HP Security Bulletin HPSBMU03075 – A potential security vulnerability has been identified with HP Network Node Manager I (NNMi) on Windows and Linux. This vulnerability could be exploited remotely to allow arbitrary code execution. Revision 1 of this advisory.
Debian Security Advisory 3021-1
Debian Linux Security Advisory 3021-1 – Multiple security issues have been found in file, a tool to determine a file type. These vulnerabilities allow remote attackers to cause a denial of service, via resource consumption or application crash.
HP Security Bulletin HPSBST03106
HP Security Bulletin HPSBST03106 – A potential security vulnerability has been identified in HP P2000 G3 MSA Array System running OpenSSL. This vulnerability could be exploited remotely resulting in unauthorized access or disclosure of information. Revision 1 of this advisory.
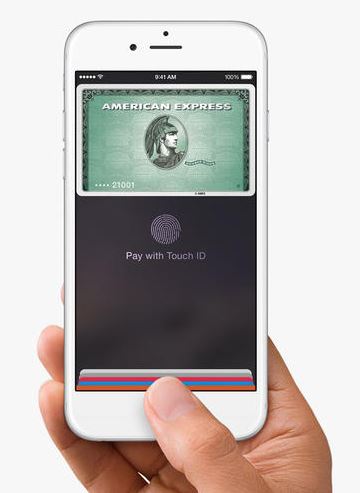
Leave your credit cards at home; Apple Pay lets you buy things with your phone
In the wake of the Target, and now Home Depot, security breaches, Apple Pay wants to provide a safer way to make a purchase.
Nestled in-between this week’s announcements of the iPhone 6 and the Apple Watch, Apple CEO Tim Cook announced a new mobile payment system called Apple Pay. New iPhone and Apple Watch owners can leave their credit and debit cards at home because the devices come with a chip that lets them tap-to-pay at major retailers.
When you are in one of 220,000 participating stores, like McDonald’s, Walgreens, Disney, or Macy’s, you use the magic of near-field communication (NFC) to hold your phone by a terminal to pay. It also requires that you place your finger over a sensor to verify your fingerprint. The Apple Watch works the same way, without the added security of the fingerprint, and syncs to your iPhone 5, iPhone 5c, and iPhone 5s. The payment system will work with American Express, Mastercard, and Visa.
Sounds pretty good. But, Google Wallet, PayPal and other NFC systems have failed to really take off; will Apple give us a better way? I asked mobile malware analyst Filip Chytrý to share his thoughts about the security of Apple Pay.
Deborah: From a security perspective, what do you think about Apple Pay?
Filip: I have some concerns. Communications between your device or watch is through Bluetooth, and we have already seen many incidences of intercepted communication between two devices using a man-in-the-middle attack. Generally, anytime you use a pay system there is communication between the phone or watch over Bluetooth. This communication works over a much longer distance than NFC, so payment interception would be easier.
Deborah: I understand the convenience of paying with Apple Pay, but how is this more secure than paying with a credit card?
Filip: Apple says, that “Each transaction is authorized with a one-time unique number, and instead of using the security code from the back of your card, Apple Pay creates a “dynamic security code†to securely validate each transaction.“ It really depends on the type of encryption which is used, but I have to admit this sounds pretty cool, but who knows how long it’s going to take to decrypt this system.
Deborah: It has to be better than the magnetic stripe cards that are still widely used in the USA. Credit card companies have given their customers until 2015 to make the transition to EMV cards using smartchip technology. These cards are supposed to help increase security and reduce fraud. Isn’t that good enough?
Filip: Generally, Apple Pay sounds like it is better secured than the current magnetic stripe cards. NFC payments are just tags which can be easily copied, but magnetic stripes are even worse. A PIN number adds an extra layer which is good, but Apple Pay might provide an even better way in future.
Deborah: Other than the basic security concerns, what happens when your phone battery dies (this will happen to me when I am on a deserted rural highway and need to fill up with gas) or you spill your coffee on it before you can pay, or you break your finger and it’s in a cast?
Filip: Those are real world problems that can’t be solved by Apple. ![]() But you’re an Android user, right? Didn’t you have a Nexus 4?
But you’re an Android user, right? Didn’t you have a Nexus 4?
Deborah: Yes, I did. Until I accidentally went in the swimming pool with it. ![]()
Filip: Not even avast! Mobile Security can protect you from that! But still, you will find this hilarious.
