sites and conduct phishing attacks via an unspecified parameter, related to login. | 2014-08-22 | 5.8 | CVE-2014-5122 BID BUGTRAQ MISC |
| google — chrome | extensions/common/url_pattern.cc in Google Chrome before 37.0.2062.94 does not prevent use of a ” character in a host name, which allows remote attackers to spoof the extension permission dialog by relying on truncation after this character. | 2014-08-26 | 6.4 | CVE-2014-3170 CONFIRM |
| google — chrome | The Debugger extension API in browser/extensions/api/debugger/debugger_api.cc in Google Chrome before 37.0.2062.94 does not validate a tab’s URL before an attach operation, which allows remote attackers to bypass intended access limitations via an extension that uses a restricted URL, as demonstrated by a chrome:// URL. | 2014-08-26 | 6.4 | CVE-2014-3172 CONFIRM |
| google — chrome | The WebGL implementation in Google Chrome before 37.0.2062.94 does not ensure that clear calls interact properly with the state of a draw buffer, which allows remote attackers to cause a denial of service (read of uninitialized memory) via a crafted CANVAS element, related to gpu/command_buffer/service/framebuffer_manager.cc and gpu/command_buffer/service/gles2_cmd_decoder.cc. | 2014-08-26 | 5.0 | CVE-2014-3173 CONFIRM |
| google — chrome | modules/webaudio/BiquadDSPKernel.cpp in the Web Audio API implementation in Blink, as used in Google Chrome before 37.0.2062.94, does not properly consider concurrent threads during attempts to update biquad filter coefficients, which allows remote attackers to cause a denial of service (read of uninitialized memory) via crafted API calls. | 2014-08-26 | 5.0 | CVE-2014-3174 CONFIRM |
| hp — service_manager | Cross-site scripting (XSS) vulnerability in the Mobility Web Client and Service Request Catalog (SRC) components in HP Service Manager (SM) 7.21 and 9.x before 9.34 allows remote attackers to inject arbitrary web script or HTML via unspecified vectors. | 2014-08-23 | 4.3 | CVE-2013-6222 |
| hp — service_manager | Cross-site request forgery (CSRF) vulnerability in the server in HP Service Manager (SM) 7.21 and 9.x before 9.34 allows remote attackers to hijack the authentication of unspecified victims via unknown vectors. | 2014-08-23 | 6.8 | CVE-2014-2633 |
| ibm — power_710 | Unspecified vulnerability on IBM Power 7 Systems 740 before 740.70 01Ax740_121, 760 before 760.40 Ax760_078, and 770 before 770.30 01Ax770_062 allows local users to gain Service Processor privileges via unknown vectors. | 2014-08-22 | 4.6 | CVE-2013-6306 XF |
| ibm — mobile_foundation | IBM Worklight Foundation 5.x and 6.x before 6.2.0.0, as used in Worklight and Mobile Foundation, allows remote authenticated users to bypass the application-authenticity feature via unspecified vectors. | 2014-08-29 | 4.9 | CVE-2014-0888 XF |
| ibm — maximo_asset_management | Cross-site request forgery (CSRF) vulnerability in IBM Maximo Asset Management 7.1 through 7.1.1.12 and 7.5 through 7.5.0.6 and Maximo Asset Management 7.5.0 through 7.5.0.3 and 7.5.1 through 7.5.1.2 for SmartCloud Control Desk allows remote authenticated users to hijack the authentication of arbitrary users. | 2014-08-29 | 6.0 | CVE-2014-3024 XF AIXAPAR |
| ibm — emptoris_contract_management | Cross-site request forgery (CSRF) vulnerability in IBM Emptoris Contract Management 9.5.x before 9.5.0.6 iFix 10, 10.0.0.x before 10.0.0.1 iFix 10, 10.0.1.x before 10.0.1.4, and 10.0.2.x before 10.0.2.2 iFix 2; Emptoris Sourcing Portfolio 9.5.x before 9.5.1.3, 10.0.0.x before 10.0.0.1, 10.0.1.x before 10.0.1.3, and 10.0.2.x before 10.0.2.4; and Emptoris Spend Analysis 9.5.x before 9.5.0.4, 10.0.1.x before 10.0.1.3, and 10.0.2.x before 10.0.2.4 allows remote authenticated users to hijack the authentication of arbitrary users for requests that insert XSS sequences. | 2014-08-26 | 6.0 | CVE-2014-3040 XF |
