Monthly Archives: June 2015
Cisco IOS XR Denial-of-Service Vulnerability
Original release date: June 11, 2015
Cisco has identified a vulnerability that could allow an unauthenticated remote attacker to cause a denial-of-service condition. The vulnerability is due to improper processing of malformed IPv6 packets carrying extension headers. A Cisco Carrier Routing System 3 (CRS-3) running a version of Cisco IOS XR software prior to 4.2.1 is affected by this vulnerability.
Users and administrators are encouraged to review the Cisco Security Advisory and apply the necessary updates.
This product is provided subject to this Notification and this Privacy & Use policy.
Ubuntu Releases Security Update
Original release date: June 11, 2015
Ubuntu has released 10 security updates to address multiple vulnerabilities affecting Ubuntu 15.04, 14.10, 14.04 LTS, and 12.04 LTS. Exploitation of one of these vulnerabilities may allow a remote attacker to take control of the affected system.
US-CERT encourages users and administrators to review Ubuntu Security Notices USN-2629-1, USN-2630-1, USN-2631-1, USN-2632-1, USN-2633-1, USN-2634-1, USN-2635-1, USN-2636-1, USN-2637-1, and USN-2638-1 and apply the necessary updates.
This product is provided subject to this Notification and this Privacy & Use policy.
Securing a Heterogeneous Internet of Things
Analyst firm IDC predicts that the number of Internet of Things (IoT) devices—from home appliances to commercial applications such as door locks and sensors—will grow into a $7.1 trillion market by 2020, compared to $1.9 trillion in 2013.
This rapidly growing market is giving rise to a land grab of sorts: companies are vying to build the one IoT platform that will link all devices, and by linking them make them “smarter” as they communicate with one another.
So it may come as no surprise that at its developer conference last week, Google announced Brillo, a new Android-based operating system (OS) for the Internet of Things. The connected OS promises to use as little as 32 or 64 MB of RAM to run, making it power-efficient and light enough for “things” such as light bulbs, keys or door locks.
By offering a familiar, widely used (Android) OS as the basis for its IoT platform, Google is offering a solution that is already familiar to developers worldwide. However, by offering yet another OS for Things, it also compounds the fragmentation of the space. There are a wide array of vendors and consortiums now offering operating systems, connectivity platforms and discovery protocols.
With each vendor and approach come security threats and attack vectors. These threat surfaces are multiplied by the connectivity and discovery protocols and by the routing of data. There is a trend to route data from each device to the cloud, even when, intuitively, this should not be necessary. This enables device manufacturers to utilize hardware, services and data business models. It is not a trend that is likely to slow down by itself.
Securing this spider web of technology and data is a challenge and a necessity. When a smart lock knows when people are home, or when your security camera sees where you put your valuables, they contain very valuable information for criminals. Less obviously, but just as worrisome, is the aggregate data about you that travels the airwaves in your home and beyond.
Brillo, being built on the mature Android platform, has the advantage of being hardened for security over time, and the disadvantage that nefarious players already know its ins and outs. Other, less widely deployed platforms will go through their own maturity evolution as developers and hackers dig through them.
Because of the vast number of suppliers of Things, and the wide variance of the platforms and protocols, a full security solution is unlikely to come from one of these players. The answer to the IoT security dilemma will more likely come via third-party security companies who’ll play a major role in providing secure, safe digital environments for users across connected devices.
To keep the Internet of Things from devolving into the Internet of Threats or the “Illusion of Trust,” the industry needs to shore up standards on privacy and security. Today, the IoT is still evolving rapidly, and its standards and regulations are just being developed. We’re at a moment in time that’s similar to the birth of the World Wide Web 25 years ago. This time, however, we can build a hyper-connected world based on safety and trust and the principles of protection and privacy—literally, we can build security into the foundation of the IoT infrastructure.
One of the fathers of the modern Web, Vince Cert, once said he regrets not building more security into the architecture of the Internet. It was difficult at the time to anticipate the level of cybercrime, cyberwarfare and cyberespionage that would emerge. The promise of the IoT is exciting, with many business and consumer applications, including the connected car and the connected home. But for our vision to come to fruition, let’s learn the lesson of our predecessors and design the IoT and its devices by prioritizing privacy and security as central features.
