By using some retailer’s apps to make your holiday wish list, more people than just Santa Claus can see your list. In fact, it may be accessible to anyone over the Internet!

America’s most popular retailers collect more information about you via apps than you may be comfortable with.
Recently, the Avast Security Warriors began looking into shopping apps to see what your favorite retailers know about you. They found that these apps, like many other apps out there, collect data and request permissions that are unnecessary for their app to function properly.
Initially, we were curious to see what retailers wanted to know about their customers based on the data they collect. We randomly chose apps from the following retailers: Home Depot, J.C. Penney, Target, Macy’s, Safeway, Walgreens and Walmart. In this blog post, we focus on Target and Walgreens.
You’re making your list and Target is checking it twice!
If you created a Christmas wish list using the Target app, it might be accessible to more people than you want to actually receive gifts from. The Target app keeps a database of users’ wish lists, names, addresses, and email addresses. But your closest family and friends may not be the only ones who know you want a new suitcase for your upcoming cruise!
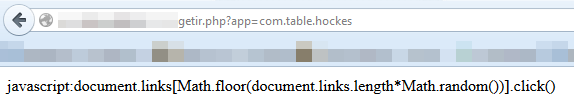
To our surprise, we discovered that the Target app’s Application Program Interface (API) is easily accessible over the Internet. An API is a set of conditions where if you ask a question it sends the answer. Also, the Target API does not require any authentication. The only thing you need in order to parse all of the data automatically is to figure out how the user ID is generated. Once you have that figured out, all the data is served to you on a silver platter in a JSON file.
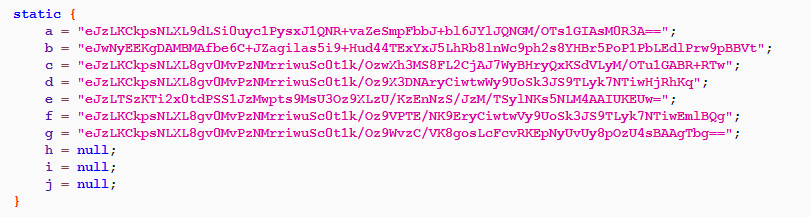
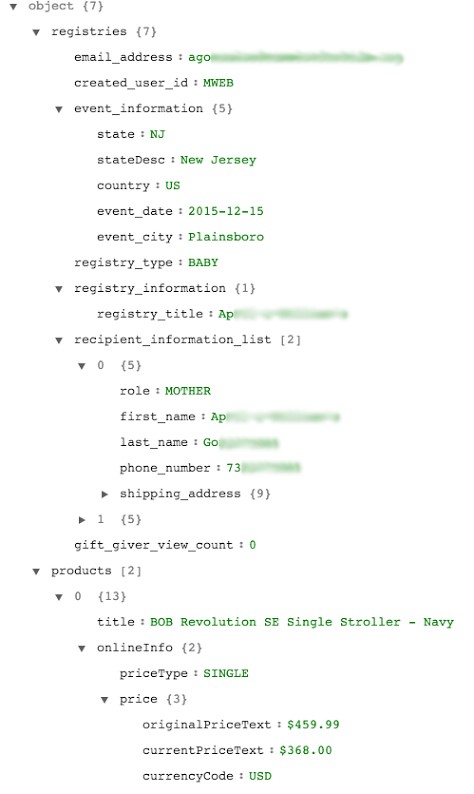
The JSON file we requested from Target’s API contained interesting data, like users’ names, email addresses, shipping addresses, phone numbers, the type of registries, and the items on the registries. We did not store any personal information, but we did aggregate data from 5,000 inputs, enough for statistical analysis.