| ibm — emptoris_contract_management | SQL injection vulnerability in IBM Emptoris Contract Management 9.5.x before 9.5.0.6 iFix 10, 10.0.0.x before 10.0.0.1 iFix 10, 10.0.1.x before 10.0.1.4, and 10.0.2.x before 10.0.2.2 iFix 2 allows remote authenticated users to execute arbitrary SQL commands via unspecified vectors. | 2014-08-26 | 6.5 | CVE-2014-3041 XF |
| ibm — emptoris_spend_analysis | Cross-site request forgery (CSRF) vulnerability in IBM Emptoris Spend Analysis 9.5.x before 9.5.0.4, 10.0.1.x before 10.0.1.3, and 10.0.2.x before 10.0.2.4 allows remote attackers to hijack the authentication of arbitrary users for requests that insert XSS sequences. | 2014-08-26 | 6.8 | CVE-2014-3061 XF |
| ibm — maximo_asset_management | IBM Maximo Asset Management 6.1 through 6.5, 7.1 through 7.1.1.13, and 7.5 through 7.5.0.6; Maximo Asset Management 7.5.0 through 7.5.0.3 and 7.5.1 through 7.5.1.2 for SmartCloud Control Desk; and Maximo Asset Management 6.2.8, 7.1, and 7.2 for Tivoli IT Asset Management for IT and certain other products allow remote authenticated users to bypass intended write-access restrictions on calendar entries via unspecified vectors. | 2014-08-29 | 4.9 | CVE-2014-3084 XF AIXAPAR |
| ibm — emptoris_sourcing_portfolio | IBM Emptoris Sourcing Portfolio 9.5.x before 9.5.1.3, 10.0.0.x before 10.0.0.1, 10.0.1.x before 10.0.1.3, and 10.0.2.x before 10.0.2.4 and Emptoris Spend Analysis 9.5.x before 9.5.0.4, 10.0.1.x before 10.0.1.3, and 10.0.2.x before 10.0.2.4 does not properly restrict use of FRAME elements, which allows remote authenticated users to conduct phishing attacks, and bypass intended access restrictions or obtain sensitive information, via a crafted web site, related to a “frame injection” issue. | 2014-08-26 | 4.9 | CVE-2014-4790 XF |
| innovaphone — innovaphone_pbx | Multiple cross-site request forgery (CSRF) vulnerabilities in innovaphone PBX 10.00 sr11 and earlier allow remote attackers to hijack the authentication of administrators for requests that modify configurations or user accounts, as demonstrated by (1) changing the administrator password via a crafted request to CMD0/mod_cmd.xml or (2) adding a new SIP user via a crafted request to PBX0/ADMIN/mod_cmd_login.xml. | 2014-08-25 | 6.8 | CVE-2014-5335 BUGTRAQ |
| invensys — wonderware_information_server | Cross-site scripting (XSS) vulnerability in Schneider Electric Wonderware Information Server (WIS) Portal 4.0 SP1 through 5.5 allows remote attackers to inject arbitrary web script or HTML via unspecified vectors. | 2014-08-27 | 4.3 | CVE-2014-5397 MISC |
| kdirstat_project — kdirstat | kcleanup.cpp in KDirStat 2.7.0 does not properly quote strings when deleting a directory, which allows remote attackers to execute arbitrary commands via a ” (double quote) character in the directory name, a different vulnerability than CVE-2014-2528. | 2014-08-26 | 6.8 | CVE-2014-2527 CONFIRM CONFIRM MLIST SUSE |
| kdirstat_project — kdirstat | kcleanup.cpp in KDirStat 2.7.3 does not properly quote strings when deleting a directory, which allows remote attackers to execute arbitrary commands via a ‘ (single quote) character in the directory name, a different vulnerability than CVE-2014-2527. | 2014-08-26 | 6.8 | CVE-2014-2528 CONFIRM MLIST |
