-----BEGIN PGP SIGNED MESSAGE-----
Hash: SHA1
- ------------------------------------------------------------------------
VMware Security Advisory
Advisory ID: VMSA-2014-0007.2
Synopsis: VMware product updates address security vulnerabilities in
Apache Struts library
Issue date: 2014-06-24
Updated on: 2014-09-09
CVE number: CVE-2014-0050, CVE-2014-0094, CVE-2014-0112
- ------------------------------------------------------------------------
1. Summary
VMware product updates address security vulnerabilities in Apache
Struts library
2. Relevant releases
VMware vCenter Operations Management Suite prior to 5.8.2
VMware vCenter Operations Management Suite prior to 5.7.3
VMware vCenter Orchestrator prior to 5.5.2
3. Problem Description
a. The Apache Struts library is updated to version 2.3.16.2 to
address multiple security issues.
The Common Vulnerabilities and Exposures project (cve.mitre.org)
has assigned the names CVE-2014-0050, CVE-2014-0094, and
CVE-2014-0112 to these issues.
CVE-2014-0112 may lead to remote code execution. This issue was
found to be only partially addressed in CVE-2014-0094.
CVE-2014-0050 may lead to a denial of service condition.
vCenter Operations Management Suite (vCOps) is affected by both
CVE-2014-0112 and CVE-2014-0050. Exploitation of CVE-2014-0112
may lead to remote code execution without authentication.
vCenter Orchestrator (vCO) is affected by CVE-2014-0050 and not
by CVE-2014-0112.
Workaround
A workaround for CVE-2014-0112 is documented in VMware Knowledge Base
article 2081470.
Column 4 of the following table lists the action required to
remediate the vulnerability in each release, if a solution is
available.
VMware Product RunningReplace with/
Product Version on Apply Patch
========== ======= ========================
vCOPS 5.8.x any vCOPS 5.8.2
vCOPS 5.7.x any vCOPS 5.7.3
vCO 5.5 any vCO 5.5.2
vCO 5.1 any patch pending
vCO 4.2 any patch pending
4. Solution
Please review the patch/release notes for your product and version
and verify the checksum of your downloaded file.
vCenter Operations Management Suite 5.8.2 and 5.7.3
---------------------------------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vcops
vCenter Orchestrator 5.5.2
--------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere
5. References
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0050
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0094
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0112
http://kb.vmware.com/kb/2081470
- ------------------------------------------------------------------------
6. Change log
2014-06-24 VMSA-2014-0007
Initial security advisory in conjunction with the release of vCenter
Operations Management Suite 5.8.2 on 2014-06-24.
2014-07-11 VMSA-2014-0007.1
Updated security advisory in conjunction with the release of vCenter
Operations Management Suite 5.7.3 on 2014-07-10.
2014-09-09 VMSA-2014-0007.2
Updated security advisory in conjunction with the release of vCenter
Orchestrator 5.5.2 on 2014-09-09.
- ------------------------------------------------------------------------
7. Contact
E-mail list for product security notifications and announcements:
http://lists.vmware.com/cgi-bin/mailman/listinfo/security-announce
This Security Advisory is posted to the following lists:
security-announce at lists.vmware.com
bugtraq at securityfocus.com
fulldisclosure at seclists.org
E-mail: security at vmware.com
PGP key at: http://kb.vmware.com/kb/1055
VMware Security Advisories
http://www.vmware.com/security/advisories
VMware Security Response Policy
https://www.vmware.com/support/policies/security_response.html
VMware Lifecycle Support Phases
https://www.vmware.com/support/policies/lifecycle.html
Twitter
https://twitter.com/VMwareSRC
Copyright 2014 VMware Inc. All rights reserved.
