5 hacker movies that got computer security well off the mark.
The post Five hacker movies that got things badly wrong appeared first on We Live Security.
5 hacker movies that got computer security well off the mark.
The post Five hacker movies that got things badly wrong appeared first on We Live Security.
On March 23rd, online video-game streaming service Twitch issued a notice that users accounts may have been hacked.
As a result of the hack, Twitch reset of all account passwords and stream keys.
In an email to users, Twitch explained what has happened and what information was potentially accessed by attackers. This included:
This isn’t the first time that hackers have targeted Twitch and its users. Some of the most well-known streamers were attacked as far back as 2013.
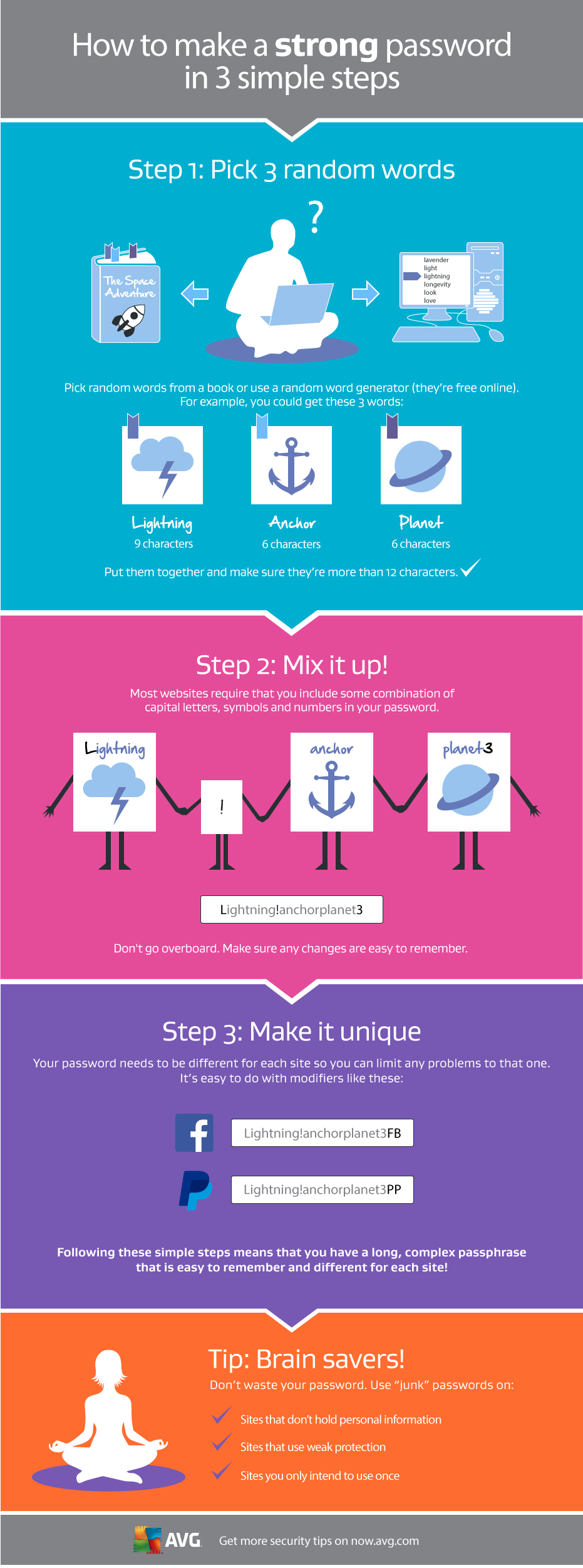
For the millions of Twitch users, the challenge remains to pick a secure and strong new password for their Twitch account. It’s important to create a new password for any account that shares the same username/password combination as their Twitch account.
Chrome got both its stable and beta versions hacked in just two minutes. Google paid $75,000 for just one buffer overflow in Chrome which allows an attacker to bypass the sandbox.
