OWASP published the latest iteration of its Testing Guide, an informational manual designed to teach developers how to build and maintain secure application.
iOS 8. Apple increases user privacy
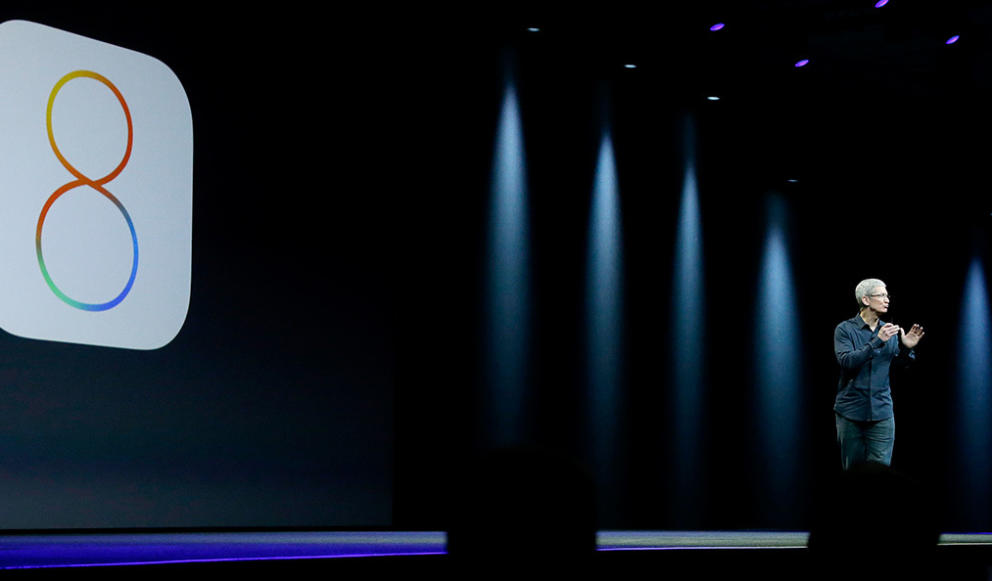
No doubt if you have an Apple device, you’ll know that the new iOS 8 operating system is now available. What you might not know is that installing it will prevent Apple from accessing users’ devices without their consent.
This has been announced by the company, which says that “unlike their competitors” they will not access users’ systems without their permission. They claim that it is therefore not technically possible for them to comply with government orders to retrieve data from devices running iOS 8.
So how is privacy enhanced with iOS 8? To prevent itself from accessing these devices, Apple has modified its encryption system which is applied automatically when users select their password.
This way, Apple’s new operating system has taken a step forward in increasing privacy, as all the information stored on users’ iPads or iPhones (photos, emails, files, etc.) will be protected not only from Apple, but also from governments.
This is clearly how Apple has responded to accusations of collaboration with the National Security Agency (NSA) by handing over its customers personal data. Similarly, the company has also assured that it only provided the data of “less than 0.00385%” of Apple device users. ”
We remind you that it’s important to scan your iPhone or iPad for malware that could affect the functionality of your device. For your peace of mind, try our antivirus for Mac.
More | Cyber-espionage. Can you avoid it?
The post iOS 8. Apple increases user privacy appeared first on MediaCenter Panda Security.
Comprehensive Guide To Obliterating Web Apps Published
Jihadi Terrorists DIDN'T Encrypt Their Comms Because Of Snowden Leaks
US Military Contractors 'Hit By Chinese Hackers'
Apple Expands Data Encryption Under iOS 8, Making Handover To Cops Moot
The dangerous side of USB convenience
How many USB devices do you own? At this moment, you probably have one or more of them connected to your computer. USB devices are everywhere, and they come in the form of flash drives, webcams, keyboards, and so on. One of the attractive things about a USB connection is that you just plug in a device and it works. That convenience, while nice to have, presents a real danger.
For years, many computer users have just plugged in USB devices without putting much thought into any vulnerabilities they might present, but hackers have found ways to prey on the carefree nature of USB usage. You may remember the Stuxnet worm that targeted nuclear facilities in Iran. USB flash drives were used to initiate the infections, and this brought a lot of attention to how USB devices could play a key role in ITÂ attacks.
Fast-forward a few years to today and USBs are a hot security topic once again because of details revealed by security researchers about an exploit called BadUSB. Essentially, the BadUSB hack makes it possible to reprogram the firmware on USB devices, which means that they can then be used maliciously. Since the majority of USB devices will just accept any firmware update that they’re offered, it’s really difficult to know if the firmware on your device is secure or not.
That said, any malware introduced via USB can be detected, depending on the payload. It is why we can consider #BadUSB as being a means to install malware on a machine rather than being a specific virus or malware itself.
