Severity Rating: Critical
Revision Note: V1.1 (July 29, 2014): Corrected the severity table and vulnerability information to add CVE-2014-4066 as a vulnerability addressed by this update. This is an informational change only. Customers who have already successfully installed the update do not have to take any action.
Summary: This security update resolves one publicly disclosed vulnerability and twenty-four privately reported vulnerabilities in Internet Explorer. The most severe of these vulnerabilities could allow remote code execution if a user views a specially crafted webpage using Internet Explorer. An attacker who successfully exploited these vulnerabilities could gain the same user rights as the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
Panda Security achieves the highest detection ratios in the industry’s leading tests
Panda Cloud Antivirus, the free cloud antivirus from Panda Security, offers the highest levels of protection according to the two leading industry product tests, those of AV-Comparatives and AV-TEST.
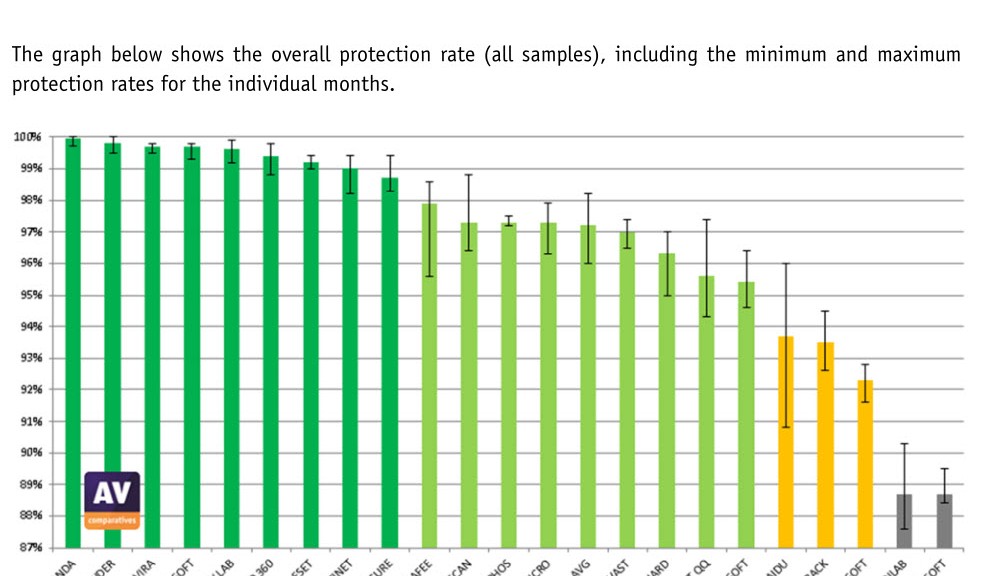
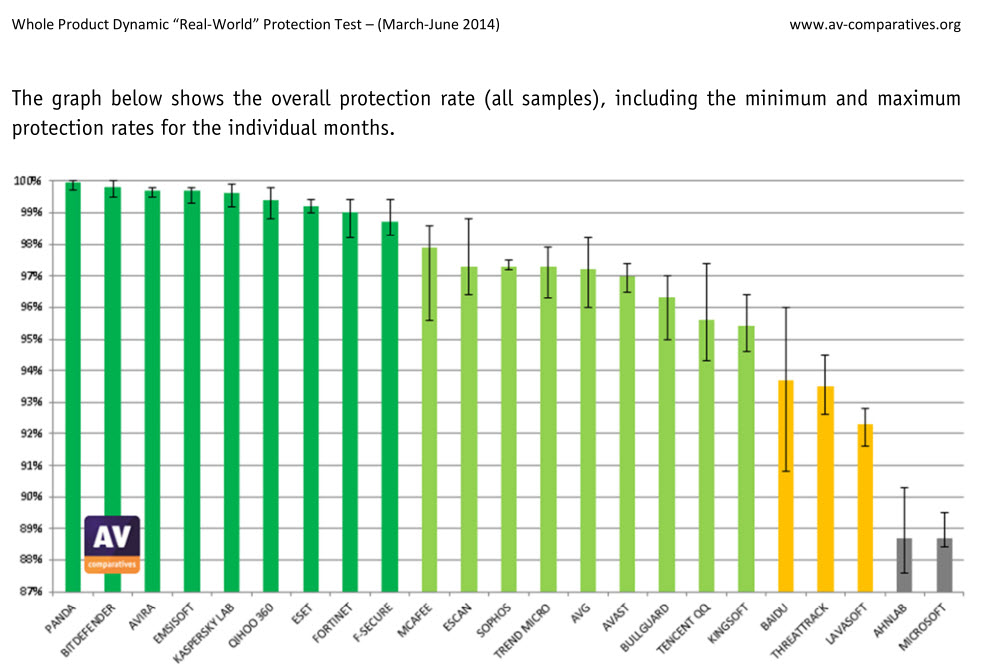
AV-Comparatives confirms a 99.9% detection ratio
During the more than 150,000 ‘real world’ proactive detection tests carried out from March to June this year by the AV-Comparatives independent laboratory, Panda Security’s free anti-malware solution managed to detect and block 99.9% of threats.
This comparative test of over 20 antivirus solutions highlights the great protection capacity of Panda Security’s solution, beating out other free products such as Avast, AVG or Microsoft’s antivirus; or pay solutions including Kaspersky, McAfee and Sophos.
For more details of the AV-Comparatives test, click here.
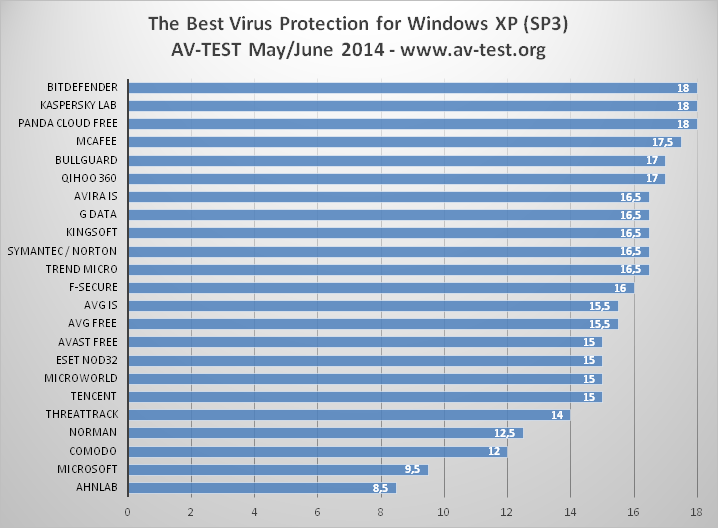
100% detection ratio, according to AV-TEST
Similarly, in the ‘Real-World Protection’ test carried out by AV-TEST in May and June, Panda Cloud Antivirus also racked up the maximum score, with a 100% detection ratio for the second consecutive month. Out of 23 products tested by the laboratory, only three achieved the maximum detection rate, and one of these was Panda Cloud Antivirus, the free solution from Panda Security.