An area we are passionate about is what we call the “law of least data.” This encapsulates the desire for data to be routed as directly between agents as possible. Two devices in your home should not have to send data to the cloud – even if they are from two different vendors – when they are talking to each other. Your next generation smartwatch should not have to talk to the cloud in order to read data out of your pacemaker. Of course some setup, or discovery metadata, may be required upon installation, but thereafter data should be kept personal whenever possible.
By agreeing on some defining principles, such as the law of least data, we can build a better Internet of Things.
![]()
![]()
Snapchat Offers Users Optional Two-Factor Authentication
Snapchat has given its users the choice of enabling two-factor authentication in the latest version of the photo- and video-sharing app.
[KIS-2015-03] Concrete5 <= 5.7.4 (Access.php) SQL Injection Vulnerability
Posted by Egidio Romano on Jun 11
———————————————————–
Concrete5 <= 5.7.4 (Access.php) SQL Injection Vulnerability
———————————————————–
[-] Software Link:
[-] Affected Versions:
Version 5.7.3.1, 5.7.4, and probably other versions.
[-] Vulnerability Description:
The vulnerable code is located in /concrete/src/Permission/Access/Access.php:
168. protected function…
[KIS-2015-01] Concrete5 <= 5.7.3.1 (sendmail) Remote Code Execution Vulnerability
Posted by Egidio Romano on Jun 11
——————————————————————-
Concrete5 <= 5.7.3.1 (sendmail) Remote Code Execution Vulnerability
——————————————————————-
[-] Software Link:
[-] Affected Versions:
Version 5.7.3.1 and probably other versions.
[-] Vulnerability Description:
The vulnerable code is located in…
[KIS-2015-02] Concrete5 <= 5.7.3.1 Multiple Reflected Cross-Site Scripting Vulnerabilities
Posted by Egidio Romano on Jun 11
—————————————————————————-
Concrete5 <= 5.7.3.1 Multiple Reflected Cross-Site Scripting Vulnerabilities
—————————————————————————-
[-] Software Link:
[-] Affected Versions:
Version 5.7.3.1 and probably other versions.
[-] Vulnerabilities Description:
1) The vulnerable code is located in…
OpenSSL Patches Five Flaws, Adds Protection Against Logjam Attack
The OpenSSL project has patched several moderate- and low-severity security vulnerabilities and also has added protection against the Logjam attack in new releases of the software. Most of the vulnerabilities fixed in the new releases are denial-of-service bugs, but one of them can potentially cause memory corruption. That vulnerability only affected older versions of OpenSSL. […]
How to stay safe when using public Wi-Fi hotspots
Many of the Wi-Fi hotspots you use in your hometown and when you travel have major security flaws making it easy for hackers to see your browsing activity, searches, passwords, videos, emails, and other personal information. It’s a public Wi-Fi connection, meaning that you are sharing the network with lots of strangers. Those strangers can easily watch what you’re doing or steal a username and password to one of your accounts while you sip your latte.
An easy and affordable way to maintain your security whenever you use free Wi-Fi is to use a virtual private network (VPN). It sounds techie, but Avast has made it simple.
A VPN service, like our SecureLine VPN, routes all the data you’re sending and receiving through a private, secure network, even though you’re on a public one. That way, SecureLine makes you 100% anonymous while protecting your activity.
