Crypto ransomware, a relatively unknown phenomenon a couple of years ago, has exploded into one of the nastier malware problems for Internet users. Variants such as CryptoLocker and CryptoWall have been siphoning money from victims for some time, and now researchers have dissected a newer variant known as TorrentLocker and found that the creators made […]
Category Archives: Security
Security
Google Releases Security Update for Chrome
Original release date: September 10, 2014
Google has released Chrome 37.0.2062.120 for Windows, Mac and Linux. This update addresses multiple vulnerabilities one of which could potentially allow an attacker to cause a denial of service.
US-CERT encourages users and administrators to review the Google Chrome release blog and apply the necessary updates.
This product is provided subject to this Notification and this Privacy & Use policy.
DSA-3023 bind9 – security update
Jared Mauch reported a denial of service flaw in the way BIND, a DNS
server, handled queries for NSEC3-signed zones. A remote attacker could
use this flaw against an authoritative name server that served
NCES3-signed zones by sending a specially crafted query, which, when
processed, would cause named to crash.
DSA-3024 gnupg – security update
Genkin, Pipman and Tromer discovered a side-channel attack on Elgamal
encryption subkeys
(CVE-2014-5270).
Details Disclosed for Critical Vulnerability Patched in Webmin
The University of Texas information security office disclosed details of a vulnerability in remote management software Webmin that could allow someone to remotely delete files on a host server.
Apache Warns of Tomcat Remote Code Execution Vulnerability
Some older versions of Apache Tomcat, the company’s open source web server and servlet container, are vulnerable to remote code execution.
TLS landscape
Transport Layer Security (TLS) or, as it was known in the beginnings of the Internet, Secure Sockets Layer (SSL) is the technology responsible for securing communications between different devices. It is used everyday by nearly everyone using the globe-spanning network.
Let’s take a closer look at how TLS is used by servers that underpin the World Wide Web and how the promise of security is actually executed.
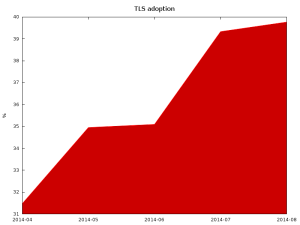
Adoption
Hyper Text Transfer Protocol (HTTP) in versions 1.1 and older make encryption (thus use of TLS) optional. Given that the upcoming HTTP 2.0 will require use of TLS and that Google now uses the HTTPS in its ranking algorithm, it is expected that many sites will become TLS-enabled.
Surveying the Alexa top 1 million sites, most domains still don’t provide secure communication channel for their users.
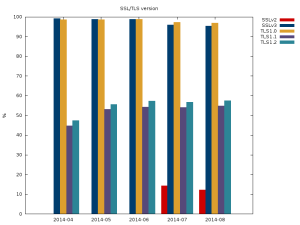
Additionally, if we look at the version of the protocol supported by the servers most don’t support the newest (and most secure) version of the protocol TLSv1.2. Of more concern is the number of sites that support the completely insecure SSLv2 protocol.
(There are no results for SSLv2 for first 3 months because of error in software that was collecting data.)
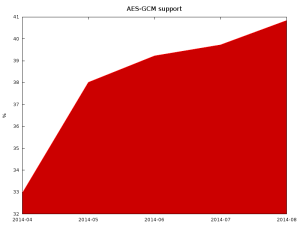
One of the newest and most secure ciphers available in TLS is Advanced Encryption Standard (AES) in Galois/Counter Mode (AES-GCM). Those ciphers provide good security, resiliency against known attacks (BEAST and Lucky13), and very good performance for machines with hardware accelerators for them (modern Intel and AMD CPUs, upcoming ARM).
Unfortunately, it is growing a bit slower than TLS adoption in general, which means that some of the newly deployed servers aren’t using new cryptographic libraries or are configured to not use all of their functions.
