PHPMemcachedAdmin versions 1.2.2 and below suffer from a stored cross site scripting vulnerability.
Monthly Archives: November 2014
CESA-2014:1827 Moderate CentOS 7 kdenetworkSecurity Update
CentOS Errata and Security Advisory 2014:1827 Moderate Upstream details at : https://rhn.redhat.com/errata/RHSA-2014-1827.html The following updated files have been uploaded and are currently syncing to the mirrors: ( sha256sum Filename ) x86_64: c470c0139168de6ef581767dde439c8dbc2b196c897d14e8b5c6336b4f6f564c kdenetwork-4.10.5-8.el7_0.x86_64.rpm 0a0c7c382d7de6557aa5960baf310bcec5314ee7659fc7369b30c78483a2fd82 kdenetwork-common-4.10.5-8.el7_0.noarch.rpm 8bf69f697fc0421e1cdb52a91566af8dd5d71fb08891ed25514d1d0dd4a5321a kdenetwork-devel-4.10.5-8.el7_0.noarch.rpm bbe73573065623e52bbb62e5711d8c389d80d7a820e29746443842885aac5961 kdenetwork-fileshare-samba-4.10.5-8.el7_0.x86_64.rpm bace8d145c634384ca65144a119354911b870e7fa5b60805450b031c0cb5ee7a kdenetwork-kdnssd-4.10.5-8.el7_0.x86_64.rpm 57837ec87c7e0ef8ace6ee0aeb20685bef538401aa7322c40174e47751aba5b9 kdenetwork-kget-4.10.5-8.el7_0.x86_64.rpm 4191d274cfcbdd9db2f3bac89a4d955c1a9f9aeccfea10e479ec0fa0f25e72c9 kdenetwork-kget-libs-4.10.5-8.el7_0.i686.rpm 4dea9e1d4e59598ce5e2bc3103827bdde09ec9b7404f93373dbfb0022500791a kdenetwork-kget-libs-4.10.5-8.el7_0.x86_64.rpm cf00f9cf82ab56adc8d02daabaf63824219321358fc8c634e26c0e1e95570f99 kdenetwork-kopete-4.10.5-8.el7_0.x86_64.rpm 7a5228c76facee58a92d61423d395e3be5d606010624dcaf3eab4344a801dee6 kdenetwork-kopete-devel-4.10.5-8.el7_0.i686.rpm ff6d5dbb0b34f7c620f846b14a09466413679cd0012caa3633dd8609eda98919 kdenetwork-kopete-devel-4.10.5-8.el7_0.x86_64.rpm 8ef46cfd0a1f9edeeb9bc67a0710a5218d63f799d7dfd0027a54253e07064d62 kdenetwork-kopete-libs-4.10.5-8.el7_0.i686.rpm a82b6cce061a5b60c29f74f7bd66c0f8ceb6981dcac0e1a291bfd6ee8b0c3f6c kdenetwork-kopete-libs-4.10.5-8.el7_0.x86_64.rpm fd2b180b4d9df1489c0c6c83f6a8b1cd62a2a6343e804797964f46e714235822 kdenetwork-krdc-4.10.5-8.el7_0.x86_64.rpm b07ed16efbba8fd1ea6cd38f20868715b5810420b507ecf1ff007b0ea8f0d7be kdenetwork-krdc-devel-4.10.5-8.el7_0.i686.rpm a7fd8bc22eb7d2c40d7ee3372226ef7c13f66f5d918acea05348b7be53abef5b kdenetwork-krdc-devel-4.10.5-8.el7_0.x86_64.rpm cf0b34d55824dd59550411e9df4a4234d8406b30c2ffc51ca837a00b40c4dd4d kdenetwork-krdc-libs-4.10.5-8.el7_0.i686.rpm 478343b28717b4c02ba956a7ede396bb4ce520255d4aa2945e9eadb7abd50f2b kdenetwork-krdc-libs-4.10.5-8.el7_0.x86_64.rpm d6efd3e180e971f470e65dde3aea971bf5c2ef963bee5ec67c7d6e3a95fc067f kdenetwork-krfb-4.10.5-8.el7_0.x86_64.rpm bb606ca79e447754fa196f87dd6b69807386e93ceb15d1d39de0418a43e6f0a2 kdenetwork-krfb-libs-4.10.5-8.el7_0.i686.rpm fe1661aa2b0e4bf5f7c2de515a86c5e7b84beb07992c2a022fa1b69ca95e8c5c kdenetwork-krfb-libs-4.10.5-8.el7_0.x86_64.rpm Source: 9c66e9ff50cb08995fbc85a2b946110a246f051408c19abebd73c77fbef20665 kdenetwork-4.10.5-8.el7_0.src.rpm