| mailpoet — mailpoet_newsletters | Cross-site request forgery (CSRF) vulnerability in the MailPoet Newsletters (wysija-newsletters) plugin before 2.6.11 for WordPress allows remote attackers to hijack the authentication of arbitrary users. | 2014-08-26 | 6.8 | CVE-2014-3907 JVNDB JVN |
| mediawiki — mediawiki | The JSONP endpoint in includes/api/ApiFormatJson.php in MediaWiki before 1.19.18, 1.20.x through 1.22.x before 1.22.9, and 1.23.x before 1.23.2 accepts certain long callback values and does not restrict the initial bytes of a JSONP response, which allows remote attackers to conduct cross-site request forgery (CSRF) attacks, and obtain sensitive information, via a crafted OBJECT element with SWF content consistent with a restricted character set. | 2014-08-22 | 6.8 | CVE-2014-5241 MLIST |
| mediawiki — mediawiki | Cross-site scripting (XSS) vulnerability in mediawiki.page.image.pagination.js in MediaWiki 1.22.x before 1.22.9 and 1.23.x before 1.23.2 allows remote attackers to inject arbitrary web script or HTML via vectors involving the multipageimagenavbox class in conjunction with an action=raw value. | 2014-08-22 | 4.3 | CVE-2014-5242 MLIST |
| mediawiki — mediawiki | MediaWiki before 1.19.18, 1.20.x through 1.22.x before 1.22.9, and 1.23.x before 1.23.2 does not enforce an IFRAME protection mechanism for transcluded pages, which makes it easier for remote attackers to conduct clickjacking attacks via a crafted web site. | 2014-08-22 | 4.3 | CVE-2014-5243 MLIST |
| monkey-project — monkey_http_daemon | Monkey HTTP Server before 1.5.3, when the File Descriptor Table (FDT) is enabled and custom error messages are set, allows remote attackers to cause a denial of service (file descriptor consumption) via an HTTP request that triggers an error message. | 2014-08-26 | 4.3 | CVE-2014-5336 XF BID SECUNIA MLIST MLIST CONFIRM |
| opendaylight — opendaylight | The Netconf (TCP) service in OpenDaylight 1.0 allows remote attackers to read arbitrary files via an XML external entity declaration in conjunction with an entity reference in an XML-RPC message, related to an XML External Entity (XXE) issue. | 2014-08-26 | 6.8 | CVE-2014-5035 XF BUGTRAQ FULLDISC MISC |
| openstack — keystone | The MySQL token driver in OpenStack Identity (Keystone) 2014.1.x before 2014.1.2.1 and Juno before Juno-3 stores timestamps with the incorrect precision, which causes the expiration comparison for tokens to fail and allows remote authenticated users to retain access via an expired token. | 2014-08-25 | 4.9 | CVE-2014-5251 MISC UBUNTU MLIST |
| openstack — keystone | The V3 API in OpenStack Identity (Keystone) 2014.1.x before 2014.1.2.1 and Juno before Juno-3 updates the issued_at value for UUID v2 tokens, which allows remote authenticated users to bypass the token expiration and retain access via a verification (1) GET or (2) HEAD request to v3/auth/tokens/. | 2014-08-25 | 4.9 | CVE-2014-5252 MISC UBUNTU MLIST |
| openstack — keystone | OpenStack Identity (Keystone) 2014.1.x before 2014.1.2.1 and Juno before Juno-3 does not properly revoke tokens when a domain is invalidated, which allows remote authenticated users to retain access via a domain-scoped token for that domain. | 2014-08-25 | 4.9 | CVE-2014-5253 MISC UBUNTU MLIST |
| openstack — image_registry_and_delivery_service_(glance) | OpenStack Image Registry and Delivery Service (Glance) before 2013.2.4, 2014.x before 2014.1.3, and Juno before Juno-3, when using the V2 API, does not properly enforce the image_size_cap configuration option, which allows remote authenticated users to cause a denial of service (disk consumption) by uploading a large image. | 2014-08-25 | 4.0 | CVE-2014-5356 MISC UBUNTU MLIST |