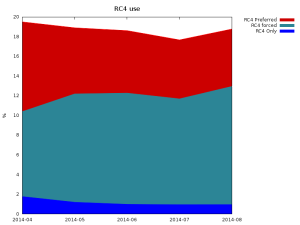
Bad recommendations
A few years back, a weakness in TLS 1.0 and SSL 3 was shown to be exploitable in the BEAST attack. The recommended workaround for it was to use RC4-based ciphers. Unfortunately, we later learned that the RC4 cipher is much weaker than it was previously estimated. As the vulnerability that allowed BEAST was fixed in TLSv1.1, using RC4 ciphers with new protocol versions was always unnecessary. Additionally, now all major clients have implemented workarounds for this attack, which currently makes using RC4 a bad idea.
Unfortunately, many servers prefer RC4 and some (~1%) actually support only RC4. This makes it impossible to disable this weak cipher on client side to force the rest of servers (nearly 19%) to use different cipher suite.
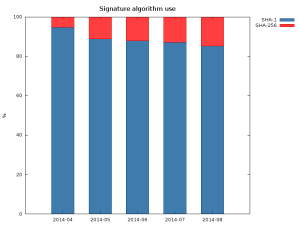
The other common issue, is that many certificates are still signed using the obsolete SHA-1. This is mostly caused by backwards compatibility with clients like Windows XP pre SP2 and old phones.
The sudden increase in the SHA-256 between April and May was caused by re-issuance of certificates in the wake of Heartbleed.
Bad configuration
Many servers also support insecure cipher suites. In the latest scan over 3.5% of servers support some cipher suites that uses AECDH key exchange, which is completely insecure against man in the middle attacks. Many servers also support single DES (around 15%) and export grade cipher suites (around 15%). In total, around 20% of servers support some kind of broken cipher suite.
While correctly implemented SSLv3 and later shouldn’t allow negotiation of those weak ciphers if stronger ones are supported by both client and server, at least one commonly used implementation had a vulnerability that did allow for changing the cipher suite to arbitrary one commonly supported by both client and server. That’s why it is important to occasionally clean up list of supported ciphers, both on server and client side.
Forward secrecy
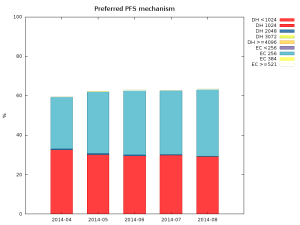
Forward secrecy, also known as perfect forward secrecy (PFS), is a property of a cipher suite that makes it impossible to decrypt communication between client and server when the attacker knows the server’s private key. It also protects old communication in case the private key is leaked or stolen. That’s why it is such a desirable property.
The good news is that most servers (over 60%) not only support, but will actually negotiate cipher suites that provide forward secrecy with clients that support it. The used types are split essentially between 1024 bit DHE and 256 bit ECDHE, scoring respectively 29% and 33% of all servers in latest scan. The amount of servers that do negotiate PFS enabled cipher suites is also steadily growing.
Summary
Most Internet facing servers are badly configured, sometimes it is caused by lack of functionality in software, like in case of old Apache 2.2.x releases that don’t support ECDHE key exchange, and sometimes because of side effects of using new software with old configuration (many configuration tutorials suggested using !ADH in cipher string to disable anonymous cipher suites, that unfortunately doesn’t disable anonymous Elliptic Curve version of DH – AECDH, for that, use of !aNULL is necessary).
Thankfully, the situation seems to be improving, unfortunately rather slowly.
If you’re an administrator of a server, consider enabling TLS. Performance issues when encryption was slow and taxing on servers are long gone. If you already use TLS, double check your configuration preferably using the Mozilla guide to server configuration as it is regularly updated. Make sure you enable PFS cipher suites and put them above non-PFS ciphers and that you as well as the Certificate Authority you’ve chosen, use modern crypto (SHA-2) and large key sizes (at least 2048 bit RSA).
If you’re a user of a server and you’ve noticed that the server doesn’t use correct configuration, try contacting the administrator – he may have just forgotten about it.
MS14-016 – Important: Vulnerability in Security Account Manager Remote (SAMR) Protocol Could Allow Security Feature Bypass (2934418) – Version: 1.2
Severity Rating: Important
Revision Note: V1.2 (September 10, 2014): Revised Update FAQ and entries in the Operating System column of the Affected Software table to further clarify what version of Active Directory must be installed on a system to be offered the update. These are informational changes only.