In addition to these excellent detection results, it’s important to note that Panda Security has scored maximum points in the AV-TEST ‘Monthly Consumer Product Testing’ performance test in June.
For more details of the AV-TEST product tests, click here
New XMT Smart Engineering engine
The results from both these labs are based on tests carried out on products based on the new XMT (Extreme Malware Terminator) Smart Engineering engine from Panda Security. With XMT, different technologies interact with each other to achieve new levels of efficiency and greater detection and disinfection power to eradicate all threats. The new XMT engine will be included in the new 2015 consumer product line that Panda Security will be presenting in August.
“The best thing is that the platform and engine with which we’re achieving these results are the basis of all our endpoint protection products. Our aim is to continue integrating technologies in the platform to stay in pole position when it comes to detection and provide our users with maximum protection and minimum impact on their systemsâ€, says Luis Corrons, Technical Director of PandaLabs at Panda Security.
Panda Cloud Antivirus 3.0
Panda Security presented Panda Cloud Antivirus version 3.0 last May, after a trial phase during which the product was downloaded more than 30,000 times across 130 countries. The new solution includes, in both the ‘Free’ and ‘Pro’ editions a new more modern and intuitive ‘look and feel’. The solution also delivers improved protection technologies against new threats and attacks that exploit software vulnerabilities and automatically vaccinates USB drives, a feature which is now available to all users of the product, and not just the Pro version, as in the past.
It also includes the highly useful Rescue Kit for dealing with emergencies caused by malware, as well as a more complete process monitor.
![]()
UPDATED : VMSA-2014-0006.9 VMware product updates address OpenSSL security vulnerabilities
-----BEGIN PGP SIGNED MESSAGE-----
Hash: SHA1
- -----------------------------------------------------------------------
VMware Security Advisory
Advisory ID: VMSA-2014-0006.9
Synopsis: VMware product updates address OpenSSL
security vulnerabilities
Issue date: 2014-06-10
Updated on: 2014-07-22
CVE numbers: CVE-2014-0224, CVE-2014-0198, CVE-2010-5298, and
CVE-2014-3470
- -----------------------------------------------------------------------
1. Summary
VMware product updates address OpenSSL security vulnerabilities.
2. Relevant Releases
Big Data Extensions prior to 2.0.0
ESXi 5.5 without patch ESXi550-201406401-SG
ESXi 5.1 without patch ESXi510-201406401-SG
ESXi 5.0 without patch ESXi500-201407401-SG
Workstation 10.x prior to 10.0.3
Workstation 9.x prior to 9.0.4
Player 6.x prior to 6.0.3
Player 5.x prior to 5.0.4
Fusion 6.x prior to 6.0.4
Fusion 5.x prior to 5.0.5
Horizon Mirage Edge Gateway prior to 4.4.3
Horizon View prior to 5.3.2
Horizon View 5.3 Feature Pack X prior to Feature Pack 3
Horizon Workspace Server 1.5.x without patch horizon-nginx-rpm-
1.5.0.0-1876270.
x86_64.rpm
Horizon Workspace Server 1.8.x without patch horizon-nginx-rpm-
1.8.2.1820-1876338.
x86_64.rpm
Horizon View Clients prior to 3.0
vCD 5.5.x prior to 5.5.1.2
vCD 5.1.x prior to 5.1.3.1
vCenter prior to 5.5u1b
vCenter prior to 5.1 U2a
vCenter prior to 5.0U3a
vCenter Support Assistant prior to 5.5.1.1
vCloud Automation Center prior to 6.0.1.2
vCenter Configuration Manager prior to 5.7.2
vCenter Converter Standalone prior to 5.5.2
Converter Standalone prior to 5.1.1
vCenter Operations Manager prior to 5.8.2
vCenter Operations Manager prior to 5.7.3
vCenter Chargeback Manager 2.6 prior to 2.6.0.1
vCloud Networking and Security prior to 5.5.2.1
vCloud Networking and Security prior to 5.1.4.1
vSphere PowerCLI 5.x
vCSA prior to 5.5u1b
vCSA prior to 5.1u2a
vCSA prior to 5.0u3a
OVF Tool prior to 5.3.2
Update Manager prior to 5.5u1b
VDDK prior to 5.5.2
VDDK prior to 5.1.3
VDDK prior to 5.0.4
NSX for Multi-Hypervisor 4.1.x prior to 4.1.3
NSX for Multi-Hypervisor 4.0.x prior to 4.0.4
NVP 3.0.x prior to 3.2.3
NSX 6.0.x for vSphere prior to 6.0.5
vFabric Web Server 5.x
Pivotal Web Server prior to 5.4.1
vCenter Site Recovery Manager prior to 5.5.1.1
vCenter Site Recovery Manager prior to 5.1.2.1
vCenter Site Recovery Manager prior to 5.0.3.2
vSphere Replication prior to 5.5.1.1
3. Problem Description
a. OpenSSL update for multiple products.
OpenSSL libraries have been updated in multiple products to
versions 0.9.8za and 1.0.1h in order to resolve multiple security
issues.
The Common Vulnerabilities and Exposures project (cve.mitre.org)
has assigned the names CVE-2014-0224, CVE-2014-0198,
CVE-2010-5298, CVE-2014-3470, CVE-2014-0221 and CVE-2014-0195 to
these issues. The most important of these issues is
CVE-2014-0224.
CVE-2014-0198, CVE-2010-5298 and CVE-2014-3470 are considered to
be of moderate severity. Exploitation is highly unlikely or is
mitigated due to the application configuration.
CVE-2014-0221 and CVE-2014-0195, which are listed in the OpenSSL
Security Advisory (see Reference section below), do not affect
any VMware products.