| openvpn — openvpn | Unquoted Windows search path vulnerability in the ptservice service in PrivateTunnel 2.3.8, as bundled in OpenVPN 2.1.28.0 allows local users to gain privileges via a crafted program.exe file in the %SYSTEMDRIVE% folder. | 2014-08-25 | 6.9 | CVE-2014-5455 MISC EXPLOIT-DB MISC OSVDB |
| php — php | Multiple buffer overflows in the php_parserr function in ext/standard/dns.c in PHP before 5.4.32 and 5.5.x before 5.5.16 allow remote DNS servers to cause a denial of service (application crash) or possibly execute arbitrary code via a crafted DNS record, related to the dns_get_record function and the dn_expand function. NOTE: this issue exists because of an incomplete fix for CVE-2014-4049. | 2014-08-22 | 6.8 | CVE-2014-3597 CONFIRM CONFIRM DEBIAN CONFIRM |
| php — php | gd_ctx.c in the GD component in PHP 5.4.x before 5.4.32 and 5.5.x before 5.5.16 does not ensure that pathnames lack %00 sequences, which might allow remote attackers to overwrite arbitrary files via crafted input to an application that calls the (1) imagegd, (2) imagegd2, (3) imagegif, (4) imagejpeg, (5) imagepng, (6) imagewbmp, or (7) imagewebp function. | 2014-08-22 | 6.4 | CVE-2014-5120 CONFIRM |
| qeiinc — epaq-9410_substation_gateway | The DNP3 driver in CG Automation ePAQ-9410 Substation Gateway allows physically proximate attackers to cause a denial of service (infinite loop or process crash) via crafted input over a serial line. | 2014-08-27 | 4.7 | CVE-2014-0762 MISC |
| qemu — qemu | vmstate_xhci_event in hw/usb/hcd-xhci.c in QEMU 1.6.0 does not terminate the list with the VMSTATE_END_OF_LIST macro, which allows attackers to cause a denial of service (out-of-bounds access, infinite loop, and memory corruption) and possibly gain privileges via unspecified vectors. | 2014-08-26 | 6.8 | CVE-2014-5263 MISC MLIST |
| sas — visual_analytics | Unrestricted file upload vulnerability in the image upload module in SAS Visual Analytics 6.4M1 allows remote authenticated users to execute arbitrary code by uploading a file with an executable extension, then accessing it via unspecified vectors. | 2014-08-25 | 6.0 | CVE-2014-5454 XF MISC |
| vmware — tools | vm-support 0.88 in VMware Tools, as distributed with VMware Workstation through 10.0.3 and other products, allows local users to write to arbitrary files via a symlink attack on a file in /tmp. | 2014-08-28 | 6.3 | CVE-2014-4199 FULLDISC |
| vmware — tools | vm-support 0.88 in VMware Tools, as distributed with VMware Workstation through 10.0.3 and other products, uses 0644 permissions for the vm-support archive, which allows local users to obtain sensitive information by extracting files from this archive. | 2014-08-28 | 4.7 | CVE-2014-4200 FULLDISC |
| wp_content_source_control_project — wp_content_source_control | Directory traversal vulnerability in the file_get_contents function in downloadfiles/download.php in the WP Content Source Control (wp-source-control) plugin 3.0.0 and earlier for WordPress allows remote attackers to read arbitrary files via a .. (dot dot) in the path parameter. | 2014-08-22 | 5.0 | CVE-2014-5368 XF BID MLIST MLIST |
| xen — xen | Certain MMU virtualization operations in Xen 4.2.x through 4.4.x before the xsa97-hap patch, when using Hardware Assisted Paging (HAP), are not preemptible, which allows local HVM guest to cause a denial of service (vcpu consumption) by invoking these operations, which process every page assigned to a guest, a different vulnerability than CVE-2014-5149. | 2014-08-22 | 4.7 | CVE-2014-5146 XF SECTRACK BID |
