
For years cybercriminals have had their focus on money, and most specifically in the financial system. For more than a decade they have been mainly targeting the weakest link in the chain: the final user that uses online banking services. This approach has some benefits for these cybercriminals: poor security in the end user, small money thefts that can go undetected for some time, etc. However it also has some cons: need of money mules, being able to find (infect) a victim that is using one of the targeted banks, avoiding antimalware software, etc.
In other words, they can make a lot of money, but at the same time it will require a lot of effort from their side.
Where is the big money? Financial institutions themselves. There is no discussion about this. However it is hard to break into them, and even more complicated to understand how their specific internal systems work in order to be able to fully compromise them, take the money and leave without leaving a trace. It requires a great investment to gather all the intelligence needed for this kind of heist, it is not easy to perform and it might require several months, if not years, of careful planning. Anyway it is worth it if 1 billion dollars can be stolen in just one hit.
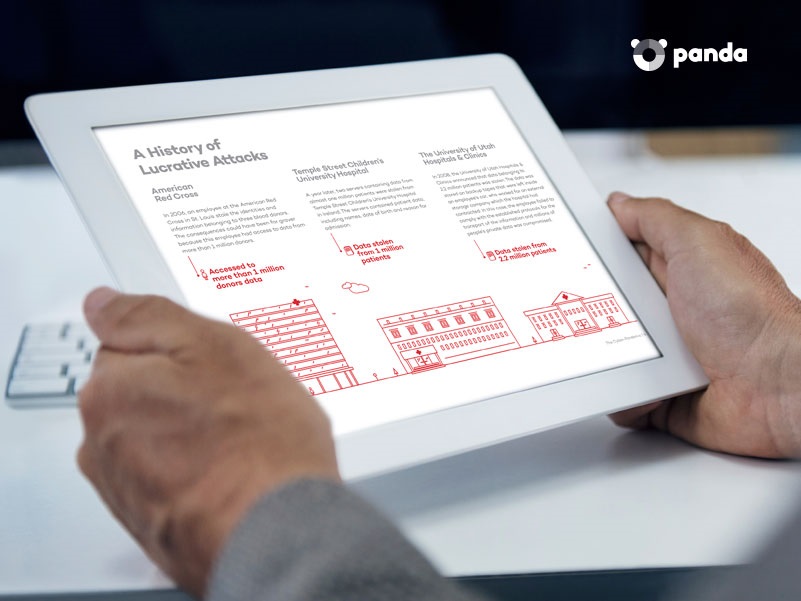
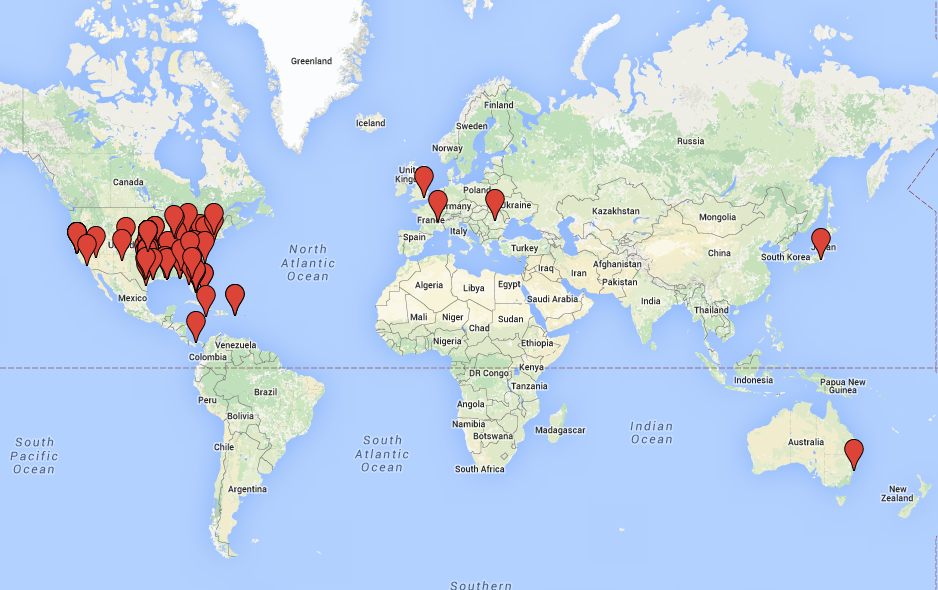
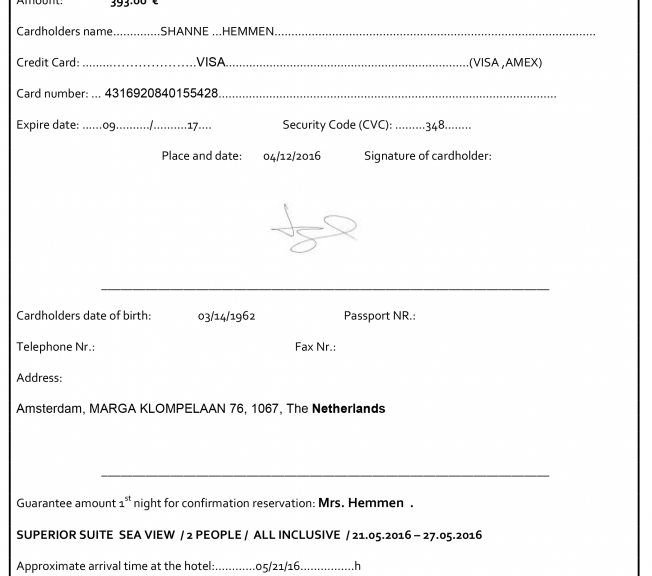
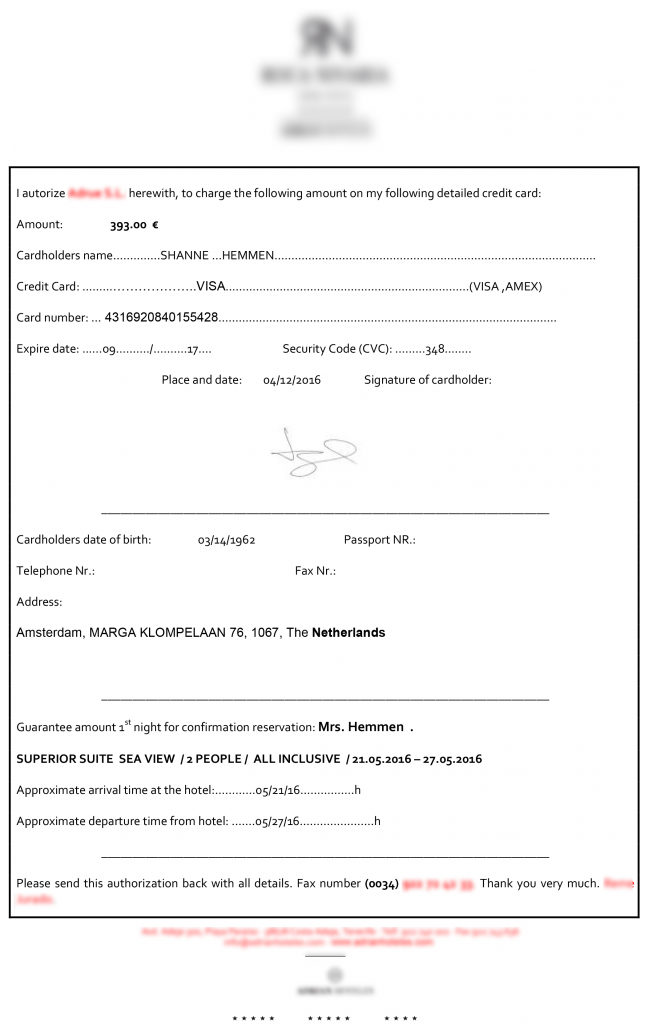
This is basically what happened in February at the Bangladesh Central Bank, where attackers infected their system with malware specifically created for this attack and tried to make fraudulent transfers totaling 951 million dollars. That money was in the account Bangladesh Central Bank had at the Federal Reserve Bank of New York. Gladly most of the transfers could be blocked, and “only” 81 million dollars were stolen. But this was not the only case.
