The OLE preview generation in Apache OpenOffice before 4.1.1 and OpenOffice.org (OOo) might allow remote attackers to embed arbitrary data into documents via crafted OLE objects.
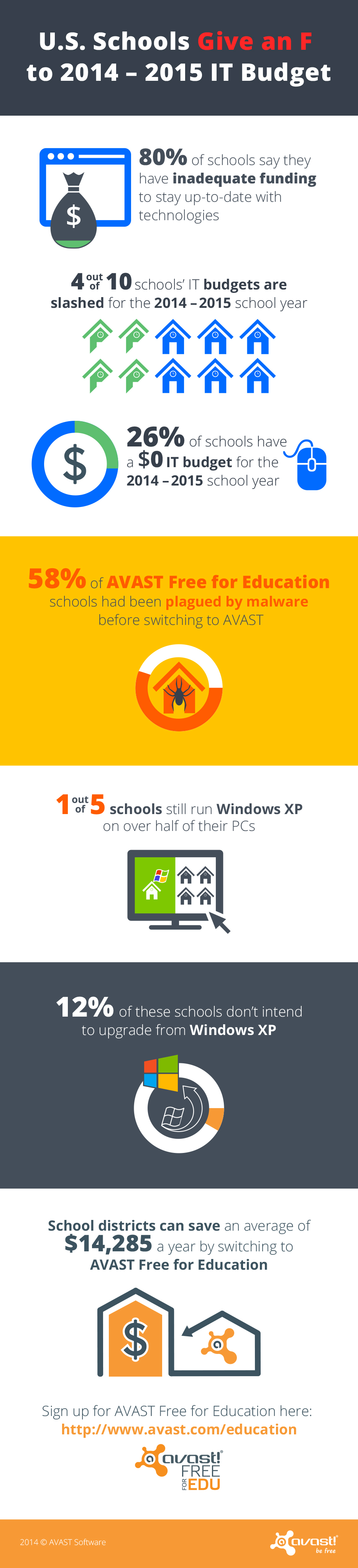
U.S. schools give an F to 2014-15 IT budget
AVAST Free for Education protects schools while significantly decreasing IT costs for security.
The beginning of the 2014/2015 school year is here. Parents and children are ready after a long summer break, but are schools prepared for the start of the new academic year?
AVAST surveyed more than 900 school IT professionals who participate in the AVAST Free for Education program and found that in terms of technology, schools are not as well equipped as parents expect.
- 8 out of every 10 schools surveyed by AVAST said they do not feel they have adequate funding to keep up-to-date with technologies
- 1 out of 5 schools still run Windows XP, and 12% of these schools said they do not intend to upgrade the unsupported operating system
Failing to upgrade to the most up-to-date software not only makes machines vulnerable to attacks, but also hinders the amount of programs that can be used by teachers and students. Keeping up with the most current technology is vital, as it has become ubiquitous in daily life, making it a valuable skill for children to have for the future. Despite technology’s important place in education,
- 4 out of 10 school’s IT budgets are slashed for the upcoming school year
- More than a quarter of schools have a $0 IT budget for this year
Technology in schools is not limited to instruction. Sensitive information about faculty, staff, and students is stored on administrative computers. This information needs to be protected from cybercriminals, which is difficult for schools with little to no IT budget. Schools without adequate protection put local families, faculty, and expensive hardware at risk.
AVAST Free for Education helps schools by providing them with enterprise-grade antivirus protection for free, saving school districts an average of $14,285 a year. The AVAST Free for Education program saves school IT departments money they can spend on software and hardware upgrades or use for supplies and salaries.
Thank you for using avast! Antivirus and recommending us to your friends and family. For all the latest news, fun and contest information, please follow us on Facebook, Twitter and Google+. Business owners – check out our business products.
Online fraud – POS malware has now hit 1,000 U.S. firms
More than a thousand U.S. businesses have been affected by point-of-sale malware – malicious software written specifically for online fraud – to steal information such as credit card details from companies and their customers.
The United States Computer Emergency Readiness Team issued a statement saying that the “Backoff†malware was rife in U.S. businesses, taking over administrator accounts and removing customer data from several hundreds of companies.
POS malware was a footnote in computing history until the Target breach, but the hi-tech online fraud now appears to be a growth industry. Ars Technica points out how quickly the software has evolved during the past two years, and emphasizes the direct impact on American consumers.
ESET Malware Researcher Lysa Myers says, “Malware attacks on Point of Sale (PoS) systems are coming thick and fast right now.†Myers offers a detailed guide for businesses concerned that they may be being targeted with POS malware.