| xen — xen | Certain MMU virtualization operations in Xen 4.2.x through 4.4.x, when using shadow pagetables, are not preemptible, which allows local HVM guest to cause a denial of service (vcpu consumption) by invoking these operations, which process every page assigned to a guest, a different vulnerability than CVE-2014-5146. | 2014-08-22 | 4.7 | CVE-2014-5149 XF SECTRACK BID |
Low Vulnerabilities
| Primary Vendor — Product |
Description | Published | CVSS Score | Source & Patch Info |
|---|---|---|---|---|
| djangoproject — django | The administrative interface (contrib.admin) in Django before 1.4.14, 1.5.x before 1.5.9, 1.6.x before 1.6.6, and 1.7 before release candidate 3 does not check if a field represents a relationship between models, which allows remote authenticated users to obtain sensitive information via a to_field parameter in a popup action to an admin change form page, as demonstrated by a /admin/auth/user/?pop=1&t=password URI. | 2014-08-26 | 3.5 | CVE-2014-0483 DEBIAN |
| ibm — tivoli_storage_manager_for_space_management | The Backup-Archive client in IBM Tivoli Storage Manager (TSM) for Space Management 5.x and 6.x before 6.2.5.3, 6.3.x before 6.3.2, 6.4.x before 6.4.2, and 7.1.x before 7.1.0.3 on Linux and AIX, and 5.x and 6.x before 6.1.5.6 on Solaris and HP-UX, does not preserve file permissions across backup and restore operations, which allows local users to bypass intended access restrictions via standard filesystem operations. | 2014-08-26 | 2.6 | CVE-2013-6335 XF AIXAPAR |
| ibm — flex_system_manager | The Configuration Patterns component in IBM Flex System Manager (FSM) 1.2.0.x, 1.2.1.x, 1.3.0.x, and 1.3.1.x uses a weak algorithm in an encryption step during Chassis Management Module (CMM) account creation, which makes it easier for remote authenticated users to defeat cryptographic protection mechanisms via unspecified vectors. | 2014-08-29 | 3.5 | CVE-2014-0897 XF AIXAPAR |
| ibm — emptoris_sourcing_portfolio | Cross-site scripting (XSS) vulnerability in IBM Emptoris Sourcing Portfolio 9.5.x before 9.5.1.3, 10.0.0.x before 10.0.0.1, 10.0.1.x before 10.0.1.3, and 10.0.2.x before 10.0.2.4 allows remote authenticated users to inject arbitrary web script or HTML via a crafted URL. | 2014-08-26 | 3.5 | CVE-2014-3033 XF |
| ibm — emptoris_contract_management | Cross-site scripting (XSS) vulnerability in IBM Emptoris Contract Management 9.5.x before 9.5.0.6 iFix 10, 10.0.0.x before 10.0.0.1 iFix 10, 10.0.1.x before 10.0.1.4, and 10.0.2.x before 10.0.2.2 iFix 2 allows remote authenticated users to inject arbitrary web script or HTML via a crafted URL. | 2014-08-26 | 3.5 | CVE-2014-3034 XF |
| ibm — emptoris_spend_analysis | Cross-site scripting (XSS) vulnerability in IBM Emptoris Spend Analysis 9.5.x before 9.5.0.4, 10.0.1.x before 10.0.1.3, and 10.0.2.x before 10.0.2.4 allows remote authenticated users to inject arbitrary web script or HTML via a crafted URL. | 2014-08-26 | 3.5 | CVE-2014-3035 XF |
| ibm — powervc | IBM PowerVC 1.2.0 before FP3 and 1.2.1 before FP2 uses cleartext passwords in (1) api-paste.ini, (2) debug logs, (3) the installation process, (4) environment checks, (5) powervc-ldap-config, (6) powervc-restore, and (7) powervc-diag, which allows local users to obtain sensitive information by entering a ps command or reading a file. | 2014-08-29 | 2.1 | CVE-2014-3093 XF |
