Mike Mimoso and Chris Brook discuss the news of the week, including Pwn2Own 2017, Microsoft’s silence around February’s Patch Tuesday, and a nasty SAP bug.
Tag Archives: hack
Has anyone hacked my IoT?

Forget about those big attacks, what about little me?
The post Has anyone hacked my IoT? appeared first on Avira Blog.
Passwords of the (not) rich and famous
I’ve got something in common with Facebook CEO Mark Zuckerburg
The post Passwords of the (not) rich and famous appeared first on Avira Blog.
SWIFT-ly goes the money
Multi-million dollar thefts with the SWIFT system have five security lessons for ordinary people.
The post SWIFT-ly goes the money appeared first on Avira Blog.
Webcams: The modern rear-view mirror
This year the new TV series, “Scream,” was released. Not bad, but in my humble opinion, it has the same problem that a lot of movies have: it has a powerful beginning but deflates and loses strength gradually until the end. The question is, why am I talking about TV in a malware- and AV-related blog?
The post Webcams: The modern rear-view mirror appeared first on Avira Blog.
TalkTalk data breach
Over the last few days, more details pertaining to the recent news that TalkTalk has suffered a data breach have been made public, but there are still many questions about exactly what was taken. In many data breach cases, details are limited by the need for the company and law enforcement agencies to ascertain the extent of the breach and to collect evidence.
With the news that a suspect has been arrested in connection to the cyber attack, I am sure more details will start to become available over the coming days.
So far, it appears the data exposed – some of which may have been encrypted – could include: names, addresses, DoBs, email addresses, phone numbers, TalkTalk account information, bank details and partial credit card details. But what could this mean practically?
Take account information, for example – is a user’s Active Choice information held within their account settings? If so, I wonder how many people would be embarrassed by people discovering they have disabled porn filters on their broadband. With this sort of personal information, could we be looking at ‘Ashley Madison 2.0′?
Looking at recent data breaches, spear phishing is a frequent method of entry – targeting individuals within a company or organization to reveal details allowing hackers access to internal systems.
This means implications for both companies and consumers. Organizations should limit employee access to sensitive information in order to limit the risk of falling victim to attacks like this. Employee education – ensuring workers are aware of the dangers – is also paramount.
My advice to consumers:
- Ensure other online accounts aren’t using the same email and password combination as stored with TalkTalk. If so, change them.
- Be wary of spammers sending emails that look like they’re coming from TalkTalk. Scrutinize these emails carefully and, if in doubt, contact TalkTalk directly to ensure it’s an official communication.
- If you are concerned that credit card details have been breached, then call your card company and have the card suspended or stopped.
![]()
![]()
Arrest Made in TalkTalk Hack
TalkTalk CEO Dido Harding said someone purporting to be the hackers who attacked the U.K. telecom demanded a ransom to keep them from publishing the stolen data.
Stagefright the sequel – Android devices vulnerable again
Researchers at Zimperium, a specialist cybersecurity company, has announced that it has found another major vulnerability in the Android operating systems that many of us use on our mobile devices.
A blog post published by Zimperium says “Meet Stagefright 2.0, a set of two vulnerabilities that manifest when processing specially crafted MP3 audio or MP4 video files.” Nearly every single device since Android 1.0, released in 2008, is affected according to the blog post. The researchers were able to exploit the flaw in devices running Android 5.0 and later, and conceptually nearly every single device since Android 1.0 (2008) could be affected. According to Zimperium, earlier devices could be impacted through media players and instant messenger that use the Stagefright library.
Media files carry additional information called metadata, which is processed when the file is opened or previewed. This means the video or audio file on the device would not even need to be opened by the user for the attack to occur. Once the device was infected, the most likely method an attacker would use would be via a web browser.
How might this happen in a real environment?
- An attacker will try to convince you to visit a link that points to an infected website via either a malicious ad campaign or using spear-phishing techniques.
- An attacker on the same network as you could inject the exploit by intercepting your mobile network traffic destined for the browser.
- Infection of 3rd party apps that are using the vulnerable software library.
Zimperium has said that they notified Google’s Android Security team in August, and that Google responded quickly to try and fix it. They’ve also said that full technical details of the exploit will not be released publicly until Google has confirmed that the issue has been fixed and is available to users.
Bugs and vulnerabilities in operating systems are not uncommon. This exploit highlights the need for users to ensure that their devices are running the very latest version of their operating system and applications.
Unfortunately, unlike the first time Stagefright appeared, when disabling the automatic retrieval of MMS messages could prevent your device from being infected, this time we need to wait for the update from Google, our phone carrier as well as our handset manufacturers to make it available to us.
