Multiple unspecified vulnerabilities in Google Chrome before 38.0.2125.101 allow attackers to cause a denial of service or possibly have other impact via unknown vectors.
CVE-2014-3199 (chrome, enterprise_linux_desktop_supplementary, enterprise_linux_server_supplementary, enterprise_linux_server_supplementary_eus, enterprise_linux_workstation_supplementary)
The wrap function in bindings/core/v8/custom/V8EventCustom.cpp in the V8 bindings in Blink, as used in Google Chrome before 38.0.2125.101, has an erroneous fallback outcome for wrapper-selection failures, which allows remote attackers to cause a denial of service via vectors that trigger stopping a worker process that had been handling an Event object.
Previously undiscovered Bugzilla exploit patched
Bugzilla, the open source bug reporting and tracking tool used by Mozilla and many popular Linux distributions, has had a potentially damaging security flaw patched, reports Brian Krebs on his Krebs on Security website.
The post Previously undiscovered Bugzilla exploit patched appeared first on We Live Security.
![]()
How cookies work?

We all know the ‘Allow cookies?’ message. This option now appears in practically all websites. In fact, nowadays more people associate the term ‘cookies’ with its Internet use rather than with its edible origin.
Cookies are small data packets which Web pages load on to browsers for a whole range of reasons. Every time you return to the same URL, the computer sends back this little package of information to the server, which detects that you have returned to the page.
When you access your email account or Facebook profile, it is cookies that allow your user name and password to be saved, so the next time you won’t have to enter them again.
But apart from storing strings of digits and letters, webmasters can use these tools for monitoring the activity of Internet users.
These virtual spies collect information about your Internet habits: the pages you visit frequently and the topics that interest you. The problem is that they usually share this information with data analysis firms or those that design targeted marketing campaigns.
If, say, an ad for a food product appears on your screen after you visit a restaurant page, don’t be too surprised. Thanks to cookies, advertising can be tailored to consumers’ preferences.
Even though cookies are safe and won’t usually infect your computer with malware, it is not always clear in whose hands the collected data ends up or where it is stored.
A team of researchers from Queen Mary University, London, has managed to shed some light on this in one of its studies. They have basically been spying on the spies. They analyzed where the data of Internet users from around the world ended up in order to draw up a data circulation map.
The experts have focused on who is running cookies on user’s browsers. External companies (such as those marketing and data analysis firms mentioned above) send these data packets from a domain different to the site so they can be detected when they do this. With this methodology they were able to analyze the 500 most popular pages in 28 countries.
The results have shown that this practice extends across the world. You can also see in the image the areas of the planet where Internet user privacy is most compromised.
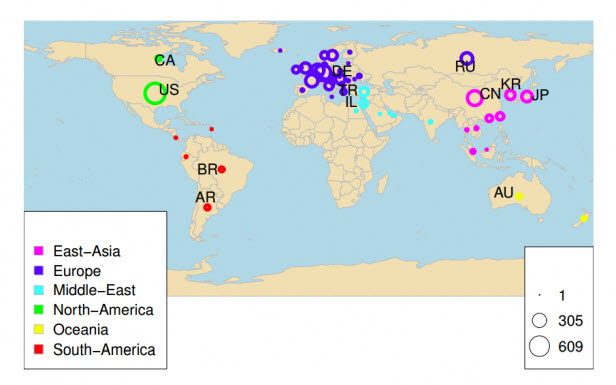
While in Europe, South America and Oceania the amount of local companies accessing user data is quite similar, the number is greater in Turkey and Israel. The origin of the snoopers is also interesting: most come from Russia or Germany. Those based in the USA often end up on browsers in the Middle East.
Scientists believe that this distribution reflects Internet privacy legislation in different countries. In most European countries, where there are laws regulating third-party access to user data, there aren’t so many ‘spies’ as in China or Turkey, where such rules are scarce. But spies are everywhere, so experts continue to call for tougher measures to combat the trafficking of personal information.
The post How cookies work? appeared first on MediaCenter Panda Security.
[Onapsis Security Advisory 2014-032] SAP BusinessObjects Persistent Cross Site Scripting
Posted by Onapsis Research Labs on Oct 08
Onapsis Security Advisory 2014-032: SAP BusinessObjects Persistent Cross
Site Scripting
1. Impact on Business
=====================
By exploiting this vulnerability a remote unauthenticated attacker would
be able to attack other users of the system.
Risk Level: Medium
2. Advisory Information
=======================
– Public Release Date: 2014-10-08
– Subscriber Notification Date: 2014-10-08
– Last Revised: 2014-09-17
-…
[Onapsis Security Advisory 2014-030] SAP Business Objects Denial of Service via CORBA
Posted by Onapsis Research Labs on Oct 08
Onapsis Security Advisory 2014-020: SAP Business Objects Denial of
Service via CORBA
1. Impact on Business
=====================
By exploiting this vulnerability a remote unauthenticated attacker would
be able to completely shut down the SAP Business Objects remotely.
Risk Level: High
2. Advisory Information
=======================
– Public Release Date: 2014-10-08
– Subscriber Notification Date: 2014-10-08
– Last Revised:…
[Onapsis Security Advisory 2014-029] SAP Business Objects Information Disclosure
Posted by Onapsis Research Labs on Oct 08
Onapsis Security Advisory 2014-020: SAP Business Objects Information
Disclosure
1. Impact on Business
=====================
A malicious user can discover information relating to valid users
using a vulnerable Business Objects Enterprise instance. This
information could be used to allow the malicious user to specialize
their attacks against the system.
Risk Level: Medium
2. Advisory Information
=======================
– Public…
[Onapsis Security Advisory 2014-027] SAP HANA Multiple Reflected Cross Site Scripting Vulnerabilities
Posted by Onapsis Research Labs on Oct 08
Onapsis Security Advisory 2014-027: SAP HANA Multiple Reflected Cross
Site Scripting Vulnerabilities
1. Impact on Business
=====================
By exploiting this vulnerability a remote unauthenticated attacker would
be able to attack other users of the system.
Risk Level: Medium
2. Advisory Information
=======================
– Public Release Date: 2014-10-08
– Subscriber Notification Date: 2014-10-08
– Last Revised:…
[Onapsis Security Advisory 2014-033] SAP Business Warehouse Missing Authorization Check
Posted by Onapsis Research Labs on Oct 08
Onapsis Security Advisory 2014-033: SAP Business Warehouse Missing
Authorization Check
1. Impact on Business
=====================
By exploiting this vulnerability an authenticated attacker will be able
to abuse of functionality that should be restricted and can disclose
technical information without having the right access permissions. This
information could be used to perform further attacks over the platform.
Risk Level: Low…
[Onapsis Security Advisory 2014-031] SAP Business Objects Information Disclosure via CORBA
Posted by Onapsis Research Labs on Oct 08
Onapsis Security Advisory 2014-031: SAP Business Objects Information
Disclosure via CORBA
1. Impact on Business
=====================
By exploiting this vulnerability a remote unauthenticated attacker would
be able to obtain information about the system that could be used to
further specialize attacks against the Business Objects platform.
Risk Level: Low
2. Advisory Information
=======================
– Public Release Date:…