| ibm — security_appscan | The installation process in IBM Security AppScan Enterprise 8.x before 8.6.0.2 iFix 003, 8.7.x before 8.7.0.1 iFix 003, 8.8.x before 8.8.0.1 iFix 002, and 9.0.x before 9.0.0.1 iFix 001 on Linux places a cleartext password in a temporary file, which allows local users to obtain sensitive information by reading this file. | 2014-08-29 | 2.1 | CVE-2014-4806 XF |
| invensys — wonderware_information_server | Schneider Electric Wonderware Information Server (WIS) Portal 4.0 SP1 through 5.5 uses weak encryption, which allows local users to obtain sensitive information by reading a credential file. | 2014-08-27 | 2.1 | CVE-2014-2381 MISC |
| invensys — wonderware_information_server | Schneider Electric Wonderware Information Server (WIS) Portal 4.0 SP1 through 5.5 allows remote attackers to read arbitrary files or cause a denial of service via an XML external entity declaration in conjunction with an entity reference, related to an XML External Entity (XXE) issue. | 2014-08-27 | 2.1 | CVE-2014-5398 MISC |
| little_kernel_project — little_kernel_bootloader | The boot_linux_from_mmc function in app/aboot/aboot.c in the Little Kernel (LK) bootloader, as distributed with Qualcomm Innovation Center (QuIC) Android contributions for MSM devices and other products, does not properly validate a certain address value, which allows attackers to write data to a controllable memory location by leveraging the ability to initiate an attempted boot of an arbitrary image. | 2014-08-24 | 1.9 | CVE-2014-0974 |
| qnap — ss-839 | QNAP TS-469U with firmware 4.0.7 Build 20140410, TS-459U, TS-EC1679U-RP, and SS-839 use world-readable permissions for /etc/config/shadow, which allows local users to obtain usernames and hashed passwords by reading the password. | 2014-08-25 | 2.1 | CVE-2014-5457 FULLDISC FULLDISC FULLDISC FULLDISC |
| social_stats_project — social_stats | Cross-site scripting (XSS) vulnerability in the Social Stats module before 7.x-1.5 for Drupal allows remote authenticated users with the “[Content Type]: Create new content” permission to inject arbitrary web script or HTML via vectors related to the configuration. | 2014-08-25 | 2.1 | CVE-2014-5456 SECUNIA |
This product is provided subject to this Notification and this Privacy & Use policy.
Jennifer Lawrence: Victim of a security hole in iCloud?

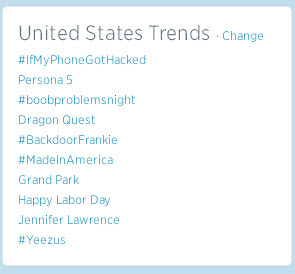
If you are on Twitter you may have noticed the actress Jennifer Lawrence has been ‘Trending Topic’ since yesterday afternoon.
The reason? The leak of nude photos of the 2013 Academy Award winner on the /b/ forum of 4Chan.
She has confirmed the story, although she is apparently not the only victim.

Other models and actresses such as Kirsten Dunst, Kate Upton or Ariana Grande have also allegedly had pictures leaked, although not all these cases have been confirmed. Meanwhile, Mary E. Winstead has acknowledged the authenticity of the pictures that have been circulated, while Victoria Justice has denied that some photos allegedly of her are authentic.
It is still not clear how ‘Celebgate’ (as some are referring to this massive hacking) was carried out. Some sources have suggested a possible security breach in iCloud, Apple’s virtual data storage platform, though the company has yet to confirm this.
Until it is known how these images were stolen, the best anyone can do is apply common sense and ensure they use strong passwords to access their services. We also recommend that users check their Apple ID account.
The post Jennifer Lawrence: Victim of a security hole in iCloud? appeared first on MediaCenter Panda Security.