-----BEGIN PGP SIGNATURE-----
Version: Encryption Desktop 10.3.0 (Build 8741)
Charset: utf-8
wj8DBQFUD2OBDEcm8Vbi9kMRAvS6AKDqvOoAKkUoghqYONuEBm98u8/ZoACg1/s3
Sxk/o2UW00LIgdOXpUKB9D4=
=nRjh
-----END PGP SIGNATURE-----
UPDATED: VMSA-2014-0007.2 – VMware product updates address security vulnerabilities in Apache Struts library
-----BEGIN PGP SIGNED MESSAGE-----
Hash: SHA1
- ------------------------------------------------------------------------
VMware Security Advisory
Advisory ID: VMSA-2014-0007.2
Synopsis: VMware product updates address security vulnerabilities in
Apache Struts library
Issue date: 2014-06-24
Updated on: 2014-09-09
CVE number: CVE-2014-0050, CVE-2014-0094, CVE-2014-0112
- ------------------------------------------------------------------------
1. Summary
VMware product updates address security vulnerabilities in Apache
Struts library
2. Relevant releases
VMware vCenter Operations Management Suite prior to 5.8.2
VMware vCenter Operations Management Suite prior to 5.7.3
VMware vCenter Orchestrator prior to 5.5.2
3. Problem Description
a. The Apache Struts library is updated to version 2.3.16.2 to
address multiple security issues.
The Common Vulnerabilities and Exposures project (cve.mitre.org)
has assigned the names CVE-2014-0050, CVE-2014-0094, and
CVE-2014-0112 to these issues.
CVE-2014-0112 may lead to remote code execution. This issue was
found to be only partially addressed in CVE-2014-0094.
CVE-2014-0050 may lead to a denial of service condition.
vCenter Operations Management Suite (vCOps) is affected by both
CVE-2014-0112 and CVE-2014-0050. Exploitation of CVE-2014-0112
may lead to remote code execution without authentication.
vCenter Orchestrator (vCO) is affected by CVE-2014-0050 and not
by CVE-2014-0112.
Workaround
A workaround for CVE-2014-0112 is documented in VMware Knowledge Base
article 2081470.
Column 4 of the following table lists the action required to
remediate the vulnerability in each release, if a solution is
available.
VMware Product RunningReplace with/
Product Version on Apply Patch
========== ======= ========================
vCOPS 5.8.x any vCOPS 5.8.2
vCOPS 5.7.x any vCOPS 5.7.3
vCO 5.5 any vCO 5.5.2
vCO 5.1 any patch pending
vCO 4.2 any patch pending
4. Solution
Please review the patch/release notes for your product and version
and verify the checksum of your downloaded file.
vCenter Operations Management Suite 5.8.2 and 5.7.3
---------------------------------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vcops
vCenter Orchestrator 5.5.2
--------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere
5. References
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0050
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0094
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0112
http://kb.vmware.com/kb/2081470
- ------------------------------------------------------------------------
6. Change log
2014-06-24 VMSA-2014-0007
Initial security advisory in conjunction with the release of vCenter
Operations Management Suite 5.8.2 on 2014-06-24.
2014-07-11 VMSA-2014-0007.1
Updated security advisory in conjunction with the release of vCenter
Operations Management Suite 5.7.3 on 2014-07-10.
2014-09-09 VMSA-2014-0007.2
Updated security advisory in conjunction with the release of vCenter
Orchestrator 5.5.2 on 2014-09-09.
- ------------------------------------------------------------------------
7. Contact
E-mail list for product security notifications and announcements:
http://lists.vmware.com/cgi-bin/mailman/listinfo/security-announce
This Security Advisory is posted to the following lists:
security-announce at lists.vmware.com
bugtraq at securityfocus.com
fulldisclosure at seclists.org
E-mail: security at vmware.com
PGP key at: http://kb.vmware.com/kb/1055
VMware Security Advisories
http://www.vmware.com/security/advisories
VMware Security Response Policy
https://www.vmware.com/support/policies/security_response.html
VMware Lifecycle Support Phases
https://www.vmware.com/support/policies/lifecycle.html
Twitter
https://twitter.com/VMwareSRC
Copyright 2014 VMware Inc. All rights reserved.