Summary: This security update resolves one privately reported vulnerability in Microsoft Windows. The vulnerability could allow security feature bypass if an attacker makes multiple attempts to match passwords to a username.
Adobe Releases Security Updates for Flash Player and Air
Original release date: September 09, 2014
Adobe has released security updates to address multiple vulnerabilities in Adobe Flash Player and Air for Windows, Macintosh and Linux. Exploitation of these vulnerabilities could potentially allow an attacker to take control of the affected system.
Â
Users and administrators are encouraged to review Adobe Security Bulletin APSB14-21 and apply the necessary updates.
Â
Â
This product is provided subject to this Notification and this Privacy & Use policy.
UPDATED: VMSA-2014-0006.10 – VMware product updates address OpenSSL security vulnerabilities
-----BEGIN PGP SIGNED MESSAGE-----
Hash: SHA1
- -----------------------------------------------------------------------
VMware Security Advisory
Advisory ID: VMSA-2014-0006.10
Synopsis: VMware product updates address OpenSSL
security vulnerabilities
Issue date: 2014-06-10
Updated on: 2014-09-09
CVE numbers: CVE-2014-0224, CVE-2014-0198, CVE-2010-5298, and
CVE-2014-3470
- -----------------------------------------------------------------------
1. Summary
VMware product updates address OpenSSL security vulnerabilities.
2. Relevant Releases
Big Data Extensions prior to 2.0.0
ESXi 5.5 without patch ESXi550-201406401-SG
ESXi 5.1 without patch ESXi510-201406401-SG
ESXi 5.0 without patch ESXi500-201407401-SG
Workstation 10.x prior to 10.0.3
Workstation 9.x prior to 9.0.4
Player 6.x prior to 6.0.3
Player 5.x prior to 5.0.4
Fusion 6.x prior to 6.0.4
Fusion 5.x prior to 5.0.5
Horizon Mirage Edge Gateway prior to 4.4.3
Horizon View prior to 5.3.2
Horizon View 5.3 Feature Pack X prior to Feature Pack 3
Horizon Workspace Server 1.5.x without patch horizon-nginx-rpm-
1.5.0.0-1876270.
x86_64.rpm
Horizon Workspace Server 1.8.x without patch horizon-nginx-rpm-
1.8.2.1820-1876338.
x86_64.rpm
Horizon View Clients prior to 3.0
vCD 5.5.x prior to 5.5.1.2
vCD 5.1.x prior to 5.1.3.1
vCenter prior to 5.5u1b
vCenter prior to 5.1 U2a
vCenter prior to 5.0U3a
vCenter Support Assistant prior to 5.5.1.1
vCloud Automation Center prior to 6.0.1.2
vCenter Configuration Manager prior to 5.7.2
vCenter Converter Standalone prior to 5.5.2
Converter Standalone prior to 5.1.1
Usage Manager prior to 3.3
vCenter Operations Manager prior to 5.8.2
vCenter Operations Manager prior to 5.7.3
vCenter Chargeback Manager 2.6 prior to 2.6.0.1
vCloud Networking and Security prior to 5.5.2.1
vCloud Networking and Security prior to 5.1.4.1
vSphere PowerCLI 5.x
vCSA prior to 5.5u1b
vCSA prior to 5.1u2a
vCSA prior to 5.0u3a
OVF Tool prior to 5.3.2
Update Manager prior to 5.5u1b
ITBM Standard prior to 1.1
VDDK prior to 5.5.2
VDDK prior to 5.1.3
VDDK prior to 5.0.4
NSX for Multi-Hypervisor 4.1.x prior to 4.1.3
NSX for Multi-Hypervisor 4.0.x prior to 4.0.4
NVP 3.0.x prior to 3.2.3
NSX 6.0.x for vSphere prior to 6.0.5
vFabric Web Server 5.x
Pivotal Web Server prior to 5.4.1
vCenter Site Recovery Manager prior to 5.5.1.1
vCenter Site Recovery Manager prior to 5.1.2.1
vCenter Site Recovery Manager prior to 5.0.3.2
vSphere Replication prior to 5.8
vSphere Replication prior to 5.5.1.1
vSphere SDK for Perl prior to 5.5 Update 2
3. Problem Description
a. OpenSSL update for multiple products.