CVE-2014-0224 may lead to a Man-in-the-Middle attack if a server
is running a vulnerable version of OpenSSL 1.0.1 and clients are
running a vulnerable version of OpenSSL 0.9.8 or 1.0.1. Updating
the server will mitigate this issue for both the server and all
affected clients.
CVE-2014-0224 may affect products differently depending on
whether the product is acting as a client or a server and of
which version of OpenSSL the product is using. For readability
the affected products have been split into 3 tables below,
based on the different client-server configurations and
deployment scenarios.
MITIGATIONS
Clients that communicate with a patched or non-vulnerable server
are not vulnerable to CVE-2014-0224. Applying these patches to
affected servers will mitigate the affected clients (See Table 1
below).
Clients that communicate over untrusted networks such as public
Wi-Fi and communicate to a server running a vulnerable version of
OpenSSL 1.0.1. can be mitigated by using a secure network such as
VPN (see Table 2 below).
Clients and servers that are deployed on an isolated network are
less exposed to CVE-2014-0224 (see Table 3 below). The affected
products are typically deployed to communicate over the
management network.
RECOMMENDATIONS
VMware recommends customers evaluate and deploy patches for
affected Servers in Table 1 below as these patches become
available. Patching these servers will remove the ability to
exploit the vulnerability described in CVE-2014-0224 on both
clients and servers.
VMware recommends customers consider
applying patches to products listed in Table 2 & 3 as required.
Column 4 of the following tables lists the action required to
remediate the vulnerability in each release, if a solution is
available.
Table 1
=======
Affected servers running a vulnerable version of OpenSSL 1.0.1.
VMware Product Running Replace with/
Product Version on Apply Patch
============== ======= ======= =============
ESXi 5.5 ESXi ESXi550-
201406401-SG
Big Data Extensions 1.1 2.0.0
vCenter Chargeback Manager 2.6 2.6.0.1
Horizon Workspace Server 1.5.x horizon-nginx-
rpm-1.5.0.0-
1876270.
x86_64.rpm
Horizon Workspace Server 1.8.x horizon-nginx-
rpm-1.8.2.1820-
1876338.
x86_64.rpm
Horizon Mirage Edge Gateway 4.4.x 4.4.3
Horizon View 5.x 5.3.2
Horizon View Feature Pack 5.x 5.3 FP3
NSX for Multi-Hypervisor 4.1.2 4.1.3
NSX for Multi-Hypervisor 4.0.3 4.0.4
NSX for vSphere 6.0.4 6.0.5
NVP 3.2.2 3.2.3
vCloud Networking and Security 5.5.2 5.5.2.1
vCloud Networking and Security 5.1.4 5.1.4.1
Pivotal Web Server 5.4 5.4.1
vFabric Web Server 5.x Pivotal Web
Server 5.4.1
Table 2
========
Affected clients running a vulnerable version of OpenSSL 0.9.8
or 1.0.1 and communicating over an untrusted network.
VMware Product Running Replace with/
Product Version on Apply Patch
============== ======= ======= =============
vCSA 5.5 5.5u1b
vCSA 5.1 5.1u2a
vCSA 5.0 5.0u3a
ESXi 5.1 ESXi ESXi510-
201406401-SG
ESXi 5.0 ESXi ESXi500-
201407401-SG
Workstation 10.x any 10.0.3
Workstation 9.x any 9.0.4
Fusion 6.x OSX 6.0.4
Fusion 5.x OSX 5.0.5
Player 6.x any 6.0.3
Player 5.x any 5.0.4
vCenter Chargeback Manager 2.5.x 2.6.0.1
Horizon Workspace Client 1.x OSX 1.8.2
Horizon Workspace Client 1.x Windows 1.8.2
Horizon View Client 2.x Android 3.0
Horizon View Client 2.x iOS 3.0
Horizon View Client 2.x OSX 3.0
Horizon View Client 2.x Windows 3.0
Horizon View Client 2.x WinStore 3.0
OVF Tool 3.5.1 3.5.2
OVF Tool 3.0.1 3.5.2
vCenter Operations Manager 5.8.x 5.8.2
vCenter Operations Manager 5.7.x 5.7.3
vCenter Support Assistant 5.5.1 5.5.1.1
vCD 5.5.1.x 5.5.1.2
vCD 5.1.x 5.1.3.1
vCenter Site Recovery Manager 5.5.x 5.5.1.1
vCenter Site Recovery Manager 5.1.x 5.1.2.1
vCenter Site Recovery Manager 5.0.3.x 5.0.3.2
vSphere Client 5.5 Windows 5.5u1b
vSphere Client 5.1 Windows 5.1u2a
vSphere Client 5.0 Windows 5.0u3a
Table 3
=======
The following table lists all affected clients running a
vulnerable version of OpenSSL 0.9.8 or 1.0.1 and communicating
over a trusted or isolated network.