CEBA-2014:1840 CentOS 7 corosync BugFix Update
CentOS Errata and Bugfix Advisory 2014:1840 Upstream details at : https://rhn.redhat.com/errata/RHBA-2014-1840.html The following updated files have been uploaded and are currently syncing to the mirrors: ( sha256sum Filename ) x86_64: b4ccade48a9ccd1df06cafdaa8b360c847edb6c80c3514bc3ac6c83ba69eec12 corosync-2.3.3-2.el7_0.1.x86_64.rpm b41bc00ff59464e35cad5f8ab289b27712233ac7f2faacea1ea207c89c48911d corosynclib-2.3.3-2.el7_0.1.i686.rpm 85cb91a43ade26a6f16e6efae0f2cee2e25c4812c06d802a4100e93e3d264bf5 corosynclib-2.3.3-2.el7_0.1.x86_64.rpm 8a8f9064849b7e741f1c3dacd4969bdcf88e6023db5833bf404f9cb7dff19f8b corosynclib-devel-2.3.3-2.el7_0.1.i686.rpm 8430651985760911fae03f9d1223094bf1b8c3484fd3b313c850ca6af5522790 corosynclib-devel-2.3.3-2.el7_0.1.x86_64.rpm Source: b156c5cceb67c5b5873cd67d57308364efc4bf54affdc13114e9381a53c71209 corosync-2.3.3-2.el7_0.1.src.rpm
CEBA-2014:1838 CentOS 7 resource-agents BugFixUpdate
CentOS Errata and Bugfix Advisory 2014:1838 Upstream details at : https://rhn.redhat.com/errata/RHBA-2014-1838.html The following updated files have been uploaded and are currently syncing to the mirrors: ( sha256sum Filename ) x86_64: 027109e86558596659e84ed6ab82126b8ba424631761f2326bef4c5ddebc81e6 resource-agents-3.9.5-26.el7_0.5.x86_64.rpm Source: db2ed4e83f7f14f6b1fcb2981b984db72a01592ca4551587d732ac9a9be07f8c resource-agents-3.9.5-26.el7_0.5.src.rpm
CEEA-2014:1839 CentOS 7 hpsa Enhancement Update
CentOS Errata and Enhancement Advisory 2014:1839 Upstream details at : https://rhn.redhat.com/errata/RHEA-2014-1839.html The following updated files have been uploaded and are currently syncing to the mirrors: ( sha256sum Filename ) Source: 37143fc2ba305e70713d6eb3a162070b14e67250c470591480c3b436f860e089 hpsa-3.4.4_1_RH1-1.el7_0.src.rpm
SA-CONTRIB-2014-107 – Scheduler – Cross Site Scripting
- Advisory ID: DRUPAL-SA-CONTRIB-2014-107
- Project: Scheduler (third-party module)
- Version: 6.x, 7.x
- Date: 2014-November-12
- Security risk: 14/25 ( Moderately Critical) AC:None/A:Admin/CI:Some/II:Some/E:Theoretical/TD:Default
- Vulnerability: Cross Site Scripting
Description
The Scheduler module allows nodes to be published and unpublished on specified dates. The module allows administrators to provide additional help text on the content editing form when scheduling is enabled.
The module doesn’t sufficiently filter the help text which could lead to a Cross Site Scripting (XSS) attack.