In the meantime there are some precautions you can take:
- Check with your handset provider or carrier for a patch/update.
- Update all the apps you have on your device.
- Avoid downloading media files from untrusted sources, and even when trusted, use caution.
- If you haven’t disabled the ‘Auto retrieve MMS’ feature, switch it off now.
Remember, the most important thing you can do is keep your operating system and apps up to date. For that extra layer of protection, download AVG AntiVirus for Android to help protect your devices against malicious phishing sites.
Follow me on Twitter @TonyatAVG
![]()
![]()
Taking a closer look at cracked Ashley Madison passwords

Photo via The Times UK
People create terrible passwords. As simple as this might sound it unfortunately remains news to millions — if not billions — of individuals who use the Internet. As proof, we’ll take a look at a selection of passwords that were revealed in the Ashley Madison leak.
Regardless of any shortcomings Ashley Madison had in terms of securing their perimeter against breaches, one thing that they did right (to the surprise of many security researchers and disappointment of many black hats) was encrypting their users’ passwords.
The leak contained a database of around 36 million usernames, with bcrypt-hashed passwords. There is no known way to crack all of these passwords before the heat death of the universe, especially assuming that some are truly random, but we can crack the worst ones.
Conveniently, the web is full of known-password lists that anyone can just download. The two we chose for this crack, which are widely available, are the so-called 500 worst passwords of all time (compiled in 2008) and the 14-million-strong password list from the rockyou hack.
Cracking the bcrypt
It should be noted that we did not use the full list of 36 million password hashes from the Ashley Madison leak; we only used the first million. So, that may skew the results towards passwords created near the beginning of the site’s existence, rather than the end. Also, since the system used contains a 6-core CPU and two GTX 970 GPUs, we set the CPU to test the 500 worst list, and the GPUs to test the rockyou list. Because we’re SMRT, we used the same million for both the CPU and GPU cracks, which therefore produced redundant results in our output files. This has the side-effect of being less efficient overall, but allows us to make an apples-to-oranges comparison of the effectiveness of the two password lists, as well as the CPU vs GPU cracking speed.
Before we get into the results, let’s take a quick diversion to explain why this hack was so difficult and only revealed a small number of passwords.
What is encryption? What is bcrypt? Why is it significant?
If you know the answer to these questions, you may safely skip this section and move on to the juicy innards of the dissection. For those who stick around, we’ll try to keep it simple… no promises.
Encryption algorithms can be broken into two broad categories: reversible and irreversible. Both have their uses in different contexts. For example, a secure website, such as Google, wants to send you data, and wants you to see the data that it sends you. This would be a case for reversible encryption:
[ plain text ] -> (encryption black box) -> encrypted data -> (decryption black box) -> [ plain text ]
The other method is irreversible encryption, which looks more like this:
[ plain text ] -> (encryption black box) -> encrypted data
Notice that there’s no decryption — the encryption black box makes that impossible. This is how passwords are stored on a server administered by someone who cares about security.
At first glance, this seems a bit strange. “If my password is encrypted and you can’t reverse the encryption, how do you know if the password is correct?”, one might inquire. Great question! The secret sauce lies in the fact that the encryption black box will always produce the same output with the same input. So, if I have some plain text that is claiming to be the password, I can input that text into the black box, and if the encrypted data matches, then I know that the password is correct. Otherwise, the password is incorrect.
There are many irreversible encryption algorithms (the more formal word for “black box”), including but not limited to:
- md5
- sha1
- sha2 (sometimes shown as sha256 or sha512 to indicate its strength)
- PBKDF and PBKDF2
- bcrypt
All of these algorithms take an input password and produce an encrypted output known as a “hash”. Hashes are stored in a database along with the user’s email or ID.
From the above list, md5 is the simplest and fastest algorithm. This speed makes it the worst choice of encryption algorithm for passwords, but nonetheless, it is still the most common. It’s still better than what an estimated 30% of websites do, which is store passwords in plaintext. So why is being fast bad for an encryption algorithm?
The problem lies in the way that passwords are “cracked”, meaning that given a hash, the process of determining what the input password is. Since the algorithm can’t be reversed, a hacker must guess what the password might be, run it through the encryption algorithm, and check the output. The faster the algorithm, the more guesses the attacker can make per second on each hash, and the more passwords can be cracked in a given amount of time with the available hardware.
To put the numbers in perspective, a common password cracking utility, hashcat, can do about 8.5 billion guesses per second on a GeForce GTX 970 (this is not the best card on the market, but we happen to have two available for use). This means that one card could take the top 100,000 words used in the English language and guess the entire list of words against each md5 password hash in a database of 85,000 hashes in a single second.