VMware Product Running Replace with/
Product Version on Apply Patch
============== ======= ======= =============
vCenter Server 5.5 any 5.5u1b
vCenter Server 5.1 any 5.1u2a
vCenter Server 5.0 any 5.0u3a
Update Manager 5.5 Windows 5.5u1b
vCenter Configuration
Manager (VCM) 5.6 5.7.2
ITBM Standard 1.0.1 patch pending
ITBM Standard 1.0 patch pending
Studio 2.6.0.0 patch pending
Usage Meter 3.3 patch pending
vCenter Converter Standalone 5.5 5.5.2
vCenter Converter Standalone 5.1 5.1.1
vCloud Application Director 6.0.x patch pending
vFabric Application Director 5.2.0 patch pending
vFabric Application Director 5.0.0 patch pending
vCloud Automation Center 6.0.x 6.0.1.2
VIX API 1.12 patch pending
vMA (Management Assistant) 5.1.0.1 patch pending
vSphere PowerCLI 5.x See VMware
KB 2082132
vSphere Data Protection 5.5.6 patch pending
vSphere Data Protection 5.1.11 patch pending
vSphere Replication 5.5.1 5.5.1.1
vSphere Replication 5.6 patch pending
vSphere SDK for Perl 5.5 patch pending
VDDK 5.5.x 5.5.2
VDDK 5.1.x 5.1.3
VDDK 5.0.x 5.0.4
4. Solution
Big Data Extensions 2.0.0
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-bde
ESXi 5.5, 5.1 and 5.0
----------------------------
Download:
https://www.vmware.com/patchmgr/findPatch.portal
Horizon Mirage Edge Gateway 4.4.3
---------------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-horizon-mirage
vCD 5.5.1.2
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download/vcloud-director
vCenter Server 5.5u1b, 5.1u2a, 5.0u3a
------------------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere
vCSA 5.5u1b, 5.1u2a and 5.0u3a
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere
Update Manager 5.5u1b
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere
VDDK 5.x
----------------------------
Downloads and Documentation:
https://www.vmware.com/support/developer/vddk
vCenter Configuration Manager (VCM) 5
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download_vcm
vCenter Operations Manager 5.8 and 5.7.3
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere-ops-mgr
OVF Tool 3.5.2
--------------
Download:
https://www.vmware.com/support/developer/ovf/
vCenter Converter Standalone 5.5.2
-----------------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-converter
Horizon View 5
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/downloadview
Horizon View 5.3 Feature Pack 3
-----------------------------------
Downloads and Documentation:
https://www.vmware.com/go/downloadview
Horizon Workspace Server 1.5 and 1.8.x
----------------------------
Release Notes and download:
http://kb.vmware.com/kb/2082181
Workstation
----------------------
https://www.vmware.com/go/downloadworkstation
Fusion
------------------
https://www.vmware.com/go/downloadfusion
VMware Player
------------------
https://www.vmware.com/go/downloadplayer
vCenter Server 5.1 Update 2a
----------------------------------------------------
Download link:
https://my.vmware.com/web/vmware/info/slug/datacenter_cloud_infrastructure/
vmware_vsphere/5_1
vCenter Server 5.0 Update 3a
----------------------------------------------------
Download link:
https://my.vmware.com/web/vmware/info/slug/datacenter_cloud_infrastructure/
vmware_vsphere/5_0
vCloud Networking and Security 5.5.2.1
------------------------------------
Download
https://my.vmware.com/web/vmware/details?downloadGroup=VCNS552_GA&productId
=353&rPId=5255
vCloud Networking and Security 5.1.4.1
------------------------------------
Download:
https://my.vmware.com/web/vmware/details?downloadGroup=VCNS514_GA&productId
=285&rPId=5131
NSX for Multi-Hypervisor, NSX for vSphere and NVP
-------------------------------------------------
Remediation Instructions and Download, available under support:
http://www.vmware.com/products/nsx
vCD 5.5.1.2 and vCD 5.1.3.1
---------------------------
Download link:
https://www.vmware.com/go/download-vcd-ns
VMware vCenter Chargeback Manager
---------------------------------
Download link:
https://www.vmware.com/go/download-chargeback
Converter Standalone 5.1.1
---------------------------
Download link:
https://www.vmware.com/go/download-converter
vCenter Support Assistant
--------------------------
Downloads:
https://www.vmware.com/go/download-vsphere
Pivotal Web Server 5.4.1
------------------------
https://my.vmware.com/web/vmware/details?downloadGroup=VF_530_PVTL_WSVR_541
&productId=335&rPId=6214
vCloud Automation Center
--------------------------
Downloads:
https://www.vmware.com/go/download-vcac
vCenter Site Recovery Manager 5.5.1.1
-------------------------------------
Remediation Instructions and Download:
http://kb.vmware.com/kb/2081861
vCenter Site Recovery Manager 5.1.2.1
-------------------------------------
Remediation Instructions and Download:
http://kb.vmware.com/kb/2081860
vCenter Site Recovery Manager 5.0.3.2
-------------------------------------
Remediation Instructions and Download:
http://kb.vmware.com/kb/2081859
vSphere Replication 5.5.1.1
---------------------------
Remediation Instructions and Download:
http://kb.vmware.com/kb/2082666
5. References
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0224
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0198
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-5298
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-3470
https://www.openssl.org/news/secadv_20140605.txt
http://www.gopivotal.com/security/cve-2014-0224
VMware Knowledge Base Article 2082132
http://kb.vmware.com/kb/2082132
- -----------------------------------------------------------------------
6. Change Log
2014-06-10 VMSA-2014-0006
Initial security advisory in conjunction with the release of
ESXi 5.5 updates on 2014-06-10
2014-06-12 VMSA-2014-0006.1
Updated security advisory in conjunction with the release of
Big Data Extensions 2.0.0, Horizon Mirage Edge Gateway 4.4.3,
vCD 5.5.1.2, vCenter Server 5.5u1b, vCSA 5.5u1b, and Update
Manager 5.5u1b on 2014-06-12
2014-06-17 VMSA-2014-0006.2
Updated security advisory in conjunction with the release of
ESXi 5.1 updates, VDDK 5.5.2, 5.1.3, and 5.0.4 on 2014-06-17
2014-06-24 VMSA-2014-0006.3
Updated security advisory in conjunction with the release of
Horizon View 5.3.2, Horizon View 5.3 Feature Pack 3,
vCenter Configuration Manager 5.7.2, vCenter
Converter Standalone 5.5.2, vCenter Operations
Manager 5.8.2, OVF Tool 5.3.2 on 2014-06-24
2014-07-01 VMSA-2014-0006.4
Updated security advisory in conjunction with the release of
ESX 5.0 patches, Workstation 10.0.3, Player 6.0.3, Fusion 6.0.4,
Horizon Workspace Server 1.5.x and 1.8.x updates, vCD
5.1.3.1, vCenter Server 5.1 update 2a and 5.0 update 3a,
vCSA 5.1 update 2a and 5.0 update 3a, Converter Standalone 5.1.1,
vCenter Chargeback Manager 2.6.0.1,
vCloud Networking and Security 5.5.2.1 and 5.1.4.1,
NSX for Multi-Hypervisor 4.1.3,
NSX for Multi-Hypervisor 4.0.4, NVP 3.2.3 and
NSX 6.0.5 for vSphere on 2014-07-01
2014-07-03 VMSA-2014-0006.5
Updated security advisory in conjunction with the release of
Workstation 9.0.4, Player 5.0.4, Fusion 5.0.5, vCenter Support
Assistant 5.5.1.1, on 2014-07-03
2014-07-08 VMSA-2014-0006.6
Updated security advisory in conjunction with the release of
vSphere PowerCLI 5.x on 2014-07-04 and Pivotal Web Server 5.4.1
on 2014-07-08
2014-07-10 VMSA-2014-0006.7
Updated security advisory in conjunction with the release of
vCloud Automation Center 6.0.1.2 and vCenter Operations Manager
5.7.3 on 2014-07-10
2014-07-18 VMSA-2014-0006.8
Updated security advisory in conjunction with the release of
patches for vCenter Site Recovery Manager 5.5.1.1 and
vSphere Replication 5.5.1.1 on 2014-07-17
2014-07-22 VMSA-2014-0006.8
Updated security advisory in conjunction with the release of
patches for vCenter Site Recovery Manager 5.1.2.1 and 5.0.3.2
on 2014-07-22
- -----------------------------------------------------------------------
7. Contact
E-mail list for product security notifications and announcements:
http://lists.vmware.com/cgi-bin/mailman/listinfo/security-announce
This Security Advisory is posted to the following lists:
security-announce at lists.vmware.com
bugtraq at securityfocus.com
fulldisclosure at seclists.org
E-mail: security at vmware.com
PGP key at: http://kb.vmware.com/kb/1055
VMware Security Advisories
http://www.vmware.com/security/advisories
VMware Security Response Policy
https://www.vmware.com/support/policies/security_response.html
VMware Lifecycle Support Phases
https://www.vmware.com/support/policies/lifecycle.html
Twitter
https://twitter.com/VMwareSRC
Copyright 2014 VMware Inc. All rights reserved.