OpenSSL libraries have been updated in multiple products to
versions 0.9.8za and 1.0.1h in order to resolve multiple security
issues.
The Common Vulnerabilities and Exposures project (cve.mitre.org)
has assigned the names CVE-2014-0224, CVE-2014-0198,
CVE-2010-5298, CVE-2014-3470, CVE-2014-0221 and CVE-2014-0195 to
these issues. The most important of these issues is
CVE-2014-0224.
CVE-2014-0198, CVE-2010-5298 and CVE-2014-3470 are considered to
be of moderate severity. Exploitation is highly unlikely or is
mitigated due to the application configuration.
CVE-2014-0221 and CVE-2014-0195, which are listed in the OpenSSL
Security Advisory (see Reference section below), do not affect
any VMware products.
CVE-2014-0224 may lead to a Man-in-the-Middle attack if a server
is running a vulnerable version of OpenSSL 1.0.1 and clients are
running a vulnerable version of OpenSSL 0.9.8 or 1.0.1. Updating
the server will mitigate this issue for both the server and all
affected clients.
CVE-2014-0224 may affect products differently depending on
whether the product is acting as a client or a server and of
which version of OpenSSL the product is using. For readability
the affected products have been split into 3 tables below,
based on the different client-server configurations and
deployment scenarios.
MITIGATIONS
Clients that communicate with a patched or non-vulnerable server
are not vulnerable to CVE-2014-0224. Applying these patches to
affected servers will mitigate the affected clients (See Table 1
below).
Clients that communicate over untrusted networks such as public
Wi-Fi and communicate to a server running a vulnerable version of
OpenSSL 1.0.1. can be mitigated by using a secure network such as
VPN (see Table 2 below).
Clients and servers that are deployed on an isolated network are
less exposed to CVE-2014-0224 (see Table 3 below). The affected
products are typically deployed to communicate over the
management network.
RECOMMENDATIONS
VMware recommends customers evaluate and deploy patches for
affected Servers in Table 1 below as these patches become
available. Patching these servers will remove the ability to
exploit the vulnerability described in CVE-2014-0224 on both
clients and servers.
VMware recommends customers consider
applying patches to products listed in Table 2 & 3 as required.
Column 4 of the following tables lists the action required to
remediate the vulnerability in each release, if a solution is
available.
Table 1
=======
Affected servers running a vulnerable version of OpenSSL 1.0.1.
VMware Product Running Replace with/
Product Version on Apply Patch
============== ======= ======= =============
ESXi 5.5 ESXi ESXi550-
201406401-SG
Big Data Extensions 1.1 2.0.0
vCenter Chargeback Manager 2.6 2.6.0.1
Horizon Workspace Server 1.5.x horizon-nginx-
rpm-1.5.0.0-
1876270.
x86_64.rpm
Horizon Workspace Server 1.8.x horizon-nginx-
rpm-1.8.2.1820-
1876338.
x86_64.rpm
Horizon Mirage Edge Gateway 4.4.x 4.4.3
Horizon View 5.x 5.3.2
Horizon View Feature Pack 5.x 5.3 FP3
NSX for Multi-Hypervisor 4.1.2 4.1.3
NSX for Multi-Hypervisor 4.0.3 4.0.4
NSX for vSphere 6.0.4 6.0.5
NVP 3.2.2 3.2.3
vCloud Networking and Security 5.5.2 5.5.2.1
vCloud Networking and Security 5.1.4 5.1.4.1
Pivotal Web Server 5.4 5.4.1
vFabric Web Server 5.x Pivotal Web
Server 5.4.1
Table 2
========
Affected clients running a vulnerable version of OpenSSL 0.9.8
or 1.0.1 and communicating over an untrusted network.