If you want to test every two-word combination of words from the top 100,000 (10 billion guesses per password hash), it would take 1.2 seconds per hash, or just over a day to test that same list of 85,000 hashes. And that’s assuming we have to try every possible combination on each password hash, which, given how common terrible passwords are, is likely not the case.
Enter bcrypt.
By design, bcrypt is slow. The same card that can test 8.5 billion hashes per second with md5 can test on the order of 50 per second with bcrypt. Not 50 million, or even 50 thousand. Just 50. For that same list of 85,000 passwords being tested against 100,000 common English words that took one second with md5, bcrypt would take over 50 years. This is why security experts unanimously agree that bcrypt is currently one of the best choices to use when storing password hashes.
But, even it only protects good passwords.
Enough about bcrypt — what did we find?
After about two weeks of runtime, the CPU found 17,217 passwords and the GPU found 9,777, for a total of 26,994; however, 25,393 were unique hashes, meaning that the CPU and GPU redundantly cracked 1,601 hashes. That’s a little bit of wasted compute time, but overall not bad. Of the 25,393 hashes cracked, there were only 1,064 unique passwords.
For reference, the top 20 most common passwords according to the 500-worst list are:
1:123456
2:password
3:12345678
4:1234
5:pussy
6:12345
7:dragon
8:qwerty
9:696969
10:mustang
11:letmein
12:baseball
13:master
14:michael
15:football
16:shadow
17:monkey
18:abc123
19:pass
20:fuckme
Below are the top 20 from the Ashley Madison list cracked so far, formatted as “rank: count password”:
1: 6495 123456
2: 3268 password
3: 2024 12345
4: 880 12345678
5: 768 qwerty
6: 453 pussy
7: 248 secret
8: 209 dragon
9: 201 welcome
10: 198 ginger
11: 173 sparky
12: 168 helpme
13: 164 blowjob
14: 152 nicole
15: 134 justin
16: 129 camaro
17: 120 johnson
18: 117 yamaha
19: 113 midnight
20: 103 chris
It’s important to note that this ranking is NOT the ranking of passwords used by the users of Ashley Madison at large. It is simply the ranking of passwords cracked so far from a subset of 1 million users of the site, which may also be the first (oldest) million. And by “so far”, we mean that the CPU crack is about 4.8% complete, and the GPU crack is about 0.0008% complete. The estimated completion time is so far in the future, hashcat is having a difficult time computing it, but it’s certainly on the order of decades or centuries.
Given those caveats, we can still make a few conclusions about the data with high confidence:
- “123456” and “password” reign supreme as the two worst possible and most-used passwords. They are constantly encroached by “12345678” and “qwerty”.
- “pussy” is, surprisingly, not significantly more or less common on a website promoting marital infidelity than it is on the web at large.
- “helpme” is, we think unsurprisingly, more common.
- “blowjob” is likely what many users want out of their membership on the site.
- Female names or nicknames appear to also be relatively common. Especially “ashley” and “madison”, for some unknown reason.
If you’re interested, here are the results of just the CPU crack so far using the 500-worst list:
1: 6495 123456
2: 3268 password
3: 1940 12345
4: 880 12345678
5: 716 qwerty
6: 454 pussy
7: 233 secret
8: 202 dragon
9: 201 welcome
10: 198 ginger
11: 173 sparky
12: 168 helpme
13: 164 blowjob
14: 152 nicole
15: 129 camaro
16: 128 justin
17: 120 johnson
18: 113 midnight
19: 110 yamaha
20: 103 chris
And just the GPU crack so far using the rockyou list:
1: 619 123456
2: 349 password
3: 279 12345
4: 116 qwerty
5: 103 123456789
6: 83 696969
7: 82 abc123
8: 82 12345678
9: 76 football
10: 73 baseball
11: 71 1234567
12: 70 fuckme
13: 69 ashley
14: 61 fuckyou
15: 58 asshole
16: 57 mustang
17: 52 superman
18: 50 111111
19: 47 password1
20: 47 hockey
This list is a little different from the list that another security researcher came up with using the same rockyou wordlist on the first 6 million passwords, but at least the top few are pretty consistent.