Tien Phong Bank, a Vietnamese bank suffered a similar attack in the last Quarter of 2015. That time cybercriminals also tried to make transfers through SWIFT, although the bank could realize in time and could halt the 1 million dollars transfers already on route. And a few months earlier, in January 2015, a bank from Ecuador –Banco del Austro –was hit in a very similar way, and 9 million dollars were stolen.

What are the similarities among the three cases? Malware was used to perform the attack, and all the money transfers were made using the SWIFT network. SWIFT (Society for Worldwide Interbank Financial Telecommunication) is a cooperative society formed by thousands of financial institutions around the world. Founded in 1973, it provides different services to their members. The secure transfer of money among banks is one of the services offered and processed by the SWIFT network.
The biggest concern was if the SWIFT network, that was believed to be secure, had been compromised. If this was the case the entire financial system could be at risk. It looks like this was not the case and SWIFT has issued a press release where it clearly states this: “the SWIFT network, core messaging services and software have not been compromised.”
However, that depends on the point of view: cybercriminals successfully used the SWIFT network to perpetrate these heists. And they took a similar approach as the one described in the beginning of this article: target the weakest link in the chain. SWIFT provides a safe environment, but at the end of the day, each financial institution has its own internal system that communicates with the SWIFT network. In the same way cybercriminals were targeting final customers with banking Trojans, now instead of going after the SWIFT network, they are going after the banks connected to it. This means that, while we can say that the SWIFT network is safe so far, we can also say that there are potentially thousands of holes that exist, as many as financial institutions connected to them.
How did these attacks happen exactly?
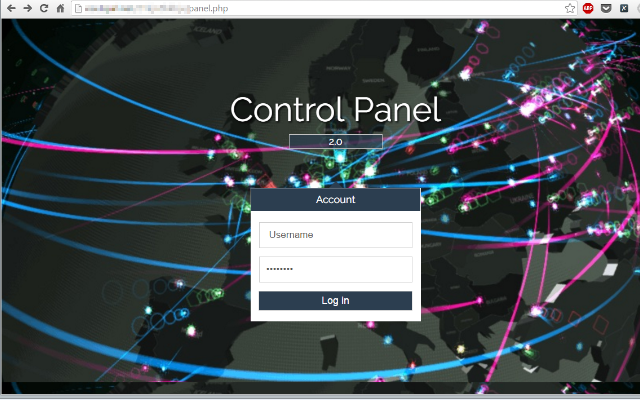
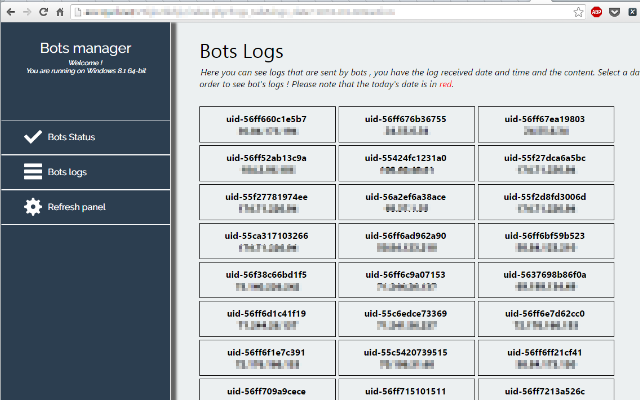
There are still many unknowns, and some of them won’t ever be solved. These criminals have covered their tracks. In fact, the main purpose of one of the malware pieces used in the heist was to delete these tracks. One thing we know for sure: malware was used. How did it enter? For this we have two different options: there was help from an insider, or it was an external attack through Internet. Both seem plausible, even more so after we learned that the security infrastructure at the Bangladesh Central Bank was obviously not good enough.