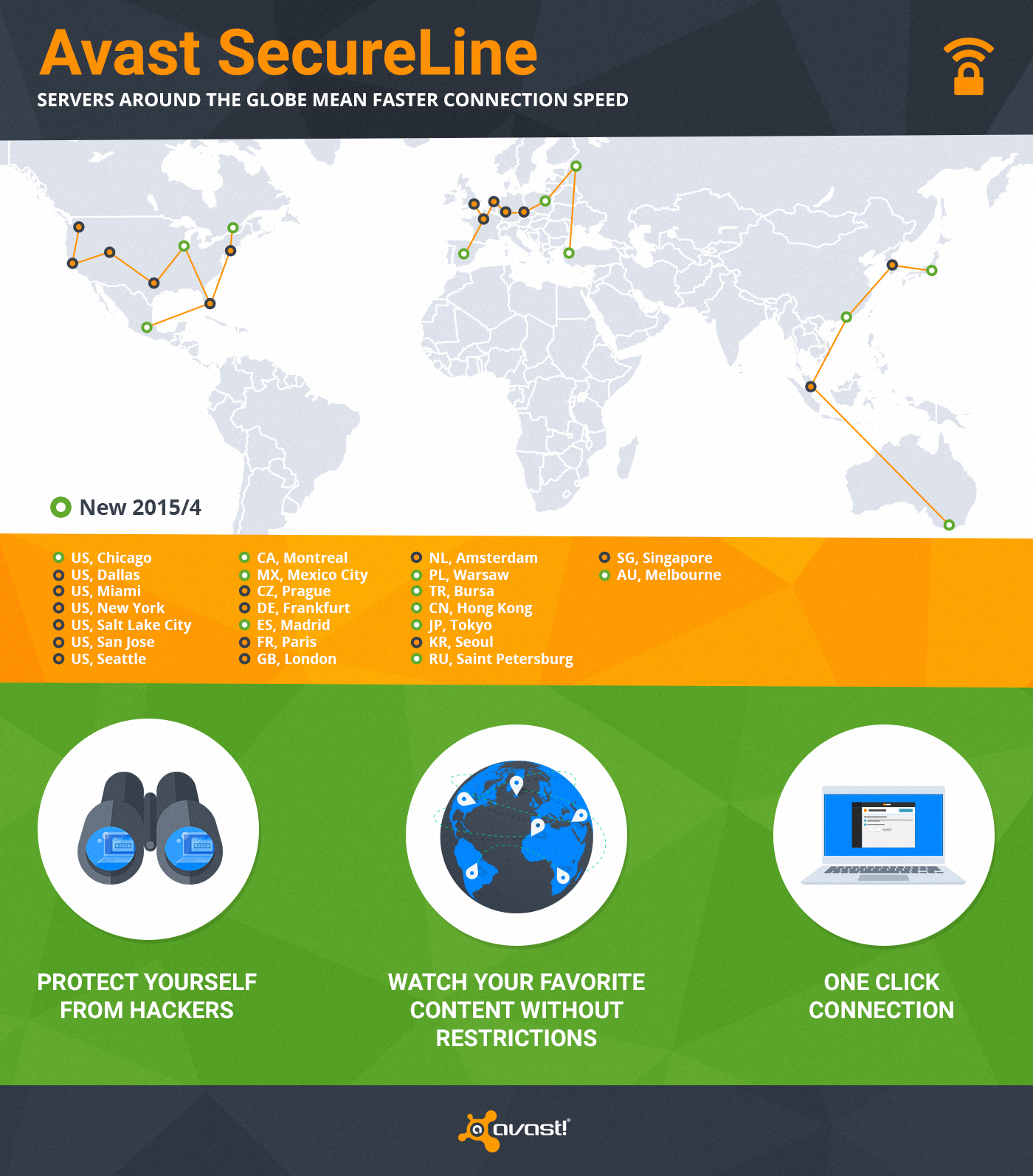
We have servers all over the world so you can connect to our virtual locations anytime you don’t want anyone to monitor or log your Internet activity. We just expanded SecureLine with an additional 10 servers to ensure you have a faster connection speed.
One of the great bonuses of SecureLine is that it allows you to visit local websites restricted to visitors from abroad. With SecureLine connected to a local server, you can watch your favorite shows or listen to streaming radio in another country. That’s because SecureLine makes it look like you’re connected from the right location to access the content. (You know those countries that have blocked Facebook, YouTube, and Twitter? A VPN is how people can still connect.)
When you connect SecureLine on your PC, Mac, or Android phone, here’s what you can expect.
1) Privacy protection – hides your Internet activity anywhere on the web
2) Bypassing geo-restricted content, so you can watch your favorite content
3) You are anonymous – we don’t log what users do when connected through SecureLine
4) Ease of use – only one click and you are connected to one of 24 servers worldwide
How to use SecureLine VPN
SecureLine VPN is part of Avast Antivirus. Simply open your Avast user interface, choose the Tools option in the left menu, then click the SecureLine VPN button. Licenses for Windows, Android, and iOS versions of Avast SecureLine VPN are separate.
Supports: Windows, iOS 7.0 or later, Android 4.0 and up
Servers: North America – Chicago, Dallas, Miami, New York, Salt Lake City, San Jose, Seattle, Montreal, Mexico City; Europe – Prague, Frankfurt, Madrid, Paris, London, Amsterdam, Warsaw, Bursa, Saint Petersburg; Asia/Oceania – Hong Kong, Tokyo, Seoul, Singapore, Melbourne