Thank you for using avast! Antivirus and recommending us to your friends and family. For all the latest news, fun and contest information, please follow us on Facebook, Twitter, Google+ and Instagram. Business owners – check out our business products.
Cisco Integrated Management Controller Vulnerability
Original release date: September 11, 2014
Cisco has released an advisory to address a vulnerability in the Cisco Integrated Management Controller (Cisco IMC) SSH module of the Cisco Unified Computing System E-Series Blade servers that could allow an unauthenticated, remote attacker to cause a denial of service condition. Migration to release 2.3.1 is available for Cisco IMC Software versions 1.0.1, 1.0.2, 2.1.0, and 2.2.0.
Users and administrators are encouraged to review the Cisco Advisory and apply the necessary updates.
This product is provided subject to this Notification and this Privacy & Use policy.
Key Flaw Enables Recovery of Files Encrypted by TorrentLocker
Crypto ransomware, a relatively unknown phenomenon a couple of years ago, has exploded into one of the nastier malware problems for Internet users. Variants such as CryptoLocker and CryptoWall have been siphoning money from victims for some time, and now researchers have dissected a newer variant known as TorrentLocker and found that the creators made […]
Winners of the ‘Betatester 2015′ competition
At last we can announce the names of the winners of the Panda Global Protection 2015 beta competition! ![]()
Our Betatester of the Year and winner of €600 is:
- Saravana Kumar S., India
The winners of €200 are:
- Anil Kumar E.S, India
- Jayakrishnan P., India
- Alex Molina, Spain
- Binshad Shahul, India
- HUANGÂ JING-KAI, Taiwan
- Andreas Ntonas, de Greece
- Kevin Appel, Switzerland
- Lauri Säde, Estonia
- Saqiya Maghisla, India
We have also awarded another 250 prizes of a one-year Panda Global Protection 2015 licence for three devices.
Thank you very much to all those who entered for your comments and suggestions!
More | Maximum protection with Panda Security’s new 2015 consumer solutions
The post Winners of the ‘Betatester 2015′ competition appeared first on MediaCenter Panda Security.
5 million Gmail passwords leaked

Do you have a Gmail account? This may interest you! A Russian cybersecurity forum has published a file containing more than 5 million Gmail accounts.
According to several experts, more than 60% of the username and password combinations were valid. However, Google says that the information is “outdated“, that is, these accounts have been suspended or the users no longer access them.
In a statement, Google said that it has no evidence that its systems have been compromised, but explains that “whenever we become aware that accounts may have been compromised, we take steps to help those users secure their accounts.“
The file published mainly contains British, Spanish and Russian accounts. If you want to know whether your account is on the list of those affected, you can do so here.
Panda Security recommends you increase the security of your passwords and use two-step verification of your Gmail account.
More | How to increase the privacy of your Gmail account
The post 5 million Gmail passwords leaked appeared first on MediaCenter Panda Security.
Facebook tag – fears over “Faceprints†after genetic match
A young man who got an email from Facebook ‘identifying’ him via Facebook tag in a series of photographs which turned out to be his mother as a young woman, says that the “oddly compelling†incident “opens the door to larger and more difficult questions,†according to a report in The Verge.
Specifically, the incident raises questions over what else Facebook’s algorithms can do.
Clearly in this case, they made an error, Fred Benenson, a data scientist at KickStarter, says, but the inadvertent ‘tagging’ shows off that the algorithm currently in use on Facebook to ‘tag’ photos can, in theory at least, trace people’s families via genetic traits translated into their faces.
“What about the cases where this algorithm isn’t used for fun photo tagging?†Benenson said to The Verge via email.
Facebook tag: What can this technology do?
“What if another false positive leads to someone being implicated for something they didn’t do? Facebook is a publicly traded company that uses petabytes of our personal data as their business model — data that we offer to them, but at what cost?”
NEC’s Neoface biometric software is already being used by police forces in the U.S. and the UK to identify people from video footage, as reported by We Live Security.
Facebook’s photo tagging is currently only used within the site, and is an option the user can control. The site has refused to say how they might use this data in future.
Facebook’s faceprints are already controversial. When Facebook extended the reach of its ‘faceprints’ so it could identify people via profile photos, as well as those they were tagged in, the ‘feature’ was banned in Europe.