Outside of the top 20, there are some other interesting observations. Again, none of these are conclusive or precise, and even the order-of-magnitude may be off, but the sample size is at least large enough to see some trends:
There are at least 25 unique passwords with the word “love” in them:
78: 27 iloveyou
132: 18 lover
236: 11 lovers
237: 11 loverboy
266: 10 mylove
270: 10 loveme
304: 9 lovely
338: 8 onelove
454: 6 lovebug
522: 5 loveyou
606: 4 lovelove
723: 3 iloveu
828: 2 lover1
848: 2 iloveyou1
849: 2 iloveme
918: 1 truelove
969: 1 loveya
970: 1 loves
971: 1 loveme1
972: 1 lovehurts
973: 1 love123
974: 1 love12
985: 1 iloveyou2
987: 1 iloveu2
1038: 1 babylove
We’re not sure how sincere those 8+ people are who used “onelove”, or if those 27+ people using “iloveyou” are lying or using “you” as a plural, but we’re pretty sure those 2+ people who used “iloveme” were at least honest with their password. And “babylove” is a bit weird.
The passwords “fuckme” and “fuckyou” were both used by 60+ people, which in this test was about as common as “baseball” and “football”:
31: 76 football
33: 73 baseball
34: 70 fuckme
38: 61 fuckyou
76: 28 fuckoff
105: 21 basketball
217: 12 fuckyou1
241: 11 fuckyou2
274: 10 football1
308: 9 fucker
431: 6 softball
500: 5 snowball
547: 5 baller
The password “panther” was also pretty common, ranking about 40th. If you are unsure why that is, it’s the opposite of “cougar”, which did not appear on the list. It’s not hard to guess what a lot of the site’s men wanted, and what demographics they fell into. There were only 3 unique passwords that we found referencing large cat species, and the other two likely reference sports teams:
40: 59 panther
259: 10 tigers
337: 8 panthers
Tigger is plausibly the most popular Winnie the Pooh character among Ashley Madison users:
108: 20 tigger
158: 16 christopher
390: 7 rabbit
443: 6 poohbear
590: 4 piglet
658: 3 winnie
664: 3 tigger1
870: 2 eeyore
Kanga and Roo fans will be disappointed, and Gopher doesn’t really count anyway.
Only 3 unique superheroes that we found:
44: 52 superman
94: 24 batman
295: 9 spiderman
380: 7 superman1
But on the bright side, “superman” is about as popular as “boobs” and “asshole”.
There were 76+ unique all-numeric passwords found, with the top 20 being:
1: 6495 123456
3: 2010 12345
4: 880 12345678
21: 101 123456789
29: 81 696969
32: 74 1234
35: 70 1234567
47: 50 111111
58: 38 654321
68: 33 121212
75: 29 1234567890
83: 26 54321
84: 26 123123
85: 26 000000
90: 25 11111
96: 24 131313
113: 20 666666
126: 19 222222
162: 16 777777
163: 16 55555
The only surprising thing about this is that, given the site in question, why 696969 isn’t ranked higher. And no, 8675309 was not in the list (although someone probably did use it, we just hadn’t found it).
This string of words caught our eyes:
118: 19 newyork
119: 19 maggie
120: 19 jackass
121: 19 dallas
122: 19 cowboy
123: 19 cookie
We’re not going to read anything into that.
Or this:
127: 18 taylor
128: 18 stupid
129: 18 princess
130: 18 patrick
131: 18 mother
132: 18 lover
George Carlin’s Seven Dirty Words didn’t all make an appearance (yet), but the list included a few additional profanities:
6: 450 pussy
34: 70 fuckme
38: 61 fuckyou
42: 57 asshole
76: 28 fuckoff
120: 19 jackass
176: 15 bullshit
217: 12 fuckyou1
241: 11 fuckyou2
308: 9 fucker
680: 3 pussycat
871: 2 dick
The months were not evenly represented:
277: 10 december
339: 8 november
502: 5 september
550: 5 august
645: 4 april
721: 3 january
Nor were the States:
118: 19 newyork
134: 18 dakota
243: 11 florida
352: 8 georgia
363: 8 california
395: 7 mississippi
404: 7 hawaii
414: 7 carolina
659: 3 virginia
Searching for the word “star” brought up “starwars”, but not “startrek”:
97: 23 stars
227: 11 starwars
231: 11 rockstar
326: 8 superstar
Below are a few amusing passwords, in that multiple people used them:
186: 14 police
189: 14 justme
348: 8 internet
351: 8 google
366: 8 booger
403: 7 hotmail
497: 5 unicorn
548: 5 badgirl
549: 5 babyboy
592: 4 peewee
620: 4 gangsta
621: 4 friend
632: 4 creative
699: 3 loser
737: 3 disney
860: 2 genius
861: 2 gangster
Creative? Genius? Just you? I think not.