An example of the data that we were able to obtain via Target’s API
Target doesn’t know if you’re naughty or nice, but they do know who you are
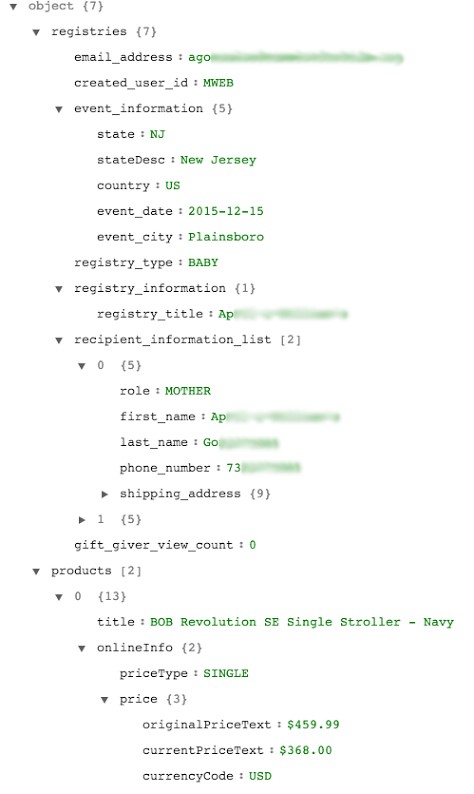
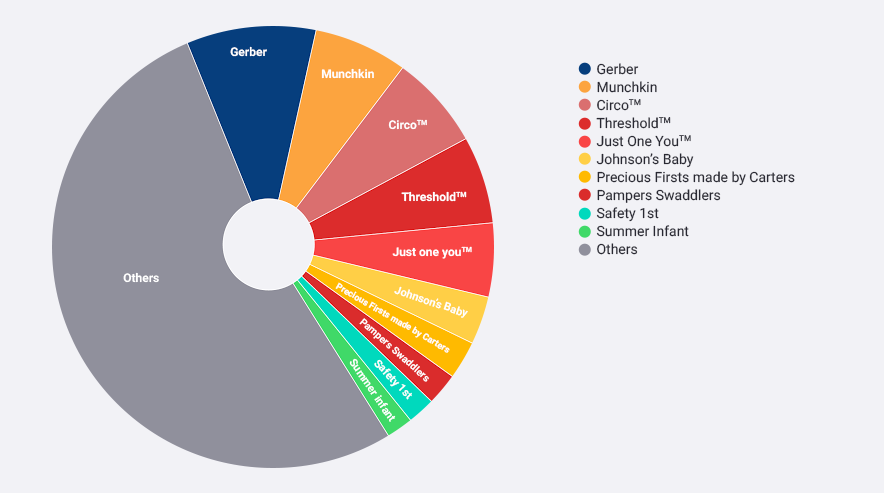
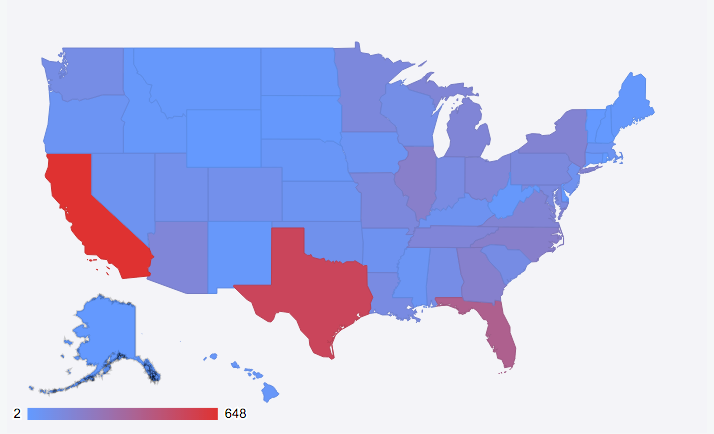
We took the 5,000 random inputs, and out of curiosity, looked at which brands appear on their registry the most, which states the Target app users are from, and what the most common names of people using Target’s app are.
The top 10 brands on Target app users’ registries
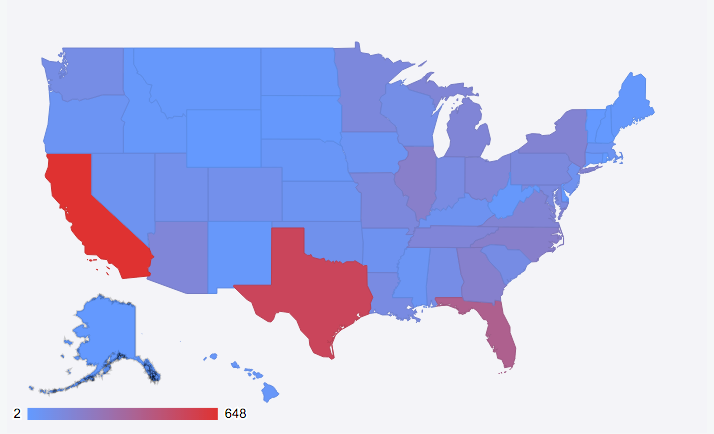
Map showing where the 5,000 app users are from within the U.S.
There were more than 1,700 unique names in our sample – these are the top 20 names of Target app users.
Jasmine 162
Jamie 132
Jessica 79
Ashley 67
Jackie 67
Jordan 64
Amanda 58
Jennifer 55
Sarah 45
Jacqueline 41
John 39
Megan 38
Dominique 36
Heather 34
Amber 33
Jade 33
Melissa 32
Stephanie 32
Katie 31
Brittany 30
In addition to collecting personal data, the shopping apps we looked at also request a plethora of permissions.