VMware Product Running Replace with/
Product Version on Apply Patch
============== ======= ======= =============
vCSA 5.5 5.5u1b
vCSA 5.1 5.1u2a
vCSA 5.0 5.0u3a
ESXi 5.1 ESXi ESXi510-
201406401-SG
ESXi 5.0 ESXi ESXi500-
201407401-SG
Workstation 10.x any 10.0.3
Workstation 9.x any 9.0.4
Fusion 6.x OSX 6.0.4
Fusion 5.x OSX 5.0.5
Player 6.x any 6.0.3
Player 5.x any 5.0.4
vCenter Chargeback Manager 2.5.x 2.6.0.1
Horizon Workspace Client 1.x OSX 1.8.2
Horizon Workspace Client 1.x Windows 1.8.2
Horizon View Client 2.x Android 3.0
Horizon View Client 2.x iOS 3.0
Horizon View Client 2.x OSX 3.0
Horizon View Client 2.x Windows 3.0
Horizon View Client 2.x WinStore 3.0
OVF Tool 3.5.1 3.5.2
OVF Tool 3.0.1 3.5.2
vCenter Operations Manager 5.8.x 5.8.2
vCenter Operations Manager 5.7.x 5.7.3
vCenter Support Assistant 5.5.1 5.5.1.1
vCD 5.5.1.x 5.5.1.2
vCD 5.1.x 5.1.3.1
vCenter Site Recovery Manager 5.5.x 5.5.1.1
vCenter Site Recovery Manager 5.1.x 5.1.2.1
vCenter Site Recovery Manager 5.0.3.x 5.0.3.2
vSphere Client 5.5 Windows 5.5u1b
vSphere Client 5.1 Windows 5.1u2a
vSphere Client 5.0 Windows 5.0u3a
Table 3
=======
The following table lists all affected clients running a
vulnerable version of OpenSSL 0.9.8 or 1.0.1 and communicating
over a trusted or isolated network.
VMware Product Running Replace with/
Product Version on Apply Patch
============== ======= ======= =============
vCenter Server 5.5 any 5.5u1b
vCenter Server 5.1 any 5.1u2a
vCenter Server 5.0 any 5.0u3a
Update Manager 5.5 Windows 5.5u1b
vCenter Configuration
Manager (VCM) 5.6 5.7.2
ITBM Standard 1.0.1 1.1
ITBM Standard 1.0 1.1
Studio 2.6.0.0 patch pending
Usage Meter 3.3 3.3.1
vCenter Converter Standalone 5.5 5.5.2
vCenter Converter Standalone 5.1 5.1.1
vCloud Automation Center 6.0.x 6.0.1.2
VIX API 1.12 patch pending
vMA (Management Assistant) 5.5.01 patch pending
vSphere PowerCLI 5.x See VMware
KB 2082132
vSphere Data Protection 5.5.6 patch pending
vSphere Data Protection 5.1.11 patch pending
vSphere Replication 5.5.1 5.5.1.1
vSphere Replication 5.6 5.8
vSphere SDK for Perl 5.5 5.5 Update 2
VDDK 5.5.x 5.5.2
VDDK 5.1.x 5.1.3
VDDK 5.0.x 5.0.4
4. Solution
Big Data Extensions 2.0.0
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-bde
ESXi 5.5, 5.1 and 5.0
----------------------------
Download:
https://www.vmware.com/patchmgr/findPatch.portal
Horizon Mirage Edge Gateway 4.4.3
---------------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-horizon-mirage
vCD 5.5.1.2
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download/vcloud-director
vCenter Server 5.5u1b, 5.1u2a, 5.0u3a
------------------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere
vCSA 5.5u1b, 5.1u2a and 5.0u3a
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere
Update Manager 5.5u1b
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere
VDDK 5.x
----------------------------
Downloads and Documentation:
https://www.vmware.com/support/developer/vddk
vCenter Configuration Manager (VCM) 5
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download_vcm
vCenter Operations Manager 5.8 and 5.7.3
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere-ops-mgr
OVF Tool 3.5.2
--------------
Download:
https://www.vmware.com/support/developer/ovf/
vCenter Converter Standalone 5.5.2
-----------------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-converter
Horizon View 5
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/downloadview
Horizon View 5.3 Feature Pack 3
-----------------------------------
Downloads and Documentation:
https://www.vmware.com/go/downloadview
Horizon Workspace Server 1.5 and 1.8.x
----------------------------
