Today, technology is all around us, and it comes with both the good and the bad. Make sure you take precautions before going on vacation this summer!
Tag Archives: Antivirus
Protect your business from malvertising: stop your employees from clicking malicious ads
Malicious advertisements, called malvertising, are capable of getting into anyone’s computers. Have you been trained on how to prevent these threats in your business environment?
New range of Panda Antivirus: Security for all your devices
Multiplatform security, management ease and light resource usage are some of the main benefits of the latest product range from Panda Security.
First-Ever Ransomware For Smart Thermostat is Here — It's Hot!
Internet of Things (IoT) is the latest buzz in the world of technology, but they are much easier to hack than you think.
Until now we have heard many scary stories of hacking IoT devices, but how realistic is the threat?
Just think of a scenario where you enter in your house, and it’s sweltering, but when you head on to check the temperature of your thermostat, you find out that it has been
![]()
Raffle: What’s your favorite Avira product?
Tell us, what’s your favorite Avira product and seize the chance to win a 1-year license key for your favorite product.
The post Raffle: What’s your favorite Avira product? appeared first on Avira Blog.
Connect to open Wi-Fi networks without getting hacked!
Connecting to public Wi-Fi networks can get us out of a jam… and also get us into one! Use these 10 security tips and surf the web carefully.
Avira Antivirus for Mac scores in AV Comparatives test
Avira Antivirus for Mac – and its development team – got great marks in the latest Mac Security Test & Review from AV Comparatives for its malware stopping ability, easy usability, and fast response to user suggestions.
The post Avira Antivirus for Mac scores in AV Comparatives test appeared first on Avira Blog.
“Click†without Risk with Panda Safe Web
The latest version of Panda Safe Web offers us new features that are essential for navigating the internet safely. Maximize your web browser now without risking your security!
Social Media, Ranked as One of the Top Threats Aimed at Companies
Long ago, the term “goods” referred to necessities like wheat, milk, sugar, and petroleum, but our necessities have changed. Now “goods” can refer to broad band or smartphones or computers or–cybercrime?
As seen in the RSA’s report about the Current State of Cybercrime, experts confirm what we already know: malware and the tools cybercriminals use are evolving. Although malware comes from different places, they have identical capabilities and continue to procreate. The amount of stolen information continues to grow, and cybercriminals are capitalizing on it. The stolen information acquired by cybercriminals has joined the other goods available in our competitive market.
The internet and its on-growing innovations keep us adapting. Next time you buy gourmet-pasta-on-a-Tuesday-and-eat-it-on-a-Wednesday, remember that cybercriminals could be capitalizing on the private information you divulge for such”conveniences”. While you are checking your email, they may be stealing and selling your log-in information for your email accounts, social media sites, and favorite online shops. Even very detailed information like medical histories from hospital patients are highly demanded and can be bought online, in bulk.
Every kind of personal information is online and has diverse buyers and sellers
But cybercriminals aren’t stooping to the deep-dark-web anymore, now they use public and open communication channels, like social media sites, for these illegal sales transactions. In fact, results from the six-month long study show that the RSA discovered more than 500 groups dedicated to fraud on social media, with an estimated 220,000 total members, and more than 60% (133,000 members), found each other on Facebook.
Financial information circulates within these online communities, including credit card information with access codes and authorization numbers, tutorials for how to perform a cyberattack, malware tools, and even zoomed-in conversations that teach users how to move money without being detected.
It is important for businesses to set aside sufficient resources to detect threats, attacks and frauds that now exist on multiple channels (Windows, Android, iOS, Mac, etc.). Since the variants can multiply and tailor themselves to the malware, prevention and protection efforts should also increase.
The post Social Media, Ranked as One of the Top Threats Aimed at Companies appeared first on Panda Security Mediacenter.
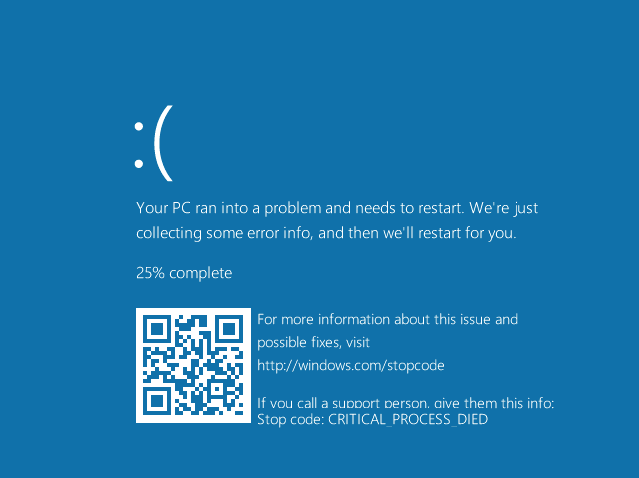
The Blue Screen of Death Gets a New Look
What a terrible feeling we have when the blue screen of death pops up. Dotted with white letters, this uh oh screen can show up unexpectedly on any old Windows-using computer. Seeing this screen will make anyone think, did my computer just DIE?
To fix the problem, the infamous screen of death reads that we should close all programs that could have provoked the issue or restart the computer altogether (using Ctrl+Alt+Supr). If we are lucky, the issue will go away after following these steps, but most of the time it won’t be that easy.
Now, this oh-so-hated blue screen of Windows has had a face-lift, making it just as terrible but a little nicer to look at. The newest version on Windows 10 (out this summer) will display a sad emoticon and a QR code that will send you to a help area once it is scanned.
The bad news is that these two-dimensional codes, or more precisely the links they contain, can be very powerful tools for cybercriminals.
First, a cybercriminal could simulate that your computer has an error, and send your computer a fake “blue screen of death”. Then the criminal could add a QR code with a link that will take you to an unexpected and malicious website that will install drive-by malware on your computer.
If the cybercriminal wants to be very sly, they could design an entire website that looks like an official Microsoft one and use it to phish for log-in information and personal data. Uneducated computer users are the easiest victims for this type of trap.
The QR code that appears on the Screen of Death can be used for phishing or downloading malware onto your computer
But using QR codes to camouflage links is nothing new. The best way to protect yourself from this type of attack is to keep your guard up. Don’t scan a two-dimensional code without knowing where it will take you and if that website is a safe place.
To defend yourself against these kind of attacks, it is essential to have a good antivirus that will detect any kind of phishing or malware that is attempting to download on your computer.
The post The Blue Screen of Death Gets a New Look appeared first on Panda Security Mediacenter.