Apple’s Safari got also hit by using a use-after-free (UAF) vulnerability in an uninitialized stack pointer in the browser and bypassed the sandbox for code execution.
Internet Explorer 11 64-bit was taken out with a time-of-check to time-of-use (TOCTOU) vulnerability allowing for read/write privileges. The attacker evaded all the defensive mechanisms by using a sandbox escape through privileged JavaScript injection, all of which resulted in medium-integrity code execution.
Mozilla Firefox was hit with an out-of-bounds read/write vulnerability leading to medium-integrity code execution.
A team of researchers showed their skills against Flash by using a heap overflow remote code execution vulnerability and then leveraging a local privilege escalation in the Windows kernel through TrueType fonts, bypassing all defensive measures. They were awarded $60,000 for the Flash bug and a bonus of $25,000 for the SYSTEM escalation. Another researcher exploited Flash by using a use-after-free (UAF) remote code execution vulnerability and sandbox escape directory traversal vulnerability in the Flash broker.
Adobe Reader was exploited twice through a stack buffer overflow – once for an info leak and again for remote code execution. The researcher leveraged an integer overflow to exploit the broker, netting him a cool $60,000 USD. For the day, that brings his total payout to $90,000 USD.
The final numbers for Pwn2Own 2015 are quite impressive:
5 bugs in the Windows operating system
4 bugs in Internet Explorer 11
3 bugs in Mozilla Firefox
3 bugs in Adobe Reader
3 bugs in Adobe Flash
2 bugs in Apple Safari
1 bug in Google Chrome
————————————-
$557,500 USD bounty paid out to researchers
As with every Pwn2Own, all vulnerabilities were disclosed to their respective vendors in the “Chamber of Disclosures,” and each vendor is working to fix these bugs through their own processes.
The post Pwn2Own: Nothing is safe appeared first on Avira Blog.
Security researchers discovered a vulnerability on the Hilton HHonors website, making it straightforward to hijack any other user’s account.
The post Hilton HHonors accounts put at risk of hijacking through simple web flaw appeared first on We Live Security.
Revision Note: V1.0 (March 24, 2015): Advisory published.
Summary: Microsoft is aware of improperly issued digital certificates coming from the subordinate CA, MCS Holdings, which could be used in attempts to spoof content, perform phishing attacks, or perform man-in-the-middle attacks. The improperly issued certificates cannot be used to issue other certificates, impersonate other domains, or sign code. This issue affects all supported releases of Microsoft Windows.
Cross-site scripting (XSS) vulnerability in the Coach NG framework in IBM Business Process Manager (BPM) 8.0 through 8.0.1.3, 8.5.0 through 8.5.0.1, and 8.5.5 through 8.5.5.0 allows remote attackers to inject arbitrary web script or HTML via a crafted URL.
IBM General Parallel File System (GPFS) 3.4 before 3.4.0.32, 3.5 before 3.5.0.24, and 4.1 before 4.1.0.7 allows local users to obtain root privileges for program execution via unspecified vectors.
IBM General Parallel File System (GPFS) 3.4 before 3.4.0.32, 3.5 before 3.5.0.24, and 4.1 before 4.1.0.7 in certain cipherList configurations allows remote attackers to bypass authentication and execute arbitrary programs as root via unspecified vectors.
The mmfslinux kernel module in IBM General Parallel File System (GPFS) 3.4 before 3.4.0.32, 3.5 before 3.5.0.24, and 4.1 before 4.1.0.7 allows local users to cause a denial of service (memory corruption) via unspecified character-device ioctl calls.
Multiple cross-site scripting (XSS) vulnerabilities in the Process Portal in IBM Business Process Manager (BPM) 8.0 through 8.0.1.3, 8.5.0 through 8.5.0.1, and 8.5.5 through 8.5.5.0 allow remote authenticated users to inject arbitrary web script or HTML via unspecified data fields.