Online fraud: Shop terminals under attack
“Over the past year, the Secret Service has responded to network intrusions at numerous businesses throughout the United States that have been impacted by the ‘Backoff’ malware,” the advisory stated. “Seven PoS system providers/vendors have confirmed that they have had multiple clients affected. Reporting continues on additional compromised locations, involving private sector entities of all sizes.”
The figure of 1,000 businesses comes from a Secret Service estimate, based on figures from vendors of POS software.
“Seven PoS system providers/vendors have confirmed that they have had multiple clients affected. Reporting continues on additional compromised locations, involving private sector entities of all sizes, and the Secret Service currently estimates that over 1,000 U.S. businesses are affected,†the advisory says.
Criminals target makers of software for shops
Ars refers to a recent  attack, where the attackers were able to guess the password to the system,and  installed the Backoff program. The malware disguises itself as an innocent Java component but ‘listens’ for credit card transactions, storing them and transmitting them to criminals, according to  US-CERT’s original advisory.
The US-CERT advisory advises companies, “Organizations that believe they have been impacted should contact their local Secret Service field office and may contact the NCCIC for additional information.â€
Â
The post Online fraud – POS malware has now hit 1,000 U.S. firms appeared first on We Live Security.
![]()
Google Images hacked? Searches fill with morbid image
An image of a Russian car crash has piled up in Google Images, regardless of what users search for. Time magazine searched for ‘puppy” and instead saw multiple images of the crash – leading to speculation that the service has been hacked. What’s less clear is why, or who might have done it.
One user says that regardless of what he searches for, he sees dozens of images of the same car crash, “Every time I search something in Google images, these creepy images are appearing. It’s apparently a crashed truck or something, but I didn’t look it up. People could say that it had something to do with what I was searching, but if I click on it, a different image appears. I have some screenshots attached.â€
Google Images: ‘Creepy images appearing’
The issue is not affecting all users, but Google product forums are full of complaints about the image, which shows a fatal car crash from several years ago.
Time magazine reports that the images vary –  Google’s own support forums tracked back and found the image came from a report on a Ukrainian news site. We’ve not linked to the report as it contains many more grisly images of the crash.
Time also reported that a related Reddit chain say that images of basketball player and occasional actor Kevin Durant have also been reported by some user.
Hours of glitches
Jalopnik says, “In the meantime, Reddit user anvile noticed that the original photos stem from a story about a car crash in Moscow that killed three people. The driver, a 28-year-old woman, was reported to be intoxicated.”
“Weirder still, the crash occurred in November of 2012, according to this Pravda article, so it isn’t recent.â€
Google has as yet not offered comment on the images, or their origin.
The post Google Images hacked? Searches fill with morbid image appeared first on We Live Security.
![]()
Oracle Event Processing FileUploadServlet Directory Traversal (CVE-2014-2424)
A code execution vulnerability has been reported in Oracle Event Processing. The vulnerability is due to a directory traversal within the FileUploadServlet servlet. A remote unauthenticated attacker can exploit this vulnerability by sending a maliciously crafted HTTP request.
HP Intelligent Management Center BIMS UploadServlet Information Disclosure (CVE-2014-2618)
An information disclosure vulnerability exists in the BIMS add-in module of HP Intelligent Management Center. The vulnerability is due to lack of authentication and insufficient input validation in the UploadServlet servlet when processing HTTP request parameters. By sending crafted HTTP requests to the target system, a remote unauthenticated attacker can leverage this vulnerability to view the contents of arbitrary files on a target system.
MOXA Device Manager Tool SCADA Buffer Overflow (CVE-2010-4741)
A remote code execution vulnerability has been reported in MOXA Device Manager Tool. The vulnerability is due to a stack based buffer overflow when handling specially crafted packets.
Adobe Flash Player and AIR Security Bypass (APSB14-18; CVE-2014-0541)
A security bypass vulnerability has been reported in Adobe Flash Player. The vulnerability is due to insufficient security restrictions while handling specially crafted SWF files. A remote attacker can exploit this vulnerability by enticing a target user to open a specially crafted SWF file using an affected version of Adobe Flash Player.
Adobe Multiple Products Flash Content Parsing Code Execution (APSA10-03: CVE-2010-2884) (CVE-2010-2884)
A remote code execution vulnerability has been reported in multiple Adobe products. The vulnerability is due to an error in the way Flash files are parsed.
HP Data Protector Opcode 28 and 11 Command Execution (CVE-2014-2623)
A command execution vulnerability exists in Hewlett-Packard Data Protector. The vulnerability is due to a design weakness when handling requests to port 5555. A remote attacker can exploit this vulnerability by sending crafted packets to the target service. Successful exploitation could lead to arbitrary command execution with system privileges on the target server.