-----BEGIN PGP SIGNATURE-----
Version: Encryption Desktop 10.3.0 (Build 8741)
Charset: utf-8
wj8DBQFUD2OBDEcm8Vbi9kMRAvS6AKDqvOoAKkUoghqYONuEBm98u8/ZoACg1/s3
Sxk/o2UW00LIgdOXpUKB9D4=
=nRjh
-----END PGP SIGNATURE-----
The Net Neutrality Battle Is Like Gangs .. It Never Dies
Today companies and public interest organizations across the country are protesting to urge the U.S. Federal Communications Commission to maintain the principle of net neutrality on the Internet. This battle has been going on for many years as different interests try to create public policies that best serve their own business goals. This isn’t inherently bad except when if it’s at the expense of users and broader public interests. ISPs and cable providers are proposing a scheme that would allow web sites and services providers to pay more so their sites could be accessed faster by users online, effectively creating a “fast lane†and a “slow lane†on the Internet. This is a fine idea if you can pay and you’re in the fast lane, but unfortunately for those that can’t pay, their users (perhaps you and me) will likely get a degraded and slower Internet experience. It will also make the web sites and services for those that can’t pay less competitive and further accelerate the digital divide.
Net neutrality is a core principle that’s made the Internet work for a long time. It ensures that all content is treated equally and without discrimination by those that pass the bits along. For example, imagine if Comcast, the largest ISP, concludes the proposed merger with Time Warner, the second largest ISP (and which also owns HBO), could make online access to their own HBO content faster than other video content provided by their competitors like Apple, Netflix, Roku. Suppose they didn’t like editorials that were critical of their organization, and they made it harder for people to access it by making it slow. The Internet wouldn’t work and we wouldn’t have the robust market of ideas that the Internet affords us. Of course there are reasonable network management requirements that may impinge on the ideological goal, but net neutrality as a principle enables the Internet to fulfill its potential as an information medium that provides a rich, uncensored, although sometimes messy, diverse set of ideas and information.
Today, AVG joined many others in the “Internet Slowdown†campaign to encourage the FCC to take a stand and reject policies that would undermine net neutrality. And just like in the movie “Colors†unless you take action, this issue will never die. You can learn more in this nifty infographic called A Guide to the Open Internet or find out how to let your voice be heard at Fight for the Future.
![]()
![]()
DSA-3020 acpi-support – security update
During a review for EDF, Raphael Geissert discovered that the
acpi-support package did not properly handle data obtained from a
user’s environment. This could lead to program malfunction or allow a
local user to escalate privileges to the root user due to a programming
error.
DSA-3022 curl – security update
Two vulnerabilities have been discovered in cURL, an URL transfer
library. They can be use to leak cookie information:
Microsoft Releases September 2014 Security Bulletin
Original release date: September 09, 2014
Microsoft released updates to address vulnerabilities in Windows, .NET Framework, Internet Explorer and Lync Server as part of the Microsoft Security Bulletin Summary for September 2014. Some of these vulnerabilities could allow remote code execution, elevation of privilege, or denial of service.
US-CERT encourages users and administrators to review the bulletin and apply the necessary updates.
Â
This product is provided subject to this Notification and this Privacy & Use policy.
Adobe Patches Host of Memory Bugs in Flash Player
Adobe announced security updates and a new version of Flash Player for Windows, Mac and Linux; the company also announced it was postponing a scheduled update for Reader and Acrobat.