This vulnerability is mitigated by the fact that an attacker must have a role with the permission “administer scheduler”.
CVE identifier(s) issued
- A CVE identifier will be requested, and added upon issuance, in accordance
with Drupal Security Team processes.
Versions affected
- Scheduler 6.x-1.x versions prior to 6.x-1.10.
- Scheduler 7.x-1.x versions prior to 7.x-1.3.
Drupal core is not affected. If you do not use the contributed Scheduler module,
there is nothing you need to do.
Solution
Install the latest version:
- If you use the Scheduler module for Drupal 6.x, upgrade to Scheduler 6.x-1.10
- If you use the Scheduler module for Drupal 7.x, upgrade to Scheduler 7.x-1.3
Also see the Scheduler project page.
Reported by
- Matt Vance of the Drupal Security Team
Fixed by
- Matt Vance of the Drupal Security Team
- Lee Rowlands of the Drupal Security Team
Coordinated by
- Lee Rowlands of the Drupal Security Team
Contact and More Information
The Drupal security team can be reached at security at drupal.org or via the contact form at https://www.drupal.org/contact.
Learn more about the Drupal Security team and their policies, writing secure code for Drupal, and securing your site.
Enterprise Linux 6.5 to 6.6 risk report
Red Hat Enterprise Linux 6.6 was released the 14th of October, 2014, eleven months since the release of 6.5 in November 2013. So lets use this opportunity to take a quick look back over the vulnerabilities and security updates made in that time, specifically for Red Hat Enterprise Linux 6 Server.
Red Hat Enterprise Linux 6 is in its fourth year since release, and will receive security updates until November 30th 2020.
Errata count
The chart below illustrates the total number of security updates issued for Red Hat Enterprise Linux 6 Server if you had installed 6.5, up to and including the 6.6 release, broken down by severity. It’s split into two columns, one for the packages you’d get if you did a default install, and the other if you installed every single package.
During installation there actually isn’t an option to install every package, you’d have to manually select them all, and it’s not a likely scenario. For a given installation, the number of package updates and vulnerabilities that affected you will depend on exactly what you selected during installation and which packages you have subsequently installed or removed.
 For a default install, from release of 6.5 up to and including 6.6, we shipped 47 advisories to address 219 vulnerabilities. 2 advisories were rated critical, 25 were important, and the remaining 20 were moderate and low.
For a default install, from release of 6.5 up to and including 6.6, we shipped 47 advisories to address 219 vulnerabilities. 2 advisories were rated critical, 25 were important, and the remaining 20 were moderate and low.
Or, for all packages, from release of 6.5 up to and including 6.6, we shipped 116 advisories to address 399 vulnerabilities. 13 advisories were rated critical, 53 were important, and the remaining 50 were moderate and low.
You can cut down the number of security issues you need to deal with by carefully choosing the right Red Hat Enterprise Linux variant and package set when deploying a new system, and ensuring you install the latest available Update release.
Critical vulnerabilities
Vulnerabilities rated critical severity are the ones that can pose the most risk to an organisation. By definition, a critical vulnerability is one that could be exploited remotely and automatically by a worm. However we also stretch that definition to include those flaws that affect web browsers or plug-ins where a user only needs to visit a malicious (or compromised) website in order to be exploited. Most of the critical vulnerabilities we fix fall into that latter category.
The 13 critical advisories addressed 42 critical vulnerabilities across six different projects:
- An update to php RHSA-2013:1813 (December 2013). A memory corruption flaw was found in the way the openssl_x509_parse() function of the PHP openssl extension parsed X.509 certificates. A remote attacker could use this flaw to provide a malicious self-signed certificate or a certificate signed by a trusted authority to a PHP application using the aforementioned function, causing the application to crash or, possibly, allow the attacker to execute arbitrary code with the privileges of the
user running the PHP interpreter. - An update to JavaOpenJDK
- RHSA-2014:0026 (January 2014). Multiple improper permission check issues were discovered in the Serviceability, Security, CORBA, JAAS, JAXP, and Networking components in OpenJDK. An untrusted Java application or applet could use these flaws to bypass certain Java sandbox restrictions.