The prize for the most unnecessary permissions requested by a retail app goes to…
 If you want to choose a shopping app based on the amount of unnecessary permissions it collects then Walgreens is the app for you!
If you want to choose a shopping app based on the amount of unnecessary permissions it collects then Walgreens is the app for you!
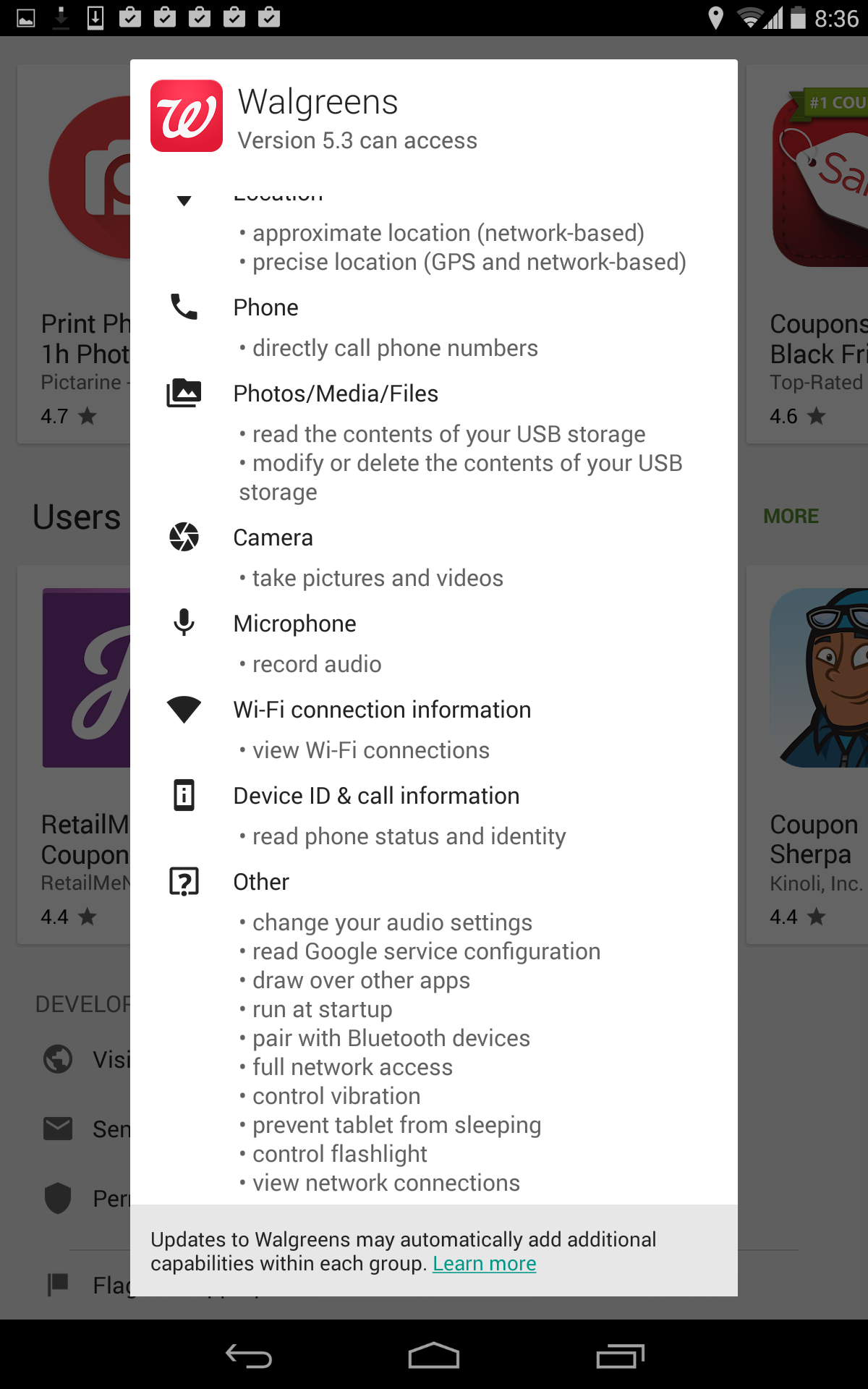
The Walgreens app not only requests permissions that are completely unnecessary for its app to function, but also requests more permissions than any of the other retail apps we looked at – see screenshot below. The Home Depot app came in close second in terms of unnecessary permissions requested.