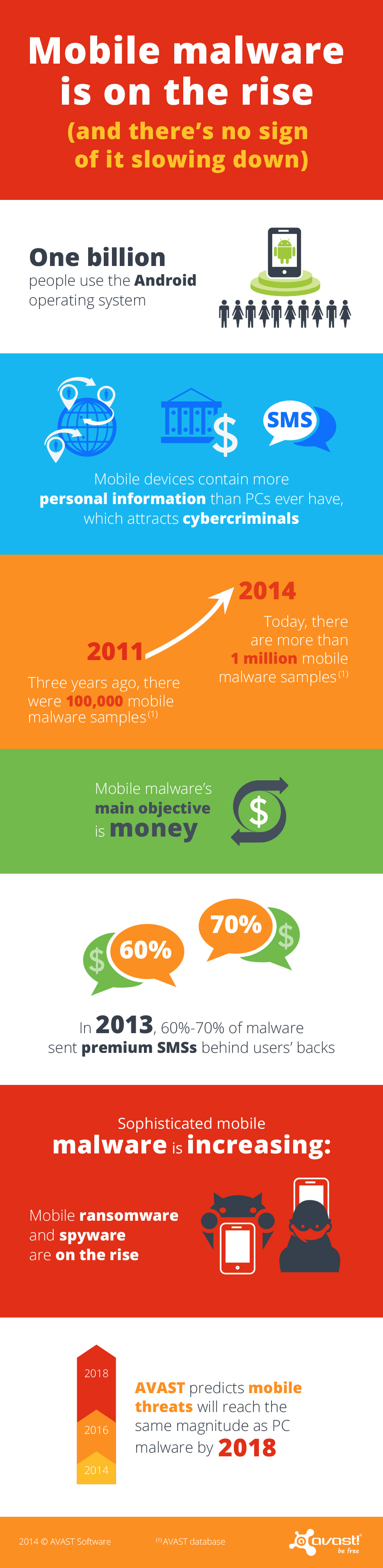
As Mobile Malware Hits the Million Samples Mark It Becomes More Devious than Ever Before
Mobile malware is growing exponentially. We now have more than 1 million malicious samples in our database, up from 100,000 in 2011. Still relatively young, most mobile malware has a pretty simple structure, yet it is designed to effectively steal people’s money. Newer mobile malware is, however, adapting and evolving, slowly embracing more deceitful and complex tactics to target users.
PC malware authors started in a garage, mobile malware authors in an office
Mobile malware is undergoing a similar development as PC malware did years ago with two significant differences: First, PC malware, in its early stages, was created by hobbyists and has only slowly evolved into a serious business within the last 10 years. Mobile malware, even with its simple structure, has been a serious business from the get-go. Smartphones and tablets are capable of gathering and storing more personalized data than PCs ever did – there is an abundance of valuable data to collect, including personal data and financial information. Thus, the focus of mobile malware has always been on monetization, meaning that even early mobile malware posed real-life threats to its victims, stealing money from them. Secondly, even though malware targeting smartphones and tablets is still young, it’s developing much faster than PC malware did in its initial years.
There are multiple entry points for mobile malware; apart from malicious apps placed in app stores and in-app ads linking to malicious content, malware authors also often take advantage of bugs in mobile operating systems, in popular apps or carrier billing structures. In 2013, around 60 to 70% of malware was tailored to send premium text messages behind users’ backs, a simple trick malware authors took advantage of to get into people’s wallets. The industry is catching up to malware and retaliating – carriers in the US and other countries have banned premium text messaging services. As the industry reacts, mobile malware authors start thinking of and using much more sophisticated and deceitful ways to get to people’s money.
The next generation of mobile malware
Elaborate malware, such as ransomware and spyware, is on the rise and is slowly taking control of mobile devices and the pool of potential victims can only get larger. Google now has more than 1 billion Android users. Formerly only known on the PC platform, a Cryptolocker-like ransomware has recently targeted Android devices for the first time, scaring users by holding their devices hostage, claiming to encrypt files until the user paid the ransom. Mobile spyware, on the other hand, is capable of tracking user location and a variety of other personal data, which can later be used to hack accounts or for identity theft.
We predict that with the emergence of new technologies, malware authors will find new ways of taking advantage of them. For example, as the use of new payment methods like Near Field Payment (NFC) increases, we expect hackers will change the way they go after money.