If we take a deeper look at the Bangladesh incident, it was a highly sophisticated attack targeting specifically the Bangladesh Central Bank, but the way the malware is structured (using an external configuration file, which makes no sense if this was just a one time job) points out that we’ll find new victims. They will go after banks that have flaws / weaknesses in their security model, such as those that do not monitor the execution of software in their network, and so far the information we have on the other attacks confirm this hypothesis.
In their customer communication SWIFT tells all the banks that their first priority should be to ensure that you have all preventative and detective measures in place to secure your environment.
So that’s easy, right? How can we ensure that? Is there anything at all that can be done to completely prevent any new heist?
Criminals will keep trying, and eventually they may succeed. Anyway we know what they are after (money) and what computers they want to target (those connecting to the SWIFT network). Access to the SWIFT network is highly restricted, it can only be performed from certain computers and only certain users are allowed access to them. Those computers have to be highly fortified, and of course we are not just talking about having updated software and use an antimalware solution.
Only pre-approved software should be let executed in those computers. All executed processes have to be monitored in real time, logging everything that happens and looking for abnormal behaviors. It does not matter if the attack comes from the Internet or with the help of an insider. No unauthorized software can be allowed to be executed in those terminals, and the allowed one has to be protected with anti-exploit technologies and monitored in real time in case some abnormal behavior takes place.
Of course, if some person has physical access to a target computer, at some point they could disable any security solution, which is not a problem by itself if you can get an alert about it on the console used by the security team. Is there any better indicator of compromise than someone tampering with the security software installed in a critical system?
How to avoid these cyber-attacks
One of the most frustrating things that victims have to go through is the lack of knowledge of how the incident happened. How did it happen? When did it start? For how long? What did they do once the computers were compromised? Was there any confidential information leak? As an example, in the Bangladesh Central Bank case, three pieces of malware could be recovered after the incident, but that’s what there was left. Attackers probably used many other tools that were deleted and the victim won’t know anything about them.
Knowledge is power: being able to know how a security incident happened will help you fix any security weakness in your environment.
There are only a few solutions that are capable of delivering this level of service, Panda created Adaptive Defense for these type of cases and we already have financial companies, governments, and big corporations in different verticals (health, hotels, insurance, public utilities, etc.) actively using Panda Adaptive Defense. All of them suffer not just the regular cyber-attacks, but really targeted attacks against their assets. We have shown some of them, such as the one targeting a luxury hotel chain a few weeks ago or the one against oil tankers.
Our conclusion after studying these attacks is that If those banks would have had Panda Adaptive Defense in their SWIFT connected terminals, the heist could have been stopped in time.
The post Billion Dollar Sting: A Financial Corporation’s Worst Nightmare appeared first on Panda Security Mediacenter.
 Trojans: Topping the Charts
Trojans: Topping the Charts 









 Avid WhatsApp-ers were the first ones to notice the new security changes the company put into action last week. Now, your conversations on WhatsApp are safer through end-to-end encryption. With this new security system, your messages safely travel from mobile to mobile, from your hands to the person on the other side of the message.
Avid WhatsApp-ers were the first ones to notice the new security changes the company put into action last week. Now, your conversations on WhatsApp are safer through end-to-end encryption. With this new security system, your messages safely travel from mobile to mobile, from your hands to the person on the other side of the message.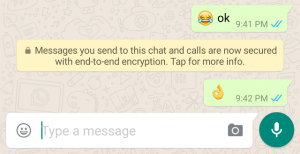




 A Logitech spokesperson has already claimed that the “vulnerability would be complex to replicate” and “is therefore a difficult and unlikely path of attack.” Despite that, the company has decided to develop a firmware update for the affected devices.
A Logitech spokesperson has already claimed that the “vulnerability would be complex to replicate” and “is therefore a difficult and unlikely path of attack.” Despite that, the company has decided to develop a firmware update for the affected devices.