This Metasploit module exploits a file upload vulnerability in ManageEngine OpManager and Social IT. The vulnerability exists in the FileCollector servlet which accepts unauthenticated file uploads. This Metasploit module has been tested successfully on OpManager v8.8 – v11.3 and on version 11.0 of SocialIT for Windows and Linux.
All posts by 007admin
WPScan Vulnerability Database a New WordPress Security Resource
Researcher Ryan Dewhurst released the WPScan Vulnerability Database, a database housing security vulnerabilities in WordPress core code, plug-ins and themes. It’s available for pen-testers, WordPress administrators and developers.
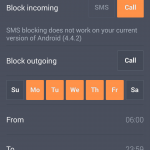
Avast safeguards your teen’s smartphone
Teenagers are responsible for their smartphones. Help them keep it safe with a few easy additions.
Seven out of ten high schoolers take a smartphone to school. Not only are these phones being used for surfing the Internet or social networking, but they help kids navigate around campus, connect with teachers and other students, and follow streaming campus news. Many parents see equipping their teenager with a mobile phone as a safety tool and a way to keep in closer contact, especially if an emergency arises.
The first thing to do after buying your teenager a smartphone
Most kids are using a device with an Android operating system and no added security protection. The first thing you should do is to download a security app to protect the phone and data on it.
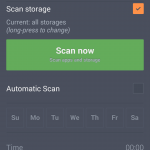
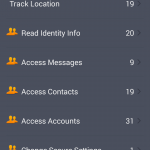
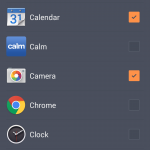
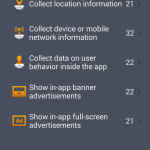
The newest version of avast! Mobile Security & Antivirus is out now, with a completely re-imagined user interface, making it simpler and even more user friendly than it was before. Avast! Mobile Security is free, and it will instantly begin protecting your child from downloading bad apps, protect against spyware and block malware, and backup contacts, SMS/call logs, and photos.
Install avast! Mobile Security and Antivirus from the Google Play store.
The second thing to do after buying your teenager a smartphone
High school students are busy people, with lots of activities, so it’s likely that your teen’s smartphone will be misplaced. Avast! Anti-theft is a stand-alone app that can be installed separately from avast! Mobile Security. You can use the phone locator features to find the lost or stolen phone, control it remotely, and lock it down.
Once you install avast! Mobile Security, you will be asked to set up the anti-theft module. You can read about that and the remote features you’ll have access to from your my.avast.com account in our avast! Mobile Security FAQs.
Install avast! Anti-Theft from the Google Play store.
Other things to do
- Set up a password for the smartphone. This is easy to do and will serve as the first line of defense against nosy people and thieves.
- Add important numbers to the contact list. Add your mobile number as well as a work line, grandparents, the school, and emergency contacts.
- Know the school’s rules. If phone usage is prohibited during school hours or allowed only during breaks, that’s important information to know.
- Talk to your kids about privacy. This includes a conversation about uploading photos and videos, sexting, and oversharing on social networks.
Thank you for using avast! Antivirus and recommending us to your friends and family. For all the latest news, fun and contest information, please follow us on Facebook, Twitter and Google+. Business owners – check out our business products.
ManageEngine Code Execution / File Deletion
ManageEngine OpManager, Social IT Plus, and IT360 suffer from remote code execution via upload and arbitrary file deletion vulnerabilities.
[ MDVA-2014:016 ] java-1.7.0-openjdk
-----BEGIN PGP SIGNED MESSAGE----- Hash: SHA1 _______________________________________________________________________ Mandriva Linux Advisory MDVA-2014:016 http://www.mandriva.com/en/support/security/ _______________________________________________________________________ Package : java-1.7.0-openjdk Date : September 29, 2014 Affected: Business Server 1.0 _______________________________________________________________________ Problem Description: Updated java-1.7.0-openjdk packages fix an upstream regression: This update provides IcedTea 2.5.2, which fixes several bugs, most notably regressions in the previous release which broke Groovy and several other Java tools and applications. _______________________________________________________________________ References: http://blog.fuseyism.com/index.php/2014/09/02/icedtea-2-5-2-released-back-in-the-groovy/ http://advisories.mageia.org/MGAA-2014-0172.html _____________________________________________
[ MDVSA-2014:191 ] perl-XML-DT
-----BEGIN PGP SIGNED MESSAGE----- Hash: SHA1 _______________________________________________________________________ Mandriva Linux Security Advisory MDVSA-2014:191 http://www.mandriva.com/en/support/security/ _______________________________________________________________________ Package : perl-XML-DT Date : September 29, 2014 Affected: Business Server 1.0 _______________________________________________________________________ Problem Description: Updated perl-XML-DT package fixes security vulnerability: The mkxmltype and mkdtskel scripts provided in perl-XML-DT allow local users to overwrite arbitrary files via a symlink attack on a /tmp/_xml_##### temporary file (CVE-2014-5260). _______________________________________________________________________ References: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-5260 http://advisories.mageia.org/MGASA-2014-0390.html _______________________________________________________________________ Updated P
How George Clooney made sure phone hackers didn’t ruin his wedding
Newly weds George Clooney and Amal Alamuddin supplied guests with “burner phones” to prevent photographs from falling into the hands of hackers and the tabloid press.
The post How George Clooney made sure phone hackers didn’t ruin his wedding appeared first on We Live Security.
![]()
How George Clooney made sure phone hackers didn’t ruin his wedding
Newly weds George Clooney and Amal Alamuddin supplied guests with “burner phones” to prevent photographs from falling into the hands of hackers and the tabloid press.
The post How George Clooney made sure phone hackers didn’t ruin his wedding appeared first on We Live Security.
![]()
AllMyGuests 0.4.1 XSS / SQL Injection / Insecure Cookie Handling
AllMyGuests version 0.4.1 suffers from bypass via malformed cookies, remote SQL injection, and cross site scripting vulnerabilities.
CloudFlare Rolls Out Free SSL
In a move that will essentially double the number of SSL-protected sites on the Web in the space of 24 hours, CloudFlare on Monday said that it was enabling SSL for all of its more than two million customers for free. The new service is called Universal SSL, and the company is making it available […]