-----BEGIN PGP SIGNATURE-----
Version: Encryption Desktop 10.3.0 (Build 8741)
Charset: utf-8
wj8DBQFTzpZcDEcm8Vbi9kMRAga+AKCzEY/Ut+tN3qGTilKf5KslUPO6aQCfXuRp
/7HxhovpiO8xURBCf/uu8EI=
=YjIJ
-----END PGP SIGNATURE-----
UPDATED : VMSA-2014-0006.9 VMware product updates address OpenSSL security vulnerabilities
-----BEGIN PGP SIGNED MESSAGE-----
Hash: SHA1
- -----------------------------------------------------------------------
VMware Security Advisory
Advisory ID: VMSA-2014-0006.9
Synopsis: VMware product updates address OpenSSL
security vulnerabilities
Issue date: 2014-06-10
Updated on: 2014-07-22
CVE numbers: CVE-2014-0224, CVE-2014-0198, CVE-2010-5298, and
CVE-2014-3470
- -----------------------------------------------------------------------
1. Summary
VMware product updates address OpenSSL security vulnerabilities.
2. Relevant Releases
Big Data Extensions prior to 2.0.0
ESXi 5.5 without patch ESXi550-201406401-SG
ESXi 5.1 without patch ESXi510-201406401-SG
ESXi 5.0 without patch ESXi500-201407401-SG
Workstation 10.x prior to 10.0.3
Workstation 9.x prior to 9.0.4
Player 6.x prior to 6.0.3
Player 5.x prior to 5.0.4
Fusion 6.x prior to 6.0.4
Fusion 5.x prior to 5.0.5
Horizon Mirage Edge Gateway prior to 4.4.3
Horizon View prior to 5.3.2
Horizon View 5.3 Feature Pack X prior to Feature Pack 3
Horizon Workspace Server 1.5.x without patch horizon-nginx-rpm-
1.5.0.0-1876270.
x86_64.rpm
Horizon Workspace Server 1.8.x without patch horizon-nginx-rpm-
1.8.2.1820-1876338.
x86_64.rpm
Horizon View Clients prior to 3.0
vCD 5.5.x prior to 5.5.1.2
vCD 5.1.x prior to 5.1.3.1
vCenter prior to 5.5u1b
vCenter prior to 5.1 U2a
vCenter prior to 5.0U3a
vCenter Support Assistant prior to 5.5.1.1
vCloud Automation Center prior to 6.0.1.2
vCenter Configuration Manager prior to 5.7.2
vCenter Converter Standalone prior to 5.5.2
Converter Standalone prior to 5.1.1
vCenter Operations Manager prior to 5.8.2
vCenter Operations Manager prior to 5.7.3
vCenter Chargeback Manager 2.6 prior to 2.6.0.1
vCloud Networking and Security prior to 5.5.2.1
vCloud Networking and Security prior to 5.1.4.1
vSphere PowerCLI 5.x
vCSA prior to 5.5u1b
vCSA prior to 5.1u2a
vCSA prior to 5.0u3a
OVF Tool prior to 5.3.2
Update Manager prior to 5.5u1b
VDDK prior to 5.5.2
VDDK prior to 5.1.3
VDDK prior to 5.0.4
NSX for Multi-Hypervisor 4.1.x prior to 4.1.3
NSX for Multi-Hypervisor 4.0.x prior to 4.0.4
NVP 3.0.x prior to 3.2.3
NSX 6.0.x for vSphere prior to 6.0.5
vFabric Web Server 5.x
Pivotal Web Server prior to 5.4.1
vCenter Site Recovery Manager prior to 5.5.1.1
vCenter Site Recovery Manager prior to 5.1.2.1
vCenter Site Recovery Manager prior to 5.0.3.2
vSphere Replication prior to 5.5.1.1
3. Problem Description
a. OpenSSL update for multiple products.
OpenSSL libraries have been updated in multiple products to
versions 0.9.8za and 1.0.1h in order to resolve multiple security
issues.
The Common Vulnerabilities and Exposures project (cve.mitre.org)
has assigned the names CVE-2014-0224, CVE-2014-0198,
CVE-2010-5298, CVE-2014-3470, CVE-2014-0221 and CVE-2014-0195 to
these issues. The most important of these issues is
CVE-2014-0224.
CVE-2014-0198, CVE-2010-5298 and CVE-2014-3470 are considered to
be of moderate severity. Exploitation is highly unlikely or is
mitigated due to the application configuration.
CVE-2014-0221 and CVE-2014-0195, which are listed in the OpenSSL
Security Advisory (see Reference section below), do not affect
any VMware products.
CVE-2014-0224 may lead to a Man-in-the-Middle attack if a server
is running a vulnerable version of OpenSSL 1.0.1 and clients are
running a vulnerable version of OpenSSL 0.9.8 or 1.0.1. Updating
the server will mitigate this issue for both the server and all
affected clients.
CVE-2014-0224 may affect products differently depending on
whether the product is acting as a client or a server and of
which version of OpenSSL the product is using. For readability
the affected products have been split into 3 tables below,
based on the different client-server configurations and
deployment scenarios.
MITIGATIONS
Clients that communicate with a patched or non-vulnerable server
are not vulnerable to CVE-2014-0224. Applying these patches to
affected servers will mitigate the affected clients (See Table 1
below).