Release Notes and download:
http://kb.vmware.com/kb/2082181
Workstation
----------------------
https://www.vmware.com/go/downloadworkstation
Fusion
------------------
https://www.vmware.com/go/downloadfusion
VMware Player
------------------
https://www.vmware.com/go/downloadplayer
vCenter Server 5.1 Update 2a
----------------------------------------------------
Download link:
https://my.vmware.com/web/vmware/info/slug/datacenter_cloud_infrastructure/
vmware_vsphere/5_1
vCenter Server 5.0 Update 3a
----------------------------------------------------
Download link:
https://my.vmware.com/web/vmware/info/slug/datacenter_cloud_infrastructure/
vmware_vsphere/5_0
vCloud Networking and Security 5.5.2.1
------------------------------------
Download
https://my.vmware.com/web/vmware/details?downloadGroup=VCNS552_GA&productId
=353&rPId=5255
vCloud Networking and Security 5.1.4.1
------------------------------------
Download:
https://my.vmware.com/web/vmware/details?downloadGroup=VCNS514_GA&productId
=285&rPId=5131
NSX for Multi-Hypervisor, NSX for vSphere and NVP
-------------------------------------------------
Remediation Instructions and Download, available under support:
http://www.vmware.com/products/nsx
vCD 5.5.1.2 and vCD 5.1.3.1
---------------------------
Download link:
https://www.vmware.com/go/download-vcd-ns
VMware vCenter Chargeback Manager
---------------------------------
Download link:
https://www.vmware.com/go/download-chargeback
Converter Standalone 5.1.1
---------------------------
Download link:
https://www.vmware.com/go/download-converter
Usage Manager 3.3
-----------------
Downloads and Documentation:
https://communities.vmware.com/community/vmtn/vcd/vcloud_usage_meter
vCenter Support Assistant
--------------------------
Downloads:
https://www.vmware.com/go/download-vsphere
Pivotal Web Server 5.4.1
------------------------
https://my.vmware.com/web/vmware/details?downloadGroup=VF_530_PVTL_WSVR_541
&productId=335&rPId=6214
vCloud Automation Center
--------------------------
Downloads:
https://www.vmware.com/go/download-vcac
vCenter Site Recovery Manager 5.5.1.1
-------------------------------------
Remediation Instructions and Download:
http://kb.vmware.com/kb/2081861
vCenter Site Recovery Manager 5.1.2.1
-------------------------------------
Remediation Instructions and Download:
http://kb.vmware.com/kb/2081860
vCenter Site Recovery Manager 5.0.3.2
-------------------------------------
Remediation Instructions and Download:
http://kb.vmware.com/kb/2081859
vSphere Replication 5.8
-----------------------
Download:
https://my.vmware.com/web/vmware/details?downloadGroup=SDKPERL552&productId
=353
vSphere Replication 5.5.1.1
---------------------------
Remediation Instructions and Download:
http://kb.vmware.com/kb/2082666
ITBM Standard 1.1
-----------------
Download:
https://my.vmware.com/web/vmware/details?downloadGroup=ITBM-STD-110&product
Id=384&rPId=6384
Release Notes:
https://www.vmware.com/support/itbms/doc/itbm-standard-edition-11-release-n
otes.html
vSphere SDK for Perl 5.5 Update 2
----------------------------------
Download:
https://my.vmware.com/web/vmware/details?downloadGroup=VR580&productId=451&
rPId=6436
Release Notes:
https://www.vmware.com/support/vsphere-replication/doc/vsphere-replication-
58-release-notes.html
5. References
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0224
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0198
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-5298
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-3470
https://www.openssl.org/news/secadv_20140605.txt
http://www.gopivotal.com/security/cve-2014-0224