Users need to become aware of how valuable smartphones really are – not just the hardware, but the data it contains
Mobile threats are increasing – we expect them to reach the same magnitude as PC malware by 2018. However, out of the more than 1 billion smartphones that were shipped globally last year, only a small percentage are currently protected with antivirus software.
To make mobile devices safer and more secure, we need to collectively work together – the security industry, carriers, app store providers and consumers. At AVAST, we are constantly refining our tactics to detect mobile malware, to protect our users with our free and paid solutions. Actions like major carriers in the US, Brazil and the UK no longer billing customers for most forms of commercial Premium SMS messages, thus shutting an important door for malware creators, are a great initiative – and we hope carriers in other countries will follow this step, soon. Also, stricter security rules for apps on Google Play and other app stores could help make some types of malware extinct.
In the end, it’s also up to users to protect their devices and data with security solutions. People need to understand that there are new threats being built to target their mobile devices. Phones and tablets contain people’s personal treasures, in the form of data, whether that be personal information about loved ones or bank details – all of which is interesting for cybercriminals. Therefore, it is essential that people care for their smartphones and tablets in the same way as they protect their PC, the majority of which has antivirus installed.
Thank you for using avast! Antivirus and recommending us to your friends and family. For all the latest news, fun and contest information, please follow us on Facebook, Twitter and Google+. Business owners – check out our business products.
Â
Chat apps leak: Billion app users from OKCupid to Grindr at risk
Nearly a billion users of a dozen chat apps for Android including popular apps such as Instagram, Oovoo, OKCupid and Grindr could be at risk from eavesdroppers and snoopers after University of New Haven researchers found serious data leakage problems.
With many of the most popular chat apps on Android affected, tech news site CNET calculates that nearly a billion (968 million) users could be putting highly private data in the hands of apps that transmit and store it unencrypted.
Many of the Android apps (the researchers focused on Android rather than iOS, although there is no evidence the iOS apps behave differently), send text wirelessly unencrypted, and store images on servers for weeks without encryption or authentication.
Chat apps leak: 12 Android apps leak text and images
According to CNET’s report, the following apps sent text, images, location maps and video unencrypted – Instagram, OKCupid, OoVoo, Tango, Kik, Nimbuzz, MeetMe, MessageMe, TextMe, Grindr, HeyWire, Hike and TextPlus.
The site notes that not every app sent every form of media unencrypted, but said that all sent at least some forms, from pictures to text in unencrypted forms.
Others stored media such as images on servers unencrypted and without any form of authentication “for weeksâ€.
‘Sniffer’ software reveals leaks
The researchers used PC ‘sniffer’ software such as Wireshark and Network Miner to monitor the data transmitted by the apps, and found images and text transmitted and stored unencrypted – and potentially at risk from snoopers.
In the series of YouTube videos, one researcher says, “We recorded network traffic in Wireshark, to see if files remained on the server. For Instagram, we found an image stored in their servers, unencrypted and without authentication.â€
“Next, we opened up Oovoo and sent the keyword “Sparklehorse,†and it was picked up in Network Miner. Next we had Oovoo send an image. It was also picked up in Network Miner.â€
CNET reports that few of the apps had replied to requests for further information, but that Grindr had said, “We monitor and review all reports of security issues regularly. As such, we continue to evaluate and make ongoing changes as necessary to protect our users.”
The post Chat apps leak: Billion app users from OKCupid to Grindr at risk appeared first on We Live Security.
![]()
Research Finds No Large Scale Heartbleed Exploit Attempts Before Vulnerability Disclosure
In the days and weeks following the public disclosure of the OpenSSL Heartbleed vulnerability in April, security researchers and others wondered aloud whether there were some organizations–perhaps the NSA–that had known about the bug for some time and had been using it for targeted attacks. A definitive answer to that question may never come, but […]