Clients that communicate over untrusted networks such as public
Wi-Fi and communicate to a server running a vulnerable version of
OpenSSL 1.0.1. can be mitigated by using a secure network such as
VPN (see Table 2 below).
Clients and servers that are deployed on an isolated network are
less exposed to CVE-2014-0224 (see Table 3 below). The affected
products are typically deployed to communicate over the
management network.
RECOMMENDATIONS
VMware recommends customers evaluate and deploy patches for
affected Servers in Table 1 below as these patches become
available. Patching these servers will remove the ability to
exploit the vulnerability described in CVE-2014-0224 on both
clients and servers.
VMware recommends customers consider
applying patches to products listed in Table 2 & 3 as required.
Column 4 of the following tables lists the action required to
remediate the vulnerability in each release, if a solution is
available.
Table 1
=======
Affected servers running a vulnerable version of OpenSSL 1.0.1.
VMware Product Running Replace with/
Product Version on Apply Patch
============== ======= ======= =============
ESXi 5.5 ESXi ESXi550-
201406401-SG
Big Data Extensions 1.1 2.0.0
vCenter Chargeback Manager 2.6 2.6.0.1
Horizon Workspace Server 1.5.x horizon-nginx-
rpm-1.5.0.0-
1876270.
x86_64.rpm
Horizon Workspace Server 1.8.x horizon-nginx-
rpm-1.8.2.1820-
1876338.
x86_64.rpm
Horizon Mirage Edge Gateway 4.4.x 4.4.3
Horizon View 5.x 5.3.2
Horizon View Feature Pack 5.x 5.3 FP3
NSX for Multi-Hypervisor 4.1.2 4.1.3
NSX for Multi-Hypervisor 4.0.3 4.0.4
NSX for vSphere 6.0.4 6.0.5
NVP 3.2.2 3.2.3
vCloud Networking and Security 5.5.2 5.5.2.1
vCloud Networking and Security 5.1.4 5.1.4.1
Pivotal Web Server 5.4 5.4.1
vFabric Web Server 5.x Pivotal Web
Server 5.4.1
Table 2
========
Affected clients running a vulnerable version of OpenSSL 0.9.8
or 1.0.1 and communicating over an untrusted network.
VMware Product Running Replace with/
Product Version on Apply Patch
============== ======= ======= =============
vCSA 5.5 5.5u1b
vCSA 5.1 5.1u2a
vCSA 5.0 5.0u3a
ESXi 5.1 ESXi ESXi510-
201406401-SG
ESXi 5.0 ESXi ESXi500-
201407401-SG
Workstation 10.x any 10.0.3
Workstation 9.x any 9.0.4
Fusion 6.x OSX 6.0.4
Fusion 5.x OSX 5.0.5
Player 6.x any 6.0.3
Player 5.x any 5.0.4
vCenter Chargeback Manager 2.5.x 2.6.0.1
Horizon Workspace Client 1.x OSX 1.8.2
Horizon Workspace Client 1.x Windows 1.8.2
Horizon View Client 2.x Android 3.0
Horizon View Client 2.x iOS 3.0
Horizon View Client 2.x OSX 3.0
Horizon View Client 2.x Windows 3.0
Horizon View Client 2.x WinStore 3.0
OVF Tool 3.5.1 3.5.2
OVF Tool 3.0.1 3.5.2
vCenter Operations Manager 5.8.x 5.8.2
vCenter Operations Manager 5.7.x 5.7.3
vCenter Support Assistant 5.5.1 5.5.1.1
vCD 5.5.1.x 5.5.1.2
vCD 5.1.x 5.1.3.1
vCenter Site Recovery Manager 5.5.x 5.5.1.1
vCenter Site Recovery Manager 5.1.x 5.1.2.1
vCenter Site Recovery Manager 5.0.3.x 5.0.3.2
vSphere Client 5.5 Windows 5.5u1b
vSphere Client 5.1 Windows 5.1u2a
vSphere Client 5.0 Windows 5.0u3a
Table 3
=======
The following table lists all affected clients running a
vulnerable version of OpenSSL 0.9.8 or 1.0.1 and communicating
over a trusted or isolated network.
VMware Product Running Replace with/
Product Version on Apply Patch
============== ======= ======= =============
vCenter Server 5.5 any 5.5u1b
vCenter Server 5.1 any 5.1u2a
vCenter Server 5.0 any 5.0u3a
Update Manager 5.5 Windows 5.5u1b
vCenter Configuration
Manager (VCM) 5.6 5.7.2
ITBM Standard 1.0.1 patch pending
ITBM Standard 1.0 patch pending
Studio 2.6.0.0 patch pending
Usage Meter 3.3 patch pending
vCenter Converter Standalone 5.5 5.5.2
vCenter Converter Standalone 5.1 5.1.1
vCloud Application Director 6.0.x patch pending
vFabric Application Director 5.2.0 patch pending
vFabric Application Director 5.0.0 patch pending
vCloud Automation Center 6.0.x 6.0.1.2
VIX API 1.12 patch pending
vMA (Management Assistant) 5.1.0.1 patch pending
vSphere PowerCLI 5.x See VMware
KB 2082132
vSphere Data Protection 5.5.6 patch pending
vSphere Data Protection 5.1.11 patch pending
vSphere Replication 5.5.1 5.5.1.1
vSphere Replication 5.6 patch pending
vSphere SDK for Perl 5.5 patch pending
VDDK 5.5.x 5.5.2
VDDK 5.1.x 5.1.3
VDDK 5.0.x 5.0.4
4. Solution
Big Data Extensions 2.0.0
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-bde
ESXi 5.5, 5.1 and 5.0
----------------------------
Download:
https://www.vmware.com/patchmgr/findPatch.portal
Horizon Mirage Edge Gateway 4.4.3
---------------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-horizon-mirage
vCD 5.5.1.2
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download/vcloud-director
vCenter Server 5.5u1b, 5.1u2a, 5.0u3a
------------------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere
vCSA 5.5u1b, 5.1u2a and 5.0u3a
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere
Update Manager 5.5u1b
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere
VDDK 5.x
----------------------------
Downloads and Documentation:
https://www.vmware.com/support/developer/vddk
vCenter Configuration Manager (VCM) 5
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download_vcm
vCenter Operations Manager 5.8 and 5.7.3
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-vsphere-ops-mgr
OVF Tool 3.5.2
--------------
Download:
https://www.vmware.com/support/developer/ovf/
vCenter Converter Standalone 5.5.2
-----------------------------------
Downloads and Documentation:
https://www.vmware.com/go/download-converter
Horizon View 5
----------------------------
Downloads and Documentation:
https://www.vmware.com/go/downloadview
Horizon View 5.3 Feature Pack 3
-----------------------------------
Downloads and Documentation:
https://www.vmware.com/go/downloadview
Horizon Workspace Server 1.5 and 1.8.x
----------------------------
Release Notes and download:
http://kb.vmware.com/kb/2082181
Workstation
----------------------
