
Craigslist is a website hosting classified ads for jobs, houses, cars… To give you an idea, there are around 10 million new Craigslist ads every month.
As sometimes happens with these kinds of pages, Craigslist has become a hunting ground for fraudsters trying to scam the people who read these ads.
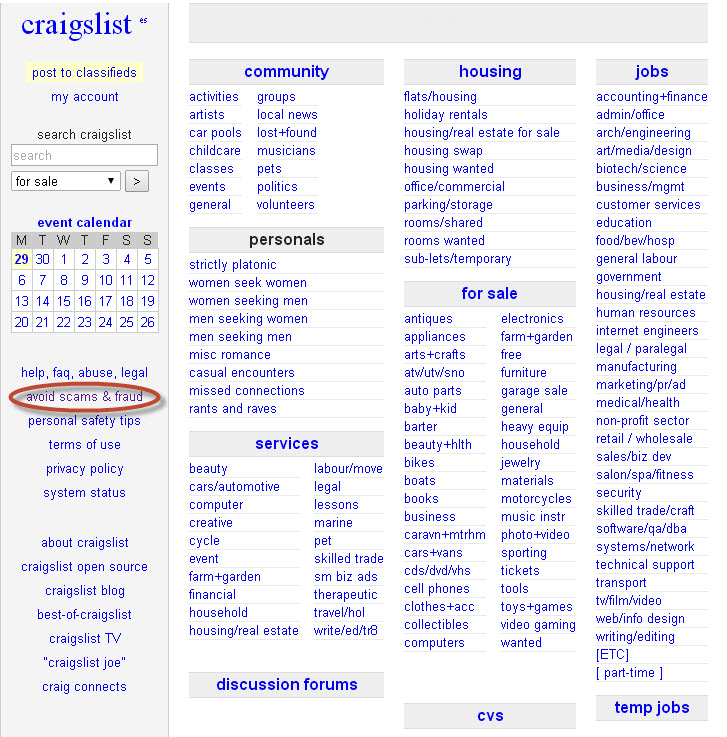
In fact, there’s even an “Avoid scams & fraud†section on the website offering advice on how to improve security in transactions.Â
How to recognize scams on Craigslist
- If the reply sent by the person you have contacted comes from another country, be wary.
- They often ask for payment via platforms such as Western Union or Money Gram or a check or money order as surety on the transaction.
- The other party can’t meet you in person to make the transaction.
- There is a ‘third-party’ who will make the transaction.
Example of fraud on Craigslist
- Companies offering work but who ask for an advance payment from the employee.
- Rental of apartments that don’t exist.
- Sale of cars that ask for payment in advance without you having seen the vehicle.
Tips for avoiding fraud on Craigslist
- Read the ad carefully.
- Don’t buy or rent anything without having physically seen it.
- Take payment in cash. PayPal is also a secure way of receiving payment. Don’t accept checks or money orders.
- Don’t give any type of personal or financial information.
- Be wary of incredible bargains. If you find a low-priced apartment in an up-market area, it’s probably a scam.
- Have a good look at photos. Many scams include photos of things that look too good for the asking price.
We know that criminals are becoming increasingly devious in disguising their scams, so, with your Internet security in mind, please take great care when buying online.
Have you ever fallen victim to a similar scam?
The post The Craigslist scams appeared first on MediaCenter Panda Security.