Controversial technology
Senator Al Franken said in a press release, “How many Faceprints does Facebook have? . “Presumably, this would lead to a significant expansion of Facebook’s faceprint database. It would also likely capture some of Facebook’s least active users—those who are visible in their public profile photo but are not tagged in any other photos. These people are often less active users who may not be aware of Facebook’s privacy changes. I urge Facebook to reconsider this change.”
Facebook has already extended the ‘reach’ of tagging, by allowing brands to reach into people’s news feeds by ‘tagging’ other brands or celebrities, according to Marketing Land, and thus reaching the news feeds of people who did not opt to follow them.
Benenson’s case shows off, The Verge says, the power of such algorithms to identify people by family affiliation, race, and even regardless of age: if someone has posted a picture on Facebook, the site will be able to identify them years later.
Facebook’s current face-matching algorithm is limited in scope, at least compared to an algorithm unvveiled as part of one of the networking giant’s AI research projects.
Deepface was one of these – and can match two previously unseen photos of the same face with 97.25% accuracy – humans can do the same with around 97.5% accuracy, a difference which TechCrunch describes as “pretty much on parâ€.
Deepface: The alarming ‘next step’
It’s a huge leap forward in the technology, which some see as having potentially alarming implications for privacy.
Although Deepface is a research project, and unrelated to the technology used on the site, it “closes the vast majority of the performance gap†with human beings according to the Facebook researchers behind it (PDF research paper here), and can recognize people regardless of the orientation of their face, lighting conditions and image quality.
Publications such as Stuff magazine describe the technology as “creepyâ€, saying that were it implemented “in the wild†it should make site users “think twice†about posting images such as “selfies.â€
Deepface uses deep learning to leap ahead of current technology – an area of AI which uses networks of simulated brain cells  to ‘recognize’ patterns in large datasets, according to MIT’s Technology Review.
The post Facebook tag – fears over “Faceprints†after genetic match appeared first on We Live Security.
![]()
Salesforce software – millions of users at risk of Dyre malware
A strain of malware which previously targeted banks has turned its attention to users of the popular Customer Relationship Management (CRM) software Salesforce, used by 100,000 organizations and millions of subscribers, according to SC Magazine’s report.
Dyre, detected by ESET software as Win32/Battdil.A, is believed to be an entirely new strain of malware, and has in the past targeted users of large banks, siphoning data from machines to steal logins, with additional features allowing it to bypass some two-factor authentication systems.
Salesforce software posted a warning on its site this month saying, “Dyre malware (also known as Dyreza), which typically targets customers of large, well-known financial institutions, may now also target some Salesforce users. If we determine that a customer has been impacted by this malware, we will reach out to them with next steps and further guidance.â€
Dyre has previously targeted Bank of America and Citigroup customers, as well as a number of British banks such as NatWest. It is thought to be delivered as a “service” to criminal customers: on sale to the highest bidder.
Salesforce software: Under threat from hi-tech malware
The Register says of the remote-access Trojan (RAT), “Once it’s installed on a Windows PC, usually via a phishing attack, the software nasty then looks out for data sent from web browsers – even SSL-encrypted data – and siphons it off to its masters.â€
It’s unclear why Salesforce software users are being targeted. SC Magazine speculates that the switch may be due to a specific order from a “customerâ€.
The magazine points out that while the company does not publish specific customer numbers of its Salesforce software, it’s estimated that 160,000 organizations and around five million subscribers use the cloud software.
Dyre: New strain of malware on sale to highest bidder
Named Dyre, or Dyreza (and detected by ESET software as Win32/Battdil.A), the Trojan software was discovered by researchers investigating a phishing scam that was spreading via Dropbox. It is believed to be a completely new family of malware, similar to but sufficiently distinct from, the Zeus malware. The news that it is targeting Salesforce software users is an entirely new “use” for the malware.
Dyre was initially designed to target certain banks in particular – Bank of America, CitiGroup, NatWest, RBS and Ulsterbank. It is thought to be an example of ‘crime-as-a-service’ – malware for hire to the highest bidder. It has been found able to bypass both SSL encryption and two-factor authentication systems.
The phishing campaign first used to spread the malware worked via asking users to download a zip file that claims to contain invoices or federal tax information. Dropbox quickly removed the links from its system, but the hackers switched to Cubby, a similar service, to continue their campaign.
The post Salesforce software – millions of users at risk of Dyre malware appeared first on We Live Security.
![]()