https://www.vmware.com/go/downloadworkstation
Fusion
------------------
https://www.vmware.com/go/downloadfusion
VMware Player
------------------
https://www.vmware.com/go/downloadplayer
vCenter Server 5.1 Update 2a
----------------------------------------------------
Download link:
https://my.vmware.com/web/vmware/info/slug/datacenter_cloud_infrastructure/
vmware_vsphere/5_1
vCenter Server 5.0 Update 3a
----------------------------------------------------
Download link:
https://my.vmware.com/web/vmware/info/slug/datacenter_cloud_infrastructure/
vmware_vsphere/5_0
vCloud Networking and Security 5.5.2.1
------------------------------------
Download
https://my.vmware.com/web/vmware/details?downloadGroup=VCNS552_GA&productId
=353&rPId=5255
vCloud Networking and Security 5.1.4.1
------------------------------------
Download:
https://my.vmware.com/web/vmware/details?downloadGroup=VCNS514_GA&productId
=285&rPId=5131
NSX for Multi-Hypervisor, NSX for vSphere and NVP
-------------------------------------------------
Remediation Instructions and Download, available under support:
http://www.vmware.com/products/nsx
vCD 5.5.1.2 and vCD 5.1.3.1
---------------------------
Download link:
https://www.vmware.com/go/download-vcd-ns
VMware vCenter Chargeback Manager
---------------------------------
Download link:
https://www.vmware.com/go/download-chargeback
Converter Standalone 5.1.1
---------------------------
Download link:
https://www.vmware.com/go/download-converter
vCenter Support Assistant
--------------------------
Downloads:
https://www.vmware.com/go/download-vsphere
Pivotal Web Server 5.4.1
------------------------
https://my.vmware.com/web/vmware/details?downloadGroup=VF_530_PVTL_WSVR_541
&productId=335&rPId=6214
vCloud Automation Center
--------------------------
Downloads:
https://www.vmware.com/go/download-vcac
vCenter Site Recovery Manager 5.5.1.1
-------------------------------------
Remediation Instructions and Download:
http://kb.vmware.com/kb/2081861
vCenter Site Recovery Manager 5.1.2.1
-------------------------------------
Remediation Instructions and Download:
http://kb.vmware.com/kb/2081860
vCenter Site Recovery Manager 5.0.3.2
-------------------------------------
Remediation Instructions and Download:
http://kb.vmware.com/kb/2081859
vSphere Replication 5.5.1.1
---------------------------
Remediation Instructions and Download:
http://kb.vmware.com/kb/2082666
5. References
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0224
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0198
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2010-5298
http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-3470
https://www.openssl.org/news/secadv_20140605.txt
http://www.gopivotal.com/security/cve-2014-0224
VMware Knowledge Base Article 2082132
http://kb.vmware.com/kb/2082132
- -----------------------------------------------------------------------
6. Change Log
2014-06-10 VMSA-2014-0006
Initial security advisory in conjunction with the release of
ESXi 5.5 updates on 2014-06-10
2014-06-12 VMSA-2014-0006.1
Updated security advisory in conjunction with the release of
Big Data Extensions 2.0.0, Horizon Mirage Edge Gateway 4.4.3,
vCD 5.5.1.2, vCenter Server 5.5u1b, vCSA 5.5u1b, and Update
Manager 5.5u1b on 2014-06-12
2014-06-17 VMSA-2014-0006.2
Updated security advisory in conjunction with the release of
ESXi 5.1 updates, VDDK 5.5.2, 5.1.3, and 5.0.4 on 2014-06-17
2014-06-24 VMSA-2014-0006.3
Updated security advisory in conjunction with the release of
Horizon View 5.3.2, Horizon View 5.3 Feature Pack 3,
vCenter Configuration Manager 5.7.2, vCenter
Converter Standalone 5.5.2, vCenter Operations
Manager 5.8.2, OVF Tool 5.3.2 on 2014-06-24
2014-07-01 VMSA-2014-0006.4
Updated security advisory in conjunction with the release of
ESX 5.0 patches, Workstation 10.0.3, Player 6.0.3, Fusion 6.0.4,
Horizon Workspace Server 1.5.x and 1.8.x updates, vCD
5.1.3.1, vCenter Server 5.1 update 2a and 5.0 update 3a,
vCSA 5.1 update 2a and 5.0 update 3a, Converter Standalone 5.1.1,
vCenter Chargeback Manager 2.6.0.1,
vCloud Networking and Security 5.5.2.1 and 5.1.4.1,
NSX for Multi-Hypervisor 4.1.3,
NSX for Multi-Hypervisor 4.0.4, NVP 3.2.3 and
NSX 6.0.5 for vSphere on 2014-07-01
2014-07-03 VMSA-2014-0006.5
Updated security advisory in conjunction with the release of
Workstation 9.0.4, Player 5.0.4, Fusion 5.0.5, vCenter Support
Assistant 5.5.1.1, on 2014-07-03
2014-07-08 VMSA-2014-0006.6
Updated security advisory in conjunction with the release of
vSphere PowerCLI 5.x on 2014-07-04 and Pivotal Web Server 5.4.1
on 2014-07-08
2014-07-10 VMSA-2014-0006.7
Updated security advisory in conjunction with the release of
vCloud Automation Center 6.0.1.2 and vCenter Operations Manager
5.7.3 on 2014-07-10
2014-07-18 VMSA-2014-0006.8
Updated security advisory in conjunction with the release of
patches for vCenter Site Recovery Manager 5.5.1.1 and
vSphere Replication 5.5.1.1 on 2014-07-17
2014-07-22 VMSA-2014-0006.8
Updated security advisory in conjunction with the release of
patches for vCenter Site Recovery Manager 5.1.2.1 and 5.0.3.2
on 2014-07-22
- -----------------------------------------------------------------------
7. Contact
E-mail list for product security notifications and announcements:
http://lists.vmware.com/cgi-bin/mailman/listinfo/security-announce
This Security Advisory is posted to the following lists:
security-announce at lists.vmware.com
bugtraq at securityfocus.com
fulldisclosure at seclists.org
E-mail: security at vmware.com
PGP key at: http://kb.vmware.com/kb/1055
VMware Security Advisories
http://www.vmware.com/security/advisories
VMware Security Response Policy
https://www.vmware.com/support/policies/security_response.html
VMware Lifecycle Support Phases
https://www.vmware.com/support/policies/lifecycle.html
Twitter
https://twitter.com/VMwareSRC
Copyright 2014 VMware Inc. All rights reserved.