VMware Knowledge Base Article 2082132
http://kb.vmware.com/kb/2082132
- -----------------------------------------------------------------------
6. Change Log
2014-06-10 VMSA-2014-0006
Initial security advisory in conjunction with the release of
ESXi 5.5 updates on 2014-06-10
2014-06-12 VMSA-2014-0006.1
Updated security advisory in conjunction with the release of
Big Data Extensions 2.0.0, Horizon Mirage Edge Gateway 4.4.3,
vCD 5.5.1.2, vCenter Server 5.5u1b, vCSA 5.5u1b, and Update
Manager 5.5u1b on 2014-06-12
2014-06-17 VMSA-2014-0006.2
Updated security advisory in conjunction with the release of
ESXi 5.1 updates, VDDK 5.5.2, 5.1.3, and 5.0.4 on 2014-06-17
2014-06-24 VMSA-2014-0006.3
Updated security advisory in conjunction with the release of
Horizon View 5.3.2, Horizon View 5.3 Feature Pack 3,
vCenter Configuration Manager 5.7.2, vCenter
Converter Standalone 5.5.2, vCenter Operations
Manager 5.8.2, OVF Tool 5.3.2 on 2014-06-24
2014-07-01 VMSA-2014-0006.4
Updated security advisory in conjunction with the release of
ESX 5.0 patches, Workstation 10.0.3, Player 6.0.3, Fusion 6.0.4,
Horizon Workspace Server 1.5.x and 1.8.x updates, vCD
5.1.3.1, vCenter Server 5.1 update 2a and 5.0 update 3a,
vCSA 5.1 update 2a and 5.0 update 3a, Converter Standalone 5.1.1,
vCenter Chargeback Manager 2.6.0.1,
vCloud Networking and Security 5.5.2.1 and 5.1.4.1,
NSX for Multi-Hypervisor 4.1.3,
NSX for Multi-Hypervisor 4.0.4, NVP 3.2.3 and
NSX 6.0.5 for vSphere on 2014-07-01
2014-07-03 VMSA-2014-0006.5
Updated security advisory in conjunction with the release of
Workstation 9.0.4, Player 5.0.4, Fusion 5.0.5, vCenter Support
Assistant 5.5.1.1, on 2014-07-03
2014-07-08 VMSA-2014-0006.6
Updated security advisory in conjunction with the release of
vSphere PowerCLI 5.x on 2014-07-04 and Pivotal Web Server 5.4.1
on 2014-07-08
2014-07-10 VMSA-2014-0006.7
Updated security advisory in conjunction with the release of
vCloud Automation Center 6.0.1.2 and vCenter Operations Manager
5.7.3 on 2014-07-10
2014-07-18 VMSA-2014-0006.8
Updated security advisory in conjunction with the release of
patches for vCenter Site Recovery Manager 5.5.1.1 and
vSphere Replication 5.5.1.1 on 2014-07-17
2014-07-22 VMSA-2014-0006.9
Updated security advisory in conjunction with the release of
patches for vCenter Site Recovery Manager 5.1.2.1 and 5.0.3.2
on 2014-07-22
2014-09-09 VMSA-2014-0006.10
Updated security advisory in conjunction with the release of
patches for ITBM Standard 1.1, vSphere Replication 5.8 and
vSphere SDK for Perl 5.5 Update 2 on 2014-09-09. vFabric
Application Director has been removed from the table above since
it is not affected by this issue.
- -----------------------------------------------------------------------
7. Contact
E-mail list for product security notifications and announcements:
http://lists.vmware.com/cgi-bin/mailman/listinfo/security-announce
This Security Advisory is posted to the following lists:
security-announce at lists.vmware.com
bugtraq at securityfocus.com
fulldisclosure at seclists.org
E-mail: security at vmware.com
PGP key at: http://kb.vmware.com/kb/1055
VMware Security Advisories
http://www.vmware.com/security/advisories
VMware Security Response Policy
https://www.vmware.com/support/policies/security_response.html
VMware Lifecycle Support Phases
https://www.vmware.com/support/policies/lifecycle.html
Twitter
https://twitter.com/VMwareSRC
Copyright 2014 VMware Inc. All rights reserved.
-----BEGIN PGP SIGNATURE-----
Version: Encryption Desktop 10.3.0 (Build 8741)
Charset: utf-8
wj8DBQFUD16eDEcm8Vbi9kMRAgBdAJsG4mzXIKqUyD2j5rTkDDQvG9giYwCfTmv4
S8n3FBEzi2wj9s5V00WS7/4=
=2ZcF
-----END PGP SIGNATURE-----