- RHSA-2014:0406 (April 2014). An input validation flaw was discovered in the medialib library in the 2D component. A specially crafted image could trigger Java Virtual Machine memory corruption when processed. A remote attacker, or an untrusted Java application or applet, could possibly use this flaw to execute arbitrary code with the privileges of the user running the Java Virtual Machine.
- RHSA-2014:0889 (July 2014). It was discovered that the Hotspot component in OpenJDK did not properly verify bytecode from the class files. An untrusted Java application or applet could possibly use these flaws to bypass Java sandbox restrictions.
- An update to ruby RHSA-2013:1764 (November 2014). A buffer overflow flaw was found in the way Ruby parsed floating point numbers from their text representation. If an application using Ruby accepted untrusted input strings and converted them to floating point numbers, an attacker able to provide such input could cause the application to crash or, possibly, execute arbitrary code with the privileges of the
application. - An update to nss and nspr RHSA-2014:0917 (July 2014). A race condition was found in the way NSS verified certain certificates. A remote attacker could use this flaw to crash an application using NSS or, possibly, execute arbitrary code with the privileges of the user running that application.
- An update to bash (Shellshock) RHSA-2014:1293 (September 2014). A flaw was found in the way Bash evaluated certain specially crafted environment variables. An attacker could use this flaw to override or bypass environment restrictions to execute shell commands. Certain services and applications allow remote unauthenticated attackers to provide environment variables, allowing them to exploit this issue.
- An update to Firefox:
- RHSA-2013:1812 (December 2013). Â Several flaws were found in the processing of malformed web content. A web page containing malicious content could cause Firefox to terminate unexpectedly or, potentially, execute arbitrary code with the privileges of the user running Firefox.
- RHSA-2014:0132 (February 2014). Several flaws were found in the processing of malformed web content. A web page containing malicious content could cause Firefox to crash or, potentially, execute arbitrary code with the privileges of the user running Firefox.
- RHSA-2014:0310 (March 2014). Several flaws were found in the processing of malformed web content. A web page containing malicious content could cause Firefox to crash or, potentially, execute arbitrary code with the privileges of the user running Firefox.
- RHSA-2014:0448 (April 2014). Several flaws were found in the processing of malformed web content. A web page containing malicious content could cause Firefox to crash or, potentially, execute arbitrary code with the privileges of the user running Firefox.
- RHSA-2014:0741 (June 2014). Several flaws were found in the processing of malformed web content. A web page containing malicious content could cause Firefox to crash or, potentially, execute arbitrary code with the privileges of the user running Firefox.
- RHSA-2014:0919 (July 2014). Several flaws were found in the processing of malformed web content. A web page containing malicious content could cause Firefox to crash or, potentially, execute arbitrary code with the privileges of the user running Firefox.
- RHSA-2014:1144 (September 2014). Several flaws were found in the processing of malformed web content. A web page containing malicious content could cause Firefox to crash or, potentially, execute arbitrary code with the privileges of the user running Firefox.
- RHSA-2014:1635 (October 2014). Several flaws were found in the processing of malformed web content. A web page containing malicious content could cause Firefox to crash or, potentially, execute arbitrary code with the privileges of the user running Firefox.
A flaw was found in the Alarm API, which allows applications to schedule
actions to be run in the future. A malicious web application could use this
flaw to bypass cross-origin restrictions.
97% of updates to correct 42 critical vulnerabilities were available via Red Hat Network either the same day or the next calendar day after the issues were public.
Previous update releases
We generally measure risk in terms of the number of vulnerabilities, but the actual effort in maintaining a Red Hat Enterprise Linux system is more related to the number of advisories we released: a single Firefox advisory may fix ten different issues of critical severity, but takes far less total effort to manage than ten separate advisories each fixing one critical PHP vulnerability.