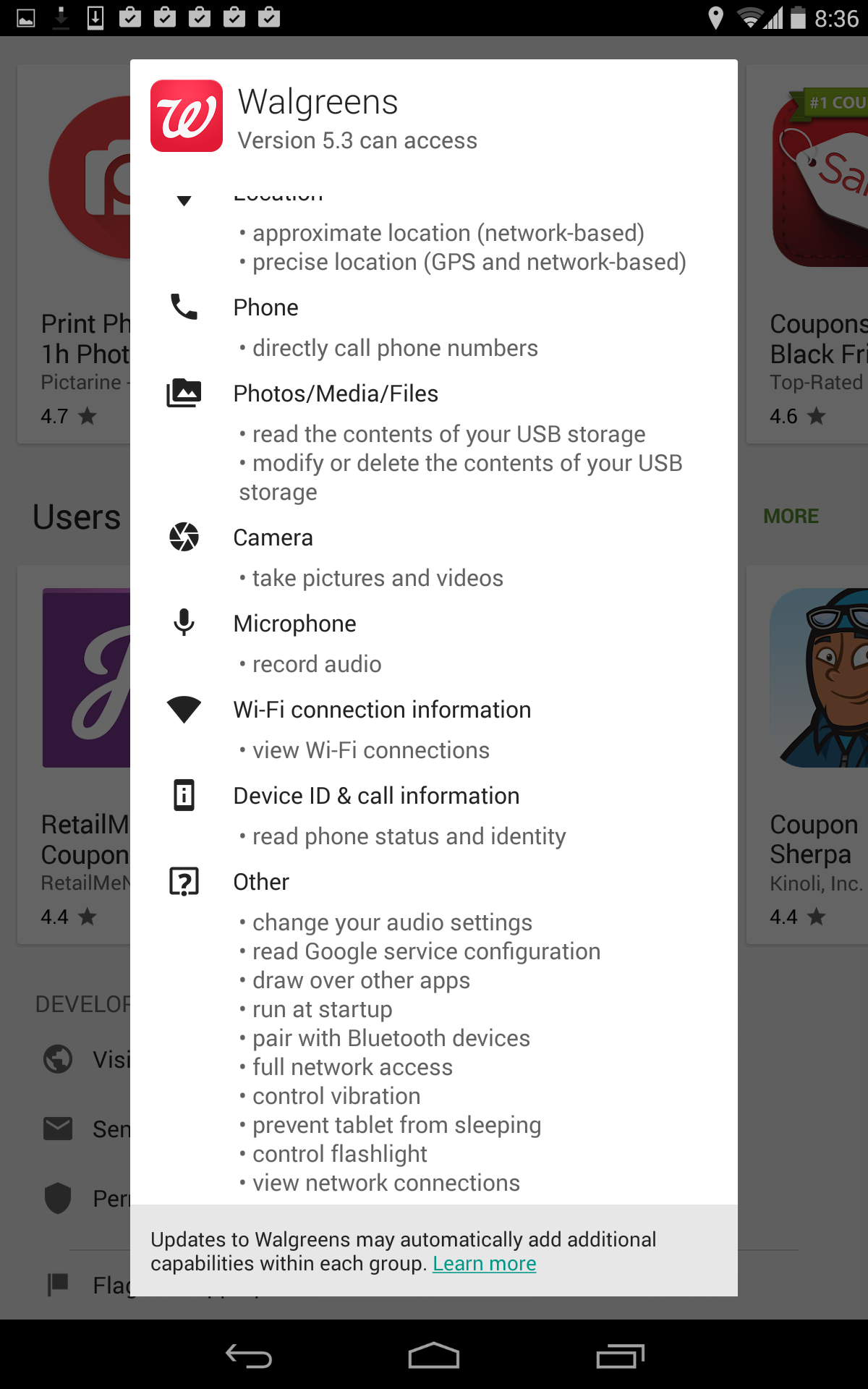
The Walgreens app has permission to change your audio settings, pair with blue tooth devices, control your flashlight, and run at startup – completely unnecessary for the app to function properly. On the bright side, these retail apps aren’t the most permission-hungry apps we have ever seen, in fact compared to other apps out there they are decent.
But, now imagine what could happen if this valuable customer data landed in the wrong hands. The ways this data could be misused are far and wide. It is, therefore, important that people are aware of how many permissions they grant the apps they use and understand what data the apps collect.
Stay tuned for more as we investigate the vulnerabilities of mobile apps and the need for mobile security.
Continue reading Retailer’s apps reveal your Christmas list to the public →
![]()



 If you want to choose a shopping app based on the amount of unnecessary permissions it collects then Walgreens is the app for you!
If you want to choose a shopping app based on the amount of unnecessary permissions it collects then Walgreens is the app for you!