Because of the insidious way in which this hack works, protecting yourself from it is really difficult at this point. One of the most logical things that you can do is to make sure that the USB devices that you use have remained only in your possession. USB flash drives in particular tend to get passed between people on a regular basis, but based on this new information, that’s not always such a good idea.
The post The dangerous side of USB convenience appeared first on Avira Blog.
New Initiative Simply Secure Aims to Make Security Tools Easier to Use
The dramatic revelations of large-scale government surveillance and deep penetration of the Internet by intelligence services and other adversaries have increased the interest of the general public in tools such as encryption software, anonymity services and others that previously were mainly of interest to technophiles and activists. But many of those tools are difficult to use […]
Airplane WiFi – Secure surfing or danger for onboard electronics?
The “fasten your seatbelts” signs turn off and you can finally recline, fold down the tray table, and switch on your notebook or tablet. Many airlines now even offer WiFi access in the cabin, so you can surf the Internet, post to Facebook, and write emails without restriction. Hard to believe, given that it wasn’t long ago that you couldn’t even leave your cell phone switched on during the flight. So, is it safe and secure to use WiFi and portable devices? There are two major aspects to this question:
- First, whether airplane systems are secure, even though WiFi radio waves are used to communicate and passengers have access to the digital infrastructure aboard the airplane.
- And second, whether passengers’ devices are also safe and secure, as they share the airplane WiFi network with all other users in the cabin.
Hacking airplane systems
A clear answer can be given to the first question, at least at the moment: Yes, the airplane is still safe and secure. The radio waves are irrelevant to the onboard electronics in terms of power and frequency, as the cockpit and internal technology have to be able to cope with completely different types of possible interference. In addition, there is no potential risk of airplane systems being hacked into. Every airplane manufacturer separates the in-flight entertainment and WiFi systems from the critical airplane systems. Furthermore, they use data and signal formats to communicate, which are incompatible with Ethernet; they also don’t use the TCP/IP protocol. Frequently, additional security functions are integrated into the systems, such as specific transmitter restrictions and extremely strict time intervals, within which data must be exchanged between communication partners. And even if there was a widespread failure of the electronics system, irrespective of what measures are taken to deal with it, all flight-critical systems have a mechanical backup – cable controls and hydraulic systems instead of servos and electronic actuators.
This doesn’t mean, however, that airplanes are immune to potential security loopholes. Researchers are repeatedly discovering weaknesses in various systems, such as those involved in satellite communications, which could theoretically be exploited. By exploiting this bug, false positioning data can be transmitted to the airplane while in flight causing a change of course; however, other experts have given the all-clear. Even if a person were able to exploit this security loophole, the pilots themselves could just simply make a course correction. Other means of communication are available in each passenger airplane which allow verification of positioning data and flight plans. On top of this, the flight-control center would also spot each course change and alarm the pilots.
The statistical probability of mounting such attacks successfully is far below the other typical causes of failure, technical or human error, which are also rare. Airplane manufacturers also want to save costs and are trying wherever possible to integrate standard IT components that transfer and process data using standard IT formats.
Airline operators have set out countless operational cases where digital data would improve services, shorten ground times, and resultingly save costs. Whether over the short term or long term, manufacturers will eventually meet these requests and integrate an ever greater amount of standard IT equipment into airplanes. Hopefully the security measures will be tightened to meet the aviation industry’s more stringent requirements.
Security measures above the clouds
So how about the information on your notebook or tablet? WiFi access aboard an airplane is just like a standard public hotspot – no difference from the one in the airport or at Starbucks. Those who use the WiFi network share the wireless network with all other users. Whether airplane manufacturers integrate specific security measures in their switches and routers is information that currently only they know. For this reason exactly, the same security measures that are also suitable at Starbucks or in the airport should apply: Either you encrypt all data traffic using a virtual private network (VPN), which companies usually install on professional users’ devices anyway, or you encrypt each app’s data. In the case of email, this can be done using encryption programs like Pretty Good Privacy (PGP), EnigMail or GnuPG. For browser-based communications, it can be achieved using Secure Sockets Layer (SSL) technology, usually identifiable by the little padlock icon in the address bar. Plug-ins for many browsers can also take care of this automatically if required, such as HTTPS Everywhere for Firefox and Chrome. Naturally, the internal firewall should be enabled on each device and the latest version of a security software solution such as Avira Antivirus Pro, Avira Internet Security Suite or Avira Free Antivirus should also be installed and active.
The post Airplane WiFi – Secure surfing or danger for onboard electronics? appeared first on Avira Blog.
Scottish independence poll – warning over phishing scams
This Thursday, September 18, is the biggest day in Scottish political history, as the country votes on whether it should become independent from the United Kingdom – but an ESET security expert has warned cybercriminals could strike.
The post Scottish independence poll – warning over phishing scams appeared first on We Live Security.
![]()