To compare these statistics with previous update releases we need to take into account that the time between each update release is different. So looking at a default installation and calculating the number of advisories per month gives the following chart:
 This data is interesting to get a feel for the risk of running Enterprise Linux 6 Server, but isn’t really useful for comparisons with other major versions, distributions, or operating systems — for example, a default install of Red Hat Enterprise Linux 6 Server does not include Firefox, but Red Hat Enterprise Linux 5 Server does. You can use our public security measurement data and tools, and run your own custom metrics for any given Red Hat product, package set, timescales, and severity range of interest.
This data is interesting to get a feel for the risk of running Enterprise Linux 6 Server, but isn’t really useful for comparisons with other major versions, distributions, or operating systems — for example, a default install of Red Hat Enterprise Linux 6 Server does not include Firefox, but Red Hat Enterprise Linux 5 Server does. You can use our public security measurement data and tools, and run your own custom metrics for any given Red Hat product, package set, timescales, and severity range of interest.
Eleanor CMS Open Redirect
Eleanor CMS suffers from an open redirection vulnerability.
Microsoft Schannel Bug Latest in Long Line of Serious Crypto Flaws
The critical vulnerability in the Schannel technology in Windows that Microsoft patched Tuesday is ripe for exploitation, experts say, and continues the long line of severe vulnerabilities in major SSL/TLS implementations in recent months. Secure Channel, also known as Schannel, is a technology that’s used in Windows to implement SSL and TLS, the main secure […]
Introducing a cleaner for iPhone, iPad & iPod Touch!Â
Yes, this is not a typo for the first time, AVG PC TuneUp will also include an all-new AVG iOS Cleaner feature to help users get rid of the hidden leftover files, which can amount to thousands, from both iOS itself as well as apps used on a daily basis.
In this and the next blog post I’d like to talk about what’s new for our PC utility AVG PC TuneUp. Let’s jump right in?
AVG Cleaner for iOS – Wait, an iOS Cleaner for PCs?
That’s right. We know that a lot of users out there are struggling with disk space on their iOS devices (iPad, iPhone, iPod touch). They’re getting messages like this when snagging a photo or downloading apps:

Also, iTunes seems to explicably show that there’s a lot of stuff in the “Other†or “Documents & Data†category. Well, if you’re running out of disk space, hidden clutter may be the culprit. That’s why we came up with AVG Cleaner for iOS. Since it’s technically not possible to have an app delete hidden temporary files and other unneeded files (more on that below), we’re doing that right from our PC and it’s the reason it’s part of AVG PC TuneUp.
How exactly does it work? (Step by Step)
Open up AVG PC TuneUp and select “Dashboardâ€. Then, go to the “Clean up†category.
Connect your Apple device to your PC and click on ‘Clean Up iPhone, iPad or iPod touch’.
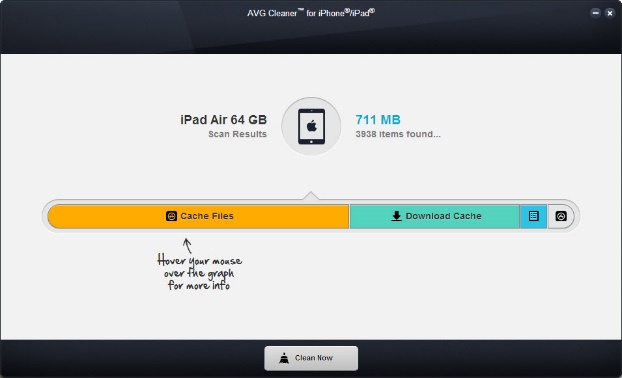
Hit the ‘Clean Now’ button. Have a look at the results.
How much did we clean up?