-----BEGIN PGP SIGNATURE-----
Version: Encryption Desktop 10.3.0 (Build 8741)
Charset: utf-8
wj8DBQFTzpZcDEcm8Vbi9kMRAga+AKCzEY/Ut+tN3qGTilKf5KslUPO6aQCfXuRp
/7HxhovpiO8xURBCf/uu8EI=
=YjIJ
-----END PGP SIGNATURE-----
[ANNOUNCEMENT] Apache HTTP Server 2.4.10 Released
Apache HTTP Server 2.4.10 Released
The Apache Software Foundation and the Apache HTTP Server Project
are pleased to announce the release of version 2.4.10 of the Apache
HTTP Server ("Apache"). This version of Apache is our latest GA
release of the new generation 2.4.x branch of Apache HTTPD and
represents fifteen years of innovation by the project, and is
recommended over all previous releases. This release of Apache is
principally a security, feature and bug fix release.
CVE-2014-0117 (cve.mitre.org)
mod_proxy: Fix crash in Connection header handling which
allowed a denial of service attack against a reverse proxy
with a threaded MPM.
CVE-2014-3523 (cve.mitre.org)
Fix a memory consumption denial of service in the WinNT MPM (used in all Windows
installations). Workaround: AcceptFilter <protocol> {none|connect}
CVE-2014-0226 (cve.mitre.org)
Fix a race condition in scoreboard handling, which could lead to
a heap buffer overflow.
CVE-2014-0118 (cve.mitre.org)
mod_deflate: The DEFLATE input filter (inflates request bodies) now
limits the length and compression ratio of inflated request bodies to avoid
denial of sevice via highly compressed bodies. See directives
DeflateInflateLimitRequestBody, DeflateInflateRatioLimit,
and DeflateInflateRatioBurst.
CVE-2014-0231 (cve.mitre.org)
mod_cgid: Fix a denial of service against CGI scripts that do
not consume stdin that could lead to lingering HTTPD child processes
filling up the scoreboard and eventually hanging the server. By
default, the client I/O timeout (Timeout directive) now applies to
communication with scripts. The CGIDScriptTimeout directive can be
used to set a different timeout for communication with scripts.
Also in this release are some exciting new features including:
*) Proxy FGI and websockets improvements
*) Proxy capability via handler
*) Finer control over scoping of RewriteRules
*) Unix Domain Socket (UDS) support for mod_proxy backends.
*) Support for larger shared memory sizes for mod_socache_shmcb
*) mod_lua and mod_ssl enhancements
*) Support named groups and backreferences within the LocationMatch,
DirectoryMatch, FilesMatch and ProxyMatch directives.
We consider this release to be the best version of Apache available, and
encourage users of all prior versions to upgrade.
Apache HTTP Server 2.4.10 is available for download from:
http://httpd.apache.org/download.cgi
Apache 2.4 offers numerous enhancements, improvements, and performance
boosts over the 2.2 codebase. For an overview of new features
introduced since 2.4 please see:
http://httpd.apache.org/docs/trunk/new_features_2_4.html
Please see the CHANGES_2.4 file, linked from the download page, for a
full list of changes. A condensed list, CHANGES_2.4.10 includes only
those changes introduced since the prior 2.4 release. A summary of all
of the security vulnerabilities addressed in this and earlier releases
is available:
http://httpd.apache.org/security/vulnerabilities_24.html
This release requires the Apache Portable Runtime (APR) version 1.5.x
and APR-Util version 1.5.x. The APR libraries must be upgraded for all
features of httpd to operate correctly.
This release builds on and extends the Apache 2.2 API. Modules written
for Apache 2.2 will need to be recompiled in order to run with Apache
2.4, and require minimal or no source code changes.
http://svn.apache.org/repos/asf/httpd/httpd/trunk/VERSIONING
When upgrading or installing this version of Apache, please bear in mind
that if you intend to use Apache with one of the threaded MPMs (other
than the Prefork MPM), you must ensure that any modules you will be
using (and the libraries they depend on) are thread-safe.
CVE-2014-3523
Memory leak in the winnt_accept function in server/mpm/winnt/child.c in the WinNT MPM in the Apache HTTP Server 2.4.x before 2.4.10 on Windows, when the default AcceptFilter is enabled, allows remote attackers to cause a denial of service (memory consumption) via crafted requests. (CVSS:5.0) (Last Update:2014-07-23)
CVE-2014-0226
Race condition in the mod_status module in the Apache HTTP Server before 2.4.10 allows remote attackers to cause a denial of service (heap-based buffer overflow), or possibly obtain sensitive credential information or execute arbitrary code, via a crafted request that triggers improper scoreboard handling within the status_handler function in modules/generators/mod_status.c and the lua_ap_scoreboard_worker function in modules/lua/lua_request.c. (CVSS:6.8) (Last Update:2014-09-04)
CVE-2014-0118
The deflate_in_filter function in mod_deflate.c in the mod_deflate module in the Apache HTTP Server before 2.4.10, when request body decompression is enabled, allows remote attackers to cause a denial of service (resource consumption) via crafted request data that decompresses to a much larger size. (CVSS:4.3) (Last Update:2014-09-04)
CVE-2014-0231
The mod_cgid module in the Apache HTTP Server before 2.4.10 does not have a timeout mechanism, which allows remote attackers to cause a denial of service (process hang) via a request to a CGI script that does not read from its stdin file descriptor. (CVSS:5.0) (Last Update:2014-09-04)
CVE-2014-0117
The mod_proxy module in the Apache HTTP Server 2.4.x before 2.4.10, when a reverse proxy is enabled, allows remote attackers to cause a denial of service (child-process crash) via a crafted HTTP Connection header. (CVSS:4.3) (Last Update:2014-09-04)