Conclusion
There is no excuse for using terrible passwords, considering that the usage of intelligent passwords plays a key role in keeping you safe from attacks and breaches. Even with one of the strongest password encryption algorithms out there, it was trivial to get a large list of weak passwords by checking known passwords against the list of hashes.
As citizens of the Internet, it’s up to us to choose strong passwords. We are responsible for our own security, and cannot trust anyone on the Internet to do it for us. Especially not a company whose mission is to promote cheating.
Are there any other trends you’d like us to look for in the recovered passwords list? Let us know by leaving a comment below! Do you have an Ashley Madison account? If so, are you worried that your password might be leaked? Leave your username and password in the comments and we’ll check for it! (Just kidding, please don’t do that.)
If you ever had an Ashley Madison account created before July 15th, 2015, then the hash was definitely leaked. The password may have been cracked already by us or someone else, especially if it was weak. If you haven’t already, go and change it. Even if it was strong, change it anyway. Here is a useful guide on how to create a strong password. Better yet, use a password manager, and only create one strong password that you must remember, and use randomly generated passwords for the rest.
Stay smart and be safe out there!
Follow Avast on Facebook, Twitter, YouTube, and Google+ where we keep you updated on cybersecurity news every day.
![]()
Physical safety is becoming digital security
Imagine rows of people hunched over soldering irons, carefully crafting systems designed to hack wireless devices and networks. Welcome to Defcon 23, a mash-up of talks, small vendor displays and hands-on hacking challenges/competitions dedicated to all things security—and how to break through it.
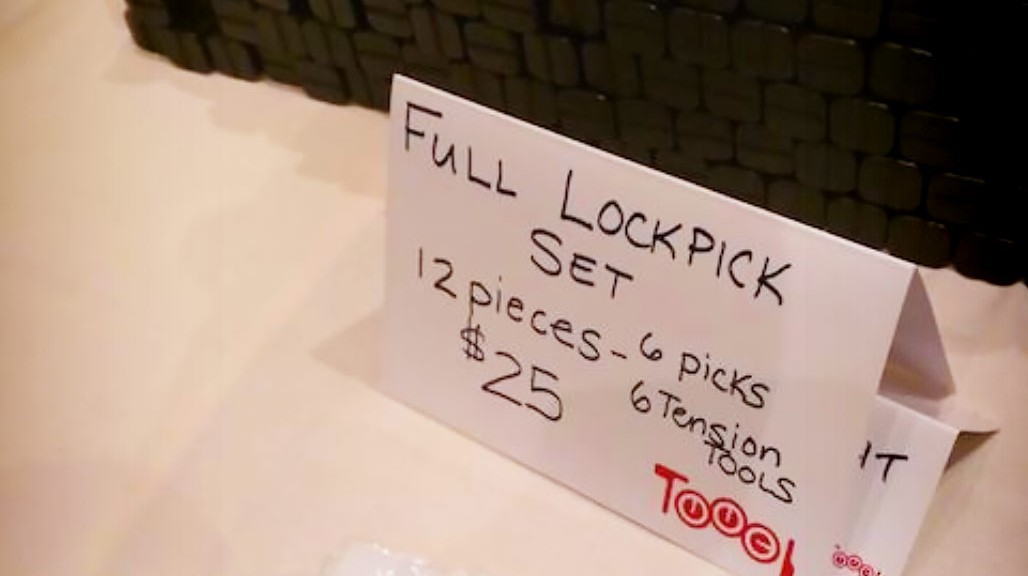
While browsing through booths of physical hacking paraphernalia, I ran across lock-picking tools from Toool. Scattered across the table were lock-picking sets as well as heaps of sample locks, so you could refine your technique.

Picking analog locks is a lot of fun, but I would have expected to see more digital hacking tools, for electronic door locks for example. At AVG we’ve been studying how physical security systems are evolving to become more digital and the security challenges that emerge from this evolution.
Your home door lock will become digital soon (here are some examples), and those skilled with wireless hacking will replace those with lock-picking expertise. Your digital lock will have more functionality than your old analog one. For example, it will probably have a camera, and allow you to let the plumber in even though you are at the office. It is easy to imagine the incremental security concerns that this opens up. While it may take years for this to occur, but it’s not too speculative to imagine that houses with high-value contents will become digital faster than others and provide an attractive target for theft.
Digitizing old technologies, like the door-lock, is just another part of the IoT trend. Next year at Defcon we might see an analog+digital hacking kit, combining lock picks and hacker hardware to open your door. This is something we’re keeping a close eye on as we also develop tools that help monitor and manage your security.
![]()
![]()