I was as surprised as you will be when I first laid my hands on an early version of our AVG Cleaner FOR iOS months ago: It found a LOT of unexpected files on my iDevices. I guess the biggest surprise was my iPad:
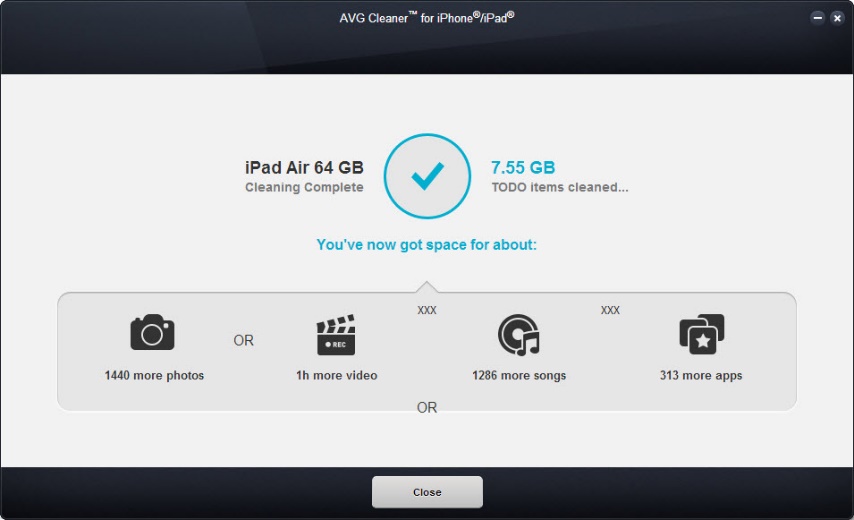
7.5 GB on my iPad. Another 500 MB on my iPhone 5S and more than 700 MB on my iPod touch. So how’s that even possible?
I found that rather incredible, and even more so after my iPad showed another 1 GB just a few weeks later:
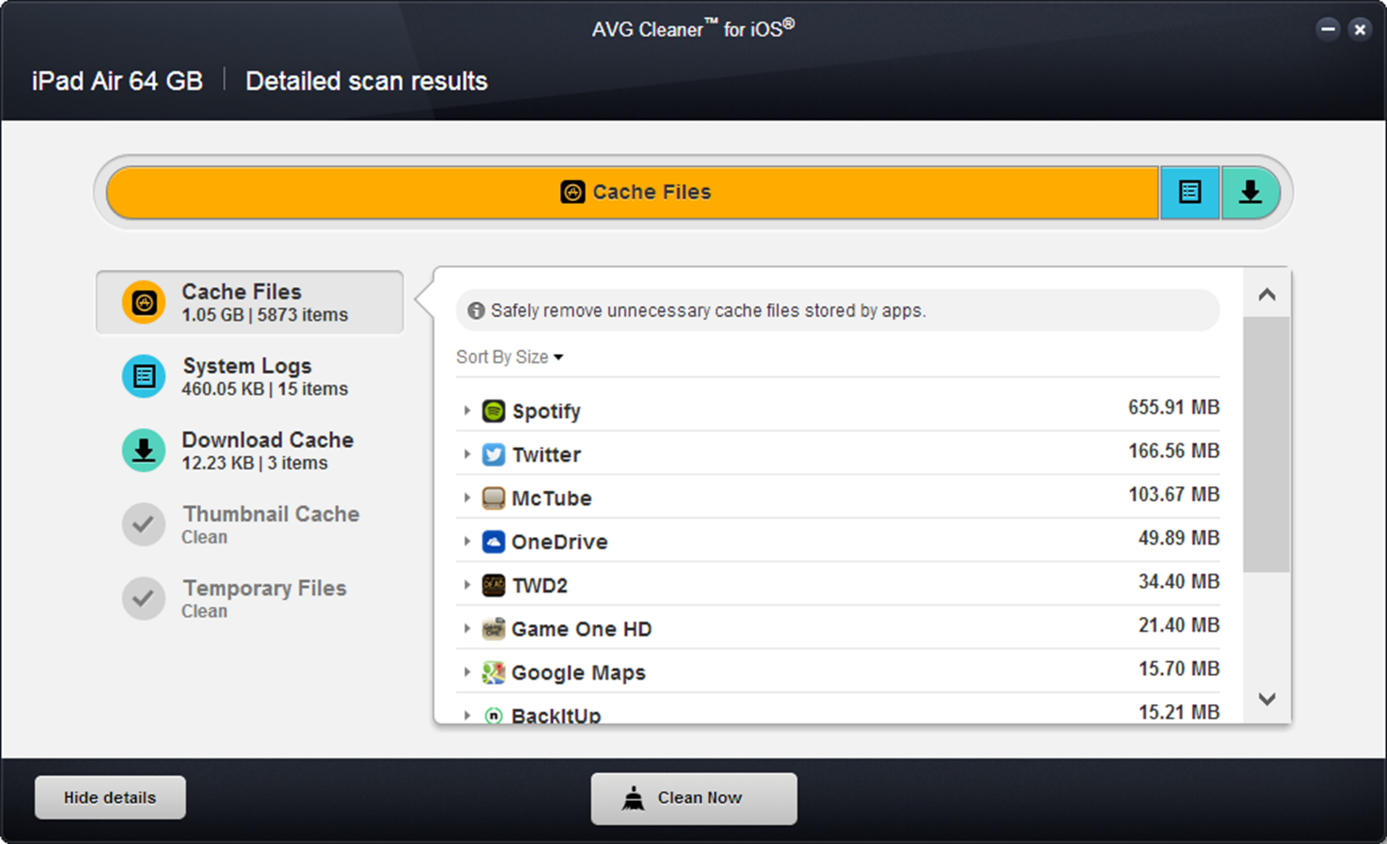
Digging deeper, I found that many of the daily apps I use create a lot of temporary files without deleting them. For example, after 2-3 days of Spotify streaming, its offline cache grew up to 655 MB on my iPad. But what is all this stuff? Let’s find out:
What AVG Cleaner for iOS cleans up
Download Cache & Temporary Files
Most apps create a “Cache†and “Temporary Files†folder to store data that’s needed while they are running. Unfortunately, many apps tend to forget to clean out these hidden downloads, which may result in your iOS device running out of space soon.
AVG Cleaner™ for iOS cleans out these hidden cache folders. Even according to Apple’s official guidelines, the cache folder is safe to delete as it includes data that can easily be renewed or downloaded again by the app – so we’re not doing anything harmful to your device. In fact, it may help even solve some problems when one of these cache files gets corrupted or damaged by a bug in the app.
Thumbnail Cache
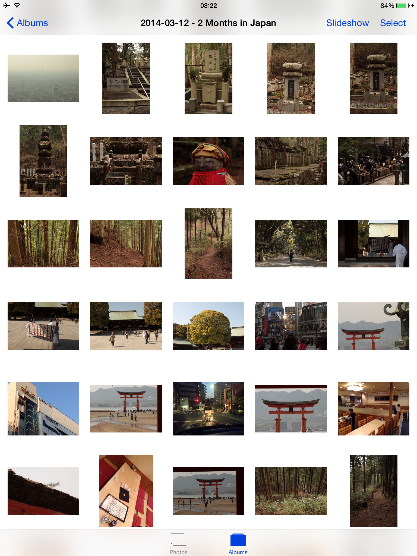
Every time you browse a photo related app, it creates thumbnail files to display the little previews (see image above), but may forget to delete them even if they’re no longer necessary.
AVG Cleaner™ for iOS cleans out all thumbnail files from 3rd party apps. It gets rid of all thumbnail files that are no longer being used and will only recreate the ones you need. Don’t worry, your stored photos will not be touched.
System Logs & Crash Reports
Every time an app crashes or an error occurs on your iPhone, iPad or iPod touch, a crash report and logs will be created. If you want to, these can be sent to Apple or the maker of the app. However, these reports take up valuable storage and may even contain personal information.
AVG Cleanerâ„¢ for iOS helps users delete system logs and crash reports, free up more disc space and the protect your privacy by removing personal information within these cookies.
Ok that’s it for now: Have you tried it out? Let us know how much you were able to clean up!
![]()
![]()